In the March/April 1998 issue of the Client Access/400 Expert, I discussed the Client Access/400 Directory Update function. I showed how to use this function to keep a copy of an application system that is installed on a personal computer at the same level as a master copy that is installed in the AS/400’s Integrated File System (IFS).
The Directory Update function is similar to the Application Update function found in older clients, such as Client Access/400 for DOS Extended and Client Access/400 for Windows 3.1. The procedures I discussed in the previous issue for Client Access/400 for Windows 95/NT will apply to these older clients as well. The older clients support an additional facility, called a trigger file. In this article, you’ll see how to use a trigger file to dramatically shorten the time required to determine whether an update needs to be performed. Before getting into that, however, I will review how the Application Update function does its job.
As you should recall, the Application Update function compares a specified directory on the AS/400 system (the source directory) with a specified directory on the PC (the target directory).
Two types of updates can be performed: package-driven updates and file-driven updates. If the application is configured to use a package-driven update, the Application Update function looks for package files in both directories, as shown in Figure 1. A package file has a file extension of PKG. If the same package file exists in both directories and the dates and times match, no update needs to be performed. Unless a file-driven update is also specified, the Application Update function will terminate.
If matching package files in the source and target directories have different dates or times, the Update function will open the source package file and process the statements it
contains. The package file must be present in both the source and target directories for an update to be performed. For each file identified by a MBRF statement, the Application Update function looks in the source and target directories for a file with that name. When the file is missing from the target directory, it will be copied from the source directory. If the file exists in the target directory, its date and time will be compared with the same file in the source directory. If the date and time are identical, no action is performed. When the dates or times differ, the source file will be copied to the target directory, replacing the target file. It doesn’t matter whether the PC version of the file is newer or older. The package file may also contain DLTF statements that cause files to be deleted from the target directory.
When an application is configured to use a file-driven update, the Application Update function will look at every file in the specified target directory. If a file with the same name exists on both systems, as shown in Figure 2, the Update function will look at the time and date when each file was last modified. If the dates or times differ, the AS/400 source file is copied to the PC, replacing the target file. It doesn’t matter whether the PC version of the file is newer or older. Files on the PC that do not correspond to files on the AS/400 are left untouched. Similarly, any files in the source directory but not in the target directory will not be copied to the target.
Trigger Files
Suppose you have set up an application so that it is maintained by the Application Update function using a file-driven update. Also suppose that the application is updated once every two or three months. If your site follows IBM’s recommended procedure, every PC has been configured to invoke the Application Update function whenever Client Access is started. Most of the time, nothing will need to be updated. However, because a file-driven update was specified, the Application Update function will need to compare every file in the target directory with its matching file in the source directory in order to determine if any files do need to be updated. As a result, it can take a considerable time before Client Access is ready to continue with normal processing. Most of this processing can be avoided by changing to a package-driven update. This, however, requires that you create a package file.
If you are using one of the older clients, you can obtain the performance benefits of a package-driven update without having to deal with the package file and its control statements by creating a trigger file. The Application Update function uses the date/time stamp of a trigger file in the same way it uses the date/time stamp of a package file.
Before performing a file-driven or package-driven analysis, the Application Update function first looks for a trigger file named QPTFIDX (see Figure 3). If the trigger file is found in both directories and the files have the same date and time, no further comparison is performed. The Application Update function will exit without examining any other files. It is assumed that all files in the target directory are up to date. If the files have different dates or times, or if the trigger files are missing, the Application Update function continues by performing the normal file-driven or package-driven analysis. During the update process, the Application Update function will automatically copy the source trigger file to the target directory. This, in effect, resets the trigger, because the dates and times of the files will again match.
You may have concluded that there is no reason to use trigger files with a package- driven update, because the Application Update function will end when it determines that the dates and times of matching package files are equal. However, checking the dates and times of package files can take an unacceptable amount of time if there are more than a few of them and if the PC is connected to the AS/400 via a relatively slow link, such as a
asynchronous modem. When trigger files are being used, the Application Update function will never check more than one file on each system as long as the date/time stamp of those files match. For this reason, Client Access uses both a trigger file and package files for its own updates.
