In our previous article, we provided a basic understanding of firmware concepts and terminology. We also introduced the important concept of concurrent firmware maintenance (CFM): what it is and what it isn't, and how it brings value in reducing (but not eliminating) the downtime associated with maintaining firmware. This article will fulfill our promise to provide a better understanding of how to install firmware fixpacks and firmware releases and how to determine if the fixpack installation will be disruptive or concurrent. We will also discuss firmware fix strategies.
Two Methods for Installing Firmware
There are two methods for installing system firmware on iSeries systems. The first is through the use of i5/OS PTFs. You can use this method to install both new releases and fixpacks. However, installing system firmware through this method is always distributive (i.e., will require a system IPL). The other method for installing firmware releases and fixpacks, and the one this article will focus on, is through the interfaces provided by the Hardware Management Console (HMC).
So how do you know if your HMC is controlling firmware Licensed Internal Code (LIC) updates? You can determine this in two ways. The first is to start the HMC Change Internal Code Wizard. The i5/OS has firmware (LIC) update control if you receive this message: "The requested action is not allowed. One or more targets are configured for LIC updates through the operating system." The other way is to issue the lslic command from the HMC Command Line Interface. The HMC controls firmware updates if the command returns "management status" as "enabled."
How Do I Know What's Installed and Whether I Can Do a Concurrent Update of My Firmware?
You can use the HMC to find out what level of system firmware code is currently installed on your system. On the left side of the HMC main menu (Figure 1), you'll see the servers the HMC is managing. Expand the Licensed Internal Code Maintenance option and click on Licensed Internal Code Updates. As you can see, the Licensed Internal Code Updates menu supports the installation of release upgrades via Upgrade Licensed Internal Code to a new release and fixpack updates via Change Licensed Internal Code for the current release. 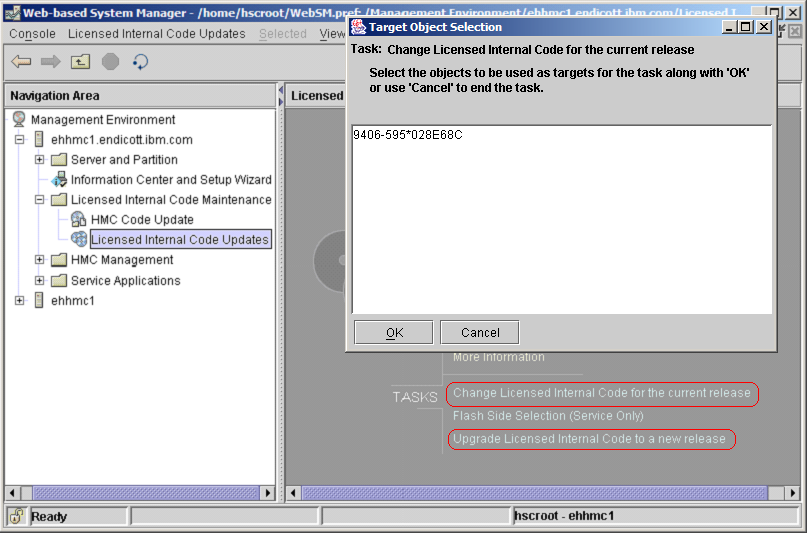
Figure 1: Perform Licensed Internal Code installation via the HMC. (Click images to enlarge.)
When you choose to install a fixpack, you'll be asked to select a "target object." For the majority of you, a target object is basically the system that will be the object of the firmware installation. What is displayed is a list of the systems managed by that HMC. Just select the system or systems (yes, you can update multiple systems at the same time) and click on OK. You may get a message asking you to wait while system information is being retrieved.
