For example, Table A has a foreign key [a key field that identifies data values in other database tables] that points to a field in Table B. Referential integrity prevents the addition of a record in Table B that cannot be linked to Table A. [A record is a complete set of information. In Domino, a record is analogous to a document. Individual rows in a relational database table are considered records. A record contains one or more fields.] Furthermore, the rules may specify the deletion of a record from Table A justifies the deletion of all records in Table B that are linked to the deleted record. This is called a cascading delete. The rules can specify the modification of a linked field in Table A results in the modification of all linked records in Table B. This is called a cascading update. This is only the tip of the proverbial iceberg, but the main point is data is king in an RDBMS.
This is great, but Domino is not a relational database. Referential integrity is not inherently supported in Domino. Referential integrity can, however, be added through the Domino development environment (Domino Designer). I will cover that issue later in the article. A brief comparison of Domino and an RDBMS is first.
Domino Versus RDBMS
The main difference between Domino and RDBMS is data storage. An RDBMS stores data in columns and subsequent rows, so the data is relational. The basic element is a table. Normalization eliminates redundant data. [Normalization is the process of organizing database data in a way that reduces duplication. Data is divided over multiple tables. The goal is the isolation of data, so changes are made only once.] SQL is used to retrieve data from one or more tables. This is called a query. Table rows have a unique identifier called a primary key. [A primary key is a unique value assigned to individual elements in a database table. The document unique ID may be used as a primary key in a Domino database.] The primary key uniquely identifies the row and the row's corresponding values within the system. Foreign key values uniquely identify data in other tables. The world of relational databases is highly formal and structured. Consequently, Domino can be a painful adjustment. The table in Figure 1 provides some comparisons between some common RDBMS elements and the Domino equivalent.
Domino
If you peered inside a Domino database, such as the Domino Directory, you would see a bunch of objects with no inherent organization or relation. This is analogous to a recipe card file. If the contents of the card file are emptied onto a table, it is a bunch of cards with no apparent relation. This is a Domino database. Here is a closer look.
A Domino view is like a relational database table or query. Views present Domino data in a tabular format. Documents may exist in one or more views and, quite possibly, in multiple rows.
A relationship in a Domino database is one or two things: document link or parent/child relationship. Document links allow the placement of a clickable link to one document in another. The parent/child relationship exists between main and response documents. Response documents inherit the unique ID of the parent, but the parent does not contain any reference to the IDs of its children. Each Domino document has a unique ID, and it may function as a primary key.
Another aspect of Domino is the strong support for remote workers through replication. Users may work disconnected from the Domino server. Users create emails, new documents, or change existing documents. The changes are replicated the next time users connect to the server. Replication is a major asset of Domino, but minor data inconsistencies can occasionally arise.
Replication Conflict
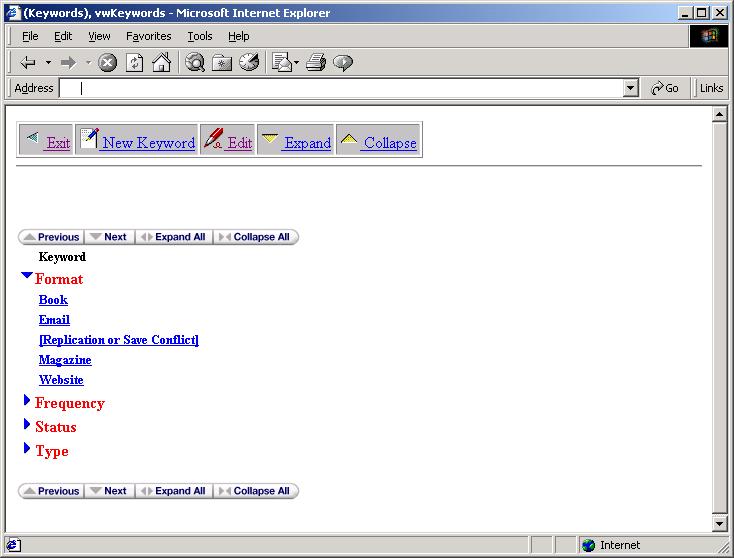
A problem occurs if two users modify the same data. Domino records this type of problem as a replication conflict. Figure 1 shows a replication conflict appearing in a view. The database administrator must manually correct these conflicts by comparing the two documents and copying needed data from the replication conflict entry to its counterpart (just above the conflict in Figure 2). Ultimately, the conflict is deleted.
