New functionality in DB2 Web Query version 1.1.2 simplifies JD Edwards reporting.
In my last TechTip, "How'd You Get Your SQL Server Data in My IBM i DB2 Data!?!," I explained how we could integrate Microsoft SQL Server data into the drag-and-drop world of DB2 Web Query reporting. In this TechTip, I will discuss how to integrate data from Oracle's JD Edwards line of applications. The IBM i has consistently been a strong platform for this application. However, because of the data structure, accessing JD Edwards data outside of its application was difficult.
JD Edwards Database Files
JD Edwards stores data in standard DB2 files. So this should be no problem for DB2 Web Query, or any other application, to report against them. So why is accessing JD Edwards data different? It's how the data is stored inside those files. JD Edwards does three major things that makes data access difficult. First, column names are not logical. Rather than being easily understood, they are six-letter and -number abbreviations. The meaning of each column is stored in a separate dictionary file. Second, while decimal data is stored, the decimal point is not. Therefore $45.67 is stored as 4567, and the dictionary file tells the application to put a decimal point two positions in. And finally, dates are not stored as date data types. Instead, they are stored as numeric data in Julian format.
The other piece of setup that can make reporting on these files difficult outside of the JD Edwards application is the use of internal security settings. For example, take an account master file. This file will contain all accounts in the application. However, assume user X is only authorized to access accounts 0000 to 6999. Inside JD Edwards, this level of security can be added. If you approach this from outside of the application, you need to replicate all this information to ensure user X does not have access to accounts 7000 to 9999, for example.
JD Edwards Application Adapter
To help with the above situation, IBM has recently released the JD Edwards Application adapter for DB2 Web Query, version 1.1.2. The JD Edwards Application adapter is available as an additional, chargeable feature as option 7 of the 5733QU2 product for version 1.1.2 only. If you are at a level of DB2 Web Query below 1.1.2, you will need to upgrade in order to use this feature.
The JD Edwards Application adapter supports both World and EnterpriseOne editions of the application from version 7 and higher. While there is support for both World and EnterpriseOne, only one of the two can be used at a time. However, this should not be an issue as most customers run just World or just EnterpriseOne.
Setup
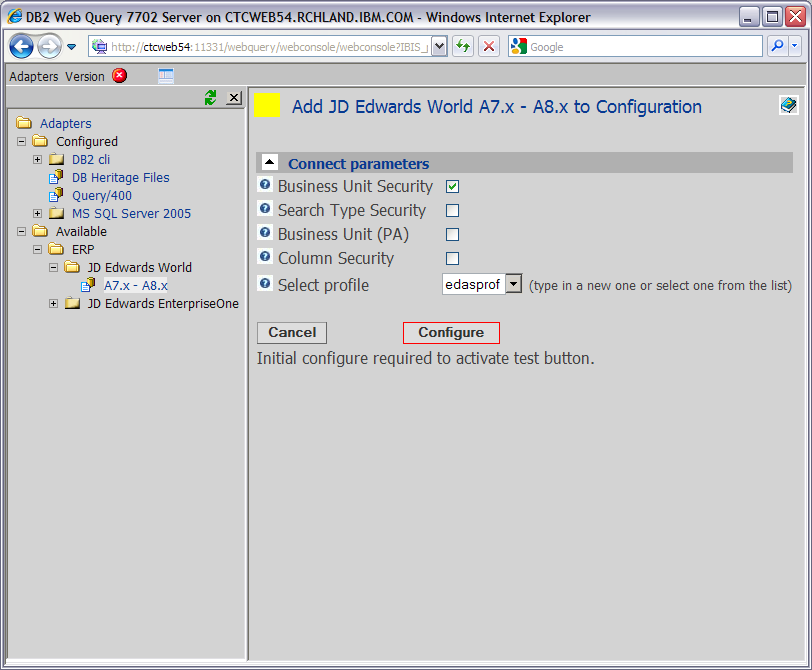
After version 1.1.2 of DB2 Web Query and the JD Edwards Application adapter Option 7 are installed, they need to be set up in the DB2 Web Query Metadata interface. This is done only once. IBM recommends that you create an application in Developer Workbench that holds just these synonyms. Create a new domain as well where this new application is first in the application path. Launch the metadata interface from this domain so that the synonyms will go into this new domain. From the list of available adapters, select the version that matches your installation of JD Edwards. Select which options, if any, you want. These options include the ability to pull in the JD Edwards application-level security mentioned above.
Figure 1: Select the desired properties for the JDE Application Adapter to use. (Click images to enlarge.)
Building Synonyms
Once the adapter is set up, there are three steps to building the synonyms. First, use the standard DB2 CLI *Local adapter to build regular synonyms to the files you want to report on. These synonyms are not very useful right now because of the issues discussed above.