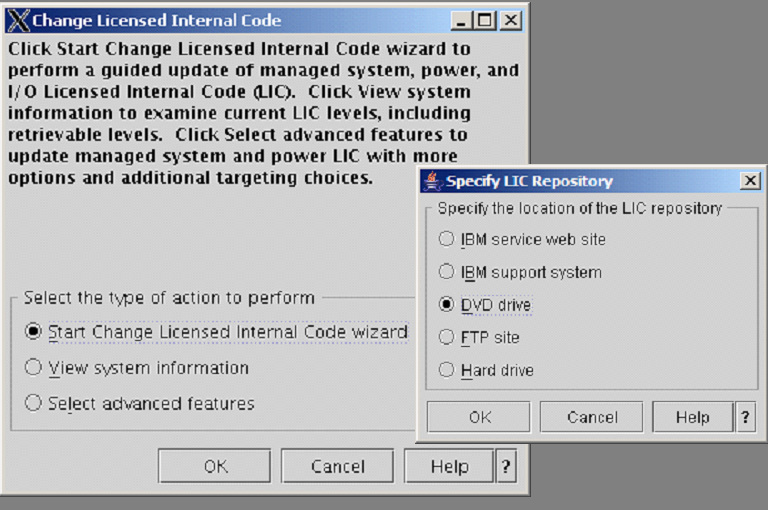
You will be given three options (Figure 2):
- To install the firmware update via the wizard
- To view system information
- To use advanced firmware installation features
Figure 2: Let the Licensed Internal Code Updates Wizard step you through the process.
The option to view system information allows you to see what has been installed and activated on the managed system (i.e., your target object). It also allows you to view what is available in the LIC (Service) repository (think of this as where the fixes to be installed are located) and to determine what can be activated concurrently based on the existing activated level. You will be asked for the location of the LIC repository (Figure 2). The LIC repository is accessible either via communication lines (e.g., IBM Retain or IBM Service Web site) or via the hard disk or DVD drive of the HMC. If you want to view what is already installed on the system to be updated, you can select none.
By the way, the HMC includes a Guided Setup Wizard to help you configure the initial network connectivity and modem setting to enable access to the IBM Web site and RETAIN. LIC (Service) repositories can support multiple fixpack levels. The IBM Service Web site will also allow you to download AIX IO drivers.
As we look at the system firmware information (Figures 3a and 3b), it is probably a good time to review some firmware concepts. The installed level is the highest level of code on the system. This code may or may not have been activated (i.e., loaded into memory). The activated level is the code level that the system is currently running; it's usually on the t-side flash. The accepted code is the lowest level of code on the system; it's usually on the p-side flash. If you specified a repository for firmware fixes, you'll also see information regarding concurrent and disruptive fixpacks. The Retrievable Disruptive Activate Level designates the highest code level in the service repository. This code if installed would result in a disruptive firmware update (i.e., you'll need to shut down all partitions and either turn the system off or put it in standby mode). Likewise, the Retrievable Concurrent Activate Level is the highest code level available in the repository location that can be retrieved, installed, and activated without a disruption. 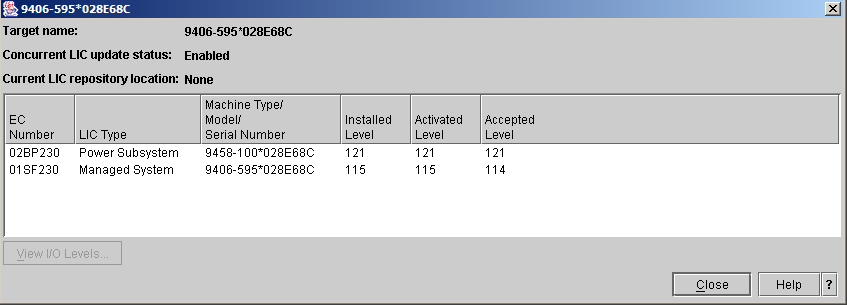
Figure 3a: Check your installed, activated, and accepted code levels.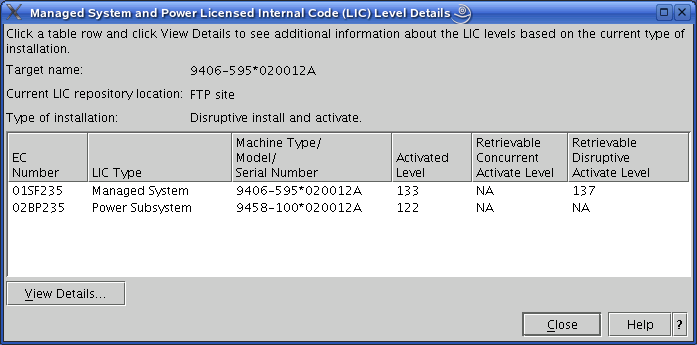
Figure 3b: Check the status of your Licensed Internal Code.