Unfortunately, IBM has removed the support for user-defined trigger files that was present in older Client Access clients—such as Client Access/400 for DOS, Client Access/400 for DOS Extended, and the entire PC Support family—from its newer clients. Older clients support two trigger files: A trigger file named QPTFIDX is used by licensed program products, including Client Access itself, and a trigger file named UPDATE.PCS is used by installation-written applications. Client Access/400 for Windows 3.1 does not recognize UPDATE.PCS. If you want to use a trigger file, you must name it QPTFIDX.
The Client Access/400 Trigger File
Before explaining how to define your own trigger file, I will explain how Client Access maintains its trigger file. Figure 4 shows part of a sample QPTFIDX file from the AS/400’s QPWXCWN directory. This file is copied to the PC’s Client Access directory during installation and, if necessary, during subsequent Application Update runs. The first line of the file identifies the installed version, release, and modification level of Client Access. In this example, it is V3R1M1. Next is the product number (5763XC1) and option number (0001).
The next lines identify PTFs that have been applied to this product and option. Each time a Client Access PTF is applied to the AS/400, a line is added to the source trigger file, causing the date and time of the trigger file to be changed. Therefore, the next time the Application Update function is run, the date/time of the source trigger file will not match that of the trigger file in the target directory. The update process will continue and the appropriate Client Access files will be updated.
Creating a Trigger File
If you want to use a trigger file for your own application, use any text editor to create a file named QPTFIDX. The contents of the file are irrelevant, but I recommend that the first line contain the application’s version, release, and modification levels, as in the following example:
V5R3M2 Our Accounting Application
Remaining lines are optional; you can add any number of lines for any purpose of your choosing.
Once you have created the trigger file, copy it to both the source and target directories. When one or more of the files in the source directory is changed, you must update the trigger file, causing its date and time to be changed. As a result, the Application Update function will detect the change and download the updated files, including the revised trigger file.
Bypassing the Trigger File
You may occasionally want the Application Update function to perform a file- driven or package-driven analysis, even when the trigger files in the source and target directories have matching dates and times. You can accomplish this by selecting the Force update option of the Client Access/400 Update window, illustrated in Figure 5. When you select this option, the Application Update function ignores any trigger files and performs a regular file-driven and/or package-driven analysis, as specified.
Get Trigger-happy
Many Client Access/400 for Windows 3.1 users avoid running the Application Update function at startup because of the time needed to compare application directories. As a result, they may find themselves with an old version of an application. By creating a
simple trigger file, you can greatly reduce the time needed to compare directories when no updates need to be performed. By reducing the startup delay, you eliminate the major excuse your users may have for not keeping their applications up to date.
Figure 1: If the application is configured to use a package-driven update, the Application Update function looks for package files in both directories.
Figure 2: If the application is configured to use a file-driven update, the Application Update function looks at every file in the specified target directory.
Figure 3: Before performing a file-driven or package-driven analysis, the Application Update function first looks for a trigger file named QPTFIDX.
V3R1M1 5763XC1 0001
SF08838 QPWXCWN/PCSETUPW.EXE
SF24060 QPWXCWN/LANNSD.DLL
SF24062 QPWXCWN/VNSWUTIL.386
SF24062 QPWXCWN/VD802.386
Figure 4: A typical trigger file would look something like this one.
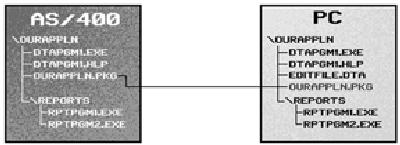
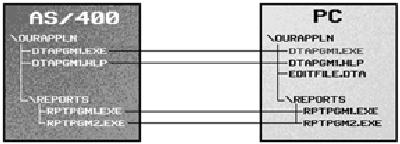
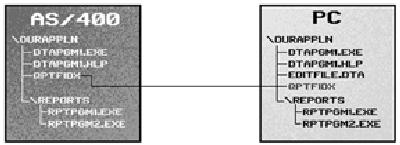
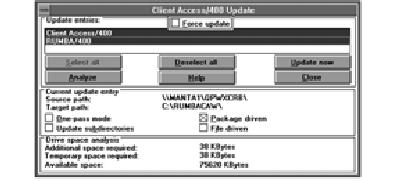
Figure 5: You can force Client Access to do a file- or package-driven update by selecting the Force update option of the Client Access/400 Update window.






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online