(Editor's Note: This article was previously published in MC Showcase. To read it in Spanish, click here.)
Throughout 2005 and even the first months of 2006, the Global Data Synchronization Network (GDSN) has seen many changes. This article includes information about advances in adoption of GDSN during this period and the significant and expected advances in functionality over the next 12 to 24 months. The content in this article assumes a basic knowledge of GDSN and its components (GDSN, source and recipient data pools, GTIN, GLN, etc.). For anyone lacking such knowledge, several good information resources are listed at the end of the article.
Significant Events in 2005
Pete Alvarez, senior director of GS1 GDSN, Inc., reports that the last 12 months have seen big advances in the adoption of GDSN. The number of certified data pools has increased from 10 to 26, covering more than 30 countries; registered Global Trade Identification Numbers (GTINs) have increased from 181,000 to 450,000; and trading partners have grown from 180 to 3,700.
UCCnet and Transora Merger
The UCCnet and Transora data pools officially merged in August 2005, creating 1SYNC, a wholly owned subsidiary of GS1 US. This brings together the largest suppliers and many of the largest U.S. retailers. In total, 1SYNC represents over 50 major demand-side entities (Wal-Mart, Wegmans, SUPERVALU, Southern Wine, Glazer's, Lowes, Associated Wholesale Grocers, etc.) and 4,000 suppliers. 1SYNC's vision is to be "the leader in synchronizing data across the global supply and demand chains."
Ruben Castano, Director, Business Development, for 1SYNC says, "The merger of Transora and UCCnet has been a powerful event for advancing the adoption of data synchronization. The merger has brought together approximately 4,000 suppliers, including most of the world's largest Consumer Products Goods companies, and 50 retailers in one data pool. This helped bring a solid base to the market and allowed us to add 16 new demand-side customers in 2005. The recently approved planned inclusion in price synchronization within the GDSN standard should be an even further boost to the effort."
WWRE and GNX Merger
WWRE and GNX completed their merger in November 2005. Together, they are now known as Agentrics. The press release announcing the merger states that "GNX and WWRE will consolidate operations and rationalize their solution portfolio, to lower the price and the cost of delivering these solutions to encourage their wider adoption across the retail industry." The Agentrics Web site expounds on the organization's mission, offering "the Single Technology Platform for Collaboration: A 'Retail Interface' that connects retailers and manufacturers to their trading partners to more effectively and efficiently share information and manage collaborative work processes."
Carrefour Advances with GDSN
As the world's second largest retailer (more than 7,000 stores under 20 different names in 29 countries) behind only Wal-Mart, Carrefour has tremendous influence. The company recently signed an agreement to receive data pool services from 1SYNC. It appears that it hopes to begin receiving and responding to supplier publications in the 2006-2007 timeframe for some of their countries of operation. Carrefour's participation in GDSN can only be seen as a very positive sign.
Alcohol Beverage Industry Pilot
The world's largest supplier (Diageo) and two of the U.S.'s largest Alcohol Beverage Industry (ABI) distributors (Southern Wine and Glazer's) successfully completed a pilot to prove the viability and validity of GDSN in the ABI three-tier supply chain and enhance the attribute sets of GDSN to properly support the needs of ABI. This project was one of the most successful GDSN advances of 2005. In about three months, Diageo was publishing product information to Southern Wine and Glazer's (sending Catalog Item Notifications, or CINs), both of which were evaluating Diageo's GTIN publications and responding back with Catalog Item Confirmations (CICs). Southern Wine and Glazer's enhanced GTIN information to meet the needs of their customers and in turn published to customers such as Wal-Mart and Albertson's by sending CINs.
GDSN Release Plans for 2006
The GDSN Release Plan Edition 1.0 details six key improvements in functionality to the capabilities of Certified Data Pools and GDSN. Each of the six functionality improvements has one or two "champions," which are companies of significant size and influence with interest in the functional area:
- Multi-Source (Dean Foods)—Standardized process to manage multiple-source suppliers within GDSN and the Global Registry
- New Item Form (Proctor & Gamble UK )—Automate the manual process associated with the introduction of new items
- Item Authorization (Coca-Cola)—A business process that authorizes the sale of specific items within a region, sector, or store
- Price Synchronization (Phase 1: PepsiCo and Ahold)—Develop requirements for synchronizing price via GDSN
- Data Accuracy (Wegmans and Conair)—To develop a standards-based set of tolerances that will be used within the network to ensure accuracy of data with specific product types
- Flexible Fields/Market-Specific Attributes (user champion to be announced)—This project's goal is to develop a method to accelerate market- or industry-specific migration to the GDSN by developing a uniform method to allow non-standard attributes to travel through the network until such a time as they become standard. The project will also include a process to manage and prune these additional attributes as required to maintain network performance integrity. The goal is the standardization of as many attributes as needed to maintain efficient commerce transactions.
