The Holy Grail of email marketing these days is the ability to send HTML content by email. Within the last year, my in-box has received an ever-increasing number of messages formatted in HTML. Now every type of email from spam to order confirmations to email newsletters uses HTML to enhance readability and capture the reader’s attention. No longer does a plain-text email grab the reader’s interest. So, the flashier your email content, the more likely someone will read it.
Sending email from a Web site is another excellent feature. Sites can now send order confirmations or allow users to email a news article to a friend, among other things. Although plain-text email is sufficient in some cases, HTML is the way to go if you want to grab the reader’s attention.
This article provides brief background information about how email has been adapted to send HTML content. I explain how to send a plain-text email from Active Server Pages (ASP) using Collaboration Data Objects (CDO) for Microsoft Windows NT Server, as well as from a product from Dimac called JMail. I also explain how to send HTML- formatted email using CDO for NTS and JMail. And I show you how to use JMail on a Web site to enable users to email an article to a friend. I finish by describing some HTML features of CDO for Windows 2000.
The History of Email
RFC 822, the baseline email architecture from which current email systems evolved, was established in 1982. This standard imposed certain limitations on email messages. Email text, for example, could contain only ASCII characters and could not exceed a certain line length or a certain overall length. Because RFC 822 did not allow for anything but plain text, HTML was not possible.
A new Internet mail standard called Multipurpose Internet Mail Extension, or MIME, was approved in 1992. One of the main goals of MIME was to allow for future expansion of email content by providing a flexible framework on which an email’s content type is specified. (An email client determines how to handle an email message based on its content type.) A second goal of MIME was to allow for backward compatibility with existing email clients that are based on the original RFC 822 specification.
MIME allows an email message to contain the following elements:
• Multiple objects in a single message
• Text with unlimited line length or overall length
• Character sets other than ASCII, allowing non-English language messages
• Binary or application-specific files
• Image, audio, video, and multimedia files
In essence, email can send much more than plain text these days.
Sending Email Using CDO for NTS
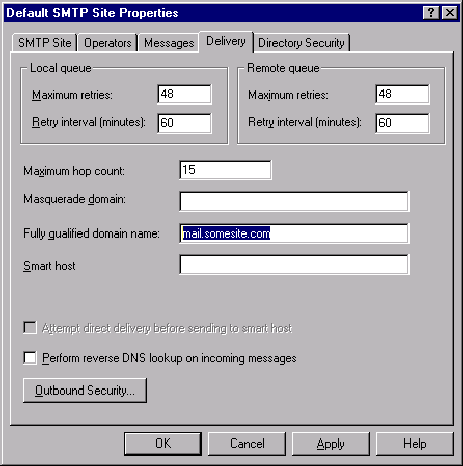
To send an email message from ASP using CDO for NTS, you must first install the Windows NT Server 4.0 Option Pack, available free to registered NT users at www.microsoft.com/NTServer/nts/exec/ overview/WhatNew.asp. During installation of the NT Option Pack, make sure you select SMTP Service. Once installed, open the Internet Service Manager and select your computer name (on the left side of panel), then select the Properties option by right-clicking on Default SMTP Site. Select the Delivery tab (as shown in Figure 1) and enter your email server in the Fully qualified domain name field. Doing so allows CDO for NTS to deliver the messages you are about to create to the specified server.
Now that you have installed the NT Option Pack and configured email delivery options, you are ready to send email from ASP. You can send a message by calling just one method. The Send method (as shown in Figure 2) has all the parameters needed to send a plain-text message. Alternatively, you could set each parameter with separate properties and execute the Send method without parameters.
Unfortunately, sending HTML email using CDO for NTS is not an easy task. As shown in Figure 3, you could concatenate a string value that represents HTML; set the BodyFormatProperty property to cdoBodyFormatHTML, the MailFormat property to cdoMailFormatMime, and the Body property to your concatenated string value; then execute the Send method. As you can see from the simple code example, anything that requires a lot of HTML formatting becomes a maintenance nightmare. You probably already have HTML pages or know how to create new pages with an editor, so why should you have to resort to string concatenation in code? Luckily, there is a much easier way with JMail.
Sending Email Using JMail
Dimac’s JMail is a Component Object Model (COM) that provides a richer feature set for SMTP messaging than CDO for NTS. To send HTML email, you can download and install JMail Version 4.0 from the Dimac Web site (www.dimac.net). The product is free for personal use, but if you plan to use it in an ISP or enterprise environment, you have to purchase it.
