Superman and the Green Hornet didn't get slick nicknames by being just average.
In this modern work climate, it's important to be really good at what you do. If you can become an expert in a technical area that everybody depends on, your peers and management will see you as a critical asset. When crisis moments happen, any opportunity to quickly resolve them and be viewed as a hero is a good thing, not only for job retention but also personal satisfaction.
One personal side effect of becoming an expert in a technical area is that you tend to be given a nickname. Sometimes a nickname is not good. Consider, for example, these: "Are you going to let Crash-Zilla drive your new car?" or "Should I put Bottleneck Bill on your development team?" In order to be proactive and get a nickname that is good not only for your career but also for your ego, I'd like to suggest some nicknames you can take when you become an expert in a specific technical area. Of course, in these examples I will be using IBM Systems Director.
Encyclopedia Man
While not really cool-sounding, nothing makes you more attractive to your boss than knowing answers that help make business decisions. If he comes up and asks, "So what's this IBM Systems Director thing? Should we look into it?", you can calmly blather on for an extended period about what IBM Systems Director provides.
For example, you can say, "IBM Systems Director Version 6.1 came out in October 2008 and is available at http://www.ibm.com/systems/management/director. It's a systems management product that we can use to manage all of our IBM hardware, including Power Systems, System x, System z, and BladeCenter. IBM Systems Director can manage IBM i, AIX, Linux, and Windows operating systems as well as other resources, like storage and network. Finally, it has rich capabilities to manage the virtual environments of PowerVM, VMware, Microsoft virtual server, Xen, and Z/VM."
"Heady," your boss will say.
You can then feather your cap with, "IBM Systems Director comes in three parts: an intuitive Web UI, a management server, and agents. Its agent support ranges from 'no agent' to 'platform agent' to 'common agent,' which we can choose from. Once we install IBM Systems Director, that system takes on the role as the management server and will house the inventory, scheduled jobs, and other data. To start using it, we simply point our Web browser to the following Web address:
https://
By the time you finish, your boss leaves your office with a tear of pride in his eye. But knowing all conversations are monitored through the company-provided coffee mugs, you finish with, "The capabilities in IBM Systems Director are quite extensive and can be summarized by listing the various plug-ins that are available (all but the last two come with IBM Systems Director; those can be optionally installed). They include:
-
Discovery Manager
-
Status Manager
-
Automation Manager
-
Update Manager
-
Configuration Manager
-
Virtualization Manager
-
Remote Access
-
Storage Management
-
BladeCenter and System x
-
Power Systems Management
-
System z Management
-
Active Energy Manager *
-
Service and Support Manager *
* Optionally installed."
Tip: I find the best way to verbalize asterisks is to make a quick double-clapping sound like you see dancers make during the tango. It exudes confidence and portrays a memorable performance!
OK. Since product knowledge only gets you so far, let's list a few other ways you can become an expert and get a wicked cool nickname that your eighth-grade buddies would "dude!" over.
Bloodhound Lord
No, this isn't referring to your collection of tiny, stuffed toy puppies (If it is, then we have a whole other range of issues to troubleshoot). This nickname applies to you because you can sniff out problems, no matter how small they appear at first, call attention to them, and get them fixed before they cause major system problems.
