Never heard of Application Administration? Don’t be surprised. Although it’s full of function, it’s one of little-known features of IBM i.
Editor's note: This article introduces the white paper "5 Ways to Control Access using Application Administration," free for download at the MC White Paper Center.
Application Administration (or App Admin as it’s commonly called) has been around for a while, but the additional features provided in the latest releases as well as recent Technology Releases make this a feature worth exploring again.
Tip #1 explains how to configure Application Administration access controls. Tip #4 explains the most recently added features, including the ability to control network access (FTP, ODBC, etc.), and Tip #5 explains how you can use App Admin with your own applications.
Application Administration
Application Administration is a function of i Navigator. It allows you to configure who can see certain functions or perform certain tasks. IBM created App Admin because there are times when you need to control access to something, but that something is a function or task and there is no object to restrict access to. For example, when you want to restrict access to a database file, you set *PUBLIC authority to *EXCLUDE, and no one can access the file. But if you want to control who can perform service traces, for example, there is no corresponding object to grant *EXCLUDE authority to. Therefore, App Admin was created to provide a facility for controlling functions.
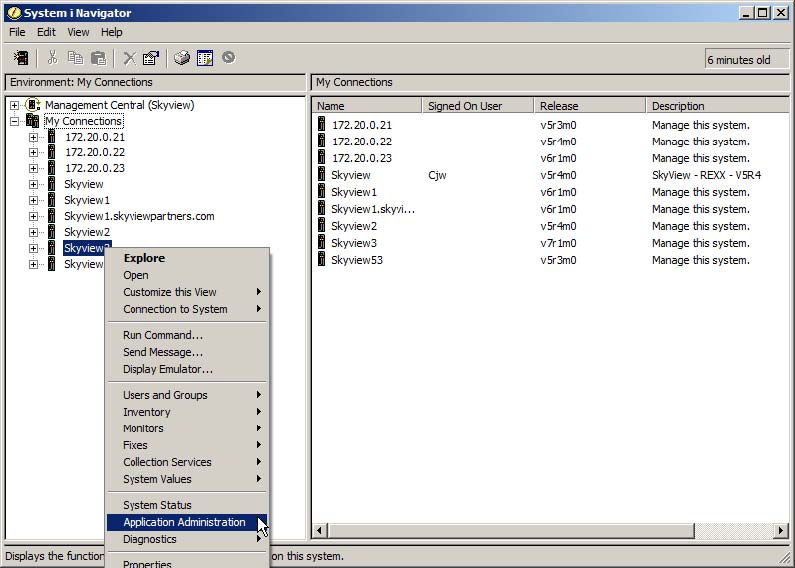
To launch App Admin, right-click on the system name in i Navigator and choose Application Administration. If you haven’t already signed on to the system, you’ll be presented with a sign-on dialog. Note: To configure most aspects of App Admin, you’ll need to sign on with a profile that has at least *SECADM special authority.
#1 – Controlling i Navigator
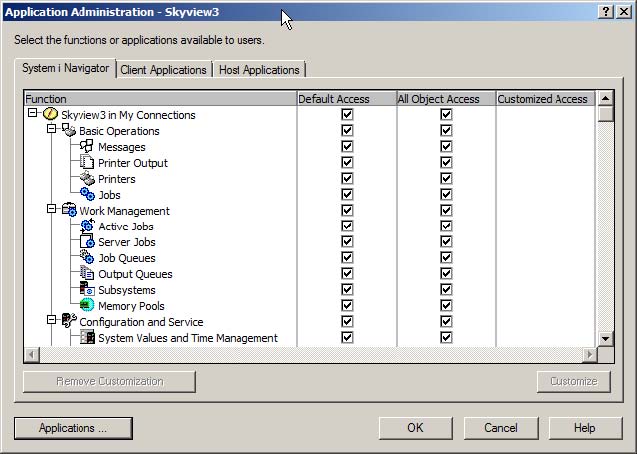
The first tab that’s presented when you launch App Admin allows you to control what parts of System i Navigator users see. For example, some organizations allow all users to manage their spool files (Printed Output) by using i Navigator but don’t want to allow users, especially end users, to see the rest of the functions provided by i Navigator.
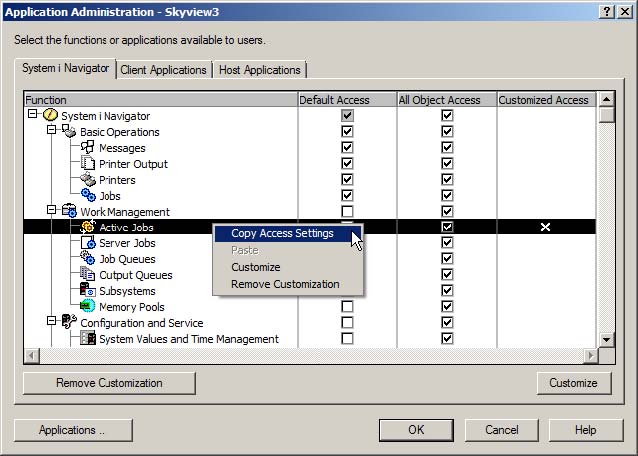
Because all of the boxes under the “Default Access” column are checked, all users are allowed to see all parts of the i Navigator structure. In addition, because all boxes under the “All Object Access” column are checked, all users with *ALLOBJ special authority assigned to their profile are also allowed to see all parts of the structure.
