As organizations expand and technology evolves, application integration
becomes increasingly important. Component reuse and interoperability
requirements have driven companies to move toward a Service-Oriented
Architecture (SOA), where self-contained business logic can be exposed and
shared efficiently across applications and platforms. At the heart of recent
success in SOA designs are Web services, a technology that enables disjoint
applications to communicate with each other in a platform- and
language-independent manner.
Specifically, a Web service is a
self-contained piece of software available via standard network
protocols—such as HTTP(S), FTP, and SMTP—and exposed by a
standardized interface, the Web Service Description Language (WSDL). The WSDL is
a schema-defined XML document that includes all of the information an
application requires to call, or consume, the Web service. Data is
exchanged between the application and the Web service, using a standard XML
messaging format called Simple Object Access Protocol (SOAP).
Web
services, like all technology, are rapidly evolving. Implementations range from
basic Remote Procedure Calls (RPCs) to loosely coupled, document-style
messaging. The WSDL and SOAP specifications are expanding to include support for
secure, reliable, transactional Web services. Enhancements in these areas are
helping to make Web services the preferred solution for application integration
throughout the industry.
Basics
Historically, differences in platforms (Windows,
UNIX, iSeries, etc.) and programming languages (Java, COBOL, C, etc.) have
created complexities, making application integration difficult and costly.
However, industry-wide standards for transport protocols, coupled with XML
standards for Web services, have helped organizations spend considerably less
time working out communication and messaging details, allowing them to focus on
servicing their business requirements.
To help describe the various
components of Web services, organizations in the industry have defined a
technology stack. An example stack that demonstrates the relationships
between various Web services standards is depicted in Figure 1.
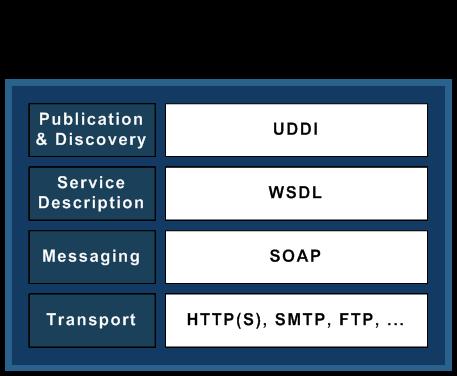
Figure 1: This example Web services stack shows the relationship between the Web Services Standards. (Click images to enlarge.)
Transport
The Web services transport layer defines the communications protocol for exchanging data between Web services. As shown in Figure 1, it can use many different Internet transport protocols. Early adopters of SOAP 1.1, the initial Web service specifications controlled by the W3C (World Wide Web Consortium), assumed HTTP(S) for Web service transport. However, other protocols, such as SMTP, FTP, and IBM's MQSeries are increasingly being used and have been incorporated into the updated SOAP 1.2 specification.
Messaging
The Web services messaging layer uses the XML-based
SOAP, which is described by
the W3C as "a simple and lightweight mechanism for exchanging structured and
typed information between peers in a decentralized, distributed environment
using XML."
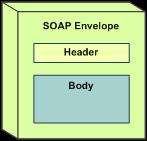
Figure 2: The SOAP message consists of three parts.
A SOAP
message (Figure 2) is an XML document consisting of three parts: the
envelope describing the message, the header describing the data
types and rules, and the body containing the actual message. The
following code example shows a basic SOAP message requesting the temperature for
a particular ZIP code:
xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:SOAP-ENC="http://schemas.xmlsoap.org/soap/encoding/"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:xsd="http://www.w3.org/2001/XMLSchema">
The platform-independent nature of XML allows applications to understand
and decode the SOAP XML messages, regardless of the platform and programming
language. For example, an application running on a UNIX platform using C++ is
able to request the temperature using the above SOAP request from an application
running on an iSeries using Java. The server-side application might respond with
a SOAP message containing an appropriate response; an example message is shown
below.
xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:xsd="http://www.w3.org/2001/XMLSchema">
Service Description
The Web Service Description Language (WSDL) is a
standardized XML document that describes everything that an application requires
to consume a Web service. It includes information such as the operations
available, their corresponding interface (input and output parameters), the
messaging format, and the transport protocol. As with the SOAP message, the fact
that WSDL is described in a standard XML format makes it machine-readable and
platform-independent. An example of a simple WSDL document describing the
temperature Web service is below: encodingStyle="http://schemas.xmlsoap.org/soap/encoding/" namespace="urn:xmethods-Temperature"/>
location="http://services.xmethods.net:80/soap/servlet/rpcrouter"/>
xmlns="http://schemas.xmlsoap.org/wsdl/"
targetNamespace="http://www.xmethods.net/sd/TemperatureService.wsdl"
name="TemperatureService">
Publication (UDDI)
Universal Description, Discovery, and Integration
(UDDI) is an XML-based standard for publishing, finding, and describing Web
services over the Internet. The UDDI specification can be used to create a
registry of Web services, similar to registries that exist for telephone
numbers.
UDDI registries are used by clients wishing to discover
and consume specific Web services and by clients wishing to publish
their own Web services. Clients use SOAP messages to communicate with UDDI
registries, which provide access to WSDL documents published by
organizations.
Figure 3 describes the relationship between SOAP, WSDL,
and UDDI.
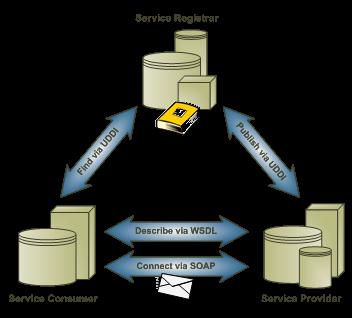
Figure 3: This diagram describes the relationships among SOAP, WSDL, and UDDI.
SOAP Messaging in Detail
The WSDL specification allows for two distinct
styles of messaging: document and RPC. With document-style messaging, the
message details contained within the SOAP body element of the request and
response are in the form of an XML document in a format agreed upon by the
sender and receiver. In contrast, RPC-style messaging uses a specific XML
representation of a procedure call to describe the message details.
The
WSDL specification also allows for two methods of serializing the XML data
contained within the SOAP body element: SOAP encoding and literal. Messages that
use SOAP encoding serialize their data by conforming to the set of rules defined
in the SOAP 1.1 specification, section 5. Literal messages are serialized
according to an XML schema definition.
These two choices in Web service
design—the messaging style and the method used to serialize the XML
data—result in four basic styles of Web services available today. These
are as shown in the table below.
|
Web Service Design
Options
|
||
|
|
Document Style
|
RPC Style
|
|
SOAP Encoding
|
Document/encoded
|
RPC/encoded
|
|
Literal
|
Document/literal
|
RPC/literal
|
Of the four styles listed, the two most commonly used are RPC/encoded and document/literal. Both styles are examined in the following sections.
RPC/encoded
RPC/encoded was one of the first Web service styles
supported by early versions of SOAP engines. SOAP engines are used to generate
implementations of the SOAP protocol, which can include the transport layer and
the creation and consumption of the WSDL and the corresponding SOAP messages.
RPC/encoded is the simplest of encoding styles because it enables SOAP engines
to serialize and de-serialize data and automatically bind data to the remote
object of an RPC. All that is left for the developer to do is map the input and
output parameters of the Web service. An RPC/encoded sample of a WSDL and
corresponding SOAP request are presented in Appendix
A.
The following excerpt taken from the WSDL section in Appendix A
highlights the reference to the section of the WSDL that indicates the messaging
style (binding style).
transport="http://schemas.xmlsoap.org/soap/http"/>
The code below references the section of the WSDL that indicates the
encoding style (use).