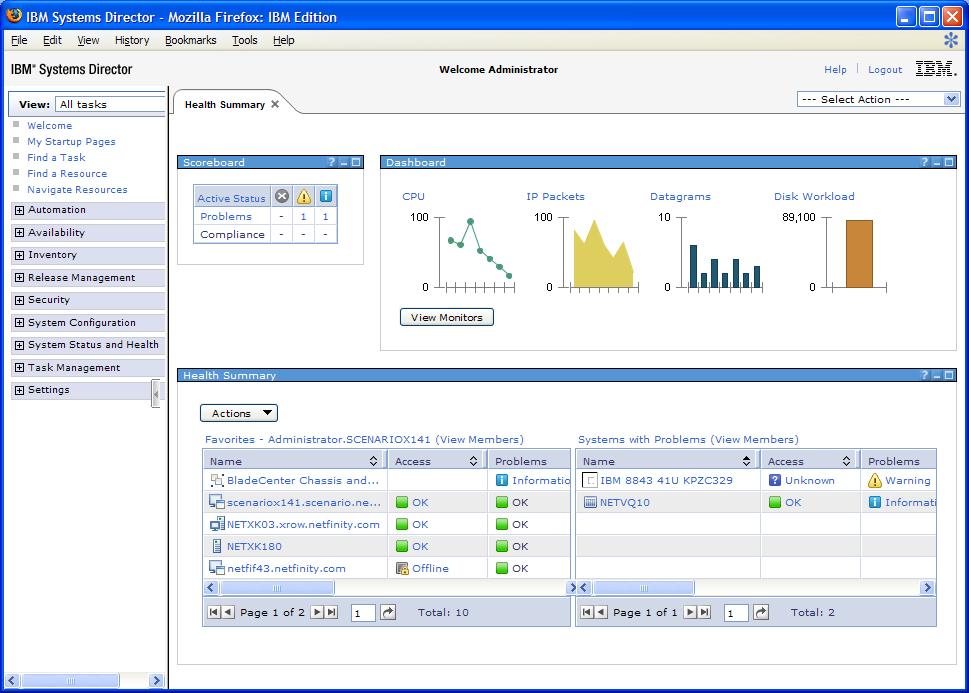
Your Lordship can choose from any of IBM Systems Director's monitoring capabilities: real-time summary pages, resource monitoring views, graphs, recording, and thresholds. You choose to start with the health summary (Figure 1).
Figure 1: Health Summary is a user-customized workspace that highlights what interests you. (Click images to enlarge.)
When your annoying colleague runs in and says, "Bloodie! Something is wrong with our Web server!", you first say, "That's Mr. Bloodhound Lord to you" and privately to yourself, "you annoying little flea." Then you say, "No fear! I've customized my health summary to highlight our Web server. Look here."
You proceed to show your health summary containing the following:
- A scoreboard summarizing any problem or compliance issue within your data center
- A dashboard that shows a collection of graph gauges for any resource monitor that interests you. In this case, you show a line graph depicting overall CPU utilization for your Power Systems running your Web server next to a graph showing the number of jobs running in your IBM i operating system where your database runs.
- A list of favorite systems and groups you want to have easy access to
- A list of systems with problems
- Any group in Systems Director that you add to the health summary as a thumbnail table
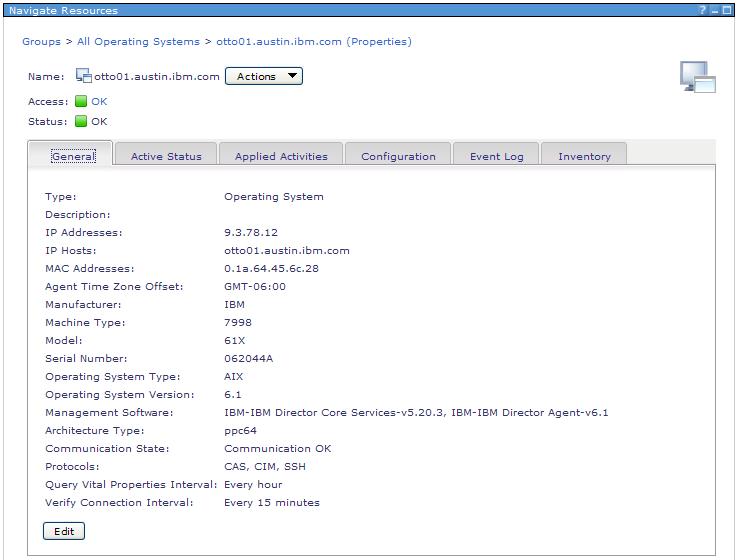
Your hound senses tell you to click the Web server in your favorites to see the properties. Seeing all the troubleshooting tabs, you decide to view all status details, then event log, then the inventory (Figure 2).
Figure 2: View Properties with tabs to troubleshoot, and use the Actions menu to run tasks.
