The iSeries LDAP server has been bundled with OS/400 since V4R3. V4R3 and V4R4 implemented LDAP Version 2; V4R5 and beyond implement Version 3. IBM steadily and quietly enhances the server and the type of information that is published to the server.
So What Is LDAP?
Since the Internet was first established in 1969 with a connection between UCLA in Los Angeles, California, and Stanford Research Institute in San Mateo, California, the need for a directory of resources--such as people, places, things, and machines--has been apparent.
You know that so-and-so uses the Internet, but you don't know his email address.
You got a phone message from someone working for your company, but you don't know who the person is, what department she's in, or who she works for.
You designed a system that requires routing remote printed output to the printer closest to a specific user, but you don't know how to find the printer.
Different organizations within your company use different email servers. It is common--especially in larger organizations--to see mixtures of technology in an organization's various operating units.
How do you locate people? How do you find their email addresses or telephone numbers?
These are just some of the problems that iSeries Directory Server (LDAP) can solve.
In the late 1980s, the International Organization for Standardization (ISO) first began to work on creating a standardized directory under the organization's Open Systems Integration (OSI) X.500 protocol. The product, Directory Access Protocol (DAP), was not viable for widespread implementation. The Internet Architecture Board and its engineering subsidiary, the Internet Engineering Task Force (IETF), picked up the challenge and produced RFC1488, The X.500 String Representation of Standard Attribute Syntaxes, in July 1993. This was the beginning of LDAP.
Today, many large public information services--such as Google.com and BigFoot.com--publish Internet directories using LDAP as the basis for their public directory systems. Microsoft, Netscape, and Lotus (Notes) incorporate LDAP into their Web and email client software, allowing users to configure their client tools to use an LDAP directory as their address book.
The iSeries LDAP server is a unique server that leverages your iSeries environment by publishing iSeries system information to your server, and there's some good information out there about how to use it. My latest book, IBM eServer iSeries--Built for e-business, published by IBM Press, describes the structure and content of an LDAP directory. An article published in the IGNITe/400 User Group newsletter entitled "OS/400 User Authentication with iSeries LDAP" provides step-by-step instructions for configuring an iSeries LDAP server. IBM has published a superb Redbook, Implementation and Practical Use of LDAP on the IBM eServer iSeries Server (SG24-6193-00), that describes in detail how to configure your LDAP server and begin publishing user and system information. In this article, I will focus on what you can do with LDAP and the information that can be implemented in a matter of minutes after configuring your LDAP server on an iSeries.
Many LDAP server implementations are available for many different platforms, and a lot of them are open-source or public domain and may be downloaded free from the Internet. Even IBM gives away its Windows, Unix, and Linux versions of its LDAP server.
The advantage of the iSeries LDAP server is the publishing utilities bundled with the product to leverage your system information instantly. Unlike other implementations, the iSeries Directory Server is ready to use within minutes.
Information About People
The iSeries Directory Server publishes information about OS/400 users from the OS/400 System Directory (WRKDIRE). "Publishing" means that information stored in your system directory is read and added to the Directory Server's database. Whenever a change is made to the system directory, the change is detected and published to the Directory Server. The quality of the information published depends on the information you have captured about users in your system directory. If you provide extensive user information--including full name, title, telephone number, etc.--this information will be automatically published to your Directory Server along with the user ID and other basic system information. The publishing job is QGLDPUBA, which runs in the QSYSWRK subsystem on your machine when both the Directory Server and the publishing jobs are configured. APIs and commands are available to update the system directory.
These publishing jobs are incredibly sophisticated. If you maintain your directory entries for your user information directly within the Directory Server, this information will not be overwritten by the publishing utility. When a new user is added to the directory, the utility detects and adds that information. If a user is removed, the Directory Server entry is removed.
LDAP Authentication
Once you start publishing your user information, you may configure your HTTP servers (original or Apache) or your WebSphere Application Server (WAS) to use your LDAP Directory Server for user authentication. This is a tremendous feature of the LDAP Directory Server. Many companies run their servers on a separate iSeries machine to isolate the HTTP servers from the production machine. To authenticate users without using LDAP, you would have to replicate your user profiles to the server machine.
With LDAP, just configure your HTTP server with LDAP-based authentication and point to the LDAP server running on your production machine. When a user is required to authenticate via HTTP basic authentication, the information will be passed securely to the LDAP server, which will authenticate your users for you. You do not have to replicate user profiles to remote machines just for authentication.
iSeries Printers
Locating a user's preferred printer and ensuring that it is available to print and that it supports the protocol you wish to use is a challenge for most shops.
