Two problems with the Copy File (CPYF) command are that it does not know what type of business you are in and that it does not know your database. For example, CPYF does not understand that insurance data is centered on policy number, claim number, selling agent, and coverage start and end dates, nor does CPYF know which database files contain these fields.
GroupCopy is a nifty utility that picks up where CPYF leaves off and has some nice features, including the ability to do the following:
• Copy groups of files from one library to another. For example, you might define a file group called POLICY, which consists of all files having a policy number. You can tell GroupCopy to copy the POLICY group, and it will execute the Open Query File (OPNQRYF) and Copy from Query File (CPYFRMQRYF) commands for each file in the group. Files are mapped by field name with a Format Option (FMTOPT) parameter of (*MAP *DROP).
• Select records. You can, for instance, tell GroupCopy to select records pertaining to policy PN005. As it copies files that have a policy number, it will select only this specific policy.
• Add data to target files or replace existing data.
• Convert data to other formats. You can do this as long as the data types are compatible. For example, a date field in an existing production file might be stored in six- digit, zoned decimal numbers in MMDDYY format, while the same field is in eight-digit, packed decimal numbers in YYYYMMDD format in a test library. Because both dates are numeric and have the same name, GroupCopy will run a program that you have written to update the file and reformat the date after CPYFRMQRYF runs. This is especially helpful for Y2K conversions and is one of the reasons GroupCopy was written.
The Objects
GroupCopy was built with ILE modules and programs. Figure 1 lists only the objects you need to understand to use this utility.
GroupCopy is table-driven, and the information it needs to do its job is in physical files. To make GroupCopy work properly, you must put correct data into the files. There
are no file maintenance programs with this utility; however, you can write your own or use a utility like DFU.
The GCLIB file tells GroupCopy which libraries it can use. Limiting GroupCopy to the libraries listed in this file keeps you from accidentally modifying production data. If you specify Y in the GLFROMONLY field, GroupCopy can read only from the library. There is a version field, which you can use to make sure you don’t copy new versions of files to old ones. GroupCopy verifies that the version number of the library being copied is less than or equal to the version number of the library receiving the copied data.
Set up the file groups in file GCGROUPS. GroupCopy was designed to work by field. For example, one group could be called POLICY, and all files with a policy number field would be in this group. There could be other groups for selling agent, claim number, and other fields. This file contains only two fields: the group name and a text description of the group.
The GCKNOWN File
Physical file GCKNOWN (files that are known to GroupCopy) is the heart of the utility. This file has four fields: physical file name, group name, filter name, and filter field name. For now, consider only the first two.
The first field is the name of a physical data file that will be copied from one library to another. The second field is the name of a group to which that data file belongs. Filling in these two fields is enough to tie files to groups.
For example, suppose you set up a group called POLICY in the GCGROUPS file and create 12 records in the GCKNOWN file with a group name of POLICY and the names of 12 files in the file name field. Telling GroupCopy to copy the POLICY group would cause the 12 files to be copied from one library to another.
However, GroupCopy can do more than that. For example, you can tell GroupCopy to copy only the records from each file that pertain to a certain policy or sales agent. This helps when loading test data because it allows you to load only a small amount of data that matches the conditions you want to test. To select records, use GroupCopy’s filtering capability.
To filter data, use the last two fields of GCKNOWN: filter name and field name. Filter name is the name of one of the Groups established in GCGROUPS. Field name is the name of the filter field in that physical file. The sample data in Figure 2 shows that physical file PDATAF is a member of the file group called POLICY. Therefore, when you tell GroupCopy to copy the POLICY group, PDATAF will be copied. If you tell GroupCopy to select records for agent 12, GroupCopy looks for records in GCKNOWN that have a file group of POLICY and a filter group of SELLAGENT. GroupCopy finds such a record and determines that the record selection field is PFSELLA. GroupCopy selects the records in PDATAF that have a value of 12 in the PFSELLA field.
If you use more than one filter, GroupCopy looks for two or more records in the GCKNOWN file. All conditions must be true for a record to be copied.
GroupCopy also allows more than one field in a file to belong to the same group. For example, suppose a file contains both a current policy number field and a previous policy number field. If you create two records in GCKNOWN with the same file name, group name, and filter name but the current policy field in the field name of one record and the previous policy field name in the field name of the other record, GroupCopy will search both fields when selecting records.
If you code the special value *MAP instead of a field name, GroupCopy looks in the GCMAPEXP file to determine how to define the field. GCMAPEXP contains the same four fields found in GCKNOWN plus two more: a name for the mapped field and an expression that calculates the mapped field. This name and expression are what you would code in the MAPFLD parameter of an OPNQRYF command.