The Microcode downloads Web page is an excellent resource for information about firmware fixes (such as current firmware level, fixpack cover letters, etc). While you are there, sign up for firmware fix notifications (under the Related Information tab). Also, be sure to check out the Hardware Management Console support page for the latest information on HMC fixes and releases.
Firmware Installation via the HMC--Advanced Option
To start the system firmware installation, Select the Licensed Internal Code Updates option under the Licensed Internal Code Maintenance tree (Figure 1). Select the target of the firmware update (i.e., your system) and click on OK. This time, when you get to the Change Licensed Internal Code menu, choose the Select Advanced Features option. This option allows you to perform the individual parts of the installation processes (such as install and activate a fixpack and accept a fixpack). It also allows you to remove a fixpack and activate the previous level (this means copy the p-side flash over to the t-side flash and reload memory with this level) and to download fixpacks from the IBM repository onto a DVD or the hard drive of the HMC (Figure 4). The option for system information is identical to that of the View System Information option previously discussed. 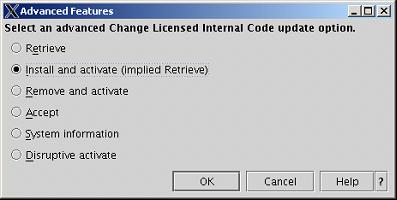
Figure 4: Take advantage of the HMC's advanced features.
If you want to install fixes, select Install and Activate (implied Retrieve). In addition to being asked where your fixpack is located, you'll be given the options to install the latest concurrent fixpack, the latest fixpack (even if disruptive), or a specific level of fixpack. You'll also be given the option to move the t-side code over to the p-side, prior to the installation. If you select to specify LIC levels, you'll be shown the Specify LIC Levels screen (Figure 5). From this screen, you can select either to view the levels available for installation or to change the level that you want to install. You can also display the fixpack cover letter by selecting to open the LIC Level Details. 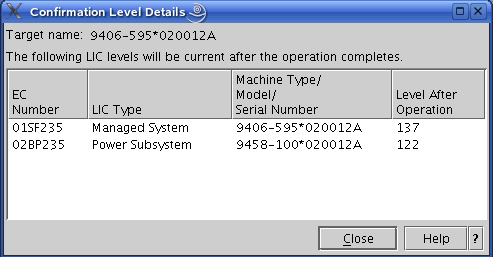
Figure 5: Specify LIC levels.
When you click OK from the Specify LIC Levels screen, you'll be told what type of install (concurrent or disruptive) this update will be. In addition, you'll be given the option to perform a concurrent install (with deferred disruptive activate) or a disruptive install and activate. IBM recommends that if the type of update is disruptive, then the install selection should be disruptive "install and activate." Lastly, you'll be given a confirmation menu (Figure 6) that provides information about the type of install (disruptive or concurrent) and information about the systems to be updated and the firmware levels to be installed. 
Figure 6: Confirm the action.
OK, that was fun (not). Is there an easier way? Yes! Read on!