After you download and run the setup program, you are ready to go. The setup program installs a PDF file that defines the JMail component in detail. To send a plain-text message with JMail requires a few more lines of code (see Figure 4, page 84) than CDO for NTS; however, you do not need to be running the NT Option Pack’s SMTP service to make it work.
Now the HTML fun begins. JMail allows you to send an HTML message by replacing the Body property with a method called GetMessageBodyFromURL. As shown in Figure 5 (page 84), simply pass in a valid URL, and JMail retrieves the URL’s contents (HTML and graphics) and packages them as the body of your email message. This method replaces any content you had previously set with the Body property. In addition to the GetMessageBodyFromURL method, JMail has a property called HTMLBody, which sets the HTML portion of an email, and a method called AppendHTML, which adds the HTML to the HTMLBody property without replacing it.
MIME encoding allows you to have a corresponding HTMLBody property for a Body property, among other things. Mail format properties are set automatically when calling the GetMessageBodyFromURL method. Sending content as both plain-text and HTML helps to ensure that the recipient will be able to read some version of your message. Some email clients do not support HTML, and some recipients turn off HTML in their email client. So, as always, test various email clients before sending HTML-formatted messages. An email may look great in Outlook Express but not look the same in Eudora.
Since JMail allows you to send HTML messages based on existing Web pages, it is possible to send your Web pages, without modification, by email. When combined with ASP and query string parameters, this technique opens up many possibilities by having the ASP script dynamically render content based on the query string. One popular example of this is sending an Web order confirmation page to the user after she placed an order online. This email could be the exact same page you show the user at the time of order. Simply call JMail’s GetMessageBodyFromURL method, passing a valid URL with an OrderID on the query string, and have the ASP look up all the detailed information and render the HTML.
It is possible to email the user an HTML form and have the transmitted form post information back to a Web site. If you have a searchable site, your email can include a small form that allows users to enter a search string. Once the Submit button is clicked, a Web browser is launched and the search results are displayed.
One of the most common formatting problems when using the JMail component is not having absolute paths to images. JMail requires an absolute image path; otherwise, images are not retrieved. Using relative paths with JMail simply will not work. So, for example, instead of  , you need to enter
, you need to enter
Another problem to watch out for is client-side script. If you have client-side scripts, verify that they work as expected by testing on various email clients. Simple JavaScript such as displaying the user a JavaScript alert() typically works. However, complex document manipulations such as mouseover events have a tendency to fail.
In addition to HTML messaging, JMail has many noteworthy features. If you have Pretty Good Privacy (PGP) installed on your Web server, you can set the PGPProperty to True and your messages will be encrypted. (The help file installed by JMail has detailed information on setting up and configuring a PGP environment on your Web server.)
Another feature of JMail is the ability to do mass mailings, which is a great component for spammers who know how to do a little VBScript. For instance, the JMail.MailMerge object’s BulkMerge method accepts an ADO recordset as an argument. Each record in the recordset is sent in an email, based on a template you define.
Using JMail to Email an Article
Many online news sites allow their readers to email news stories to a friend. Setting this up is a fairly trivial task with JMail. Start by downloading the code for this article from the MC Web site (www.midrangecomputing.com/mc). Once the code is downloaded, copy the article.asp, emailarticle.asp, and mc.gif files to an ASP-capable Web server that has the JMail component installed.
There are three requirements for sending an HTML message from ASP. First, you need a small form for the reader to enter his own email address and that of the recipient, as well as a Submit button. This form is typically placed on the Web page that contains the news article to be emailed.
Second, you need to create an ASP process page that uses JMail to email the Web page. The emailarticle.asp file receives the recipient’s email address, the sender’s email address, and the URL (with HTML content) from the posted form. The ASP process page sets the From property, adds a recipient by using the AddRecipient method, sets the Subject property to a static value, retrieves the HTML content by calling the
GetMessageBodyFromURL method, and executes the Send method. Once the email is sent, the sender is notified, and a link to return to the article is displayed.