The LDAP publishing utility, QGLDPUBE, will automatically publish information about all iSeries printers to the LDAP server. This utility is incredibly sophisticated. It will publish the status of the printer (Active or Inactive) and update your LDAP directory upon detecting a change in status. The publishing utility picks up local twinax as well as network printers. It locates print queues and identifies the type and capabilities of the printer.
I built a facility that allows users to update their directory entries with their preferred printers. My application programs can retrieve this information and quickly and easily locate the correct printer for each user. You may wish to allow users to override the printer when they are away from their desks, and you may let them choose several printers with different capabilities so that they can select the most appropriate printer for the specific print job.
Publishing iSeries printers to the LDAP directory is not documented; I was told about this facility from one of my IBM contacts. Here, I am sharing this information with you.
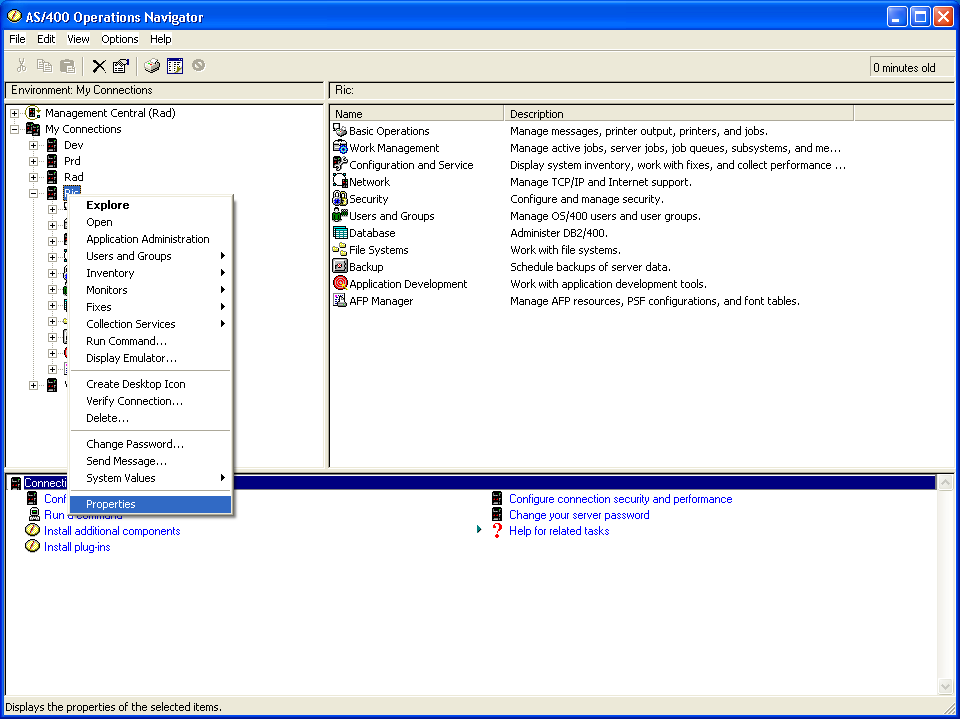
In Operations Navigator, select the machine that you wish to publish data from. Right-click on the machine name and select Properties, as shown in Figure 1.
Figure 1: Select the machine that you wish to publish data from.
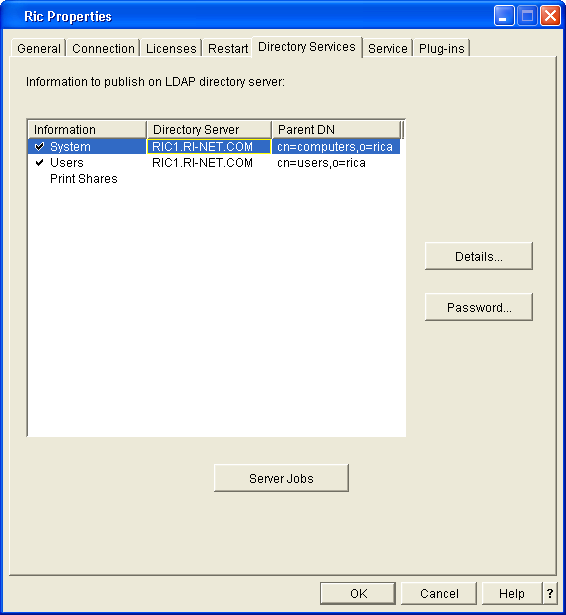
Figure 2 illustrates the main LDAP publishing screen found on the Directory Services tab. This system is already configured to publish system information and user information. Click Details to publish printers.