Installing Firmware Fixpacks via the HMC Wizard
The Start Change Licensed Internal Code Wizard option is the simplest way to install firmware fixpacks. It installs the latest level and automatically accepts the previously activated level or moves the previous level of fixes from the t-side to the p-side flash (in iSeries terminology, moves firmware fixes from B-side to A-side). Let's use the easiest method, the wizard, to install a firmware fixpack. The first thing you will be prompted for is the location of the fixpack (Figure 3). You will go through two prompts; click Next to both of these prompts. The first prompt just tells you that you are attempting to perform a firmware update and that if no fixpacks are in the firmware repository, nothing will happen and no further prompts will be shown. The second prompt lets you know whether the firmware update will be concurrent, disruptive, or deferred. It also gives you the option of changing the installation method to the advanced procedure. By the way, the wizard will also tell you whether you are at the latest level of fixpack (i.e., no firmware update required) and whether a new release level of firmware is available (in case you would prefer to cancel the fixpack update and instead perform a release upgrade, but remember that release upgrades are disruptive). Lastly, you'll be shown a confirmation menu (Figure 6). Note that on the confirmation screen, both managed system and power subsystem updates are available. The power subsystem updates (if required for your system) will be installed first. Then system firmware updates will be installed. A failure in the power subsystem update will stop the update process, and the managed system firmware update will not occur.
Upgrading to a New Release Level
The discussion so far has been about updating the firmware within a certain release. At some point, you will need to update to a new release level, either because the new release has new function you want or because the release you are on will soon reach the end of the one-year fix support window. The good news is that you've already learned almost everything you need to know in the instructions above.
Starting from the panel called Licensed Internal Code Installation via the HMC, select Update Licensed Internal Code to a New Release. The next steps will be nearly the same as the Change Licensed Internal Code path. Target selection and repository selection are just as described above. The first thing that is different when upgrading to a new release level is that you must accept the license for the new firmware (Figure 7). 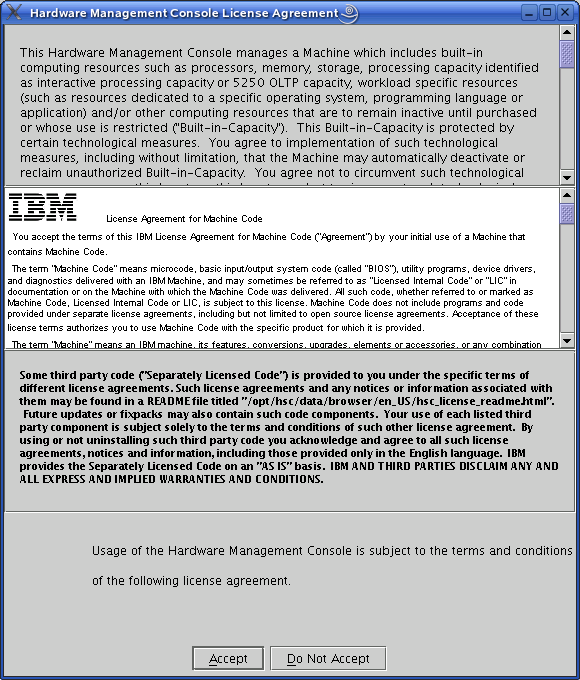
Figure 7: Accept the license for the new firmware.
After accepting the license, a panel will show which firmware components will be updated and which firmware levels will be installed (Figure 8). When you press OK on this panel, the installation will begin, and a progress panel will be shown.
Figure 8: Confirm the action.
There are a few things you should know. As described above, an upgrade to a new release is always disruptive, so there will be no option to do this concurrently; therefore, it's important to do the upgrade at a maintenance window when you can perform a deep IPL. Another thing is that a release upgrade automatically performs the "accept" step as well, so at the end of the upgrade, both the temporary and permanent flash sides will be at the new release. If your system has Bulk Power Control (BPC) firmware (on an i595 system) both the BPC and the system firmware will be updated to the new release; it is not an option to have the components at different release levels. And one last thing: It is always recommended that you first update your HMC to the new release level before updating any system firmware components to the new release.
