Get to know the runtime array, a handy structure for storing data used during an ILE RPG program’s execution
Editor’s Note: This article is excerpted from chapter 11 of Programming in ILE RPG: Fifth Edition, by Bryan Meyers and Jim Buck.
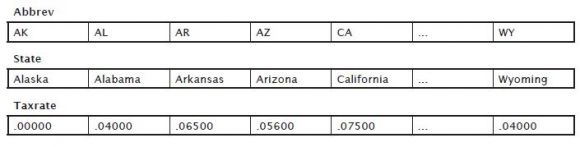
An array is a grouping of data that contains multiple elements, all defined with a common name. The major difference between an RPG array and the tables as we are used to thinking about them is that a typical RPG array represents only one column of data. A table of state sales tax data might be represented in a program by three arrays, as shown in Figure 1:
Figure 1: Example of arrays
A program can refer to an individual element in an array by the element’s ordinal position—for example, State(3) to refer to Arkansas, or it can refer to the entire array by name, such as State.
An array can be a grouping of simple data items (i.e., standalone variables or data structure subfields), or it can be a grouping of identical data structures. Array elements that are simple data items all have the same data type with the same length and (if the elements are numeric) number of decimal positions. In the Abbrev array, the state codes are all two-byte character data. The state names in the State array, however, have different lengths. To use the names in an array, you have to determine the length of the longest state name (South Carolina and North Carolina both have 14 characters) and pad the names of the other states with trailing blanks to make them all 14 characters long.
You define arrays in the declaration section of the program. The required entries are similar to those necessary for other data items. The only restriction in naming the array is that the name generally cannot begin with TAB. Typically, a simple array is defined as a standalone variable, so you use the Dcl-s instruction to declare it. Unlike other standalone variables you have worked with, however, an array stores multiple values, called elements. You must indicate the data type and length of each array element, along with the number of decimal positions (for numeric data). To signify how many elements the array contains, you must include the Dim (Dimension) keyword, specifying the number of table elements within parentheses after the keyword.
Let’s look at how to define the previous three arrays:
Dcl-s Abbrev Char(2) Dim(50);
Dcl-s State Char(14) Dim(50);
Dcl-s Taxrate Zoned(5:5) Dim(50);
These definitions define three arrays—Abbrev, State, and Taxrate—with 50 elements each (as the Dim keyword indicates). Each element of Abbrev is a two-byte character field, each element of State is a 14-byte character field, and each element of Taxrate is a five-digit zoned decimal number with five decimal places. The arrays are standalone variables and are not necessarily related to each other. The resulting runtime arrays are so called because you load then with values during the course of program execution (i.e., at runtime; the values can also change while the program is running). You can initialize the entire array with the Inz keyword, or you can assign initial values to a runtime array by assigning values during the processing, as the following code illustrates:
Taxrate(2) = .04;
Taxrate(3) = .065;
Taxrate(4) = .056;
Taxrate(5) = .075;
...
Taxrate(50) = .04;
If you do not initialize an array, its initial elemental values will be compatible with its data type—blanks for character arrays, zeros for numeric arrays, and so on.
