In a previous article, I revealed that using iSeries Navigator can help you become a superhero. Really! Although you can't save the world, you can definitely do a better job at saving the day in your IT shop--and maybe even have some fun while completing your work more efficiently.
One of the superheroes I introduced you to was the Wireless Wonder, a superhero you can become just by using iSeries Navigator for Wireless. In this article, I'd like to peek inside the world of the Wireless Wonder and show you where she gets her power, how she trains to become the best she can be, what villains she battles, and how she uses her super powers to save the day.
Her Source of Power
Wireless Wonder's source of power comes from her utility belt, which only the coolest superheroes have. What does she have on her utility belt? Two things: iSeries Navigator and iSeries Navigator for Wireless.
iSeries Navigator is a robust application filled with rich functions to manage your iSeries systems. It comes on the iSeries Access for Windows CD and has new functions in every release. (Tip: Always use the latest iSeries Navigator release, currently V5R2. Even if you don't have OS/400 V5R2, go to the iSeries Access Web site and get the latest CD. You'll be glad you did). For the Wireless Wonder, the most important parts of iSeries Navigator are the monitoring functions, multi-system tasks, and command definitions, as well as the job and message functions. But in order to take advantage of these functions while wirelessly saving the world, the Wireless Wonder also needs iSeries Navigator for Wireless.
iSeries Navigator for Wireless is a companion to iSeries Navigator that allows the Wireless Wonder to manage her iSeries systems from anywhere by using an Internet device such as a PDA or an Internet-capable phone. As you'll see later in this article, she can do things like view system health, run commands, hold jobs, reply to messages, and view long-running tasks. She works with both tools and knows how to set up her tools and items of interest at a fully functional workstation using iSeries Navigator and then manage what she's interested in from anywhere.
How She Trains
The Wonder Cave is where the Wireless Wonder trains. From there, she works on making iSeries Navigator for Wireless work the best. Since iSeries Navigator for Wireless connects to her central system, which is where she can define all of her monitors, definitions, and long-running tasks using iSeries Navigator, she starts her training by setting up the monitors, command definitions, and tasks that she'll need. iSeries Navigator for Wireless will only work as well as iSeries Navigator is set up, so the first thing she does is to tell iSeries Navigator what she's going to be interested in while she's out and about. How? Simple. She opens iSeries Navigator and sets up the following:
Interest: She has three systems she's totally responsible for and eight other systems for which she's responsible for the HTTP servers. She wants to make sure she can see the health of all those systems from her wireless device. Action: She adds all 11 systems and endpoint systems under Management Central in iSeries Navigator. In addition, she groups the last eight systems into a system group.
Interest: She wants to know the overall CPU utilization across all 11 systems as well as the disk usage for the first three systems. Action: She creates and starts two system monitors. The first will monitor CPU utilization across all 11 systems, and the second will monitor disk usage and disk space for the first three systems.
Interest: She wants to monitor her HTTP servers on the first three systems and all of her jobs across all 11 systems. Action: She creates and starts a job monitor by selecing HTTP Server from the Servers To Monitor tab. She also creates and starts a job monitor that looks for all jobs across all 11 systems that she owns.
Interest: She wants to be alerted when inquiry messages are sent across her three primary systems. Action: She creates and starts a message monitor that points to the QSYSOPR message queue, monitoring for any inquiry message.
Interest: She has a number of trouble-shooting commands she runs regularly. From her Internet phone, it's difficult to type those commands in, so she needs a way to run these recurring commands quickly. Action: She creates a number of command definitions by opening Management Central, selecting Definitions, and then selecting Command. Any command definition she creates will be available from her phone. (Tip: Name them with short names. Phone displays usually show only about 20 characters at a time!)
Interest: There are three very important files on each of her systems. If they're changed, she needs to know. Action: She creates and starts a file monitor that points to the three files she is interested in. She specifies the Status metric, telling it to trigger if any of the files change.
Interest: Two of her primary systems have integrated xSeries servers on them, and she needs to know how they're doing and needs the ability to perform emergency actions if something goes wrong. Action: She verifies that her primary systems have been added as endpoint systems. That's all she has to do, because managing integrated xSeries servers is built into iSeries Navigator for Wireless as long as the system is an endpoint.
As you can see, the more she trains for her wireless adventures into the real world, the more prepared she'll be. If she sets up all of this beforehand, when some villain tries to foil her Utopian network, the monitors will tell her that something she cares about needs attention, and she can fix it before the villain wins.
Villains She Meets
Now that Wireless Wonder has fully trained for her mission, she starts her adventure. Today is going to prove to be an exciting day, with a number of villains challenging her every move.
Techno Tommy, the Pain-Inflicting Developer
Overwhelmed with an obsession to inflict pain and suffering upon system administrators like the Wireless Wonder, Techno Tommy spends all day and night developing hard-to-configure Web application servers. He won't stop until he hears every administrator within a thousand miles yell, "PLEASE STOP!"
Dr. CPU Voodoo
Once a mild-mannered professor, Dr. CPU Voodoo is now known to unleash powerful and processor-hungry jobs that can bring any computer to its knees (or casters, as it were). He knows that once a system is reaching its CPU usage capacity, it can be rendered useless by all but the most patient users.
Object Locker Boy
Nothing stops a job in its tracks faster than making it stall because it's waiting on a locked object, and Object Locker Boy knows it! His passion in life is to lurk in the shadows of an iSeries and pounce whenever an important job is about to access an object. Just then, he'll do some read/write action on an object, lock it, and sit back and snicker.