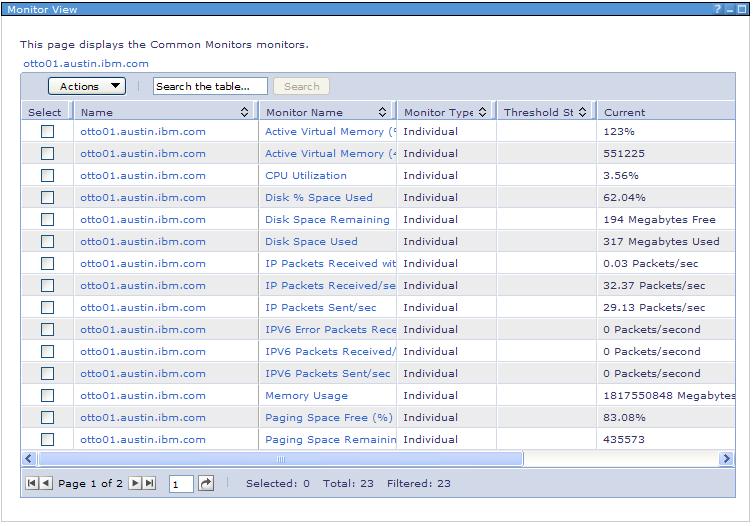
When you have zoned into the single system that is causing problems, your bloodhound prowess can use the Monitors task (Actions > System Status and Health > Monitors) to see all the important real-time monitors available for the system. For example, if I have a Linux operating system running on my Power System, I may want to monitor several values (Figure 3).
Figure 3: The Common Monitors view shows real-time data on your operating system.
For each of these real-time monitors, you can view the data in larger graphs, add them as small gauges in the health summary, or record them for a period of time. You can even add them in the Column Management Monitors so that they can be added to any table view you want.
Since bloodhounds historically tend to provide help once they find a problem, IBM Systems Director provides tasks to fix problems. Cross-platform tasks that use common UIs and command lines are available (like create virtual server, edit processor allocations, power on and off, etc). You also have the ability to launch platform-specific tasks (like IBM i work management tasks). Additionally, because you won't want to stare at IBM Systems Director all day and night (you certainly don't want to be known as Bloodshot-Eyes Kid), you can activate thresholds on those real-time monitors of interest so that when the threshold is exceeded, you can automate tasks like sending email or even running the tasks you used to fix the problem in the first place.
RoboPlan Man
While my wife says I am a robot because I don't cry at movies, I think you should take the nickname RoboPlan Man as a source of pride due to its organizational, planning, and anticipating-the-future-before-it-happens overtones. (I did take credit for shedding a tear at the end of Star Wars. Who wouldn't choke up at the wookiee roar or R2's bleeps of victory!)
In an IT shop, this nickname is highly sought--not only for the benefits to the business, but also for the fact that this nickname rhymes with the '70s song "Rubberband Man," which gives you not only a nickname, but a groovy groove to walk down the datacenter aisles to.
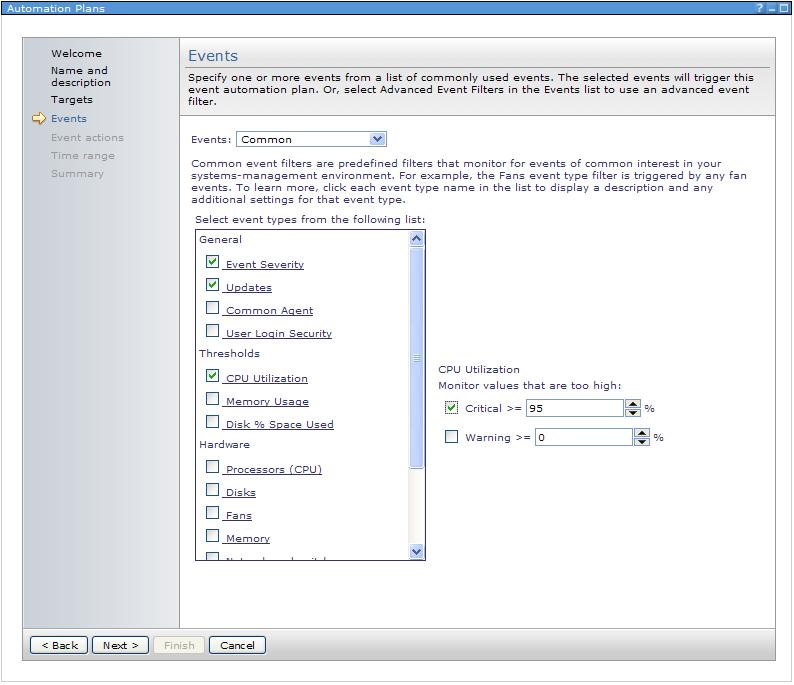
RoboPlan Man knows the main building blocks IBM Systems Director provides to get excellent automation going:
- Events--Systems Director's event log is the foundation that all automation is based on. The better-filled your event log is, the better and more precise your automation can be. Basic hardware events and alerts are automatically added to the event log from the managed systems. In the monitors UI, you can add custom threshold events for updates, energy, jobs, and system monitors.