Each champion devotes large amounts of time and resources to help drive improvement. The timetable, as of this writing, for these functionality improvements is referred to as the Release Timeline:
- May 2006: standards approved
- June-September 2006: data pools to implement standards
- September-December 2006: certifications to take place
What's Really Important for 2006? Price Sync!
Currently, the GDSN provides an efficient way to synchronize item attributes but not price attributes. Looking back to the foundational study for data synchronization, Action Plan to Accelerate Trading Partner Electronic Partnership by A. T. Kearney, price synchronization is a requirement to achieve higher ROI for e-collaboration.
Based on the findings of this study and internal investigation, many companies have commented that they would find significant benefit in the joint synchronization of both price and item attributes. According to Pete Alvarez, "Price synchronization is the top priority for the GDSN community this calendar year." Looking at the expected breadth of adoption of price sync, it is important to note that not all organizations want share price information Via GDSN. Some participants want to synchronize only item attributes.
To get the price sync ball rolling, the participants in price sync in the Global Standards Management Process (GSMP) have developed a plan to make price sync a reality in GDSN for 2006. The history of and plan for price sync are summarized in the next section.
Price Sync Gets Started in GDSN
Price has been referred to as Relationship Dependent Data (RDD), because price is frequently different between trading partners. RDD has been discussed at great length over the last two years. It started with the RDD work team comprised of representatives from Ahold USA, Cadbury Schweppes Americas Beverages, Coca-Cola, Johnson & Johnson, Nestle, Purina PetCare, PepsiCo, SUPERVALU, and Unilever. This team, which worked from June 2003 through November 2004, developed what is commonly referred to as the Three Document Model:
- Trading Partner Profile (TPP)—Captures agreements between two trading partners, including the specifics of how pricing will be handled
- Condition Document—Governs how components of price will be reflected on an invoice
- Monetary Document—Lists details of the monetary values of pricing components of a single GTIN or all GTINs associated with a TPP
To help advance RDD to a real functioning piece of the GDSN, in February 2005, the GDSN RDD Industry Requirements Team (GDSN RDD IRT) was formed with the following objectives:
- Develop the criteria for implementing price synchronization within the GDSN, including determining how the information will be passed through the network and how the data pools will be involved
- Develop and conduct a pilot test
- Prepare guidelines for implementing price synchronization within the GDSN
The original action plan of the GDSN RDD IRT called for four objectives to be met:
- Make XML schemas available for use by end of Q1 2005
- Design and conduct pilot test by summer 2005
- Complete implementation guidelines by December 2005
- Make RDD price synchronization via GDSN available to all GDSN members at the beginning of 2006
Although the team has worked very hard, these deadlines were missed. At this time, it appears another solution is likely to be adopted.
Single Price Message
At the November 2005 Price Sync meetings in Atlanta, conducted by GSMP, a competing model to the Three Document Model was presented, called the Single Price Message. This model arose largely out of the success that GS1 Australia has had with combined item and price synchronization over the last four or five years. GS1 Australia and Australia's leading retailer (Coles Myer Ltd) presented the case at the November meetings, and it was further discussed at price sync meetings in New York in mid-January and in Dallas in early February 2006. As of the close of the Dallas meeting, it appears that price sync will occur within GDSN using the Single Price Message model.
Here's a summary of the Single Price Message background and details:
- In operation in Australian grocery sector for the past 4-5 years
- Significant momentum achieved in the last 1-2 years, following stronger retailer mandates
- Data model includes item (200+) and price (100+) attributes sent as a single message
- Data model replicates attributes contained on the paper-based Universal Buying Forms (UBFs) and Universal Price Change Forms
- Promotional pricing and promotional allowances are currently considered out of scope
According to Tom Heist, Global Standards Director, GS1 GSMP, price synchronization within GDSN will be complete by the end of the second quarter of 2007, as shown in Figure 1:
Figure 1: The 2006-2007 schedule includes price synchronization and its corresponding certification schedule within GDSN. (Click images to enlarge.)
(Author's note: Information presented in this article on the status of price synchronization in GDSN is current as of its submission for publication in early February 2006. The key stakeholders of price sync are working to ensure a model that accomplishes the goal of meeting the price sync global business requirements. The current model has not yet achieved this goal. Further discussion is likely to occur, including, but not limited to the technical definition of the model. In this author's opinion, this discussion could significantly impact the final outcome and timing of the model for price synchronization.)
Worth the Wait
2005 has been an event-filled year for data synchronization and the GS1 GDSN. Several key organizations involved with the effort have merged. The number of certified data pools and countries served by certified data pools has increased dramatically, as have the number of GTINs registered in the GDSN and the number of demand-side participants (retailers and wholesale distributors).
