In this article, we will present WRKLPAR, a utility that relies on the Change Logical Partition Configuration API (QYHCHCOP) and allows for viewing and changing status of certain parts of the system's hardware configuration, such as processors and storage.
The primary audience of this article obviously consists of system administrators and other related staff responsible for the creation and maintenance of iSeries partitions, but because we will cover some other subjects like XML, stored procedures, and panel groups, we think that this article reaches a wider audience.
Logical partitioning (LPAR) was introduced with OS/400 V4R4 and was enhanced in V5R1 to allow dynamic movement of resources--such as CPU, memory, and interactive performance--without requiring an IPL.
This new dynamic movement of processor/memory and interactive resources means you can move these resources to and from partitions as required. For example, during workload peaks or prior to starting your month-end routine in a production partition, you can move entire or partial processors from non-critical partitions to this production partition. Once the month-end is complete, you can then transfer the resources back or reassign them to other partitions.
Since V5R1, you have two choices: You can use the GUI functions from iSeries Navigator that allow immediate or scheduled movements, or you can use the traditional green-screen menus in DST/SST. But if you need an application-based resource movement, you can use the chargeable LPAR API Toolkit that provides a rich set of commands that allows you to write simple CL programs to retrieve and dynamically modify processing resources for existing partitions. Or you can write your own commands and directly call QYHCHCOP, the same API used by iSeries Navigator.
Do You Speak XML ?
This exciting new API, apart from requiring an extremely detailed knowledge of iSeries hardware and LPAR internals, doesn't get requests and send responses with data mapped to standard record formats as other APIs do. Instead, it communicates with XML messages. Here, we assume you are already a little familiar with this text-based standard for representing data.
In practice, a typical request to be sent to the API in order to get the system information is an XML message like this:
And this is the response from the API:
SerialNumber="00-00ABC" PointerTagsInactiveCapable="Yes"
CommercialProcessingWorkloadTotal="11180"
CommercialProcessingWorkloadInteractive="11180"
HighSpeedLinkCapable="Yes" HighSpeedLinkPoolMaximum="1"
VirtualOptiConnectCapable="Yes"
VirtualOptiConnectPoolMaximum="1" PartitionsConfigured="6"
PartitionsMaximum="32" PhysicalProcessors="8"
PhysicalProcessorsAvail="1" PhysicalProcessorsAvailPending="1"
ProcessingUnits="7.00" ProcessingUnitsPending="7.00"
ProcessingUnitsAvail="0.00" ProcessingUnitsAvailPending="0.00"
ProcessorPoolCapable="Yes" ProcessorPoolsConfigured="1"
ProcessorPoolsMaximum="1" MainStorage="65536"
MainStorageAvail="0" MainStorageAvailPending="0"
InteractivePerformance="100" InteractivePerformanceAvail="26"
InteractivePerformanceAvailPending="26"/>
Interpreting this reply requires a process called "parsing," which can be done in many ways: You can do it with RPG ILE code (using, for example, the %SCAN built-in function), or you can use a professional parser. Our utility relies on the IBM licensed program XML Toolkit for iSeries (5733-XT1), an XML parser based on cross-platform, open-source code that is designed to be compliant with industry standards. In addition to providing the XML for C++ parser, the Toolkit includes a unique iSeries interface called XML Procedural Parser that allows applications written in RPG, C, or COBOL to access an XML parser.
The XML Toolkit allows multiple XML parsers, XSL transformer versions, XML scripting, and Web Services Client to be installed on the same iSeries platform simultaneously. The installation procedures are structured to allow you to separately install the parsers and transformer (service programs) or the development environment (API documentation, include files, and samples) or both for each XML parser and XSL transformer version you want.
To install the XML Toolkit, you insert the XML Toolkit for iSeries CD-ROM into the device drive and install the *BASE option and any other required options by using the Restore Licensed Program (RSTLICPGM) command. To use this utility, you have to install at least options 3 and 4:
This code installs the *BASE code required for all other options.
This installs the XML Version 5.0 parser service programs. This option is installed as QXML4C500 and QXML4PR500 in library QXMLTOOLS.
This installs XML Version 5.0 parser API documentation, sample, and include files. The C, RPG, and COBOL development environment is installed in library QXMLDEV500. The C++ development environment is installed in the IFS directory /QIBM/ProdData/xmltoolkit/xml5_0_0.
