Grant varying levels of IBM i security to different interfaces.
Do the majority of your users have access to your critical data? Do you still rely on menu and command-line restrictions for security? Can you monitor network access attempts? Is your security program flexible enough to restrict access to individual objects?
When the "AS/400" first appeared on the market, most developers used application menus and command line restrictions to ensure that data could not be accessed outside an application. There was no Internet, system access was usually from dumb terminals, and though the AS/400 contained an object-based security mechanism, it wasn't often used.
Things changed in the early '90s. IBM enhanced the operating system (OS/400) to support TCP interfaces, such as FTP and ODBC. While the interfaces represented a huge step forward in data openness, they also exposed the lack of object-level security. Now, you could run programs and access data outside of a green-screen display.
Along with these new interfaces, IBM introduced a new security layer, the network exit point. Exit points allow an exit program to be called when someone makes a network access attempt, such as an FTP-based file transfer request. However, even exit programs are not automatically secure. An exit program only does as much (or as little) as its programmer codes it to do.
Exit Point Management Is Key
PowerTech Network Security helps you manage exit points by providing exit programs for common network interfaces. Using Network Security, you set rules that allow or reject requests made through network interfaces. You can control user requests based on the type of request, the user (or group) making the request, and the location where the request originated.
Because the network exit program is called before the transaction is passed to the operating system for authority checking and execution, the exit program can reject transactions that might otherwise be permitted by the operating system. This also allows you to record a powerful user's activities to a secure log, such as the IBM security audit journal (QAUDJRN).
Object Security for a Layered Defense
According to PowerTech's annual State of IBM i Security Study, a well-designed object security scheme is still rare. This is partly because the operating system controls were designed for a single point of access to objects, even though there are now numerous entry points. Thus, providing a user with change access in a green-screen application opens up a huge exposure through ODBC or FTP. Also, excluding a user from one data interface means that the data might not be available for legitimate business purposes though another interface.
In fact, the best security infrastructure is built in layers. If users break through one defense layer (the exit point), they are faced with another layer (object security). Network Security offers an object-level security option that can restrict access to specific objects, libraries, or IFS files.
Profile Switching Adds Flexibility
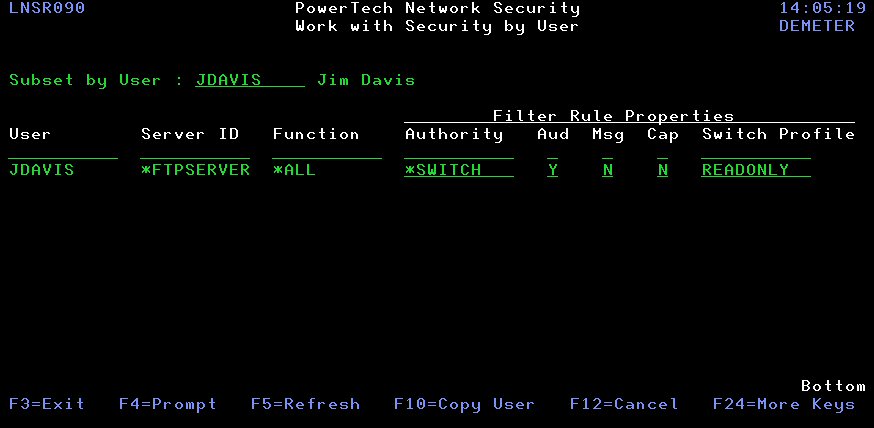
Network Security also includes a powerful "switch profile" feature that allows a transaction to run under a different profile than the profile that initiated it. While typically used to elevate authority, you can apply the same technique to reduce the authority of a user. In the case of the powerful *ALLOBJ users, you can selectively change their requests to run under a lower-level *USE, or even *EXCLUDE, access profile.
Figure 1: Specify a switch profile for a user. (Click image to enlarge.)
You can define profile switching to occur at a very discrete level and be completely transparent to the user. Entire servers, individual server functions, or even specific transactions can be set to run under specific profiles regardless of the requester's authority. Instead of being tied to the single level of security that even a well-implemented object-level security model provides, Network Security offers significant flexibility between interfaces. For example, you can grant a user *EXCLUDE authority through ODBC, *USE to a particular library through FTP, and *CHANGE for a legacy 5250 application.
Controlling the Uncontrollable
People today are still surprised that network interfaces provide such powerful and open access to their application data. Network Security offers a solution that helps you reduce the risk from powerful users with *ALLOBJ authority. You define the level of access you are comfortable with, and Network Security takes care of the details. Call for your free 30-day trial. Learn more about Network Security by clicking here.






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online