Search the IFS for objects by name and type—excluding the file systems or directories you wish—and save the result to a database file.
Have you struggled to find certain objects in the IFS? This command solves the problem.
The main characteristics of the Find Object (FND) command are the following:
- The object name specified in the search can be a regular expression.
- A list of file systems and/or directories can be excluded from the search.
- Symbolic links pointing to directories can be followed or not.
- Multiple paths to the same directory can be searched or not.
- A sort sequence can be specified to determine the order in which matches found are shown and the order in which subdirectories of a directory are searched.
- The search result can be sent to the display, a printer file, or a database file.
- The log generated in the process can be sent along with the result or printed to a separated spool file.
This command can be downloaded for versions 7.1 and 7.3 in English and Spanish. <- Kara, please put the zip files into the two links. Note the “en” for English and “es” for Spanish.
FND Parameters
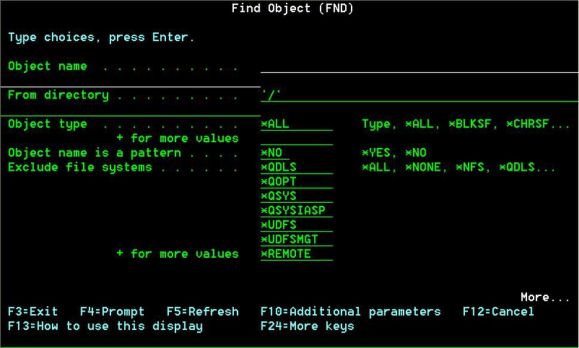
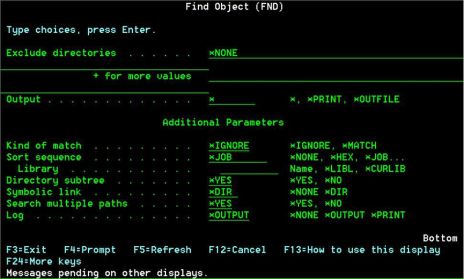
The parameters of the command are shown in Figures 1 and 2:
Figure 1: Parameters of command FND, part 1
Figure 2: Parameters of command FND, part 2
The Search
The search in a directory first examines the objects contained in the directory. Then, if it has been specified to search the subdirectories of directories (parameter SUBTREE), the search continues in these subdirectories in the order specified in the sort sequence (parameter SRTSEQ).
For every directory, the objects that match the name and type specified are listed in the order indicated in the sort sequence.
When a directory can be reached through different paths, the objects contained in this directory might appear several times in the search result. Parameter MLTPATH (search multiple paths) specifies whether all of the paths to a directory are searched—as the UNIX command find does—or only one of them (the first one reached according to the search order).
Regular Expressions
The patterns allowed in the object name are the extended regular expressions (EREs) used in the UNIX commands awk, ed, and grep. These expressions are similar to those used in the SQL predicate REGEXP_LIKE.
Some of the special characters used in these regular expressions are the following:
|
|
|
|
. (dot) |
Any character |
|
? |
The preceding item can appear 0 or 1 times |
|
* |
The preceding item can appear 0 or more times |
|
+ |
The preceding item must appear 1 or more times |
|
^ |
Beginning of line/name |
|
$ |
End of line/name |
|
\ |
Removes the special meaning of a special character |
|
\d |
Digit |
|
\D |
Any character that is not a digit |
|
\s |
Generic space—that is, space, tab, end of line, line feed, or carriage return |
|
\S |
Any character that is not a generic space |
|
| |
Any of the preceding or following items (OR) |
|
() |
Group |
|
[abc] |
Any of the characters enclosed in brackets |
|
[^abc] |
Any character not enclosed in brackets |
|
[a-f] |
Range of characters |
|
[^a-f] |
Any character out of the range of characters |
Regular expressions are managed through the procedures regcomp, regexec, and regfree of service program QC2POSIX. Documentation about these procedures can be found in the IBM i handbook ILE C/C++ Runtime Library Functions.
The prototypes for these procedures are listed in member REGEX of file QSYSINC/H. These prototypes, converted to RPG, can be downloaded along with the command FND.