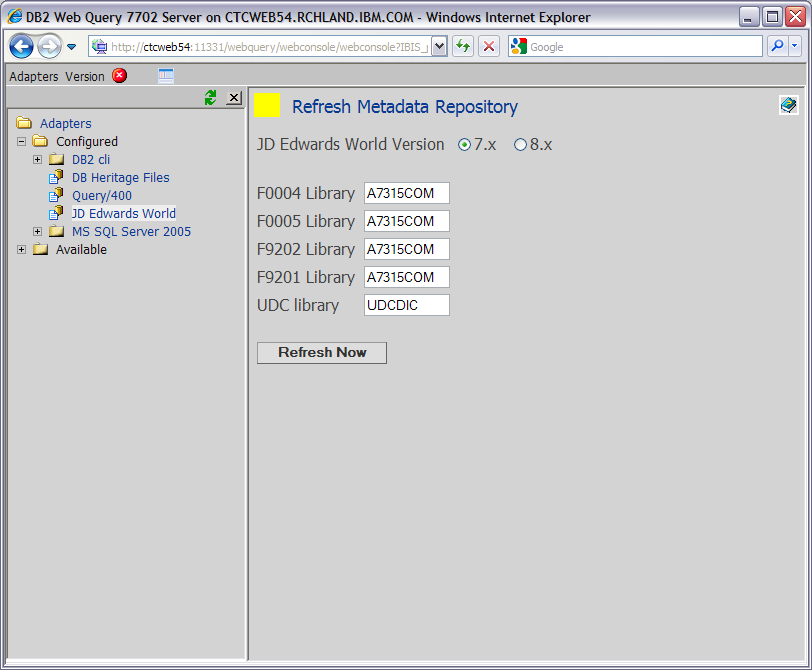
The second step is to build the JD Edwards Adapter Metadata Repository. Right-click on the JD Edwards adapter and select Refresh Metadata Repository. It will ask for the location of various files, depending on the options selected. Provide the library name for each file listed. If you are unsure of the library, you can find it from the command line. As an example, if it asks for file F0004, use WRKOBJ OBJ(*ALL/F0004) OBJTYPE(*FILE) and see what library is returned. Once all file libraries are listed, click Refresh Now.
Figure 2: Provide the correct library names for the list of files provided (your list may vary based on options selected).
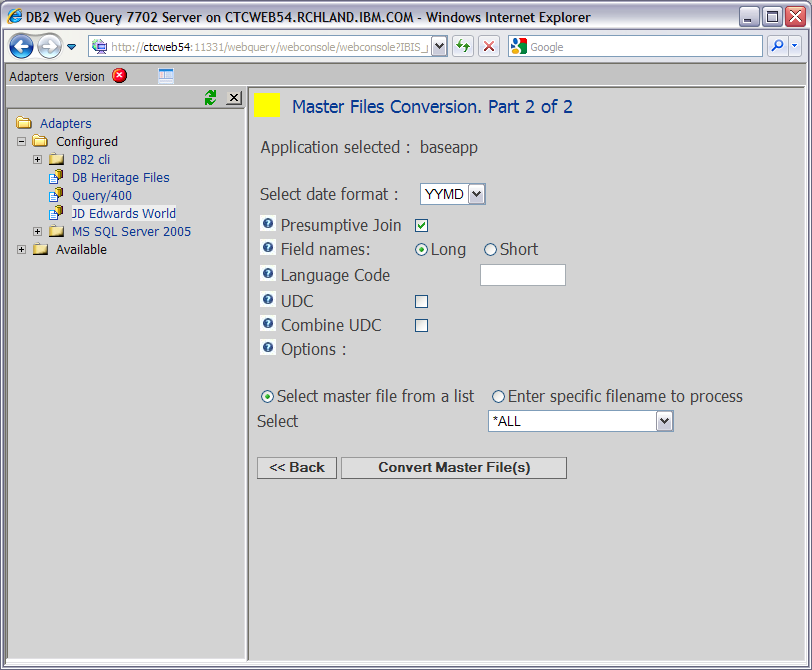
Finally, you need to merge the data from the CLI synonyms with the Metadata Repository. Again, right-click on the JD Edwards adapter and select Convert Master Files. Select the desired date format and the file or files from step 1 that you want converted and click Convert Master File(s). If you created an application for these synonyms, you can just select the All option for that application. This will merge the data together and update the synonyms to have real column names and descriptions, decimal data, and date data types.
Figure 3: Select the date format and field name type to complete the metadata merge.
Once this conversion is complete, you can use these synonyms to build reports or graphs just as you would any other synonym within DB2 Web Query.
Remote File Considerations
The JD Edwards Application adapter can work against database files on a remote system. Remember, the first step above was to use the DB2 CLI Adapter to create synonyms to the files. While most people will use the *LOCAL setting, it is possible to build them against remote files (I will cover more on this in my next TechTip). Simply build the synonyms to the remote system instead of *LOCAL.
The other difference comes when you build the JD Edwards Adapter Metadata Repository. For this step, the files must be on the local system with DB2 Web Query. Based on your version of JD Edwards, it will provide a list of what files need to be moved over to the local system. Once here, complete this step as normal. These files need to be here only for this step and can be moved after the synonyms are built.
More Information
If you would like more details about the JD Edwards Application adapter for DB2 Web Query, please visit the DB2 Web Query site. For pricing and ordering or to upgrade DB2 Web Query, please contact your Business Partner or IBM marketing rep. The best way to learn DB2 Web Query is to follow the tutorial-driven IBM Redbook Getting Started with DB2 Web Query for i.
as/400, os/400, iseries, system i, i5/os, ibm i, power systems, 6.1, 7.1, V7,





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online