PowerTech's Interact product monitors critical security events in real time.
Let's face it; monitoring security events on IBM i servers probably isn't at the top of anyone's "bucket list." However, it's a critical process that every organization should perform to ensure that unauthorized activities don't occur unnoticed. Typically, there are two main issues with monitoring a system manually: 1) you have to deliberately (and repeatedly) check to see if something has happened, and 2) you are probably looking for the proverbial needle in a haystack of logged events.
PowerTech conducts hundreds of free compliance assessments each year and compiles many of the statistics into a published report. While performing these assessments, we frequently uncover user profiles that have been subjected to multiple invalid sign-on attempts. Ranked #1 in 2011 was a single profile with over 700,000 invalid attempts logged against it! That's amazing, but still not the all-time leader; that dubious honor is bestowed on a user from 2010 whose attempts surpassed the one million mark. What makes these stunning statistics worse is that the security team was oblivious to these activities and therefore clueless about the cause. I challenge whether they'd be more concerned if they discovered that the profile in question was QSECOFR. Sure, the profile might have been disabled after the first few attempts, but perhaps this is the one and only red flag warning of unauthorized activity against the system. Financial giant Citigroup reportedly received a $500,000 fine recently for not acting on red flags about unauthorized insider activities.
PowerTech Compliance Monitor is one of the most popular tools on the market for simplifying complex audit-related tasks, including the forensic analysis of audit journal data. With Version 3, you can schedule hundreds of audit reports in batch and make the results available as .xls and PDF files. The product can even place the completed reports in the IFS or distribute them as email attachments—encrypted, of course!
Security officers and auditors like to know the instant that something unexpected occurs on the system. If you prefer to have your IBM i system escalate critical system events as they happen, then you should look at PowerTech Interact. Installed quickly as a small IBM i agent, Interact is like a security camera for your system. Interact aids your security team by escalating three types of events:
- Critical system messages from QSYSMSG or QSYSOPR
- IBM security audit journal (QAUDJRN) entries
- PowerTech product events from Network Security and Authority Broker
Configuration couldn't be easier. Simply supply the IP address of your syslog or ISS security console and start the monitor job. If you don't maintain a Security Information Event Management (SIEM) environment—such as ISS, ArcSight, LogRhythm, or TriGeo—you can choose to send a notification to a message queue that is monitored by a messaging tool, such as Help/Systems' Robot/CONSOLE and Robot/ALERT or Bytware Messenger.
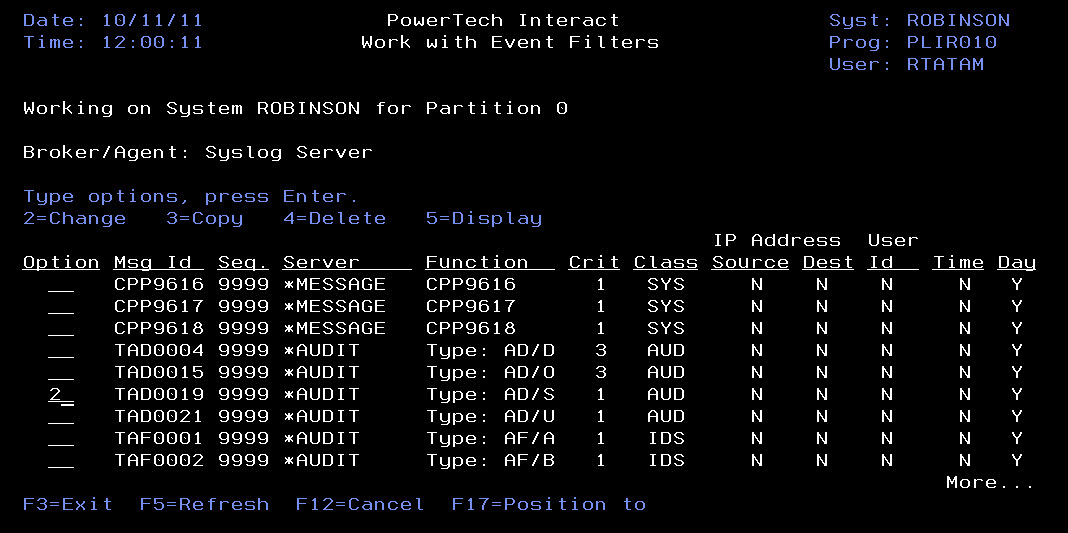
Interact comes with almost 600 event filters predefined (see Figure 1), and you can specify thousands more.
Figure 1: Interact helps you monitor hundreds of events easily. (Click images to enlarge.)
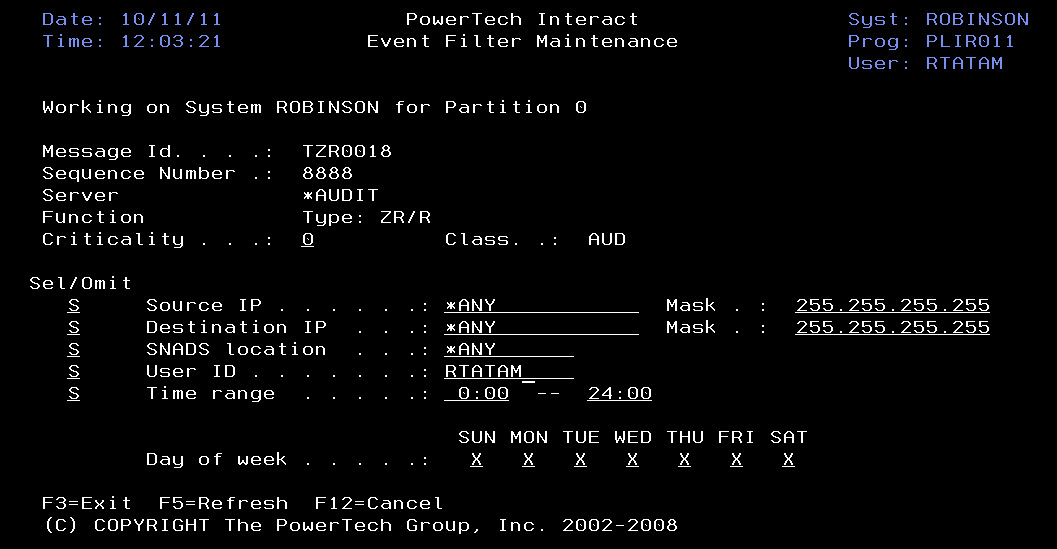
The filters define which events should be escalated and which should be ignored (see Figure 2). They also indicate how critical the event is to help the remote console differentiate between important events and simple notifications.
Figure 2: Interact allows you to specify the criteria used to filter events.
Interact sees events as they occur, formats the data, and then sends it to the remote console. The vast majority of SIEM monitoring solutions can process the events without modification due to the industry-standard syslog format used by Interact. This means you can spend less time configuring and more time monitoring. No more surprises when an audit uncovers system values that are out of compliance or profiles that have been targets of invalid signon attempts. Of course, Interact also detects events generated by other PowerTech products, including users switching to alternate profiles in Authority Broker, and important network events, such as ODBC connections, IFS activities, and FTP file transfers in Network Security.
Click here for more information on Interact. And don't forget to check out the entire line of PowerTech security solutions at www.powertech.com.






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online