After the product has been installed, you can use it directly from your RPG ILE program:
Include the parser procedure prototypes:
Create a parser object:
Parse the XML document:
During this step, the parser verifies that the document is well-formed and valid and builds a DOM tree containing the XML document content
Make sure the parser did not find any errors in the document:
%str(ErrMsgp:120) = %TRIMR(Qxml_ErrMsg);
QxmlXercesDOMParser_delete(DomParse );
QxmlTerm();
ErrMsg = %trim(ErrMsg) +
' Row: ' + %char(Qxml_RtnLine) +
' Column: ' + %char(Qxml_RtnCol);
SndPgmMsg ('*ESCAPE': 'ParseSystem': ' ':ErrMsg);
endif;
Get a reference to the parsed document:
Use DOM parser procedures to navigate the DOM structure (in the XML reply message shown above, for example):
SystemInfo.TypeModel = getAttr(Node:'TypeModel');
SystemInfo.FeatureCode = getAttr(Node:'FeatureCode');
SystemInfo.SerialNumber = getAttr(Node:'SerialNumber');
To get partition information, as you will see in the last paragraph of this article, first get the number of partitions:
Then, get the attributes for each partition:
Node = getNode('PartitionInfo/Partition':i-1);
PartitionInfo.Partition.PartitionName(i) = getAttr(Node:'PartitionName');
....
And finally, reclaim all the parser objects and resources:
QxmlDOMNodeList_delete(Node);
QxmlXercesDOMParser_delete(DomParse);
Once you write some reusable procedures that interface the XML parser, you can easily navigate the DOM structure and get children or attributes for a given element, retrieve elements by tag name, get tag name and/or content associated with an element, get element count, etc. with very little programming.
Install the WRKLPAR Utility
You can install and run the utility either on the primary partition or on any or all secondary partitions, but the API will always run only on the primary. You will see how to do it in a moment.
Download the code and move all members into a source file called QLPAR. The LPARSRV service program parses the XML messages returned from the QYHCHCOP API and returns all the information into the structures described in the LPARMG, LPARPA, LPARSY, and LPARSS /copy members. This service program contains some procedures--like getNode, getText, getAttr, and getElementCount--that you can reuse to easily parse other documents. Compile it by running the LPARSRVXX REXX script with PDM Option 16.
Now, if you plan to run the utility in the primary partition only, simply compile the following objects with PDM option 14: DSPLPAR, DSPLPARR, LPAR01, and command WRKLPAR with PGM(LPAR01).
At present, the command allows you to work on any partition, but--especially if you use it from a secondary partition--you can limit the FROMPAR and TOPAR parameters to restricted values. For example, you can disallow moving resources from or to the primary partition.
Before compiling LPAR00, you must have a service tools user ID and password that match the OS/400 user profile and password of the user that is calling this API (make sure the password cases match between the OS/400 user profile and the service tools user ID). The OS/400 profile can be a *SIGNOFF profile. You can find more details in the "Authorities and Locks" paragraph of the QYHCHCOP API documentation and in the "Security Requirements" section of the IBM Scheduling LPAR Resource Moves article.
Open the LPAR00 member; fill in the primary system name, user, and password fields; and compile with PDM option 14.
If you run the utility from a secondary partition, however, you must call the QYHCHCOP API that always runs in the primary. We will use a stored procedure.
Sign on to the primary partition, start an interactive SQL session, and execute this command:
(INout REQUEST CHAR(10000),
INout REQUESTLEN INT,
INout REQUESTTYPE INT,
INOUT RCVVAR CHAR(20000),
INout RCVVARLEN INT,
INOUT BYTESAVAIL INT,
INOUT ERRORCODE CHAR(120))
LANGUAGE PLI
EXTERNAL NAME QYHCHCOP
NOT DETERMINISTIC NO SQL
PARAMETER STYLE GENERAL
Then, sign off. You won't do anything more here.
In the secondary partition, compile all the objects listed above. However, for LPAR00, after you fill in the system name, user, and password needed to access the primary partition, compile with the following additional parameters:
USER(PrimaryUserName) PASSWORD(PrimaryPassword)
SQLPKG(QGPL/*OBJ)
Remember that on the secondary partition, you don't need any SST or SECOFR user because you can run the utility under any profile. Obviously, WRKLPAR its not a command like WRKACTJOB, and it's up to you to allow its usage only to special users.