Object Types
The types of objects specified (parameter OBJTYPE) can be of the file system QSYS.LIB (*FILE, *PGM, etc.) or other file systems. The object types not belonging to QSYS.LIB are the following:
|
|
|
|
*BLKSF |
Block special file |
|
*CHRSF |
Character special file |
|
*DDIR |
Distributed directory |
|
*DIR |
Directory |
|
*DOC |
Document |
|
*DSTMF |
Distributed stream file |
|
*FIFO |
First-in-first-out special file |
|
*FLR |
Folder |
|
*SOCKET |
Socket |
|
*STMF |
Stream file |
|
*SYMLNK |
Symbolic link |
The special values for parameter OBJTPE are the following:
|
|
|
|
*ALL |
Any type |
|
*ALLDIR |
Any directory (*DDIR, *DIR, *FILE, *FLR, *LIB) |
|
*ALLNODIR |
Any type that is not a directory |
File Systems Excluded
Parameter EXCFS allows us to specify the file systems that are going to be excluded from the search. The values used to refer to file systems are the following:
|
|
|
|
*NFS |
Network file systems (NFS). Remote. |
|
*QDLS |
Document library services file system (QDLS) |
|
*QFSVR400 |
File server file systems (QFileSvr.400). Remote. |
|
*QNTC |
NetClient file systems (QNTC). Remote. |
|
*QOPENSYS |
Open Systems file system (QOpenSys) |
|
*QOPT |
Optical file system (QOPT) |
|
*QSYS |
Library file system (QSYS.LIB) |
|
*QSYSIASP |
Independent ASP library file systems |
|
*UDFS |
User-defined file systems |
|
*UDFSMGT |
User-defined management file systems |
|
*REMOTE |
Remote file systems (*NFS, *QFSVR400, *QNTC) |
The default value for this parameter is *NONE, but, if the command is prompted, all of the file systems except root and QOpenSys will be included in the parameter (see Figure 1). This can be useful if you search the UNIX-like file systems most of the time.
However, these values—and any other default value for the other parameters—can be altered by changing the prompt override program of the command. An example of this program is shown next:
PGM PARM(&C_CMD &C_PARM)
/* */
DCL &C_CMD *CHAR 20
DCL &C_PARM *CHAR 202
DCL &EOL *CHAR 1
DCL &EXCFSKWD *CHAR 15
DCL &EXCFSVAL *CHAR 100
DCL &PARMLEN *DEC 3
/* */
MONMSG MSGID(CPF0000) +
EXEC(GOTO CMDLBL(ERRORS))
/* */
CHGVAR &EOL X'00'
CHGVAR &EXCFSKWD '??EXCFS('
CHGVAR &EXCFSVAL +
'*QDLS *QOPT *QSYS *QSYSIASP *UDFS *UDFSMGT *REMOTE)'
CHGVAR &C_PARM (' ' *CAT &EXCFSKWD *TCAT &EXCFSVAL)
/* */
CHGVAR &C_PARM (%trimr(&C_PARM) *CAT &EOL)
CHGVAR &PARMLEN (%scan(&EOL &C_PARM) - 3)
CHGVAR %bin(&C_PARM 1 2) &PARMLEN
/* */
RETURN
ERRORS:
CHGVAR &C_PARM X'0000'
FINAL:
ENDPGM
You can find more information about prompt override programs in the IBM i handbook CL Overview and Concepts.
Output
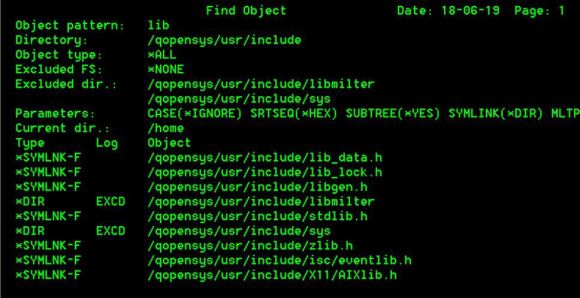
The search result can be sent to the display, a printer file, or a database file. Figure 3 shows an example of output sent to the display or a printer file:
Figure 3: Example of output for command FND
The first seven lines of the result of Figure 3 (from lib_data.h to zlib.h) correspond to the entries of directory /qopensys/usr/include, and the next lines to the entries of its subdirectories.
If the output is directed to a database file, this file is created with the following format:
|
|
|||
|
Field |
Type |
|
Text |
|
OBTYPE |
10A |
Object type |
|
|
OBLOG |
5A |
Log |
|
|
OBPATH |
256A |
VARLEN |
Object path |
Log
Parameter LOG specifies whether a search log is kept or not as well as whether it is sent along with the search result or printed to a separate spool file.
The events that can be included in the log are the following:
|
|
|
|
DUP |
Directory duplicated, that is, already searched |
|
ECHK |
Error in checking object |
|
ECLO |
Error in closing directory |
|
ECMP |
Error in comparing object name |
|
EOPN |
Error in opening directory |
|
EREAD |
Error in reading directory entries |
|
EXCD |
Excluded directory |
|
EXCFS |
Excluded file system |
|
LONGN |
Name too long |
|
LONGP |
Path too long |
|
LOOP |
Searching this directory would cause a loop |
|
NAUT |
Not authorized to object |
|
NDIR |
Object is not a directory |
|
NFND |
Object not found |
The FND command helps you find the objects in the IFS that you’re looking for. Enjoy!






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online