Now, class, does everyone know what a macro is? A macro is a sequence of keyboard and/or mouse actions that can be executed as a single action. These actions and commands can also help simplify some of your everyday functions. For example, you can have a macro automatically sign onto your AS/400 session, run AS/400 commands, and even transfer files. The list goes on and on. To make using macros even easier, you can attach them to a hot spot on your PC5250 session, to specific keys on your keyboard, or to a button on a pop-up keypad, or you can even create a toolbar icon in your Client Access 5250 session.
Macros have been part of Client Access and its 5250 emulation package since that product was first rolled out to the AS/400 community. One interesting thing I discovered on my hike through macro land is that you can create a macro using VBScript. The VBScript engine is automatically installed as part of the Client Access base. Scripts allow for more functional performance by using logic that is not available in standard macros. This article shows you how to use VBScript to create scripts in Client Access PC5250.
What exactly is VBScript? VBScript is a watered-down version of Microsoft’s Visual Basic programming language. It doesn’t have all of the functionality that Visual Basic has but, rather, was created as a lightweight substitution for client control in Web development, namely for the Internet Explorer browser. VBScript is a scripting language that is interpreted, not compiled. This means that a program built with VBScript must be executed in an environment that contains the scripting language’s interpreter and cannot run as a standalone application. Behind the scenes, PC5250 passes a pointer to the text stream in the script, and the VBScript engine parses and filters everything and then interprets the data.
This article assumes that you already have some understanding of VBScript and its capabilities and focuses only on the PC5250 objects that can be used. For more information on using VBScript, visit the Microsoft Windows Script Technologies Web site at msdn.microsoft. com/scripting/default.htm. But before taking a peek at these PC5250 objects, I’ll explain the interface used to enter the statements for the scripts by jumping in and building a script. As you will see, it’s really not that difficult.
VBScript
Step by Step
Follow this step-by-step guide to build a PC5250 VBScript macro:
1. Start a Client Access 5250 emulation session. Please note that this works with both Client Access for Windows and Client Access Express. 2. From the 5250 emulation screen, select the menu option Assist.
3. Click Start Recording Macro.
4. In the Record Macro/Script As window, under File Name, type in signon.mac. For the description, enter auto signon to AS/400. Make sure that VBScript is selected under Record format. Click the OK button. 5. Type in a valid AS/400 user profile. Press Field Exit, if necessary, to get to the Password field. 6. Enter your AS/400 profile password. Press the Enter key.
7. Select menu option Assist again.
8. Select Stop Recording Macro.
9. Click Assist and select Macro/Script Setup.
10. In the Macro/Script Setup window, select signon (name of the script) under the Macro/Script drop-down box. Click the OK button. This macro will now automatically execute every time this PC5250 emulation session starts.
That wasn’t too painful, was it? Now take a look at the VBScript that was automatically built.
How to Customize Your VBScript Macro
Let me review the Customize Macro/Script window. This is the place where you can edit an existing macro/script or create a new one. To access the window, perform the following steps:
1. Click the Assist menu option.
2. Select Macro/Script Setup and, in the Macro/Script Setup window, click the Customize button.
3. In the Customize Macro/Script window, click menu option File/Open and find signon.mac.
4. Click the OK button. The window in Figure 1 (page 68) shows what your window should look like.
If you are familiar with VBScript, the Script Statements text box shouldn’t scare you away. On the other hand, if you’re not familiar with VBScript, this code may cause you some apprehension. Take a moment to study it. You’ll find that, except for some cryptic function names, VBScript is really quite easy to understand. If you find that you are still having problems understanding it, there are a lot of resources available to help you learn. Check the references section at the end of this article for some great resources.
The code shown in the Script Statements text box shows the steps that I recorded earlier for the sign-on script. The macro information was recorded and transformed into VBScript. By looking at the code, you should be able to decipher what is happening with each statement. The Select a Key Action box at the top of this panel allows you to add preexisting macros, keyboard characters, and PC5250 functions to your script. Please note that preexisting macros and keyboard characters cannot be added to your VBScripts, only to macros.
The PC5250 functions are what you really need to understand before you start using them in macros. These functions are the building blocks you use to put the scripts together. To understand which objects are available for you to use, check out Client Access’s Help Section under Script Statements. You now can start to piece together how you want your scripts to function. For the purposes of this discussion, there are two main
objects that you need to review before diving into another example: autECLConnMgr and autECLSession.
Using Objects
AutECLConnMgr is used to manage all personal communications sessions on a given PC. It contains methods relating to the management of sessions, such as starting sessions, stopping sessions, and querying the existing status of current sessions. AutECLSession is an object of autECLConnMgr and is a collection of information for each emulator session. It provides for general emulator-session-related services and contains other important objects in the Emulator Class Library. The Emulator Class Library (ECL) contains the objects provided in Client Access that allow your scripts to “talk” to the 5250 session. These key objects are as follows:
• AutECLPS is used to perform operations in the presentation space (PS), basically the entire window that you see for your 5250 session.
