Over the years, IBM has designed many features to help you integrate your AS/400 with Novell NetWare environments running on PC servers and on the Integrated Netfinity Server for AS/400 (formerly known as the Integrated PC Server, or IPCS). Over the next few years, IBM will discontinue support for running Novell NetWare on the Integrated Netfinity Server. (See the sidebar “What if You Currently Have Novell NetWare Installed on the Integrated Netfinity Server?” for more details.) However, AS/400 shops will still be able to use many advanced AS/400-NetWare integration features with their existing Novell NetWare server networks and the new Intel-based NetWare servers they will install in years to come.
In this article, we are going to examine how you integrate Novell NetWare with your AS/400 by using IBM’s Enhanced Integration for NetWare. With this product, you can tightly integrate AS/400 and NetWare functions—such as AS/400-to-NetWare user profile synchronization, AS/400-to-NetWare print spooling, NetWare data management from the AS/400 Integrated File System (AS/400 IFS), and remote NetWare volume management—right from your AS/400 green-screen. What’s more is that the Enhanced Integration product is available now and will continue to be available even after IBM discontinues support for running Novell NetWare on the Integrated Netfinity Server. So, if you want to tie your AS/400 and NetWare servers together, this article shows you how to achieve that goal.
Extending AS/400-NetWare Integration
If you are running Novell NetWare on an Integrated Netfinity Server for AS/400, you currently have the following Licensed Program Products (LPPs) installed on your AS/400:
• 5769SA2 (SA2), Integration Services for the Integrated PC Server
• 5769SA3 (SA3), Integrating AS/400 with Novell NetWare When you use the SA2 and SA3 products, the amount of AS/400-NetWare integration you can perform is fairly limited. With these products, you can execute only the following functions for NetWare on the Integrated Netfinity Server from your AS/400:
• Monitoring the status of your server by viewing console logging messages sent to your NetWare server’s job log
• Configuring a single LAN adapter for AS/400 and NetWare server communications
• Saving NetWare server data to an AS/400 tape device by using NetWare backup programs such as SBACKUP or ArcServe
These functions are useful, but to really take advantage of AS/400-NetWare integration, you need to order and install option 25 of product 5769SS1, Enhanced Integration for NetWare. This product does not require SA2 or SA3 to be installed on the AS/400. Enhanced Integrated is an independent product that allows your AS/400 to manage and integrate with Novell NetWare servers anywhere on the network, whether they are located on an Integrated Netfinity Server or a standalone Intel-based server.
In-depth with Enhanced Integration for NetWare
Enhanced Integration consists of two parts: an AS/400 component and a Novell NetWare component. The AS/400 component adds the OS/400 displays and commands to perform NetWare server management and integration on the green-screen. The NetWare component is a NetWare Loadable Module (NLM) that intercepts requests from the AS/400 and responds by processing the correct function.
There are two versions of the Enhanced Integration NLM. One version runs on NetWare 3.12 servers; the other version runs on NetWare 4.10, Intranetware 4.11, NetWare 4.2, and NetWare 5 servers. These NLMs are designed to allow all NetWare servers in your network to be managed from an AS/400 command screen.
The Enhanced Integration product provides your AS/400 with many of the same capabilities as a NetWare PC client. AS/400 applications can fully utilize resources maintained by your NetWare server, including file and print sharing and server management. You can manage server disk partitions, monitor NetWare server status, and even submit NetWare commands to a server console.
For NetWare Directory Services (NDS) servers, you can view the NDS tree structure and attributes of objects contained in the tree. In addition, you can manage NetWare users by synchronizing AS/400 users with user profiles in the NetWare NDS tree and NetWare 3.12 servers.
