In October, IBM announced the repackaging of its Application Development ToolSet/400 (ADTS) to include Web application development tools. This new set of tools, which has been renamed WebSphere Development Tools for AS/400, includes CODE/400, VisualAge RPG, VisualAge for Java for AS/400, and WebSphere Studio for AS/400. These tools help programmers build server, client/server, and Web applications. Although this new toolset includes enhancements and new capabilities that would justify a price increase, IBM dropped the price by nearly 75 percent to $300. This price reduction allows WebSphere Development Tools for AS/400 to fit into almost any IT budget.
For most AS/400 developers, the first thing they will look at is the CODE/400 editor. This editor provides a GUI editing environment that is much more capable and productive than SEU for maintaining AS/400 applications. The CODE/400 editor allows you to edit, compile, debug, and analyze program source in an integrated development environment (IDE) that augments all of these operations.
In addition to CODE/400, WebSphere Development Tools for AS/400 provides several tools that target client/server and Web-enabled AS/400 application development. The first tool, VisualAge RPG, appeals to RPG programmers interested in developing applications with a GUI interface. The other WebSphere Development Tools for AS/400 tools are VisualAge for Java for AS/400 and WebSphere Studio for AS/400. These provide support for Java and Web application development.
Before releasing WebSphere Development Tools for AS/400, IBM packaged CODE/400 and VisualAge RPG together as Application Development ToolSet Client/Server. Although Application Development ToolSet Client/Server provided a functional AS/400 development environment, the high price and installation problems inhibited adoption. Many shops could not justify the cost or went back to using SEU after becoming frustrated while trying to order, install, and configure this product. IBM addressed these concerns by simplifying the order process, cutting the price, and providing wizards that guide you through the installation.
Get Acquainted with WebSphere Development Tools for AS/400
The four main tools packaged with WebSphere Development Tools for AS/400 are CODE/400, VisualAge RPG, VisualAge for Java for AS/400, and WebSphere Studio for
AS/400. The following is a brief introduction to the Web and GUI development tools included with WebSphere Development Tools for AS/400.
VisualAge RPG is used to update and create client-based RPG applications that have a GUI interface. With the popularity of Java, many believe that VisualAge RPG is not a strategic product. IBM has countered this criticism by adding the ability for VisualAge RPG to generate Java applications. RPG programmers will find the learning curve for VisualAge RPG is less than for other GUI development tools like Java or Visual Basic because a dialect of RPG is used. However, the learning curve is still steep: Although the underlying language is RPG, VisualAge RPG applications use an event-driven model quite different from their ILE or Original Program Model (OPM) counterparts.
VisualAge for Java for AS/400, provides WebSphere Development Tools for AS/400 with a Java development environment. There are several versions of VisualAge for Java; the version that comes with WebSphere Development Tools for AS/400 is the professional one with some additional AS/400 integration support. VisualAge for Java is the most comprehensive Java development environment available, supporting every conceivable Java development task, including designing, developing, cataloging, and debugging of Java applets, applications, and servlets. It is also the most tightly integrated with the underlying Java Development Toolkit (JDK). For these reasons, it also requires extensive resources and takes longer to learn. Support for the latest JDK in VisualAge for Java also tends to lag behind that of some of the other Java development tools.
WebSphere Studio for AS/400 is a Web development tool used to layout, manage, build, and debug Web-based applications. This tool allows you to define and work on Web development projects from a GUI workbench that supports standard templates, wizards, and a content manager. WebSphere Studio for AS/400 tracks Web content and its relationships, while updating and correcting links automatically when publishing changes. WebSphere Studio for AS/400 also integrates with the remote debugger, allowing debugging of Java server pages.
Some Assembly Required
Ordering WebSphere Development Tools for AS/400’s predecessor was a challenge. IBM greatly simplified and improved the ordering process. Now you have several options. You can call your IBM or business partner sales representative and order WebSphere Development Tools for AS/400, or you can go to www.ibm.com/shop/as400. Another Web site that you may want to check out is www.as400.ibm.com/websphere, which contains product descriptions, fixes, and links to other useful WebSphere sites.
