Make important security events trigger an alarm.
To have any chance of preventing a major security breach, early detection of suspicious activities is critical. Fortunately, IBM i contains comprehensive event auditing functionality that is capable of satisfying most regulatory requirements. Using the Change Security Auditing (CHGSECAUD) command, you can create the security audit journal and the initial journal receiver, as well as configure the two main auditing system values—QAUDCTL and QAUDLVL.
In addition to general system events, you should also consider auditing the activities of powerful users and attempts to access important objects. You can configure these two tasks using the Change User Auditing (CHGUSRAUD) and Change Object Auditing (CHGOBJAUD) commands, respectively. You can find additional information on these commands in the IBM Information Center or in the white paper "Common Sense Security Auditing" available on the PowerTech Web site.
Once the event data is flowing into the security audit journal, the challenge becomes what to do with the audit data. Unfortunately, many IBM i shops do nothing with it, although collecting the data does at least allow forensics to be performed later, should that become necessary.
A commercial audit reporting tool, such as Compliance Monitor from PowerTech, provides a valuable way to quickly review static configuration elements (user profiles, system values, and so on), as well as easily filter and analyze the dynamic events written to the audit journal.
But what if you don't have the time or inclination to perform ongoing forensic analysis? Or what if you're concerned that an important event won't be noticed in a timely enough manner to prevent it from becoming a far bigger and potentially serious issue? Interact, from PowerTech, offers the answer.
Real-Time Event Handling
Interact, a powerful real-time notification agent for IBM i, can process more than 500 system event types. Using Interact, you can escalate IBM i events to interested parties in several ways:
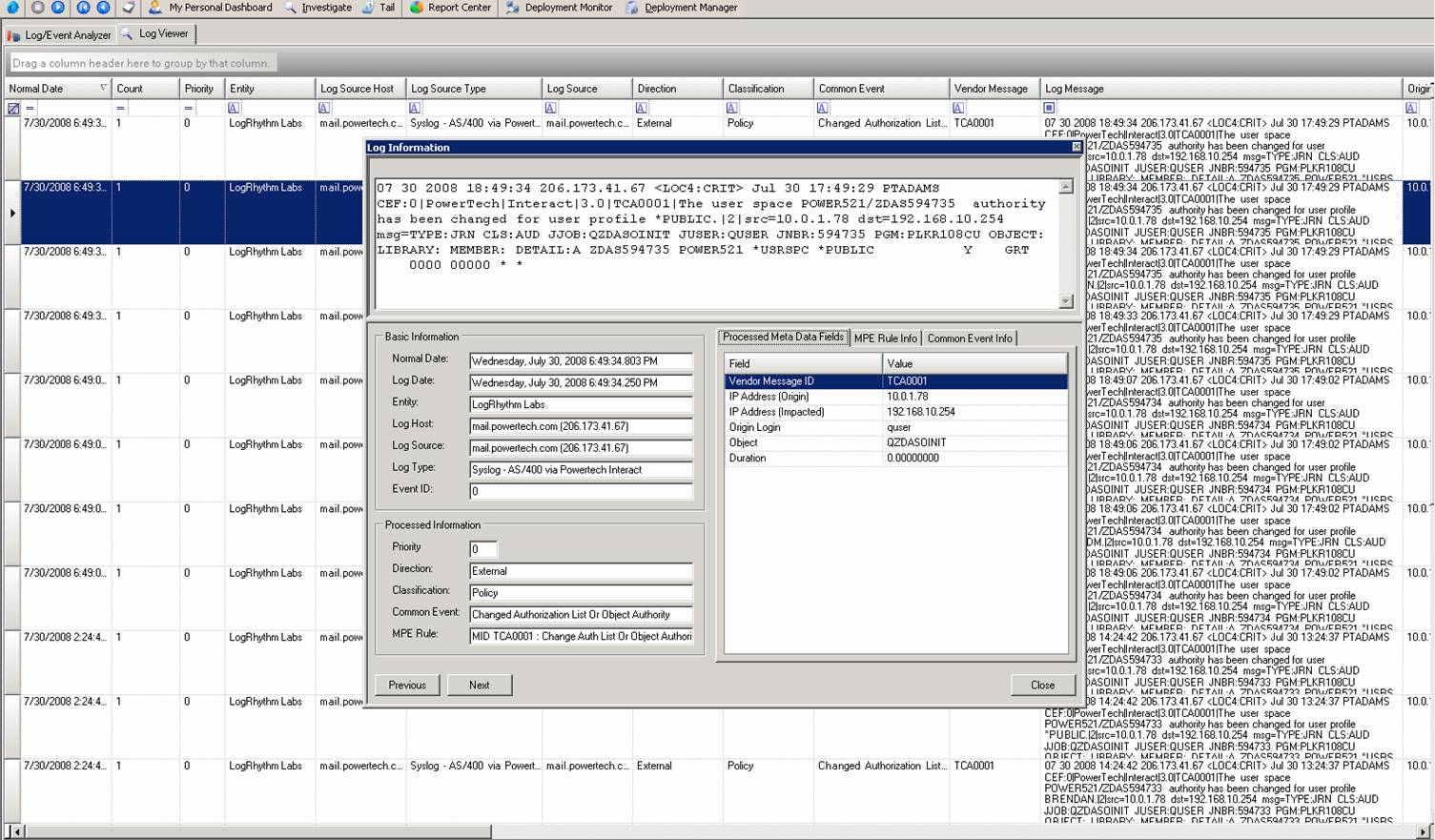
- Syslog server—If you're using a Security Information and Event Management (SIEM) solution, IBM i events can be escalated to it in the industry-standard syslog format (see Figure 1). Enterprise monitoring solutions such as ArcSight, LogRhythm, and Tivoli provide powerful event correlation and categorization functionality for a wide range of servers, now including Power Systems servers running IBM i.
Figure 1: Interact can send IBM i events to your enterprise monitoring solution. (Click image to enlarge.)
- Message queue—Message queue solutions, such as Robot/CONSOLE and Robot/ALERT from Help/Systems and MessengerPlus from Bytware, can escalate messages in numerous ways. This usually involves generating formatted messages that are sent to one or more recipients via email or to a mobile device such as a cell phone or PDA.
- Internet Security Systems—If you're using an IBM ISS monitoring solution, Interact can relay events to the console immediately in an ISS-compatible format.
Not Just IBM i System Events
Interact's benefits extend beyond the escalation of system-generated events. This is important because some types of activities do not generate events. For example, network interfaces such as FTP and ODBC do not include any type of logging capability. While some network functions may cause an auditable event (for example, an object deletion), downloading or uploading a data file is typically transparent—a major compliance violation.
By combining the power of Interact with PowerTech's other security solutions, you gain the important ability to escalate other types of security events as well. By adding PowerTech Network Security, you can detect permitted and failed network access attempts. Imagine being notified proactively that a user logged in to FTP or unsuccessfully attempted to run a remote command through REXEC! Additionally, PowerTech Authority Broker can detect and escalate user profile switches to ensure that the activities are deemed appropriate and necessary.
Sit Back and Relax
If you would like to put Interact (or any PowerTech solution) through its paces, we make it easy with a free 30-day trial. Trial applications are fully functional and can be licensed permanently without reinstalling. We can even help you with the configuration process! After all, if we're going to save you time and effort by bringing the security events to you, we want to make setting up the tools as easy as 1-2-3.






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online