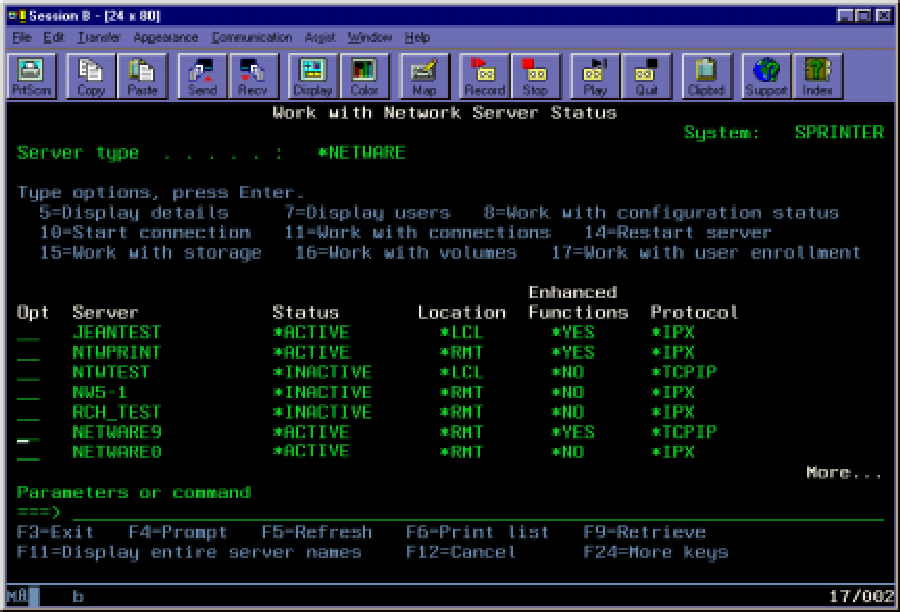
After installing Enhanced Integration, you invoke the main AS/400 screen used for NetWare server management by calling the Work with Network Sever Status (WRKNWSSTS) command as follows:
WRKNWSSTS SERVER(*ALL) SVRTYPE(*NETWARE)
This command displays a screen similar to the one in Figure 1; it shows the status and attributes of each NetWare server you are managing. Servers marked with *LCL in the Location column are running on an Integrated Netfinity Server installed on your current AS/400. Remote servers, designated with *RMT as their location, are NetWare servers running on external PC servers or an Integrated Netfinity Server inside another AS/400. Active servers with the Enhanced Integration NLM loaded are marked with *YES under the Enhanced Functions column. The Protocol column lists the protocol that OS/400 uses to communicate with the server; IPX is the default protocol unless the TCP option is explicitly specified when you load the Enhanced Integration NLM.
Starting a NetWare Session Inside OS/400
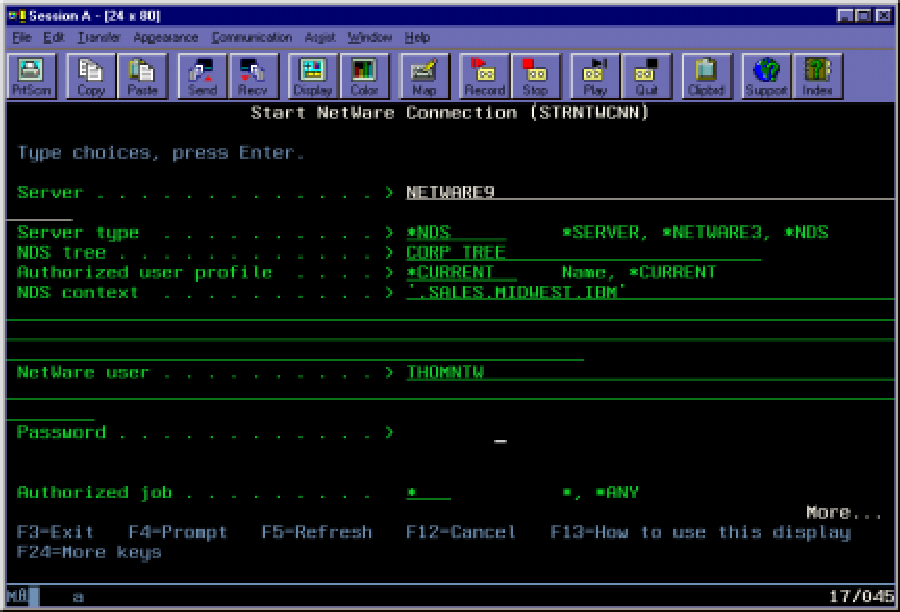
To use NetWare resources inside OS/400, you need to create a logged-in connection to your NetWare server from your AS/400. You can start an AS/400-based NetWare connection manually by using option 10 (Start connection) from the WRKNWSSTS screen
or by using the Start NetWare Connection (STRNTWCNN) command. Your AS/400 can also start a NetWare connection automatically when needed.