After you receive your WebSphere Development Tools for AS/400 CD-ROM, the first step is to review the readme file, which describes the various installation options, service pack information, known problems and workarounds, and documentation corrections. Windows 95 or 98 users in particular will want to review this information. The readme file contained in the root directory points to the actual readme file, which is contained in a zip file. (If it were too easy to install, you would lose the sense of accomplishment.)
If you are using Windows 95 or 98, you will need to make sure that your path statement in your AUTOEXEC.BAT file is short enough to add the directories necessary to support the WebSphere Development Tools for AS/400 programs. This problem is likely to arise on systems that have Client Access installed because Client Access insists on adding several entries to your path. WebSphere Development Tools for AS/400 adds several additional directories to your path, and, if there is not enough room, some components like help or the debugger will not work. If your path is longer than 200 characters, you should remove any unnecessary directories and convert long directory names to their DOS equivalents.
Now that you have reviewed the readme file and verified your path, you are ready to begin the installation process. Insert the CD-ROM into your system and follow the
prompts. When the installation completes, you must reboot your system. The first thing you will see when your system comes back up is a connection test prompt. Enter the name or IP address of your AS/400 and your user ID and password. You can add additional AS/400s using the Connection Manager. CODE/400 uses this information to set up the Connection Manager and check your AS/400 for the requisite PTFs. This test also checks to be sure that your profile is associated with a current library, in which CODE/400 will place some communication files. Developers using CODE/400 should have a unique current library associated with their profile.
To use Java macros or compile Java source programs, you need to have the 1.2 or later JDK installed on your system. You can download the JDK from Sun Microsystems’ Web site at www.javasoft.com. CODE/400 shares the JDK documentation, so if you plan to edit Java programs you should download the documentation with the JDK.
Now Meet CODE/400
The tool that I will be focusing on in this article is CODE/400, which is an IDE supporting AS/400 program development. CODE/400 enhances programmer productivity by streamlining the development process and making common programming tasks more accessible. CODE/400 has three components: the Live Parsing Extendable (LPEX) editor, CODE Designer, and the Distributed Debugger.
The central component of CODE/400 is the LPEX editor. This editor provides many convenient features such as undo/redo, syntax checking, color coding, templates, keyboard shortcuts, and context-sensitive help. Because the editor has a graphical interface, only your monitor size and resolution limit the editing work area that it provides. With a
21” monitor and 1280 x 1024 resolution, I can display over 80 lines of code.
CODE/400 supports all of the programming languages used on the AS/400 including C, COBOL, RPG, CL, REXX, and Java. This support comprises syntax checking, remembering compile options, and color-coding of opcodes. Also, the ability to check for errors by pre-compiling DDS, COBOL, and RPG programs, makes remote access programming much more productive. Precompiling brings in external file definitions, allowing CODE/400 to do more than a simple syntax check.
As the “extensible” part of the LPEX name implies, you can customize and extend the editor to suit your environment. REXX and Java macros provide support for many of the editor’s features. You can modify these macros or write your own to add new features to the editing environment. For example, if you use a change management package that includes its own compile process, you can incorporate that process into the editor.
Another great productivity booster is CODE/400’s context-sensitive help system. Help text is displayed by pressing F1 or by clicking on Help from the menu list at the top of the screen. There is help available for the editor, the AS/400’s programming languages, DDS, and Java. In many cases, the help system will bring up the relevant topic based on where you requested help. If it does not, the help system includes a search engine that will assist you in finding what you are looking for.
Getting on the Road with CODE/400
You are now ready to take CODE/400 for a test drive. Launch the LPEX editor from the Windows Start button by following the path Programs/VisualAge RPG and CODE400/CODE400 Tools/CODE Editor. One of the best ways to familiarize yourself with the CODE/400 editor is to go through the tutorial. To get the tutorial, establish a connection to the Internet and click on Tutorial from the Help drop-down menu in the CODE/400 editor. This will take you to a Web page where you can download the tutorial. For those who do not have an Internet connection or don’t like structured tutorials, I will walk you through some of the more common editing tasks in the following paragraphs.
One of the first things you need to explore in CODE/400 is the help system. The Help drop-down menu provides access to the information relevant to your current task. The
LPEX editor will also bring up context-sensitive help when you press Help in the editor window. Many help screens have a Synchronize button. Pressing this button will display a navigation frame and identify your relative location.