New industries have started actively working with GDSN. Current industry participation includes CPG, Grocery, Hardlines, Entertainment, Alcohol Beverage, Office Supply, Direct Store Delivery (DSD), Health, Beauty, and OTC Pharmaceutical (CVS, Walgreens, etc.). Countries in Europe, Latin America, and AustralAsia have made significant efforts to advance data synchronization.
The spread of GDS may have cost more and taken longer than early participants hoped for, but what major movement hasn't (computer usage, EDI, the Internet)? However, the idea of implementing effective standards and doing things once and doing them right is pretty hard to disagree with. This is the business model for which GDS provides the basis.
With that said, many companies will want to see quantifiable benefits for business case justification (as we get further down the wave). The best proof of the expected benefits was presented by Marianne Timmons, director of e-commerce, Wegmans Food Markets. At the Marketechnics conference on January 31, 2006, their presentation showed that Wegmans has proven what the earlier-referenced A.T. Kearney study claimed: A company that embraces GDSN may see about $1 million of annual benefit per $1 billion in annual sales. Figure 2 (from her presentation) shows a breakdown of where the benefits come from. (To see the full presentation, please visit URL.)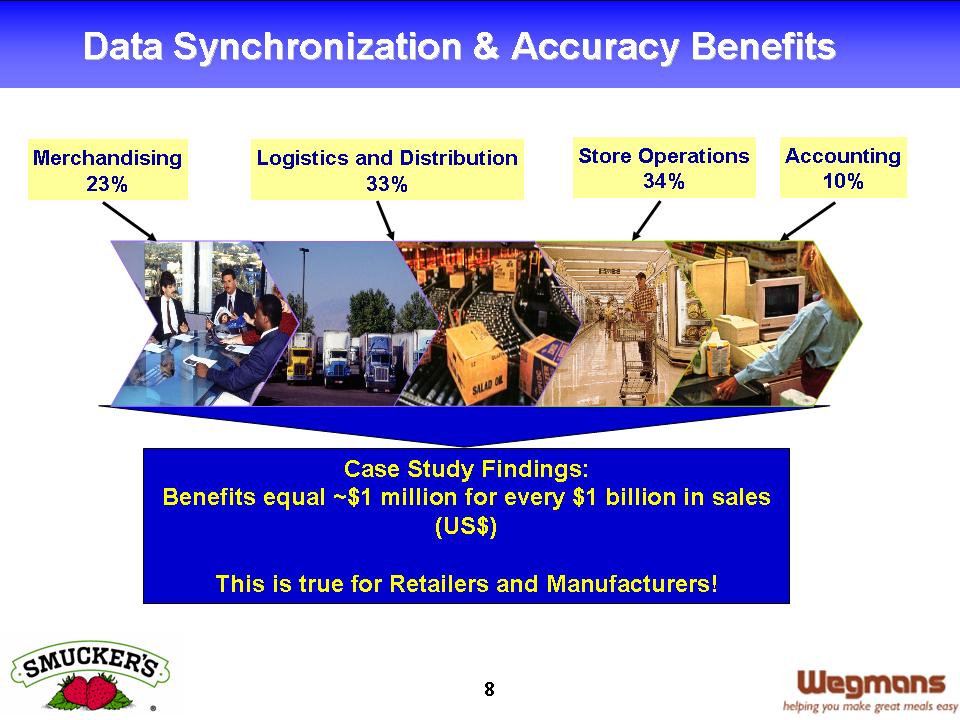
Figure 2: This is where the benefits come from.
Given the growth in all areas of GDS detailed in this article, the six areas of functional improvement for GDSN targeted for 2006 (most notably price sync), the dropping costs of participation, and more detailed and quantified benefits of participation, the future of data synchronization for 2006 and 2007 may soon be bright.
GDSN Reference Resources
• GDSN reports and materials
• Trading partners
• Action Plan to Accelerate Trading Partner Electronic Collaboration—Case studies outline the benefits of GDS to supply-side entities
• The Case for Global Standards: Creating the Business Case for Global Data Synchronisation in Your Company
• Global Data Synchronisation at Work in the Real World—How to benefit from the lessons of the last few years
• GDSN FAQs
• Global Standards Management Process (GSMP) – Task Group
• GSMP_Quarterly_Newsletter
• GSMP Quarterly Newsletter
• GDSN Background and other useful resource materials
• A GDSN Overview
• What is the GS1 Global Data Synchronization Network?
• What is the GDSN Process?
• What is a source data pool?
• What is a Recipient Data Pool?
• What is a GTIN? (or http://www.uc-council.org/ean_ucc_system/pdf/GTIN.pdf)
• What is a GLN?
Jeff Holzman is LANSA's director of solution product sales and regional director of Latin America. Jeff is responsible for moving LANSA into the GDSN business and has led the company's international expansion into Latin America and the Caribbean. Jeff welcomes any questions you may have; you may reach him at




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online