Figure 2: On the Directory Services tab, click Details to publish printers.
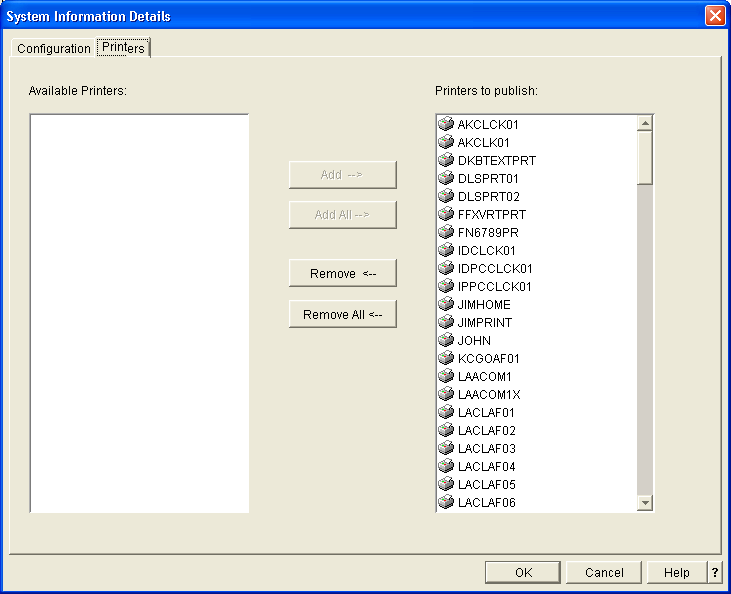
Figure 3 illustrates the System Information Details view of the Directory Server publishing function in Operations Navigator. This display is presented when you click the Printers tab at the upper left corner of the screen. When you initially open the display, all printers known to your iSeries will be displayed in the left column. You may add or remove printers by selecting printers from the list on the right and clicking the buttons in the middle of screen.
Figure 3: The System Information Details view displays all printers known to your iSeries.
Allow up to 10 minutes for the publishing utility to locate and publish your printers. From this point forward, the directory will automatically be updated if an active printer becomes inactive or if an inactive printer becomes active.
Windows Printers
Printers that are defined and controlled by a Microsoft Windows NT/2000/XP server can be published to your iSeries LDAP server to provide a single repository of printers for all of your applications to use. See the Redbook Implementation and Practical Use of LDAP on the IBM eServer iSeries Server (SG24-6193-00) for detailed, step-by-step instructions for publishing Windows printers.
LDAP Schema
LDAP is a self-defining facility. It contains a schema (a form of data dictionary) with over 2,500 predefined classes provided by IBM to handle common business and technical entities. You may either use the publishing tools or populate these classes yourself. You may also add classes and/or attributes to the schema to store any type of information you would like to store in your directory. The guideline is to store information that is retrieved frequently but updated rarely.
IBM's LDAP Directory Schema: Overview is a superb online Web-based tool that allows you to explore IBM's standard schema definitions.
Accessing LDAP
After you set up LDAP and begin publishing information to your LDAP-based directory server, you will want to retrieve information from the directory. You may use standard tools or write your own program access.
Mail Clients
Most modern mail clients--including Microsoft Outlook, Lotus Notes, and Netscape's mail client--allow you to configure an LDAP directory server as an address book. The client will search the directory server as well as any local address books to resolve names. You may add several servers to your mail client and search them all in the order specified.
The IBM Directory Management Tool (DMT)
IBM provides a tool to retrieve information about the structure of your LDAP schema as well as the data contents of the server. You may login with sufficient authority and use the DMT to add, delete, or update entries in the directory.
Figure 4 illustrates a partial screen capture of a DMT display that lists the printers published to this particular server.
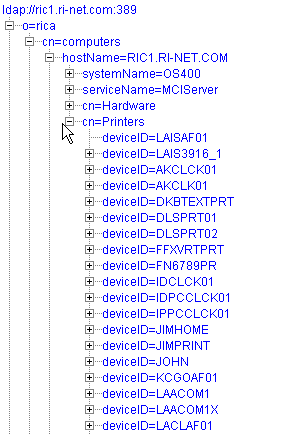
Figure 4: The DMT view of the Directory Information Tree lists the printers published to a particular server.