To begin working on a new program or DDS source member, click on Properties from the File drop-down menu and set the source type and member attributes. To try out the editor on an existing local file on your PC, click Open from the File drop-down menu. On the next prompt, expand the
.IRP and .ICB. Before opening a source member on your AS/400, you will need to start the Connection Manager daemon. The Connection Manager handles communications between your PC and any AS/400s you are connected to. In most cases, the installation procedure adds a Windows startup task that starts the Connection Manager. To see if it is running, check the Windows system tray for the Connection Manager icon. The icon is a PC with an arrow pointing to an AS/400. If the Connection Manager is not running, start it by selecting Start/Programs/VisualAge RPG and CODE400/Connection Manager server.
Once you have a connection established with an AS/400, you can begin editing files. Click on Open from the File drop-down window. Click the + next to your system name. This will bring up a list of libraries on your AS/400. If the library you need is not shown, right-click on the system name and click on Filter. Next, change *libl in the displayed prompt to the library containing your source member. Click on the + next to the library name, and click on your source file. Select your source member and click on OK.
As you begin editing a file, you will notice that the LPEX editor behaves a lot like SEU. This is because the default personality is SEU. This personality smoothes the transition to a GUI editor because the function keys and basic line commands are familiar. After you are comfortable using the editor, you should switch to one of the less cumbersome personalities. To change personalities, select Key behavior from the Options drop-down menu. Six personalities are available: LPEX, Brief, EPM, ISPF, SEU, and XEDIT. You can also create your own custom personality. I prefer the LPEX personality.
Now that you have a file opened, a few of the features you should explore are the begin and end matching macro, the indented source view, and cross-reference view. To match begin and end statements, place your cursor on an IF or END statement and press Ctrl+m. This will highlight the IF block. Figure 2 shows the indented view, which is found on the View drop-down menu.
To compile your changes, click on Compile from the Actions drop-down menu. The first time you compile a program, you need to click Prompt. This will bring up the compile dialog shown in Figure 3. To change the global compile defaults, just change compile options shown. To set compile options for a single program or set of programs, select the proper compile command from the list and type over the value shown in Label. Save the changes by clicking on the Add button. Your custom compile attributes will be associated with this new compile option and will not have to be specified again. When you finish, click on Submit to submit the compile to your AS/400.
When your compile completes, CODE sends a message to your PC. When an RPG, COBOL, or DDS compile ends abnormally, you will get a message asking if you want to go to the command shell; click on No. CODE will then bring up an error list window. This window shows all errors, warnings, and informational messages for the compile. To remove the informational messages, which can be overwhelming and have little value, uncheck Informational messages by clicking on the Options drop-down menu followed by Include. Double-clicking on a message in the message list will take you to the
source line associated with the message. If you select a message by clicking on it once and press F1, the message details will be displayed.
You create and update ILE programs and service programs using the Create program and Update program options found on the Actions drop-down menu. This Create program dialog works like the Compile dialog. To specify special compile options for a program, select the compile type from the list shown. Type your program name over the value shown in the Label and type the program library/name in the Program area. Click Options to specify your compile options. Next, click Add to save your compile definition, followed by Submit.
Two other options you should look at are the file compare utility and program verifier. To use the file compare utility, open two members that you would like to compare for differences and click Compare from the Actions drop-down menu. The program verifier goes beyond simple syntax checking to bring file descriptions, /copy members, and data areas into a local cache and ensure that your program will compile. If you work from a remote location, you will certainly want to explore this feature. When objects in your program references have changed, click Prompt from the verifier dialog and click on Use cache and Refresh cache, which are located on the Setting tab.
In order to extend the editor, you need to set a value called the LPATH. This path works like a library list and determines the search order for editor macros. First, set up a directory to contain your custom macros. I put mine in the directory C:CODEMacros. The easiest way to include your directory in the LPATH is to run the extras macro, which is included with CODE and also adds some useful options to your menu bar under an Extras drop-down menu. To run this macro, hit the escape key and type the following command:
extras on c:codemacros
Because this macro is a REXX macro, it is not case sensitive. Java macros are case sensitive. After running the macro, open a file and the Extras drop-down menu should appear. Options on this menu include Host Command, Change Management Tools, and RPG Smart Enter.