Figure 2 shows an AS/400 user prompt for starting a NetWare session by using the STRNTWCNN command. Here, users enter the server or tree they wish to log into, the NetWare user ID to log in, and the NetWare password. For NDS tree connections, the context containing the NetWare user is required. STRNTWCNN also contains an Authorized job (AUTJOB) parameter that allows other AS/400 jobs running under the same user ID to use the connection. You can also start a NetWare connection on behalf of another user by specifying the proper user ID in the Authorized user profile (AUTUSR) parameter. The Connection type (CNNTYPE) parameter specifies which type of NetWare server connection to start: a normal user-based connection, a connection to NetWare backup services that enables your AS/400 to back up and restore the NetWare file system and NDS by using the AS/400’s Save Object (SAV) and Restore Object (RST) commands, or a connection that uses both of these functions.
A NetWare connection can be started automatically by configuring a NetWare authentication entry for a specific AS/400 user. The authentication entry stores the NetWare connection information needed to run STRNTWCNN. When an AS/400 job needs to access NetWare resources, it can start a connection automatically by using the values in the authentication entry. If you set the AS/400 Retain Server Security Data (QRETSVRSEC) system value to 1, the user’s NetWare password is also stored in the authentication entry (in hidden form, of course). There are three AS/400 commands that you can use to configure a NetWare authentication entry:
• Add NetWare Aut Entry (ADDNTWAUTE) adds authentication entries to your AS/400.
• Remove NetWare Aut Entry (RMVNTW-AUTE) removes existing authentication entries from your AS/400.
• Work with NetWare Aut Entries (WRKNTW-AUTE) allows you to work with all of your existing authentication entries.
Figure 3 shows an example of how you could use ADDNTWAUTE to add an authentication entry that allows an AS/400 user to log into an NDS tree as a different user. If you configure the authentication entry manually, you must configure the NetWare user ID password manually to maintain synchronization with the AS/400 user ID. Password synchronization, however, can be automated by using Enhanced Integration’s user propagation feature.
Keeping AS/400 and NetWare User IDs Synchronized
OS/400’s Enhanced Integration product contains a user propagation feature that automatically creates NetWare users with the same user name and password as an AS/400 user. User propagation can also add and maintain NetWare authentication entries so NetWare connections can be started automatically whenever they are needed, providing a seamless interface for AS/400 users to utilize NetWare resources.
An AS/400 user can be enrolled (propagated) to NetWare in two ways. First, you can change the NetWare Network Server User Attributes associated with an AS/400 user profile by using the Change Network Server User Attributes (CHGNWSUSRA) command as follows:
CHGNWSUSRA USRPRF(user_name) +
PMTCTL(*NETWARE) attributes
When you enter this command, it displays a screen in which you can specify the NDS trees and NetWare 3.12 servers with which this particular AS/400 user should synchronize. You can enter the exact NetWare information or use the *NWSA value for the default server type as follows:
CHGNWSUSRA USRPRF(user_name) +
PMTCTL(*NETWARE) DFTSVRTYPE(*NWSA)
*NWSA indicates that the server values, including the name and context of your preferred NDS tree, should be retrieved from the AS/400’s global Network Server Attributes. The Display NWS Attributes (DSPNWSA) and Change NWS Attributes (CHGNWSA) commands maintain the global Network Server Attributes. You can also change a user’s Network Server Attributes by making the user a member of an AS/400 group profile and using CHGNWSUSRA to change the group profile’s attributes as follows:
CHGNWSUSRA USRPRF(group_profile_name) +
PMTCTL(*NETWARE) attributes
Running CHGNWSUSRA for a group profile enrolls the user profile members contained in that group.