Firmware Maintenance Information Strategy
IBM has roughly two firmware releases per year. Each firmware release is supported for at least one year, and fixpacks are created as necessary for the supported firmware releases. The average size of a fixpack is around 13 MB, so broadband access (RETAIN or IBM Web site) is the most efficient option. Dial-up access will require a connect to RETAIN, so if you have no communication lines to the HMC, you can either download the ISO image to a PC and create a CD or order a CD from IBM Service. IBM recommends that your system firmware be 01SF23_126 or higher and that your HMC firmware be at a minimum of V4R5.0 HMC code with efix MH00318.
Firmware Maintenance Strategy
The above discussion addresses the tools provided for firmware maintenance, but how do you apply these tools most effectively to keep system firmware up-to-date with the least downtime? These tools and processes require some additional decisions, since there will be more than one release available to choose from.
The first suggestion is that if a system is HMC-managed, use the HMC for firmware updates. Using the HMC allows you to take advantage of being able to do concurrent firmware updates when they are available.
The second suggestion is to stay on the same release level (e.g., 2.3.0) until there is a good reason to switch. Then, plan the switch well in advance. For most people, there will be four reasons to switch to another release level:
- The release level you are on is approaching its end-of-service date (i.e., has been available for about a year and hence will go out of service support soon).
- You have multiple systems in your environment, and you wish to have all at the same firmware level.
- A new release has new function that is needed in your environment.
- You have a scheduled maintenance action that will cause a platform reboot. This would be a good time to examine whether you should also update to a new firmware release. This way, if fixes are needed in the future, you will be on a release where the fixes are provided, and you can apply them concurrently.
When updating the system firmware to a new release, you should also update your HMC to the corresponding HMC firmware release. The HMC update should be installed prior to installing the system firmware.
The third suggestion is to install all firmware fixes that can be applied concurrently. You should consider checking the IBM repository on a regular basis (perhaps monthly) for new fixes and then apply newer fixes that can be applied concurrently.
What if the most current fixpack would result in a disruptive install (non-concurrent)? In this case, it makes sense to examine the content of the fixpack to see what was fixed and whether it impacts your system. IBM releases disruptive fixpacks only when it is necessary to fix important problems; therefore, if one of these fixes in the fixpack affects your system, it may make sense to schedule a maintenance window to get the fix installed. Every fixpack has a corresponding README file (also known as the "XML" file) that describes the fixpack contents. Disruptive fixes are listed first, and these disruptive changes should be examined closely to see whether your system requires any of them.
If it is necessary to install a disruptive fixpack, consider whether a fixpack is available at a newer release that contains the fixes you need. Since the update process will be disruptive, it may make sense to also get on a newer release.
Lastly, for best performance during the firmware installation, you should first download the latest firmware levels to the Service Repository located on your HMC. Then, you should install the firmware from the HMC hard drive.
Got It?
We hope this article has given you a better understanding of the strategies you might employ to install firmware. If you'd like additional information, IBM has provided an education module called "Performing Licensed Internal Code Maintenance" on IBM Resource Link at https://www-1.ibm.com/servers/resourcelink/edu03010.nsf/Web+Search/CC3C9D290831717A85256FF90050EC70?Open&Highlight=2,Performing,licensed. (Note: This sight requires user ID and password.)
Stephen Linam is a Senior Technical Staff Member in IBM Global Firmware Development. He was an architect of the P5 Concurrent Firmware Maintenance Support; before that, he worked in architecture and development for P5 and pSeries P4 firmware and the AIX operating system. Before joining IBM in 1984, he developed applications in RPG. Stephen can be reached at
Becky Schmieding is an IBM Certified Executive Project Manager at IBM Rochester on the Product Definition Team (PDT) responsible for the E2E upgrade process. She is a noted speaker and author on PC5250, iSeries Navigator, and the iSeries Access family of products. She can be contacted at




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online