Putting CODE Where You Need It
After you have been using CODE for a while, you will want to use it for more than just RPG source files. You can launch CODE in a variety of ways. Rather than use SEU, Notepad, or some other editor because it is the default for the environment you are in, you can add access to CODE.
One of the handiest ways to access CODE is from Windows Explorer. To add this support, create a shortcut pointing to codeedit.exe in the SendTo directory located in the Windows directory on Windows 95/98, and in the WinNTProfiles directory of Windows NT. Now you will be able to send any file to CODE from Windows Explorer by simply right-clicking on the file, selecting Send To and then Code Editor.
Another easy way to access CODE is to start it from PDM. To set up, start PDM and press F16 to work with user options. Next, press F6 and give your option a name like C4. Enter the following in the command, replacing YOURSYSNAME with your AS/400’s system name:
CALL QCODE/EVFCFDBK PARM(‘37’ ‘Y’ ‘YOURSYSNAME’ ‘
/N’)
CODE/400 also comes with an Operations Navigator plug-in. The plug-in allows you to edit, browse, compile, and debug from the file systems tab. This allows you to launch CODE/400 from within the explorer interface of Operations Navigator.
Until Next Time
If you are not currently using a full-featured IDE for your AS/400 development, now is the time to start. IBM combined several of its best development tools into an affordable package. Most programmers will find that CODE/400 greatly enhances their productivity. CODE/400 is only one of the productivity enhancing tools in WebSphere Development Tools for AS/400. The other tools included with WebSphere Development Tools for AS/400 will help you modernize your applications. Look for more articles about these modern tools in subsequent issues of Midrange Computing.
REFERENCES AND RELATED MATERIALS
• DB2 for AS/400 SQL Programming (SC41-5611-03, CD-ROM QB3AQ803)
Figure 1: The Subset function of the Select file—Open for Edit dialog makes it easy to find the file you need to edit.
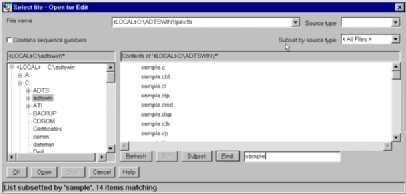
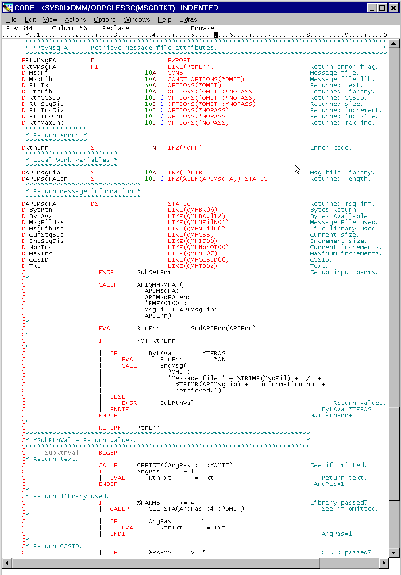
Figure 2: CODE/400 can display RPG code in an indented format.
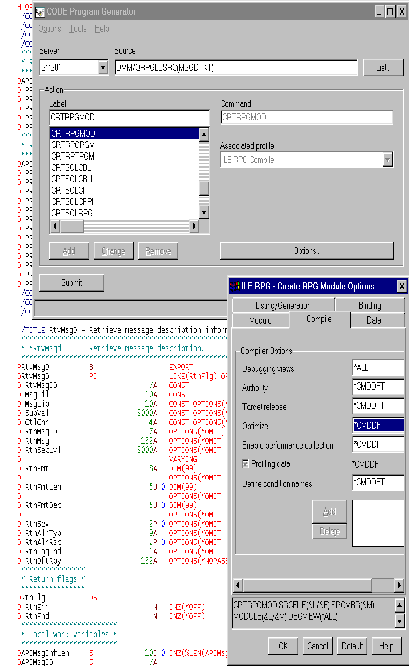
Figure 3: CODE/400 allows you to prompt compilation options.
























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online