- Event Action--The event actions that IBM Systems Director can perform range from sending email notification to running custom scripts on managed systems or even relocating virtual servers.
- Event Filter--Event filters are used to look through the event log to find exactly what you are interested in. If you want to get emailed if any critical event happens, your filter should look for any event of a critical severity. However, if you want to run a custom CL command on a single endpoint when your favorite file is deleted, then your filter should specify that criteria.
- Automation Plan--The automation plan is what ties it all together. In creating an automation plan, you select the systems you care about, the event filter to use to look for the events you care about, and then the event action to select the action you want to run.
Being a robot, you know there is a basic wizard to get initial automation started (Figure 4).
Figure 4: The basic automation plan wizard asks what events you want to monitor.
A simple wizard will enable you to set initial thresholds on important systems and will send emails when those thresholds are exceeded.
The expertise comes in when you want to get more-advanced automation. This involves diving deep into the event filters and event actions. The result is that you can plan for many intricate problems and have them automatically fixed. You can be notified at the earliest moments when something bad is happening, and you can customize how to respond to the problem efficiently and powerfully with command definitions.
Note: IBM i's messages can be monitored as events. For example, an event filter can select all IBM i systems and monitor for select messages from the QSYSOPR message queue. The result is that any QSYSOPR message can be used as an event-action trigger. (I can already see your robot ears wiggling in excitement!)
Finally, since RoboPlan Man loves to code small tools, you can create a small program on your managed operating systems that monitors some very unique aspect of your system or custom application and, when it's found, generate a Systems Director event. Once you give it a unique ID, the event is sent to Systems Director, where your event filter catches it, and your automation plan calls a custom action to run.
Virtual Sergeant Dictator
While dictatorship is not usually a positive job trait, controlling your system resource use through virtualizing your systems is quite positive. When you can force your many applications to run on a few physical servers, when you can squeeze every ounce of performance and shared utilization out of them, when you can relocate running virtual servers to different hardware with no downtime, you can be Virtual Sergeant Dictator. (Tip: Always keep "Sergeant" in the nickname, or add your own fierce-sounding label. Just having Virtual Dictator as your nickname will quickly be shortened to "VD" then to "VD Boy"...and that is not good).
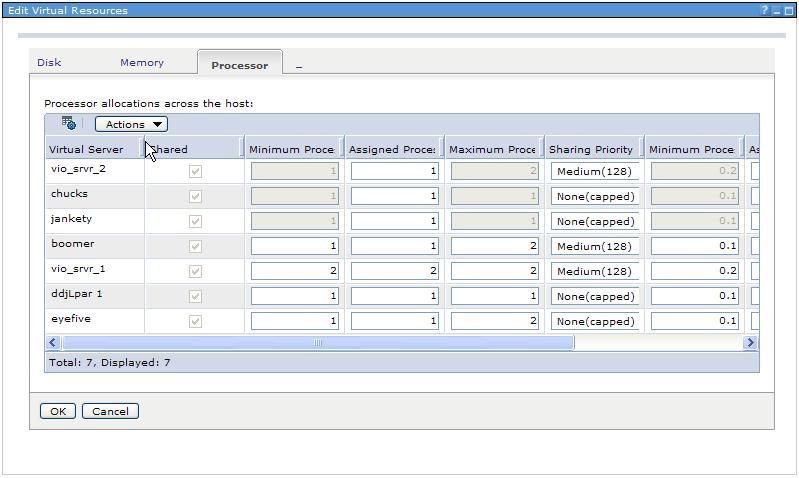
IBM Systems Director provides all the tasks you need to become Virtual Sergeant Dictator. I suggest taking it in stages. Start by creating virtual servers. The simplified wizards make it easy to create your Linux, AIX, or IBM i partition. You can also use the same wizard to create virtual servers on VMware, Xen, and Microsoft Virtual Server. Once they've been running awhile, you can demand more out of your system by editing your hosts (Figure 5). This will let you change disk, processing, and memory for all virtual servers running on a system at will.