An administrator can monitor the status of AS/400 enrollments by selecting option 17 (Work with User Enrollments) for a particular NetWare server off the WRKNWS-STS screen or by using the Work with NWS User Enrollment (WRKNWSENR) command. The WRKNWSENR screen shows which servers and trees each AS/400 user is enrolled in as well as pending updates and possible enrollment failures. User propagation is made possible by starting a connection for the special AS/400 profile, QNETWARE. The profile synchronization program uses QNETWARE to log into NetWare and create or modify NetWare user profiles. A NetWare administrator must manually create a NetWare user named QNETWARE in the root of the NDS tree or on a NetWare 3.12 server with administrator authority and a password equal to the AS/400 QNETWARE profile. The AS/400 can then start a connection for the QNETWARE user to perform profile synchronization tasks as AS/400 user profiles are enrolled and modified. To ensure AS/400 security, the QNETWARE profile is created as *DISABLED and should stay that way. But the QNETWARE user on NetWare must be enabled and have a valid password so logins will be successful when profile synchronization tasks are attempted.
OS/400 and NetWare File and Printer Sharing
When AS/400 users log into Novell NetWare, they can access files and objects in the QNETWARE file system on the AS/400 IFS. The QNETWARE file system is added to your AS/400 IFS when the Enhanced Integration product is installed. QNETWARE is the root directory under which applications and users access NetWare servers and trees. The Copy to Stream File (CPYTOSTMF) and Copy from Stream File (CPYFRMSTMF) commands can be used to copy files from NetWare to AS/400 physical files and back again. Higher-level language programs such as C and C++ can be written to read and write NetWare files and integrate their data into AS/400 applications. There are several AS/400 IFS commands, such as Work with Object Links (WRKLNK), Copy Object (CPY), and Rename Object (RNM), that can be used to traverse the QNETWARE tree and manipulate files. WRKLNK can also be used to traverse and view the objects in a NetWare NDS tree.
NetWare printer management is another useful feature of Enhanced Integration for NetWare. Using the Create Output Queue (CRTOUTQ) command, the AS/400 can be configured to print spool files to NetWare output queues. When using CRTOUTQ to create a remote output queue, you use the Remote system (RMTSYS) parameter to specify the NetWare 3.12 server or NDS tree that contains the NetWare print queue. The Remote printer queue (RMTPRTQ) parameter is used to specify the NetWare print queue. If the print queue is in the NetWare NDS tree, the print queue name must be a fully qualified NDS name that begins with a period (.). If the name does not begin with a period, it is
appended to the default context value found in the Network Service Attributes (which you can view by running the DSPNWSA command).
For your AS/400-to-NetWare remote output queues, you should consider entering *NOWAIT in the Destination options (DESTOPT) parameter on the CRTOUTQ command. The *NOWAIT option indicates that the AS/400 can remove the spool file from the AS/400 output queue before the spool file has completed printing in NetWare. By default, the AS/400 waits until NetWare has printed or deleted the file before removing it from the AS/400 output queue.
Using this remote output queue technique, an AS/400 writer job starts a temporary NetWare connection for the AS/400 user associated with the spool file whenever it sends a spool file to the NetWare remote output queue on the AS/400. This connection times out and ends after 15 minutes of idle time.
NetWare Volume Management from Your AS/400
To manage NetWare server volumes from your AS/400, select option 16 from the WRKNWSSTS screen or use the Work with NetWare Volumes (WRKNTWVOL) command. Using this command, you can create, delete, or change the size of your NetWare volumes.
Another way to mount volumes or perform any other NetWare command that can be typed on a NetWare console screen is to use Submit Network Server Command (SBMNWSCMD). This feature is useful for loading additional NLMs, performing simple maintenance on your NetWare servers, or checking NetWare server status. For example, to check the version of the Enhanced Integration NLM that you have installed on a NetWare
4.1 server (whose NLM name is AS4NW410 NLM), type the following command from the AS/400 console:
SBMNWSCMD CMD(‘modules AS4NW410’)
SERVER(NETWARE9)
The command returns with the data displayed on the NetWare console.
Support Continues
Although the need to move from an Integrated Netfinity Server to an Intel-based PC server is required, the primary integration features continue to be available. The ability to manage NetWare users, provide host-to-LAN printing, and manage NetWare volumes are all provided with the NetWare Enhanced Integration product. There are currently no plans to end support for this product, so you can expect these AS/400 integration features to continue to assist you with your multiplatform environment.