GCY2KPGM tells GroupCopy the program (which must be one you have written) to use to reformat the data in a file. This file contains only two fields: a file name and an unqualified program name. GroupCopy scans the library list to find this program at runtime.
The GroupCopy Program
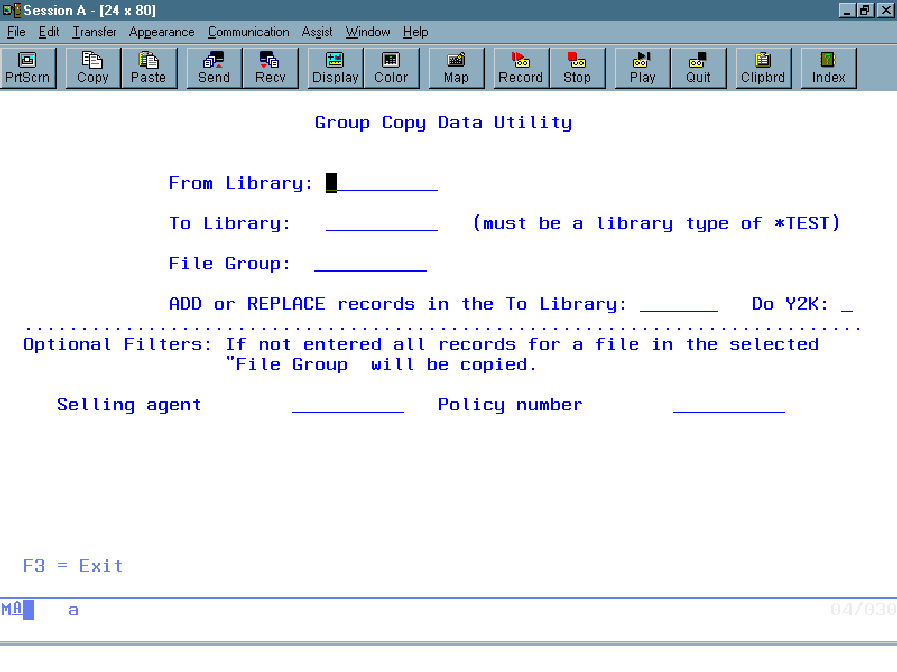
To run this utility, type CALL GROUPCOPY at a command line and press Enter. You’ll see a display like that in Figure 3.
From library is the name of the library containing the existing data. To library is the library to which the data is to be copied. This library must have a type attribute of *TEST.
In the third entry field, specify the name of a group that has been set up in the GCGROUPS file and had files assigned to it in the GCKNOWN file.
In the fourth field, key either REPLACE or ADD to tell GroupCopy whether to clear the receiving file members before it copies the data. This corresponds to the MBROPT parameter of the CPYF and CPYFRMQRYF commands.
The Do Y2K field lets you tell GroupCopy whether to run your data conversion programs.
The bottom half of the display lists the filter groups. To select records, key a field value in a blank. For example, to select records for a certain policy, key the policy number into the blank to the right of the Policy number prompt.
Installation
Source code for this utility is available for download from the Midrange Computing Web site at www.midrangecomputing. com/mc/99/07. The code is available in two formats: ASCII text and a binary save file. Create a library called GroupCopy and load the source code into it. Then, compile GC9997, GC9998, and GC9999 and run them in order. GC9997 builds the error message file, GC9998 builds the files, and GC9999 builds the modules and the programs.
The download also includes source code to build the example database used here and to fill the GroupCopy files to run over the sample libraries GCSAMPLEFR and GCSAMPLETO.
This utility has saved programmers many hours. If you’re converting from one version of software to another or trying to figure out why a program never works correctly for a certain data value, use GroupCopy to quickly load data into a test database.
Object Object type Description
GROUPCOPY Program Driver program
GCGROUPS Physical file Group names
GCKNOWN Physical file Files that are known to GroupCopy
GCLIB Physical file Libraries to which GroupCopy has access
GCMAPEXP Physical file Mapped fields and the expressions that define them
GCY2KPGM Physical file Y2K conversion programs
Figure 1: Access GroupCopy through these interfaces.
File name File Group Filter group Field name
PDATAF POLICY SELLAGENT PFSELLA
PDATAF POLICY POLICY PFPOLN
Figure 2: The GCKNOWN file defines relationships between file groups and filters.
 |




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online