Figure 5: The Edit Virtual Resources task shows all the virtual server settings for that host.
Note that all of these virtualization tasks have command-line equivalents so you can change the resource allocations based on events coming in.
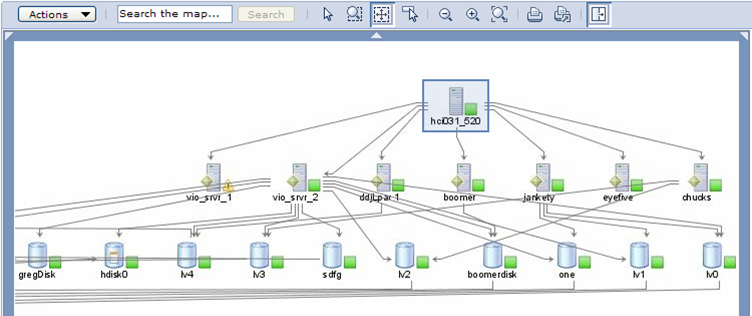
Next, show the results in a topology map. A good dictator always wants to see its subjects line up in orderly fashion, in this case by showing relationships between the resources, which identify places where changes can benefit the whole system. This also makes your management wonder again how they can live without you...along with your ego-stroking, sergeant-barking response to their requests: "SIR YES SIR!"
Figure 6: The topology perspective "Virtualization Common" shows the virtual innards of a power system.
Finally, to complete your Virtual Sergeant Dictator mutiny, start using relocation plans. These let you plan a live relocation of a running Linux or AIX virtual server, based on any event you want as a trigger. The result is that, when an event that concerns you appears, a single virtual server or all virtual servers on a host will be relocated to different hardware. The event can be anything, ranging from hardware errors, performance peaks, energy use, temperature, even job or subsystem performance.
Knox
Like Fort Knox, you can have a reputation of tightly securing IBM Systems Director tasks. You also can benefit from it sounding scary: "Hey, he might knock me around if I don't comply with his security measures." IBM Systems Director comes with role-based security that lets you not only decide which tasks a user can perform within IBM Systems Director, but also to which systems. With over 300 tasks you can perform, you can make sure your data center is securely managed. Further, IBM Systems Director includes credential mapping, which provides single sign-on support to remote consoles like the HMC Web console or the AIX Web console.
Smiley Face
I know what you're thinking: "Dude, this nickname is not cool! I want to be a critical asset, not just an ...". Trust me. Nothing says "I'm the one you want around to keep everything happy and current" more than a smiley face. In your case, you are the one who always keeps a system up-to-date with its firmware and operating system updates. That, in turn, makes your boss smile. When your boss wants a warm fuzzy that all systems are up-to-date, he will think, "Let's get Smiley in here."
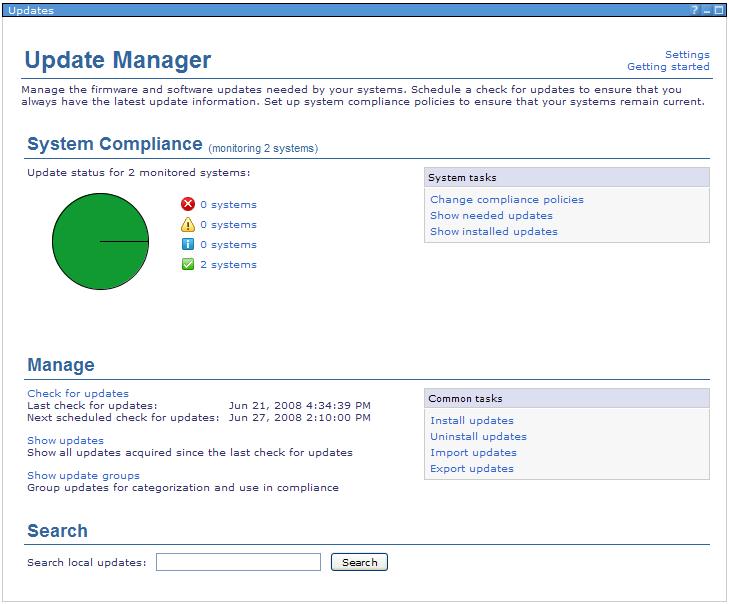
Update Manager, a part of IBM Systems Director, helps you manage firmware and operating system updates. It can manage firmware updates for HMC, Power Systems, BladeCenter, and System x. It can also manage operating system updates for Linux, AIX, and IBM i. For IBM i, Update Manager can also handle cumulative packages and PTF groups.