References and Related Materials
Integrating AS/400 with Novell NetWare V4R3 (SC41-5124-01) can be viewed online atpublib.boulder.ibm.com/cgi-bin/bookmgr/DOCNUM/SC41-5124-01.
What if You Currently Have Novell NetWare Installed on the Integrated Netfinity Server?
IBM has announced that product 5769SA3 (SA3), Integrating AS/400 with Novell NetWare, will no longer be available in OS/400 releases after V4R4. SA3 is used for running Novell NetWare on the Integrated Netfinity Server. This announcement means that customers can expect support from IBM through January 2001 for problems relating to current SA3 product capabilities but cannot expect any enhancements; the product will no longer be available.
If you’re running Novell NetWare on the Integrated Netfinity Server for AS/400, IBM advises that you migrate your NetWare data to an external PC server as soon as it is convenient. By moving to an external server, you can still take advantage of the Enhanced Integration for NetWare product and not worry about having problems with an unsupported product.
IBM has also announced the end of support for product 5769SA2 (SA2), Integration Services for the Integrated PC Server. This does not mean that IBM is ending support for the Integrated Netfinity Server for AS/400. It means only that this particular software offering will no longer be available. IBM will still offer other software products that run on the Integrated Netfinity Server for AS/400; that solution will continue to be available.
The end of SA2 support will happen around May 31, 2001. This may cause some concern about what to do with the Integrated Netfinity Server that you already own. If the adapter you own has a Pentium 200-MHz or faster processor, you can install product 5769SS1, option 29—AS/400 Integration with Windows NT Server—as an option to migrate your NetWare data to Windows NT before SA3 loses support.
Another migration option is to load your NetWare data on the AS/400 IFS and access it with AS/400 NetServer. IBM has a new Redbook, Advantage AS/400 NetServer (SG24-5196), which contains a chapter on migrating OS/2 WarpServer and Novell NetWare data to AS/400 NetServer. For future information about NetWare and WarpServer withdrawal from support, see informational APAR II11689, “Warp Server and NetWare IPCS Migration,” on the IBM APAR Web site at as400service.rochester.ibm.com/n_dir/nas4apar.nsf/nas4aparhome.
Figure 1: The WRKNWSSTS screen displays the status of each NetWare server you are managing and its related attributes.
 |
 |
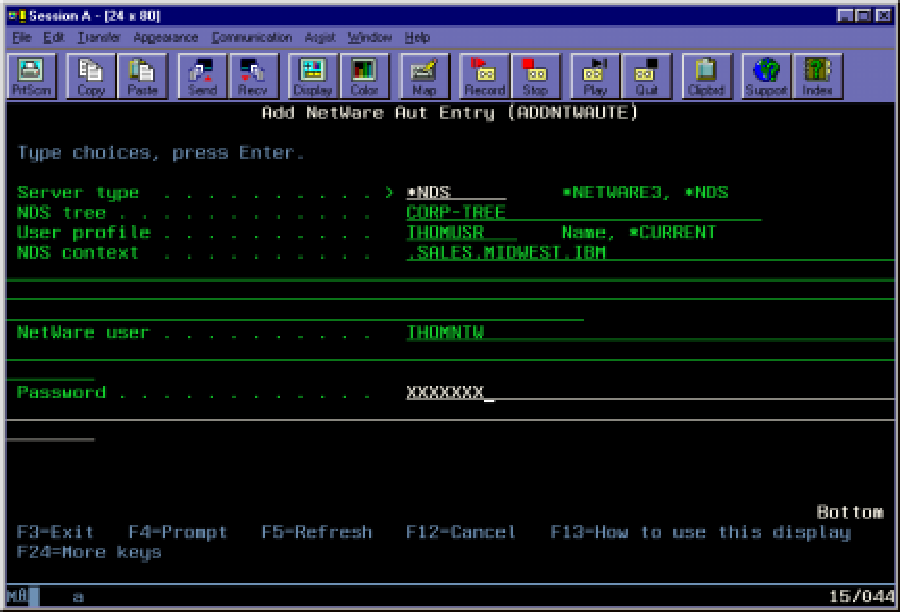 |
Figure 3: Use ADDNTWAUTE to allow an AS/400 user to log into an NDS tree as a different user.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online