This is a corporate New Year's resolution you can't afford to break.
The champagne corks, confetti, and party favors have all been swept up and discarded, marking the demise of yet another busy year. Now it's time to refocus and regroup with new personal and professional resolutions. While weight loss and smoking cessation are typical personal goals, security and compliance continue to be top corporate initiatives—and with good reason. The yet-to-be-released 2011 PowerTech "State of IBM i Security" study continues to report inadequate security controls among a rising tide of regulations and security violations.
One thing I hear repeatedly during my travels is that many folks just don't know where or how to begin a security initiative. In one of my COMMON presentations on the habits exhibited by secure organizations, I discuss the need to start by creating a security policy and following that up with an assessment of the current environment. While the IBM i server has always enjoyed an envious reputation for its integrated security controls, a common misconception is that it comes that way from the factory. The reality is that it takes a fair amount of configuration—initial and ongoing—to get there. Far too often, companies start on a project to fix individual issues before they really understand the risks associated with the different vulnerabilities, and they don't have a solid game plan to achieve the defined goals.
So how do you actually get started? PowerTech's newly updated Open Source Security Policy, available as a Microsoft Word document at no charge, is an excellent entry point if you don't currently have a (good) policy. You can use it as is, or you can customize it to your own requirements. Having a policy allows you to track your existing configuration and compare it to the policy to ensure ongoing compliance to a defined standard.
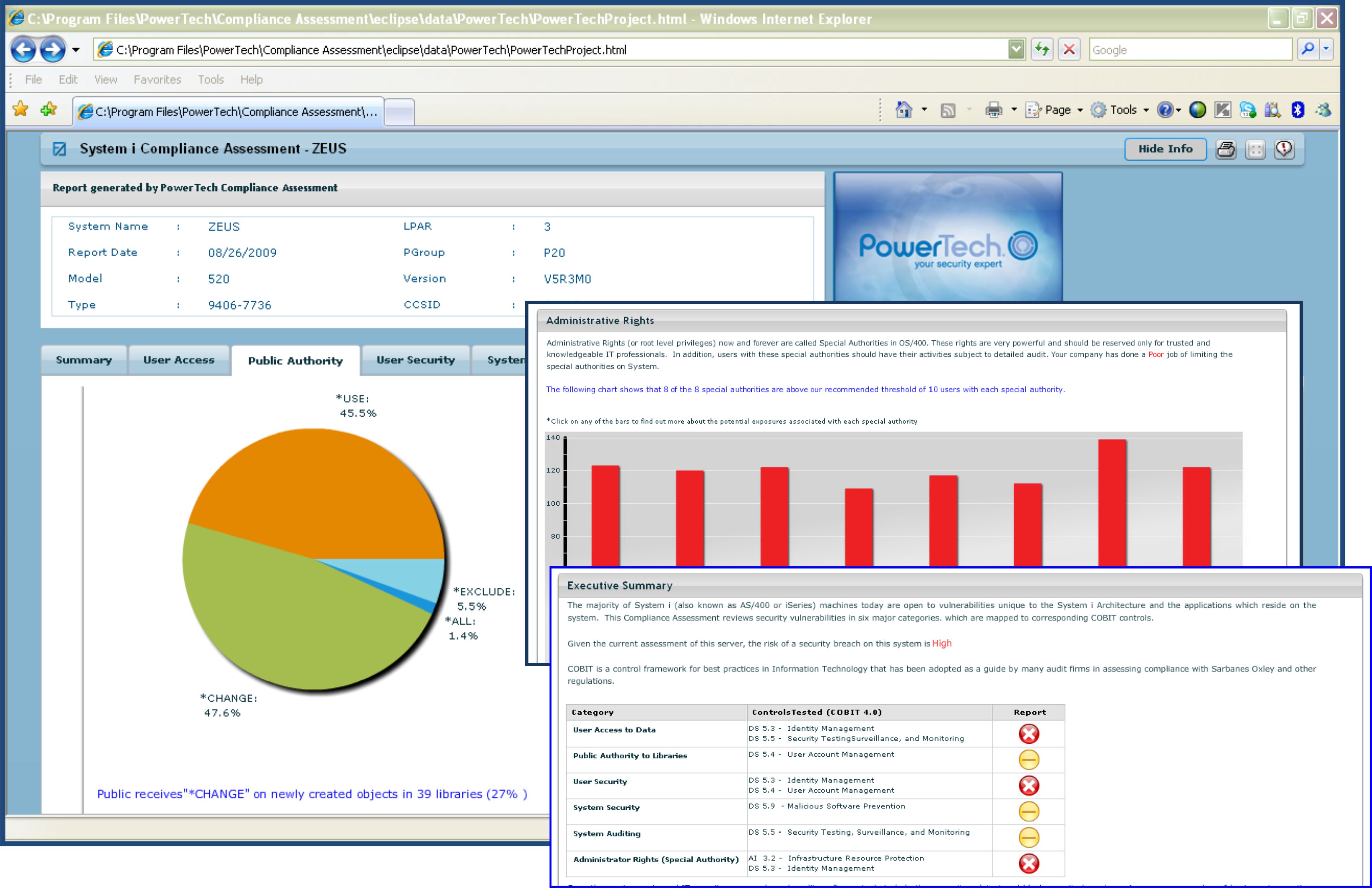
To assess your current standing, I recommend another fantastic PowerTech resource: the Compliance Assessment. The no-cost, no-obligation assessment allows you to evaluate risks as they apply to your entire infrastructure. It's an automated scanning solution that can quickly review a system—typically in just a few minutes—searching for common vulnerabilities. The findings display immediately in a browser-based, interactive application and can be saved or printed for sharing (see Figure 1).
Figure 1: PowerTech's Compliance Assessment provides an overview of the state of security on your system. (Click image to enlarge.)
When you're ready, start by establishing a Security Officer role whose first task is to reconfigure the factory default system values, and then set up auditing for monitoring subsequent (unauthorized) changes. User profile management is another critical area that is frequently overlooked. Review existing profiles for special authorities, along with the amount of access that users have to application objects. Role-based profile maintenance can be very useful. You also should pay attention to the number of (typically transparent) network transactions, such as FTP and ODBC. After you address the basics, also consider additional areas, such as SSL for Telnet connections, and advanced options, such as data encryption and integration into an enterprise security information and event monitoring (SIEM) environment.
Once you have identified the most significant risks for your organization, PowerTech can help with remediation with market-proven solutions that include the leading exit point monitor, powerful user management tools, a configuration and audit journal reporting solution—including event notification in real time—and now database monitoring. Find more information on the PowerTech security solutions in our Security Guide.
Beyond world-class software, PowerTech also has consultants who can do deep-dive security assessments, as well as consulting on the security controls already included in the operating system.
With a proven track record of providing security resources to the IBM Power Systems community, PowerTech is trusted by hundreds of customers to be far more than just another software vendor. Simply put, if you want to become more secure in 2011, make PowerTech your new best friend.
as/400, os/400, iseries, system i, i5/os, ibm i, power systems, 6.1, 7.1, V7,






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online