Your smiley-ness will start when you click "Get Started with Updates." This wizard will guide you through checking ibm.com for the latest updates for any systems you want. Every time Update Manager checks ibm.com for updates, if it finds that systems it is monitoring have updates available, a warning or critical compliance status will be added to those systems. Then, from the Update Manager summary page, you can quickly glance to see which systems need updates (Figure 7).
Figure 7: The Update Manager summary page shows system compliance, management tasks, and areas to search for updates in your data center.
You can then give your boss a smiley facial. For example, if your boss says, "Hey, are my systems current?", you glance at your update manager summary page. Your response? Smile. Your boss's response? Smile. You can also customize a policy to check for a certain group of updates. So if your boss says, "Hey, do my systems have those security patches we talked about?", let the smile-fest commence.
Green Monster
While a famous philosopher once said, "It's not easy being green," it actually is with IBM Systems Director. By mastering the skills of monitoring and managing the energy use in your data center, your nickname will be understood and respected even by folks outside the industry. The bonus? The Internet sells all kinds of green-colored accessories to reinforce the "monster" part of your nickname.
Active Energy Manager is an optional plug-in to IBM Systems Director. You can download it for a 60-day evaluation period. During that time, you can hone your green monster skills by monitoring energy use, temperature, and effective CPU speed to see how they all relate. You can manage your systems' power capping and power savings during that evaluation period as well. If you like Active Energy Manager, you can purchase a license to continue monitoring and managing. If you don't think it's worth it, you can let the evaluation period expire and, though the management functions will be disabled, the monitoring functions will still be available.
Note: If you try out the power capping or savings during the evaluation period, once the evaluation period expires, Active Energy Manager will reset all systems you changed back to their default energy settings. If this happens, your nickname may turn into "Green Puke Monster," which is entirely bad. So plan accordingly by using test systems or announcing this may happen.
Just as other monsters use clubs, bats, or other instruments to help in their domination, you are no different. In addition to the long list of IBM hardware that provides energy and temperature sensors, Active Energy Manager also works with third-party sensors, cooling units, and iPDUs (intelligent power distribution units...like fancy power strips) to help manage energy use for older systems without the function built in.
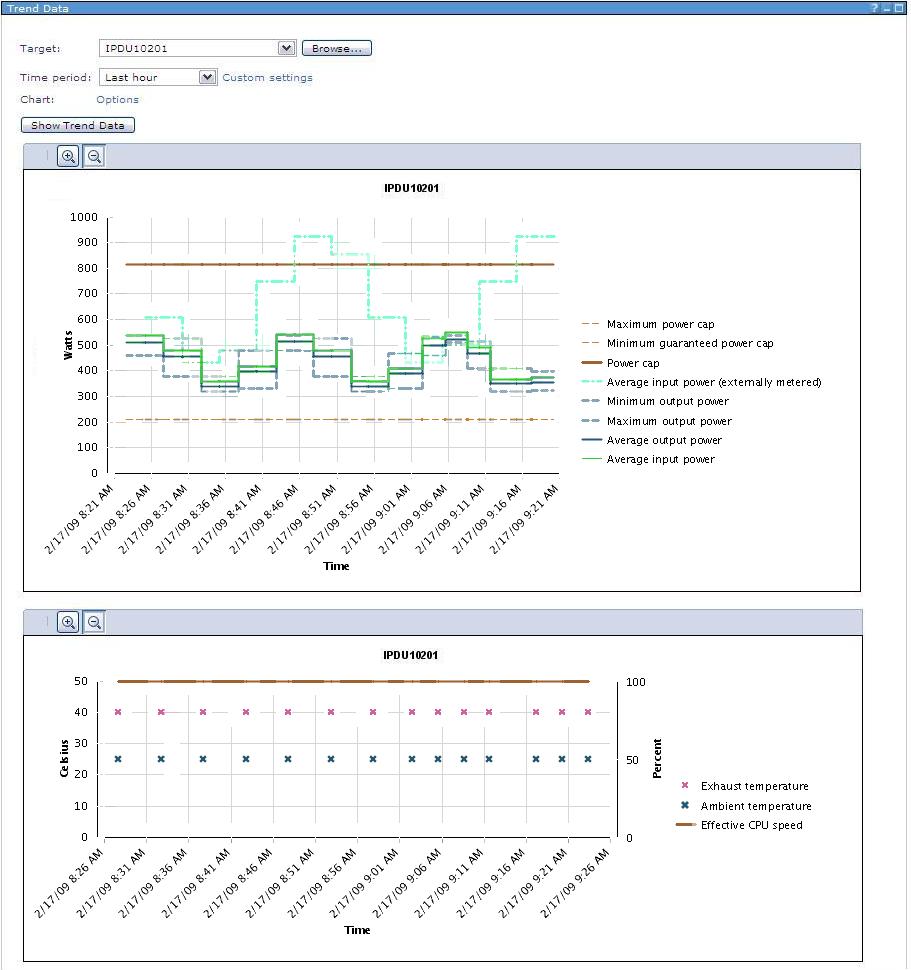
While traditional green monsters leave nothing but destruction in their wake, you leave nothing but cash. The savings can be real. And while other green monsters use sharp teeth and whipping tails to keep their minions in line, you use Active Energy Manager tasks like power capping, power savings, cost calculator, trend data, and built-in policy support to keep your systems in line.