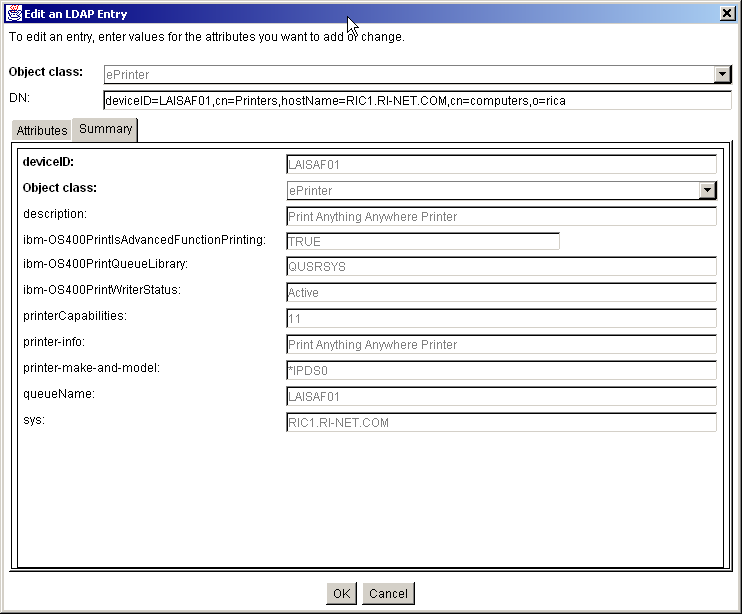
Figure 5 shows the detailed attributes of an AFP/DS printer as displayed in the DMT. Notice that the printer reports that it is Active.
Figure 5: The DMT Summary display for a printer shows the detailed attributes of an AFP/DS printer.
Qshell Commands
The LDAP Directory Server for iSeries is delivered with a set of commands that you may run from within the Qshell command interpreter. The "ldapsearch" utility is the most useful; it allows you to test and run queries in the Qshell environment to ensure that your query syntax is correct when you write programs. For details on LDAP command support, see the Directory Server topic under Networking ->TCP/IP in the IBM iSeries Information Center.
APIs
A full set of APIs suitable for use with RPG, COBOL, C, or C++ may be found in the IBM Information Center by using the new API Finder and selecting Directory Services from the drop-down list of system components.
Java JNDI
If you are writing applications in Java that need to access your LDAP-based Directory Server, you will want to use the Java Naming and Directory Interface (JNDI). You may download this Java API from http://java.sun.com/products/jndi/ and also locate documentation and sample code.
The JNDI provides a Java interface to retrieve and update any type of directory server that supports the JNDI interface (both LDAP and DNS are supported).
Other Uses
My goal is to use the iSeries LDAP Directory Server as a repository of our company's infrastructure-type information, such as branches, office addresses, equipment, people, jobs, etc. Our strategy is to start small, leveraging the user and printer information published automatically by IBM to the server.
We will write Java JNDI-based programs to retrieve data from the server, and then we'll front-end the Java programs with RPG programs that replace our existing utility programs that read database files today. This way, we can gradually migrate our applications to LDAP as a central repository.
Since we use Lotus Domino as our mail server while our parent and affiliate companies use other mail servers, we will all use LDAP as a common address book and repository of contact information to locate people and resources through the greater company.
Over time, we will migrate more information to the LDAP Directory Server and add program function to retrieve and use this information.
A Final Note
Since we enabled the system publishing feature for LDAP and we use Management Central to keep our information updated and current, we can now see all of our products, PTFs, and a great deal of other information published by Management Central to the LDAP Directory Server. At V5R2, IBM's Quality of Service (QoS) facility now publishes QoS policy rules to your LDAP server.
It appears that IBM will continue to leverage the LDAP Directory Server as a repository for information about the system as time progresses. In fact, it seems that the LDAP Directory Server is becoming the main OS/400 information repository.
Bob Cancilla is the author the popular IBM Press book, IBM eServer iSeries: Built for e-business. He also wrote Getting Down to e-business with AS/400, available from MC Press.























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online