Are you constantly interrupted during the day with questions like, “Can you help me? The printer attached to the sales system is not working. What was the command to get it running again?” Do you get paged at night by the system operator asking, “What should I do? I’m getting a communication error message on the system again.” Do you wish there was some way to put commands and fix-it tricks in a central location, in plain English, so you could end those interruptions? You can—all it takes are a few command definitions and tasks using the Operations Navigator component called Management Central. Before we discuss how to set up and use the function, we’ll cover some Management Central basics.
The Basics of Management Central
While many of the functions in Operations Navigator are for all users, the Management Central component is primarily for system administrators and operators. For this reason, it is an optionally installable part of Operations Navigator. In fact, the default is not to install this component, so the first thing you’ll need to do is perform a selective installation of AS/400 Client Access Express for Windows and request the installation of the Management Central component. To accomplish this from the PC on which you want to install Management Central, click on the Windows Start button and then select Programs/IBM AS/400 Client Access Express/Selective Setup. Follow the on-screen options to selectively install Management Central.
Next, you need to understand a few basic terms when using Management Central:
• Endpoint System—This is any iSeries or AS/400 system on which you want to perform an operation such as running a command or program. (For the purposes of this article, we will use iSeries to refer to both AS/400 and iSeries systems.) Endpoint Systems must use TCP/IP for connectivity to other iSeries and PC systems. Endpoint Systems can be grouped together to form a System Group.
• Central System—This is a special Endpoint System for which Management Central applications are defined and controlled. To accept user-specified information required to
define the Management Central application, the Central System must have connectivity to a graphical client. To control the application, the Central System must also have connectivity to any other Endpoint System. Management Central controls the Endpoint Systems by creating a control application on the Central System to ensure that all requested Endpoint Systems start the defined application (such as running a command) and report back with the required information.
• Graphical client—This is your PC. The graphical client acts as an interface that enables the setup, running, and viewing of Management Central applications. Graphical clients connect directly to the Central System to communicate with the control applications managing your network of Endpoint Systems.
• Command definition—This is a template that contains user-specified information such as commands or programs to run. Whether output should be saved is also stored in the Command definition. Definitions are stored on the Central System and can be shared for others to view, change, or copy.
• Command task—This is an instance of a command definition that has been requested to be run or has been scheduled to be run at a specific time on a set of Endpoint Systems and System Groups. A command task has a definite beginning and end. It can be shared with other users, but it cannot be changed.
Now that we’ve introduced installation and the basic concepts of Management Central, it’s time to set up your command definitions and get them to work for you.
Defining a Command
Wouldn’t it be nice to have a place where your system operators could go if they ran into a specific error message or needed to issue a command to a system? Management Central can provide the place for a repository of common commands known as command definitions. As an example, suppose you need to issue a command to start your payroll jobs. To set up this command, you need to be working from your graphical client (PC). Click on the Operations Navigator icon on your desktop. If you have installed the Management Central component, you should see the words “Management Central” in the left panel of the Operations Navigator window. Click on the plus sign (+) by Management Central and you will then see Definitions (see Figure 1). Click on the plus sign by Definition to show the Command icon. Right-click on the Command icon and a pop-up menu will be displayed. Select New Definitions, and you will be shown the default properties for your new definition (see Figure 2).
The General tab is the first one shown for the command definition property page. The page under this tab requires you to give your definition a name, such as Get payroll jobs running, and an optional description such as “This will start the queue for payroll jobs.” You will also enter the command you would like to run when this is executed as a command task on this page. One cool feature—if you previously specified a command and you’ve forgotten the exact command syntax—is to press the Previous Commands button and view the commands you’ve used. The default saves the last 20 commands, but the number of saved previous commands can be changed to your preference. In addition, there is a button on this tab that will cause Management Central to initiate a syntax check of an entered command. The syntax check is based on the command as it exists on the Central System. If the syntax of the entered command is not correct, help text will appear. To ensure that the commands you enter are syntactically correct, you can enter the command on the iSeries and press F14 to display the command with its keywords. In a future release of Operations Navigator, the ability to prompt commands within Management Central may be available. This should help alleviate any parameter errors. At this point, you can copy
the command to the graphical client’s clipboard and then paste it into the Command window in Operations Navigator. Make sure that the commands you enter will work in batch mode by using the Display Command (DSPCMD) command. For example, to see if DSPLIBL can be run in batch mode, you would enter DSPCMD DSPLIBL and look at the information shown as Mode(s) in which valid, which indicates it will run in *BATCH.