encodingStyle="http://schemas.xmlsoap.org/soap/encoding/"
namespace="http://soapserver.jsm.lansa.com"/>
The major strength of the RPC/encoded style
is its ease of use for both the service provider and the service consumer. The
WSDL resembles an intuitive RPC-type interface. RPC/encoded SOAP messages
include the operation name, allowing them to be dispatched accordingly, as shown
in the add operation in the following example:
However, RPC/encoded Web services do have some major drawbacks. First, the style is not compliant with WS-I. (The WS-I is an organization that governs standards for Web service interoperability.) A Web service is considered compliant with WS-I if it is written in accordance with these standards. This means that with RPC/encoded Web services, there is a possibility that clients on other platforms might not be able to properly use the Web service. The second drawback is that the message details and the Web service interface (WSDL) are tightly coupled. Any change to a particular parameter of a specific operation of the Web service requires changing and re-publishing the entire WSDL; thus, consumers of the Web service will have to re-build their client-side SOAP engine according to the revised WSDL.
Document/literal
The document/literal style of Web services is
becoming more commonly used. It overcomes the two major issues with RPC/encoded
Web services: 1) Document/literal Web services conform to the WS-I guidelines
for interoperability, and 2) There is loose coupling between the message body
and the WSDL. Because the message body is a normal XML document defined by a
schema and is independent of the WSDL, changes to message parameters do not
require a change to the WSDL. In this case, the client would be required to
modify only the XML messages to match the new schema and would not have to
adjust the SOAP engine.
Appendix
B contains an example of a WSDL for a document/literal Web service. Notice
that the WSDL binding style indicates a document style of messaging and a
literal
encoding.
transport="http://schemas.xmlsoap.org/soap/http"/>
One
drawback to this style is that because an XML schema defines the message body
(independent of the WSDL), the operation name in the SOAP message is lost.
Without the operation name, it is difficult, if not impossible, for the SOAP
engine to dispatch the message appropriately. This can be seen in the SOAP
message request fragment below:
Notice that the body of the SOAP request contains two parameters, person
and phone, but the operation name (add) is not reflected anywhere in the body of
the message.
To overcome this limitation, many implementations are
beginning to use the wrapped convention for document/literal-style
messages. Wrapped document/literal messages are document/literal messages that
follow two additional rules: 1) The body of the message contains only one
element, and 2) That element has the same name as that of the operation being
invoked. An example of this is presented in the code fragment below. The
complete SOAP message is listed in Appendix B.
The body of this SOAP request now contains one element, appropriately
named after the "add" operation, which wraps the message parameters (person and
phone). This allows SOAP engines to determine the invoked operation from the
SOAP document and dispatch the message accordingly.
The only significant
limitation to the wrapped document/literal style (also true for the non-wrapped
document/literal style) is the inability to override operations within the Web
service. This is because a Web service with overridden operations would require
defining multiple elements with the same name, which is not allowed in the
schema specification. This limitation does not exist for RPC/encoded Web
services.
Which One to Use?
Wrapped document/literal Web services present many advantages that generally outweigh their limitations. As Web services and SOAP tools become more advanced, added complexity will become a non-factor. On one hand, RPC/encoded Web services allow for overriding operations and provide a straightforward interface to a pre-existing RPC. On the other hand, where flexibility and interoperability are key requirements, wrapped document/literal Web services are the most suitable and are the recommended approach moving forward.
The Evolution of Web Services
Web services are quickly becoming the method of choice for many organizations looking for interoperable application integration. And while the basic specifications have been mostly effective in this area, companies and individuals are looking to expand on them to allow for features such as increased security, reliable messaging, and support for transactions. As a result, organizations such as Microsoft and IBM have collaborated to create a set of specifications to meet these demands. These include specifications for security, transactions, and reliable messaging, which are discussed in more detail below.
Composability
To ensure that these new capabilities are not
imposed and don't affect existing Web services solutions, the specifications
have been designed using the principle of composability. This term
describes the design concept in which individual services (or specifications)
can be used as required. For example, one organization can choose to implement a
Web service utilizing the security and reliable messaging specifications, while
another may choose to implement transactions only. Each specification is
completely optional and independent, allowing companies to implement only the
specifications they require.
Figure 4 shows an updated Web services
stack, which now includes specifications for security, transactions, and
reliable messaging.