• AutECLOIA retrieves operator information area (OIA) information. These are flags located at the bottom of your screen. Some examples of things that reside in the OIA include Caps Lock, Num Lock, Message Waiting, and Input Inhibited.
• AutECLXfer allows file transfer to and from the PC.
• AutECLWinMetrics allows for manipulation of the current window session. You can access the window title, window size, and window state from this object, to name a few options.
Other key methods in both autECLPS and autECLOIA are the different types of wait conditions. You can wait for something to happen in the OIA or presentation space before continuing on with the script. You can find more information about these objects and their methods and properties in the Personal Communications help section of Client Access.
Once you have built your script in the Customize Macro/Script Window, you just save it. Go to the File menu option and select Save. If this is a new script, give it a name, provide a description, and press OK. Once the macro has been created, you can run it many different ways. You can attach your macro to a specific keyboard function, a 5250 pop-up keypad, a hot spot on your screen, or a mouse action by creating a toolbar item. Back on your 5250 session, you’ll see an Assist menu option. From this drop-down list, you can tie your macros to some of the previously listed functions.
Locating Your Macro Code
All macros are normally stored in the path c:program filesibmclient accessemulatorprivate on your PC and can be opened and edited with any text editor such as Notepad.exe. When you open one of these macro scripts, you’ll find header information at the top that will be similar to the following:
[PCOMM SCRIPT HEADER]
LANGUAGE=VBSCRIPT
DESCRIPTION=Midrange Computing Client Access VBScript demo
[PCOMM SCRIPT SOURCE]
OPTION EXPLICIT
The line [PCOMM SCRIPT HEADER] tells Client Access that this is a VBScript macro and not a PC5250 macro. The second line, LANGUAGE=VBSCRIPT, tells
PC5250 which script engine to load. IBM supports only VBScript at this time. DESCRIPTION gives the user a description of the macro and its function, and PCOMM SCRIPT SOURCE is the end of the header statement that gets passed on, along with the rest of the code, to the script engine. An examination of the actual VBScript code is the best way to see how these objects work with real-life examples.
Sample VBScript Macros
I’ve put together some sample VBScript macro code (Figure 2, page 69) that you can use to learn more about building your own VBScript macros. You can download this code from the MC Web site at www.midrangecomputing.com/mc. MSGBOX and INPUTBOX are built-in functions of the VBScript language and are used throughout the code. They are helpful because they provide a visual aid to the client. Included in the sample code is the following important information for PC5250 objects:
• How to build a list of active sessions—This is done with the autECLConnMgr.autECLConnList objects and properties. Figure 3 presents such a list.
• How to use some of the key objects from the autECLSession—AutECLWinMetrics, autECLOIA, and autECLPS use only a few of the many available properties available to you, but they’re a good example of how to get at the data. A message box produces some results for you based on whichever session was selected.
• How easy it is to start up additional AS/400 sessions—A validation routine runs in the background to verify that it is a valid session and, if so, starts up another 5250 emulation session.
Follow these steps to use the sample script:
1. Download the code from the Web. It can be found at www.midrangecomputing.com/mc. The file that is downloaded is a standard ASCII text file.
2. Open the text file in your favorite text editor.
3. Copy the entire contents of the file to your clipboard.
4. On your 5250 emulation screen, access Assist/Macro/Script Setup/Customize. You are now on the Customize Macro/Script window.
5. Select File/New/VB Script.
6. Now select menu option Edit/Paste. This will paste the script into the Script Statements text area.
7. Select File/Save and name the macro whatever you wish. Add a description and press the OK button to officially save it.
8. Now go back to your 5250 session. From your menu, select Assist/Start Playing Macro/Script. Choose the macro you just created and press OK.
9. Watch your macro in action.
Now It’s Your Turn
Well, there you have it. I’ve given you an overview of how VBScript works with Client Access. Another interesting fact about the VBScript engine is that you can create and use Component Object Model (COM) objects, too. COM is a software architecture that allows applications to “talk” to each other. ADO, or ActiveX Data Object, is an example of a COM object that can be used to manipulate databases on the AS/400 or any other platform in your scripts. Macros provide an easy way to automate routines for your AS/400 session, and, with the VBScript examples I’ve provided here and in the downloadable code, you are well on your way to creating them.
REFERENCES AND RELATED MATERIALS
• Microsoft Windows Script Technologies Web site: msdn.microsoft.com/scripting/default.htm (Select VBScript.)