Runtime arrays are useful for storing related values to use in calculations during the course of the program’s execution. For example, it is easier to define and process a single Monthlysales array as a standalone variable in a program instead of 12 individual standalone variables to hold monthly sales totals:
Dcl-s Monthlysales Packed(11:2) Dim(12);
Runtime Arrays and Data Structures
An alternative to declaring arrays as standalone variables is to define them as data structures or data structure subfields:
Dcl-ds Taxes Qualified Inz;
Abbrev Char(2) Dim(50);
State Char(14) Dim(50);
Taxrate Zoned(5:5) Dim(50);
End-ds;
In this example, you define the arrays as part of the Taxes data structure. This type of structure might be useful when two or more arrays are related to each other. In this case, the first element in each array relates closely to the first element in each of the other arrays in the data structure—they all relate to values for Alaska. Because Taxes is a qualified data structure, to refer to the first element in each array, the program names Taxes.Abbrev(1), Taxes.State(1), and Taxes.Taxrate(1):
Taxes.Abbrev(1) = 'AK';
Taxes.State(1) = 'Alaska';
Taxes.Taxrate(1) = 0;
The Taxes data structure can itself be an array data structure, a data structure declared with the Dim keyword:
Dcl-ds Taxes Dim(50) Qualified Inz;
Abbrev Char(2);
State Char(14);
Taxrate Zoned(5:5);
End-ds;
The previous example declares 50 instances of the Taxes data structure, and each instance contains the three subfields. Because you have only one array, Taxes, you refer to the elements differently:
Taxes(1).Abbrev = 'AK';
Taxes(1).State = 'Alaska';
Taxes(1).Taxrate = 0;
or
Taxes(1) = 'AKAlaska 00000';
Array data structures must be runtime arrays and must contain the Qualified keyword. The qualified name must include an index.
The array values can come from a database file. Let’s assume the data is in a file called Statefile. To load the arrays, use the following SQLRPGLE code fragments:
Dcl-c Endoffile '02000';
Dcl-s Habbrev Char(2);
Dcl-s Hstate Char(14);
Dcl-s Htaxrate Zoned(5:5);
Dcl-s X Uns(5);
Dcl-ds Taxes Dim(50) Qualified Inz;
Abbrev Char(2);
State Char(14);
Taxrate Zoned(5:5);
End-ds;
…
Exec SQL Declare Statecursor Cursor For
Select Abbrev, State, Taxrate
From Statefile
Order by Abbrev
For Read Only;
Exec SQL Open Statecursor;
For X = 1 to %Elem(Taxes);
Exec SQL Fetch Statecursor Into :Habbrev, :Hstate, :Htaxrate;
Select;
When Sqlstate = Endoffile;
Leave;
Other;
Taxes(X).Abbrev = Habbrev;
Taxes(X).State = Hstate;
Taxes(X).Taxrate = Htaxrate;
Endsl;
Endfor;
Exec SQL Close Statecursor;
Presumably, the program executes this code once, when the program first starts, perhaps in a subroutine. If the program subsequently changes the array values, it can execute the following code just before it ends to write those changes back to Statefile:
For X = 1 to %Elem(Taxes);
Habbrev = Taxes(X).Abbrev;
Hstate = Taxes(X).State;
Htaxrate = Taxes(X).Taxrate;
Exec SQL Update Statefile
Set State = :Hstate, Taxrate = :Htaxrate
Where Abbrev = :Habbrev;
Endfor;
Both of these examples use the %Elem (Get number of elements) function to return the number of elements in the Taxes array. This type of programming, sometimes called soft-coding, documents the dependency between the number of For loop iterations and the dimension of the Taxes array. Instead of your hard-coding a value of 50, the compiler determines the correct value for the number of For loop repetitions by checking the Dim keyword on the Taxes declaration. If the number of elements in the parent Taxes ever changes, recompiling the program automatically changes the number of child For loop iterations.
You can use a data structure overlay to provide initial values to a runtime array whose data does not come from a file:
Dcl-ds *N;
*N Char(9) Inz('Sunday');
*N Char(9) Inz('Monday');
*N Char(9) Inz('Tuesday');
*N Char(9) Inz('Wednesday');
*N Char(9) Inz('Thursday');
*N Char(9) Inz('Friday');
*N Char(9) Inz('Saturday');
Days Char(9) Dim(7) Pos(1);
End-ds;
This example initializes the first 63 bytes of the unnamed data structure with values that correspond to the names of the days of the week. Notice that you don’t need to name each data structure subfield if you do not use the name elsewhere in the program. The Inz keyword provides the correct initial value for each nine-byte section of the data structure. The Days subfield is an array with seven elements, each nine bytes long. Days starts in position 1 of the data structure (overlaying the previous subfields), so its elemental values are the days of the week.