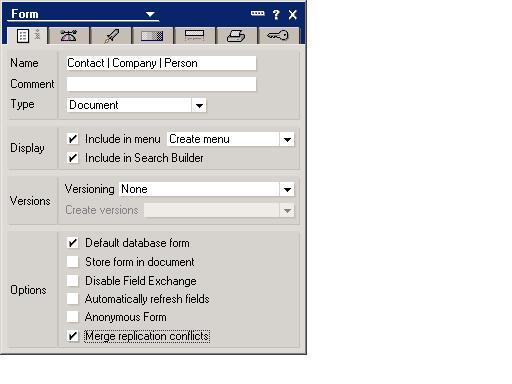
A Domino database can automatically resolve all conflicts at the field level. This option is available during application development. Figure 3 shows the option in the Domino Form properties. Merge Replication Conflicts is selected at the bottom of the figure. If User A changes a field and User B changes another field, the changes are merged. A replication conflict only occurs when two users change the same field, thus database administrator intervention is required. Similar circumstances produce a save conflict.
Save Conflict
A save conflict occurs when two or more users edit and save the same document on the same Domino server. This conflict occurs even if different data fields are altered. The first document saved is the main document with the other appearing as a save conflict. It appears like a replication conflict (see Figure 1). Again, the database administrator resolves the conflict: the administrator manually compares two (or more) documents, consolidates the data, and removes the conflict document.
Replication and save conflicts are two problem areas monitored to guarantee Domino data integrity. In addition, Domino developers may design applications using basic Domino design elements and code to guarantee data consistency and integrity.
Doing the Impossible
Up to this point, I have stressed Domino is not relational, and referential integrity does not exist out-of-the-box. Now, I want to turn your attention to the different aspects of instituting referential integrity in a Domino system. The Domino Designer integrated development environment (IDE) has many tools (such as Java, LotusScript, and formulas) for providing data consistency and integrity.
Data Consistency
Domino documents may be locked with LotusScript code. A flag field on the document is set when a user edits a document. All users accessing this document are locked out until the first user finishes. This institutes changes on a first come basis. The Domino development environment is event driven; events fire at various stages of a database, view, and document's life. The code to lock a document executes when it is opened in edit mode. This is the QueryOpen event (with a check for edit mode). It eliminates the dreaded save conflict when accessing a database on a Domino Server, but does not address integrity.
Referential Integrity
Referential integrity can be setup by way of a relational approach to Domino database design. The normalization process is applied to eliminate redundant data (within the application). Different databases or forms are utilized. Domino provides a variety of formulas (@Formula) for this process. I'll examine three in this section: @Unique, @DBLookup, and @DBColumn.
- @Unique--Used to create a random, unique (to the database) text value. This value is used to mimic the functionality of primary or foreign keys.
- @DBLookup--Retrieves data values from other documents based upon a key value.
- @DBColumn--Retrieves data values from a specific view column.
Note: Notes/Domino documentation provides details of these and related items.
The last two formulas retrieve data from any Domino database accessible by the application and user. This allows the reuse of data across applications. For example, customer data is maintained in one database and used to create a customer order in another.
LotusScript provides more options. LotusScript allows the development of custom code to perform needed tasks. It may retrieve values from other databases or documents or update data in corresponding documents. This function allows deletes or changes to be cascaded. The limits are determined by the ability of the development team. In addition, data outside the Domino environment is easily integrated.
RDBMS Interaction
Domino is easily integrated with enterprise data stores like Oracle or SQL Server by way of Lotus Enterprise Integrator (LEI ) and Domino Enterprise Connection Services (DECS). DECS offers real-time data access and is a standard feature of Domino R5. LEI is more suitable for batch processing and is available for purchase from Lotus as a Domino add-on. These products facilitate the integration of enterprise data and Domino. Therefore, the relational features of the RDBMS are combined with Domino features like workflow, replication, and Web presentation. It is the best of both worlds.
Wrapping Up
Once again, Domino is not and never will be a relational database system. This is paramount to proper design of a Domino-based application. Experienced developers may implement relational features, like record locking (which is making a database record inaccessible to other users. Records are usually locked for editing, so other users can read the information but not alter it.) and referential integrity with formulas or custom code. Also, Domino offers rich enterprise integration features combining existing RDBMS data with the power of Domino. Domino is a powerful tool for building robust applications.
Tony Patton works with various technologies like Java, XML, HTML, and Domino. He is the author of Practical LotusScript and Domino Development with Java, both of which are available from Manning Publications (www.manning.com). You can reach him at
| RDBMS | Domino |
| Table or query | View |
| SQL query | View |
| Primary key | Document unique ID |
| Foreign key | Document unique ID |
| Relationship | Document link; parent/child relationship |
Figure 1: This table contains common RDBMS elements and their Domino equivalents.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online