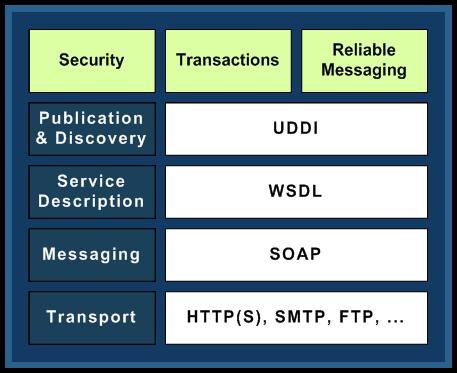
Figure 4: An updated SOAP stack includes security, transactions, and
reliable messaging.
Security
The basic Web services
specifications allow for security to be handled at the transport level.
Transport protocols can ensure that communication between two parties is secure.
Therefore, Web services can take advantage of transport protocol
implementations, such as HTTPS and FTPS to secure the communication
link.
Sometimes, however, additional security is required at the
application level. For example, it may be required that all or part of the SOAP
message be encrypted to ensure that only the intended party is able to decrypt
and view the contents. WS-Security enables this type of security. The
specification utilizes existing security protocols such as Kerberos and X509 and
defines how they are to be used in an interoperable manner.
Another
security specification, WS-Trust, enables Web services to establish trusted
relationships between applications. For example, an organization using Web
services with WS-Trust is able to use a security token to validate the sender of
a particular SOAP message.
The additional security specifications,
including WS-Security and WS-Trust, can work in addition to transport-level
security to help companies achieve the level of security that they
require.
Transactions
Some business functions are difficult to
implement because they require coordination between related business processes.
For example, imagine a financial institution that provides a service allowing
individuals to transfer money from one account to another. Such a service is
actually made up of a number of smaller services, including services to check
the source account balance, debit the source account, and credit the target
account. These services need to be carried out within a transaction,
i.e., they must be coordinated and performed in a particular sequence. A
credit should not be applied to the target account before the balance of the
source account is verified. These types of transactional business services would
be difficult to implement using the basic specifications for Web
services.
However, recent specifications are providing Web services with
these transactional capabilities. WS-Coordination, for example, facilitates
coordination between related services. It defines additional elements to be
included within related SOAP messages and defines a coordinator service,
which acts to coordinate and sequence the related operations.
WS-AtomicTransaction and WS-BusinessActivity build on the WS-Coordination
specification, adding support for atomic, all-or-nothing business transactions,
with error and exception-handling capabilities.
Reliable
Messaging
The inherently unreliable nature of application communication
over the Internet forces companies to build reliable messaging techniques into
their distributed applications. Until recently, organizations using Web services
have had to employ techniques outside of the base Web services specifications to
ensure that messages are exchanged reliably. These techniques are employed at
the application level and require some negotiation on standards between business
partners.
The WS-ReliableMessaging specification allows companies to
enable reliable messaging from within the Web services stack, once again
allowing applications to focus back on the business logic. The specification
defines a protocol that ensures that messages are delivered in the correct order
without duplication.
With Web Services, SOA Is Evolving
Organizations are evolving toward a Service-Oriented Architecture, enabling services to be shared across applications, networks, and platforms. Web services have helped to achieve this difficult task, employing XML standards that allow data exchange and application integration in a platform-independent manner. Wrapped document/literal-style messaging is providing for increased flexibility and interoperable Web services, where entire XML documents are exchanged containing the request and return parameters. In addition, emerging standards for security, transactions, and reliable messaging are enabling organizations to rely on Web services to help with creating state-of-the-art distributed, multi-platform applications, while allowing their focus to shift back to what they know best: their business.
References
An
Introduction to the Web Services Architecture and Its Specifications
Secure,
Reliable, Transacted Web Services: Architecture and Composition
Which
Style of WSDL Should I Use?
The
"Wrapped" Document/Literal Convention
Keep
Up with the Web Service Styles (and Uses)
Rahim
Lalani is a senior professional services consultant at LANSA, a leading provider of
application development and integration software. He has worked with numerous
clients to design and implement enterprise-scale applications, taking advantage
of the latest technologies for application integration. You may contact Rahim at




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online