Runtime Arrays and Externally Described Files
It is common for programmers to want to define some fields within an input record as an array to facilitate coding repetitive operations. Although you cannot directly define fields as array elements within an externally described file, you can use a data structure to let you redefine separately defined input fields into elements of a single runtime array. Remember that an array can be a data structure subfield or an entire data structure, as well as a standalone variable.
Assume you have a file of sales records from all of a company’s sales staff. Each record contains a salesperson’s identification number and that person’s total sales for each month during the past year—12 sales figures in all. Each sales figure is 11 digits with two decimal positions. Because you plan to redefine the sales figures as an array, you have defined Sales as one large character field, as the following DDS specifications show:
*.. 1 ...+... 2 ...+... 3 ...+... 4 ...+... 5 ...+... 6 ...+... 7 ...+... 8
A..........T.Name++++++RLen++TDpB......Functions+++++++++++++++++++++++++++
* Externally described file SalesFile with 12 sales figures defined as
* a single field
A R Salesrec
A Slsnbr 5A Text('Salesperson Number')
A Sales 132A Text('Twelve Months Sales')
You are writing a program that uses file SalesFile as input, and you want to refer to the 12 sales figures within each record as elements of an array. To do this, you must include within the program’s declarations a data structure definition that references the sales input field and redefines it as an array. The following specifications illustrate such a data structure:
Dcl-ds *N;
Sales Char(132);
Salesarray Zoned(11:2) Dim(12) Pos(1);
End-ds;
In this unnamed data structure, the character field Sales (from file SalesFile) occupies the first 132 bytes of the data structure. Next, Salesarray is declared as an array of 12 zoned decimal elements, each with two decimal positions, also occupying bytes 1–132 of the data structure. Salesarray represents a redefinition of the Sales field, dividing the Sales field into 12 array elements, each 11 bytes long.
Another way to externally describe the sales file is to define each month’s sales figure separately, as the following DDS shows:
*.. 1 ...+... 2 ...+... 3 ...+... 4 ...+... 5 ...+... 6 ...+... 7 ...+... 8
A..........T.Name++++++RLen++TDpB......Functions+++++++++++++++++++++++++++
* Externally described file SalesFile
A R Salesrec
A Slsnbr 5A Text('Salesperson Number')
A Sales01 11S 2 Text('January Sales')
A Sales02 11S 2 Text('February Sales')
A Sales03 11S 2 Text('March Sales')
A Sales04 11S 2 Text('April Sales')
A Sales05 11S 2 Text('May Sales')
A Sales06 11S 2 Text('June Sales')
A Sales07 11S 2 Text('July Sales')
A Sales08 11S 2 Text('August Sales')
A Sales09 11S 2 Text('September Sales')
A Sales10 11S 2 Text('October Sales')
A Sales11 11S 2 Text('November Sales')
A Sales12 11S 2 Text('December Sales')
Given the preceding file definition, you must slightly change the data structure to manipulate the sales figures as array elements:
Dcl-ds *N;
Sales01 Zoned(11:2);
Sales02 Zoned(11:2);
Sales03 Zoned(11:2);
Sales04 Zoned(11:2);
Sales05 Zoned(11:2);
Sales06 Zoned(11:2);
Sales07 Zoned(11:2);
Sales08 Zoned(11:2);
Sales09 Zoned(11:2);
Sales10 Zoned(11:2);
Sales11 Zoned(11:2);
Sales12 Zoned(11:2);
Salesarray Zoned(11:2) Dim(12) Pos(1);
End-ds;
This data structure defines each month’s sales amount as a successive 11-byte area within the data structure. Array Salesarray, overlaying the entire 132-byte Sales data structure, redefines the 12 sales figures as its 12 elements.
With either method of defining the input file and its associated data structure, each time you read a record from Salesfile, the 12 sales figures from that record are stored in array Salesarray. When a new input record is read, the sales figures from that record replace the previous contents of the array. Thus, the contents of Salesarray change as the program is running, and that’s why we call Salesarray a runtime array.

























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online