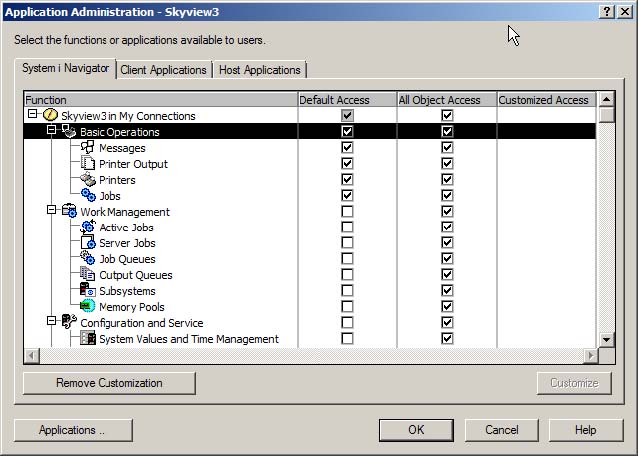
If you only want users with *ALLOBJ to see all parts of iNavigator, leave the “All Object Access” column checked and uncheck the appropriate boxes under the “Default Access” column. With the configuration shown in the next figure, all users can see the Basic Operations of i Navigator but nothing else. *ALLOBJ users can see the entire structure.
Customizing the Access
This all-or-nothing approach may not work for your organization. You may have some users who don’t have *ALLOBJ but need to view and use some i Navigator functions – programmers and operators, for example. To set up this configuration, you’ll need to use the Customize feature. Click on one of the specific features. This will highlight the line and activate the Customize button in the lower right.
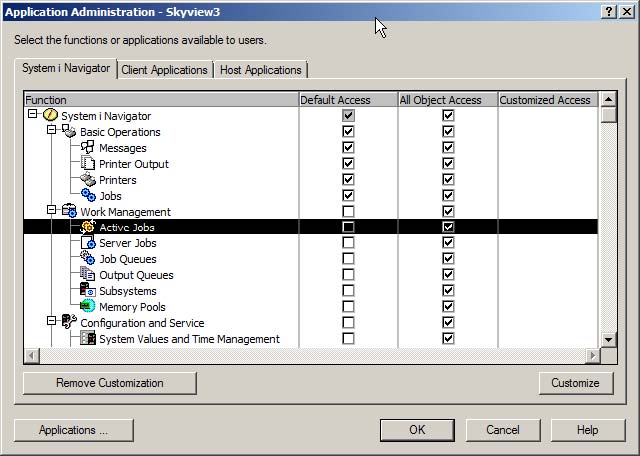
Clicking the Customize button produces the following dialog. Leaving the Default Access box unchecked means that, by default, no users can see this feature. Then, you can open the Users and Groups and select which individuals or groups are allowed to use the feature.
Note: You can do the reverse: allow all users and deny specific users or groups, but that tends to be a maintenance nightmare. I prefer the "deny by default" and allow only approved users or groups.
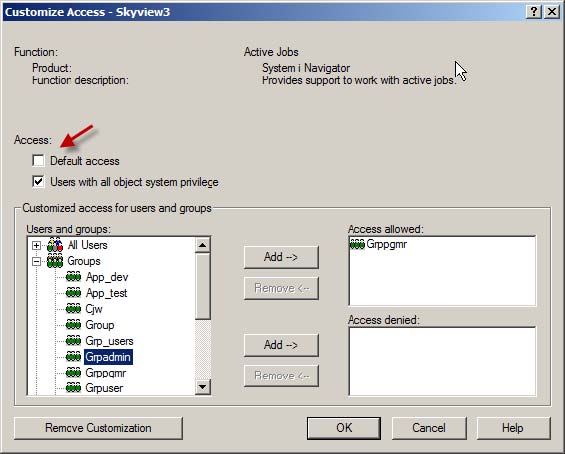
Click OK when you have the list of users or groups that are allowed to use this feature.
When you return to the main dialog, you’ll see that there is an "X" in the Customized column for this feature. To replicate this setting to other features, right-click on the customized line and choose Copy Access Settings. Move your cursor to a single feature or to a feature heading, right-click, and choose Paste to copy the settings to that feature or to the whole category.
Want to Know More?
Download the free white paper "5 Ways to Control Access using Application Administration" at the MC White Paper Center.


























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online