The next tab, Options, allows the user to specify additional information. The first item on the Options tab allows you to specify whether inquiry messages are to automatically get a response. If you do not choose to reply automatically to inquiry messages and they occur, the command task will stay in the status of Started but will not continue processing until the user replies to the message. The other item on the Options tab allows the user to specify whether a job log is to be kept upon successful completion of a task. Unless you have a specific reason to store job logs, you probably will not want to save job logs once you are sure the command is working correctly.
The final tab, Share, allows you to decide if others can access a definition. You’ll want to specify no sharing until after you have tested your definition and know it is doing what you want. At that point, you may choose to switch to read-only sharing. Shared command definitions can become the first resource for your administrators and operators to use.
Running a Command Task
Now that you’ve defined command definitions and shared them with others, it’s time for your system operator to get involved. Your system operator can use the graphical client to start the evening processes for all systems in the network. This can be accomplished by starting Operations Navigator and going into Definitions under Management Central to view the command definitions that have been set up. Commands such as Get payroll jobs running can be found here (see Figure 1). Right-clicking on the command definition in the right panel and selecting Run will bring up a dialog box (see Figure 3, page 103) in which your system operator can select the systems that he wants the command to run. The appropriate Endpoint Systems or System Groups should be selected, and clicking on the Add button will put them in the Selected Systems list. Once all the systems and groups are chosen, the Central System will inform the appropriate Endpoint Systems to issue the command that will start the correct jobs for payroll. At this point, the graphical client will be used only to view the status of the command task. The Central System is now in control of the command and will receive information from each Endpoint System on the status of the task. It is not necessary to have your PC connected to the Central System for the commands to be completed on the Endpoint Systems.
Checking and Rerunning Commands
Now that you have created a command task, you will want to see if it has been completed successfully. To do this, expand the Management Central part of Operations Navigator. You will see a container just below Management Central called Task Activity, which you can select to explore its contents. In the right pane, you should see your Get payroll jobs running command task. Double-click on the task to open the Status window shown in Figure 4. This will allow you to see if the task is completed or failed for each Endpoint System, and you will be given the option to view any spooled file generated. To view a job log or output, you must have a connection to the Endpoint System from your graphical client, since the job log resides on the Endpoint System. This is the only instance in which the graphical client would need to have a direct connection to the Endpoint System.
Suppose a command was not completed successfully, or suppose you want to rerun the same command tomorrow night. What do you do now? You have two options. If the command task was completed successfully but you would like to run it on a different set of systems, you can select the command task and click on Start based on.... This will run the
same command task but allow you to select a different set of Endpoint Systems. If the
command task failed and you need to change the actual command or program to be run, you will need to go back to the original command definition and make the appropriate changes to the command. The task activity and command definitions allow you to reuse them over and over again without figuring out the command, program, and system details every time.
Automatically Scheduling Commands
The payroll example could be a job you need to ensure runs every month. Why don’t you automate it so that your system operator doesn’t even have to think about it? Automating this job is quite simple. Go back to Command Definitions, right-click on the Get payroll jobs running command, and select Run. You will be asked to select the systems on which to run the command. Instead of clicking the OK button, this time click the Schedule button (see Figure 3). You will be taken to the Management Central Scheduler panel, where you will be asked to specify the date, frequency (e.g., once, daily, weekly, monthly), and time to start running this command (see Figure 5). Click OK, and the task will be placed in the list of scheduled tasks. The scheduled tasks are listed right under the initial task activity container. If you need a more elaborate job scheduler, you can purchase the IBM Advanced Job Scheduler. The Advanced Job Scheduler product has an Operations Navigator plug-in to be used in place of the Management Central Scheduler. If you do use the Advanced Job Scheduler, we recommend that you ensure that the Advanced Job Scheduler plug-in is installed on those graphical clients that will have access to scheduled tasks. However, the Advanced Job Scheduler only needs to be installed on the iSeries being used as the Central System, since all scheduling is initiated from that machine.