• Teach Yourself VBScript in 21 Days. Keith Brophy and Tim Koets. Indianapolis, Indiana: Sams Publishing, 1996
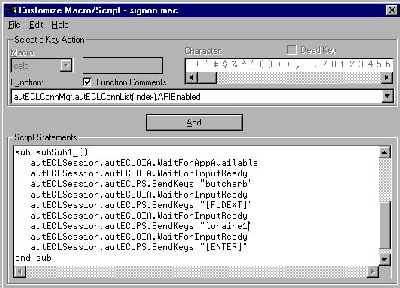
Figure 1: In the Customize Macro/Script window, you can view and edit a script or create a new one.
[PCOMM SCRIPT HEADER]
LANGUAGE=VBSCRIPT
DESCRIPTION=Midrange Computing Client Access VBScript demo
[PCOMM SCRIPT SOURCE]
call startup
'startup sub-routine
sub startup()
dim connection_message 'display message for user
dim connection_selected 'number of session you have selected
dim dft 'default session
dim number_of_connections 'number of AS400 connections
dim result 'answer
dim x 'counter
'run this refresh to get an accurate count of # of session objects
autECLConnMgr.autECLConnList.Refresh
'get number of active AS400 sessions
number_of_connections = autECLConnMgr.autECLConnList.Count
if number_of_connections > 0 then
'build string to show all of the active AS400 sessions on desktop
connection_message = " "
x = 1
do while x <= number_of_connections
if x = 1 then
dft = autECLConnMgr.autECLConnList(1).Name
end if
connection_message = connection_message & cstr(x) & _
") Session Name: " & autECLConnMgr.autECLConnList(x).Name & _
chr(13)
x = x + 1
loop
connection_message = connection_message & chr(13) & "99) Start New Session"
'show input box - get attributes of specific AS400 session or start new session
'this input box is displayed in Figure 2 of the article
result = inputbox(connection_message,"Select a Session for Attributes","1")
If len(result) = 0 then
msgbox("You have pressed the cancel key")
exit sub
end if
if not isnumeric(result) then
msgbox result & " is not a valid Session #."
exit sub
end if
connection_selected = cint(result) 'make sure we are dealing with integer value
if connection_selected = 99 then
call start_session
exit sub
end if
if connection_selected > 0 and connection_selected <= number_of_connections then
call display_attributes(autECLConnMgr.autECLConnList(connection_selected).handle)
else
msgbox "Invalid Session#. You asked to view Session # " & _
cstr(connection_selected) & " and it exceeded highest " & _
"valid session # of " & cstr(number_of_connections)
exit sub
end if
end if
end sub
'this sub routine shows some of the attributes that can be retrieved
sub display_attributes(mysession)
dim attributes
autECLSession.SetConnectionByHandle(mysession)
attributes = "*** WinMetrics Attributes:" & chr(13) & chr(13) & _
"Windows Title:" & autECLSession.autECLWinMetrics.WindowTitle & (chr(13)) & _
"Maximized:" & autECLSession.autECLWinMetrics.Maximized & _
chr(13) & chr(13) & "*** OIA Attributes:" & chr(13) & chr(13) & _
"UpperShift Key:" & autECLSession.autECLOIA.UpperShift & (chr(13)) & _
"CapsLock:" & autECLSession.autECLOIA.CapsLock & chr(13) & chr(13) & _
"*** Presentation Space Attributes:" & chr(13) & chr(13) & _
"Number of Rows: " & autECLSession.autECLPS.NumRows & chr(13) & _
"Number of Columns: " & autECLSession.autECLPS.NumCols & chr(13)
msgbox attributes
end sub
'start_session routine - starts a new session
sub start_session
dim found
dim profile
dim result
dim valid_choices
valid_choices = "CHANDLERDOTYMARINOMCCABEMIZERA"
'this inputbox is depicted in Figure 3 of the article
result = inputbox("Choose AS400 Session to Start: CHANDLER," & _
chr(13) & "DOTY, MARINO, MCCABE or MIZERA" & _
chr(13) & chr(13) & "If left blank, the default will be used!","Start AS/400 Session", _
"MARINO")
if len(result) = 0 then
msgbox "Cancel Pressed - No Session Started"
exit sub
end if
result = ucase(result)
found = instr(valid_choices,result)
if found > 0 then 'a valid AS400 Session Name found
profile = "Profile=" & result
autECLConnMgr.StartConnection(profile)
else
msgbox result & " is an Invalid Session Name!"
end if
end sub
Figure 2: Some sample VBScript will help you learn more about building your own VBScript macros.
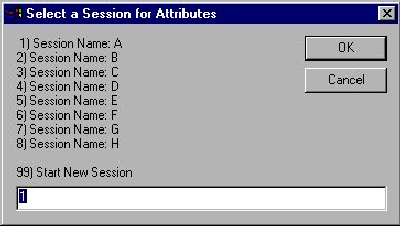
Figure 3: The input box lets you select a specific session or start a new session.





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online