PowerTech Compliance Monitor includes centralized compressed storage for audit journal events from multiple partitions.
According to PowerTech's "State of IBM i Security" study, approximately 20 percent of enterprises aren't performing any system, user, or object auditing. When you factor in those that are capturing only a few event types, those that don't do anything with the data once it is captured, and those that are using the event data for high availability purposes rather than security, you end up with a river of events flowing through the cracks, completely unnoticed.
Why Don't People Audit?
So why is it that administrators aren't rushing to take advantage of an operating system with the built-in capability of collecting event information? Auditing is the topic of many PowerTech Webinars, as well as a popular subject for presentations at COMMON and regional user groups. I have observed three main reasons people don't audit:
- Lack of Awareness and Understanding of the Auditing Functions—Ignorance might be bliss in some aspects of life, but in security auditing, it's never a good thing. You can't expect to see anything unless you turn on the function—akin to turning on a flashlight in a dark hallway. Fortunately, the operating system contains a simple command that performs all the heavy lifting (CHGSECAUD), and PowerTech can provide the background knowledge to help you configure it to collect data efficiently.
- Poor Forensics Capability—Without a good forensics solution, the audit data is just a mass of raw data without any business benefit. While IBM i contains a basic extract command, you still need to write queries or programs to make much sense out of it. I would suggest that collecting but not reviewing event data is better than not collecting any data at all—at least the data is there if you need to review it—but it is unquestionably better to have an efficient way to search, filter, and extract entries from the generated audit data.
- Insufficient Storage Space for Overwhelming Volumes of Journal Data—Although disk management is not directly related to the auditing function, anyone who has turned on auditing can testify to what I'm talking about. Large systems have the capability of generating gigabytes of data every day. Not only does this make a forensics solution an absolute must, it also requires careful consideration of the DASD units that house the audited data. Sure, you can (and should) be selective about how and what is audited and you should save the audit data frequently for disaster recovery, but making recent events accessible quickly for reporting, while consuming far less disk space, is usually more desirable and a much better option.
Compliance Monitor Has an Answer
PowerTech, the market leader in security solutions for IBM i, can teach you how to configure the operating system's auditing controls efficiently. You then can use Compliance Monitor, a professional auditing solution, to address the challenges posed by reasons number two and three.
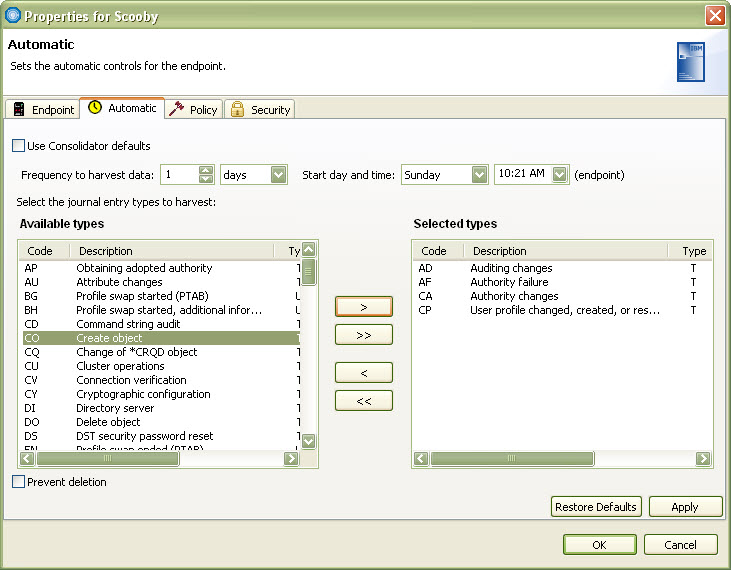
One of the advanced features in Compliance Monitor is the ability to harvest audit journal data. You can choose the data you want from one or more endpoint partitions based on the audit journal type code and then transfer and store the information on a central partition. A built-in scheduler in the GUI reporting console (see Figure 1) allows you to transfer the data on a regular schedule on the days and times that are most convenient for your business.
Figure 1: Compliance Monitor lets you specify the schedule and the event types to harvest and store. (Click image to enlarge.)
The harvested data is stored on the central partition in compressed form. Because of the nature of audit journal data, you often can achieve upward of 90 percent compression. For example, 1 GB of audit data now takes less than 100 MB of disk space! Imagine keeping a full 30 days of audit history online in the same amount of disk space previously consumed by just three days worth of data. When you need the data for forensic reporting, Compliance Monitor automatically handles the decompression for you; you don't have to worry about locating and manually restoring journal receivers from tape or transferring immense files over FTP.
Compliance Monitor can help you search, filter, and extract entries from your audited data. Click here to learn more about Compliance Monitor or request a free Webinar demo.
as/400, os/400, iseries, system i, i5/os, ibm i, power systems, 6.1, 7.1, V7,






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online