Third, you need a generic function that determines what page the Web user is currently viewing. The function GetThisPageURL, found in the article.asp file, accomplishes this task. This function requires no arguments and simply returns a string that holds the absolute base URL of the page running the function. Retrieving the base URL prevents you from having to hard-code each and every page you want to email-enable. You also use the base URL to prefix the IMG SRC property so that images have a fully qualified URL. (Without a fully qualified URL to an image, the email would show blank placeholders for the images.) You then set a hidden form field to the string value returned by the GetThisPageURL function, along with the page name and any query string parameters.
That is all there is to sending an HTML message from ASP. The key pieces of the example should be easy to pull apart and incorporate into your own design.
CDO for Windows 2000
Windows 2000 ships with a much-improved version of CDO that does not require a local SMTP service, making installation simple. This updated version of CDO is not available with other versions of Windows. For anyone in a Windows 2000 environment, this option deserves consideration.
The CreateMHTMLBody method provides similar functionality to JMail’s GetMessageBodyFromURL method. Given a URL, CDO retrieves the HTML assets and sets the appropriate message object properties. In addition, you have the ability to suppress HTML content when retrieving a page. So if you want the images and formatting without the audio files, you can exclude them with this function.
The Microsoft Web site has thorough documentation on CDO for Windows 2000 (http://msdn.microsoft.com/library/default.asp?URL=/ library/psdk/cdosys/cdosysaboutcdoforwindows2000.htm). From that site, you can navigate through various CDO topics by using the hierarchical tree on the left panel.
Email with Pizzazz
This article should provide a good foundation for you to start sending email with a little pizzazz and to help you decide what email components best fit your environment. If Windows NT is your primary environment, the JMail component is the way to go. If, on the other hand, Windows 2000 is your primary environment, CDO for Windows 2000 has some interesting features.
The email content in your in-box will be transformed over the coming years. As companies strive to compete, they will undoubtedly resort to producing content that grabs the reader’s attention. One way the sender can attract readers is by embedding animations and sounds into an HTML message. Imagine having a message show up in your in-box with a repeating audio file that screams, “Buy it!”
REFERENCES AND RELATED MATERIALS
• CDO for Windows 2000 Web site: http://msdn.microsoft.com/library/ default.asp?URL=/library/psdk/cdosys/cdosysaboutcdoforwindows2000.htm
• Dimac Web site: www.dimac.net
• Introduction to CDO for NTS site: http://msdn.microsoft.com/library/ default.asp?URL=/library/psdk/cdo/_denali_cdo_for_nts_library.htm
• MIME Types Web site: www.crosswinds.net/san-marino/~jom/filex/mime.htm
• Windows NT Server 4.0 Option Pack: www.microsoft.com/NTServer/nts/exec/ overview/WhatNew.asp
Figure 1: The SMTP properties page in Internet Service Manager lets you define how email is sent from your Web server.
Dim objNewMail
Set objNewMail = Server.CreateObject(“CDONTS.NewMail”)
objNewMail.Send “
“some subject”,”here is the message body”
Set objNewMail = Nothing
Figure 2: This code shows how simple it is to send an email from an ASP page via CDO.
Dim objNewMail
Set objNewMail = Server.CreateObject(“CDONTS.NewMail”)
objNewMail.BodyFormat = 0
objNewMail.MailFormat = 0
objNewMail.Body = “HTML
Email with CDONTS”
objNewMail.Send “
Set objNewMail = Nothing
Figure 3: This code sends an HTML formatted message via CDO for NTS by encapsulating the entire message in a string.
Dim objNewMail
Set objNewMail = Server.CreateObject("JMail.Message")
with objNewMail
.From= "
.FromName = "John Smith"
.AddRecipient "
.Subject = "Here is an plain text Message."
.Body = "If I had something clever to write, I would enter it here."
.Send ("mail.somesite.com")
End With
Set objNewMail = Nothing
Figure 4: This code sends a plain-text email via JMail.
Dim objNewMail
Set objNewMail = Server.CreateObject(“JMail.Message”)
With objNewMail
.From= “
.FromName = “John Smith”
.AddRecipient “
.Subject = “Here is an plain text Message.”
.GetMessageBodyFromURL(“http://www.yahoo.com”)
.Send (“mail.somesite.com”)
End With
Set objNewMail = Nothing
Figure 5: This code uses the JMail GetMEssageBodyFromURL to simplify sending HTML-formatted emails.


















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online