Additional Perks
We have discussed ways to automate your system operations, but how else can you take advantage of Management Central functions? Management Central can be used to automate system operator tasks that are proactive, such as running redundant cleanup tasks or activating devices. You can also build a repository of commands that can be performed on a system or group of systems to fix problems or handle unexpected situations, such as using VRYCFG to vary back on a device. I cannot think of a better place to keep your repository of knowledge (a.k.a. Operators Guide Run book) than on an iSeries. These tools will help you keep control of your system and correct problems quickly. With a bit of thought and some hands-on experience with Management Central command definitions and tasks, you can create your own iSeries book of knowledge. As an added benefit, you might just get your days and nights back to yourself.
REFERENCES AND RELATED MATERIALS
• A Smart Way to Manage AS/400 Systems, Redbook (SG24-5407-00)
• Management Central home page: www.ibm.com/eserver/iseries/sftsol/MgmtCentral.htm
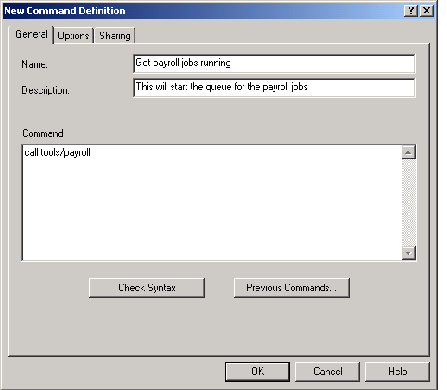
Figure 1: View all your command definitions on this screen.
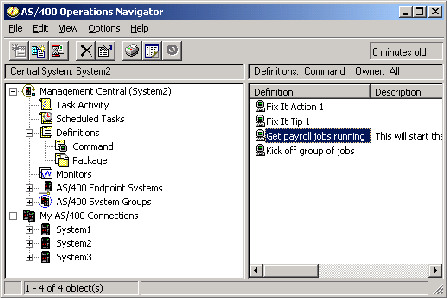
Figure 2: This screen shows the basic information for a new command definition.
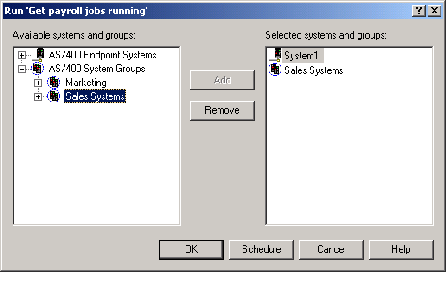
Figure 3: Run a command now or schedule it for later.
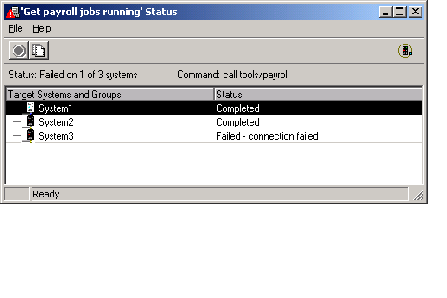
Figure 4: Use this window to check the status of the command task.
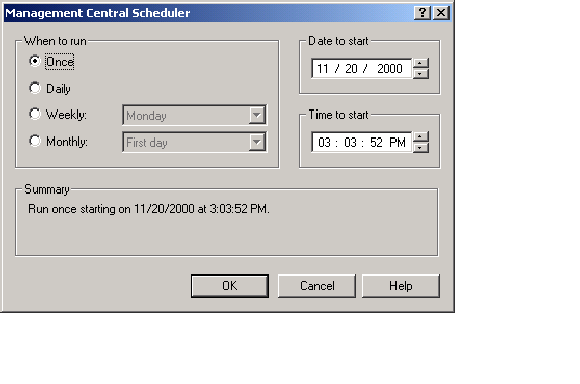
Figure 5: Use the Management Central Scheduler panel to schedule a task.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online