And Now, Move Your Processors
Again, we assume that you already have a partitioned iSeries and maybe you already have used iSeries Navigator to move resources like processors and storage. For additional information, take a look at the Redbook LPAR Configuration and Management (SG246251), which explains in depth how to use the new V5R1 dynamic resource movements in LPAR and how to use the new GUI interface for LPAR (but unfortunately, it doesn't say anything about using the QYHCHCOP API).
With our WRKLPAR utility, you can move processors and storage and set the minimum and maximum processors allowed. In addition, you can easily add your own code to move your IOP devices, as does the LPAR Toolkit.
Enter WRKLPAR and press F4, the default parameter for FUNCTION in *VIEW. This can be used to monitor the partition details. When you use this function, the QYHCHCOP API is called twice--the first time with the XML message you saw above and a second time with this XML message:
In this example, we are interested in getting all the information for all the partitions, but we can limit the information retrieved with the
We decided to show partition information in a panel group, instead of a common display file. This programming technique is described in Application Display Programming (SC41-5715); it requires some additional effort, but it's worth it. Figure 1 shows what the partition panel looks like.
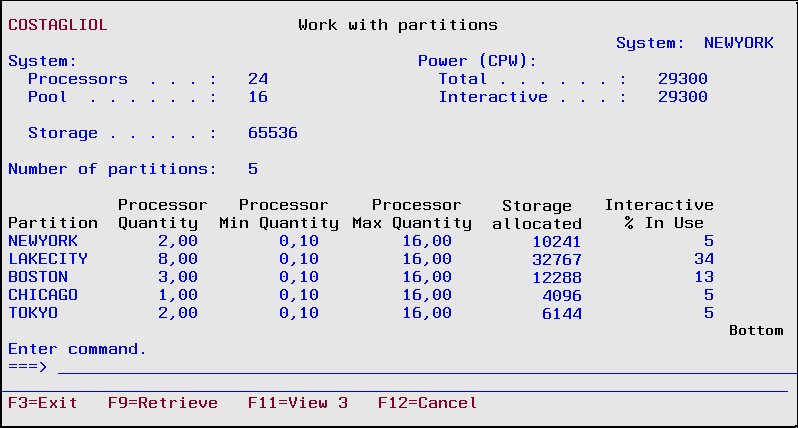
Figure 2 shows an example of how to move half a processor from Boston to Tokyo.
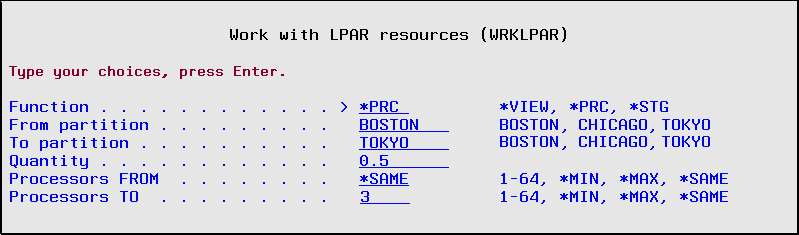
Figure 2: Use the Work with LPAR resources screen to move processors to where you need them.
Do your preliminary validations against the parameters inserted, and start a session with this XML message:
The API returns an XML Session Message:
ActionStatus="Successful"
LPARConfigurationID="zzzzzzzzzzzzzzzzzz">
You have to parse this in order to get the Session Handle that must accompany any further requests to the API:
Now, you are ready to send the ConfigurePartition request for each partition involved in the change:
PartitionID="02"
VirtualProcessors="3"
ProcessingUnits="2.50"
PartitionID="04"
VirtualProcessors="3"
ProcessingUnits="2.50"
Before going on, check the XML message reply for successful completion.
Finally, confirm your request and close the session:
'
'
After the command completes, processor moving is immediate, while storage moving may take more time. So don't be impatient and don't get scared if after running WRKLPAR *VIEW again it seems that nothing has changed yet.
We spent a lot of time learning how to use the QYHCHCOP API and building this utility. We decided to share it with MC Press readers, and we hope that you will like it.
Francesco Candia and Giuseppe Costagliola are programmers in Turin, Italy. You can reach them at




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online