Imagine the following scenario:
Your boss says, "Greeny!" You want to respond, "It's MR. GREEN MONSTER, you ignorant, would-be-serving-fries-if-you-didn't-marry-out-of-your-league loser!" But instead, you respond, "Yes, sir. Green Monster here to help."
"I just got word from the power guys that our new lab has a maximum wattage rating. Our system count cannot increase, and our workloads are increasing. Go forth and fix all that!"
Your first task is to look at the Trend Data (Figure 8).
Figure 8: Trend data shows historical energy data.
This task shows a history of your systems' energy use. You see there is room for improvement. The next task is to study the Cost Calculator, where you can get an understanding of how much money a system takes to run (both in direct wattage and indirect cooling costs). This gives you a baseline to compare with after the new lab is in.
Next, as the systems are moved, you use Power Capping to guarantee that the system will not use more watts than what you specify, making sure that your systems combined don't exceed the lab floor rating.
Now your green monster gills start flapping happily because you use Power Savings to dynamically reduce the energy use of the systems. Depending on the platform, some simply reduce voltage and frequency of the processors, while other platforms offer dynamic settings to choose from. Options include "save energy but optimize for performance" or "save energy and optimize for energy savings." In order to get extra green goo awards, you schedule that task: From 6:00 a.m. to 6:00 p.m., your systems optimize for performance; from 6:00 p.m. to 6:00 a.m., your systems optimize for energy savings.
Next, because you want to ensure that these settings are in action, you decide to schedule Active Energy policies so that the power settings you want are enforced at all times.
Finally, as your boss prepares an energy summit, you start partnering with Virtual Sergeant Dictator to automate the virtual aspects of your energy-optimized servers. Based on overall system usage, you decide to live relocate all remaining virtual servers to other hardware and set the power cap very low on the unused server over the weekend. Then you schedule to increase the power cap and to live relocate the virtual servers back early Monday morning.
As your boss walks in, you open your Green Monster maw and devour him in one swift gulp. Actually, that was how it happened in your dreams. When he walks in, you simply state what you've done. After congratulating you, he gives you an afternoon off to scare the locals at the beach.
Summary
There you have it. If you want to be an expert using some really great systems management function and get yourself some nicknames you can call home about, give IBM Systems Director a try. For more information, check out the following Web sites:
IBM Systems Director Web site:
http://www-03.ibm.com/systems/management/director/
IBM Information Center - Systems Director 6.1 content:
http://publib.boulder.ibm.com/infocenter/systems/director_6.1/fqm0_main.html




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online