Henry the Hacker
Once the faithful partner to the Wireless Wonder, Henry the Hacker was found guilty of accessing files he wasn't authorized to. The former Wireless Wonderboy, Jr. Grade attempted to access personnel files and promote himself to Lieutenant Wireless Wonder. His expulsion from the superhero ranks turned his heart cold, and he continues to attempt to break into his former work to change those files!
The Wired Whiner
While not a true villain, the Wired Whiner is a coworker of the Wireless Wonder. He has a PDA but doesn't have the smarts necessary to fix problems properly. The problem is, he doesn't know that. He needs to be able to view his monitors and tasks but not take any actions.
How She Saves the Day
6:00 a.m. The day starts just like any other day. The Wireless Wonder wakes up, gets dressed, and straps on her superhero utility belt. Along side, she keeps her Internet-capable phone and wireless PDA. In the Wonder Cave, she finishes setting up iSeries Navigator so that she is completely prepared for what might lie ahead. It's nearly 8:00 a.m., and she is about to head to the streets to make the world a safer place.
8:00 a.m. Wham! Her Internet phone cannot access iSeries Navigator for Wireless! She soon realizes that her assistant never set up the Web application server running iSeries Navigator for Wireless. What is she to do? She knows it's not really her assistant's fault; it's the evildoings of Techno Tommy, the Pain-Inflicting Developer! His deepest hope is that she wastes an entire day setting up that Web application server! She only has a few minutes before she has to be at the third annual superhero brunch, so she whips out the iSeries Navigator for Wireless User's Guide and finds a script she can run to instantly set up the Web application server. She runs the script, types in the URL, and presto, she's up and running.
Techno Tommy, the Pain-Inflicting Developer, foiled again!
10:00 a.m. While at the superhero brunch (today's topic is "Super Hero Dress Code: The Tights of Tomorrow"), the Wireless Wonder feels her PDA vibrating. This can only mean one thing: Something she cares about needs attention! She opens her PDA and reads an email from her iSeries saying, "Help! I have a job that is running out of control on System8, and I can't seem to stop it! Signed, CPUMonitor5" (which, by the way, was done by first purchasing a third-party application to notify her and then adding that message to her system monitor). This message was sent because she set iSeries Navigator to notify her if CPU usage got above 80%.
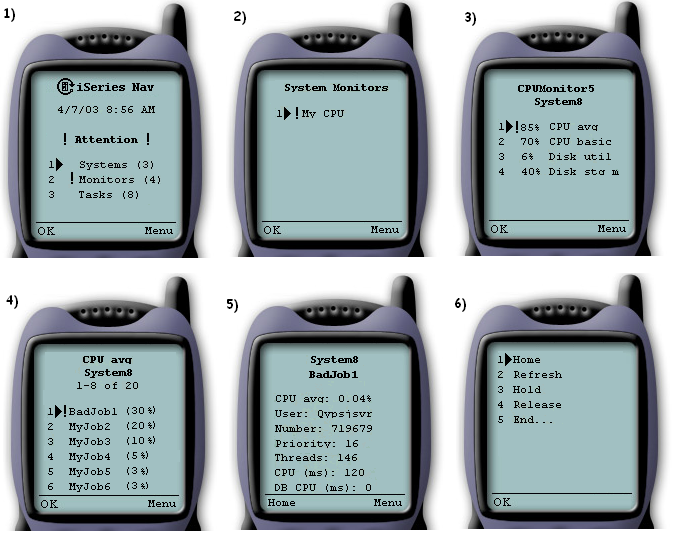
So as not to disturb the brunch, she calmly opens iSeries Navigator for Wireless and navigates to CPUMonitor5. She instantly sees the cause of the problem: Dr. CPU Voodoo! The evil professor has unleashed two of his power-hungry jobs. One is on a V5R2 iSeries, and the other is on an older V4R5 AS/400. The Wireless Wonder navigates to the iSeries and sees that Job5 is taking up much of the CPU on the system. She quickly selects that job, opens the menu, and clicks Hold. This lets her solve the problem but allows her to keep the job around so that she can troubleshoot to prevent it from happening again. Figure 1 shows how the navigation looks on an Internet-capable phone.
Figure 1: From an Internet-capable cell phone, you can perform all iSeries Navigator functions. (Click image to enlarge.)
The next troubled system is that older V4R5 AS/400. iSeries Navigator for Wireless added the feature of holding of jobs in V5R1, so how is she going to get back to that V4R5 system? Not a problem! Because she's well-prepared, she goes to the system monitor that's monitoring that V4R5 AS/400, selects the job, and holds it! How is that possible? Only the central system (the system where the PDA is connecting to) needs to be at V5R1 or later to act on jobs. The endpoint systems being affected can be any supported release.
Dr. CPU Voodoo foiled again!
12:30 p.m. After brunch, Wireless Wonder travels downtown to work on her wireless electricity invention. As she walks through the door labeled "No Batteries, No Wires, Just Pure Electric Power," she gets a call from a friend telling her that her company's Web site is very slow. Instantly, she opens iSeries Navigator for Wireless to take a look. Sure enough, her job monitor for the HTTP server jobs has triggered. When she investigates why it triggered, she realizes that the Object Locker Boy has struck again. Fortunately, she has a program that will fix the problem. She brings up her favorite command definition, FixLockedObjectProblem, and runs it right from her wireless PDA. In no time, the job is no longer waiting on that locked object, and the Web site is healthy and stable.
Object Locker Boy foiled again!
3:00 p.m. While driving back to the Wonder Cave in her WonderMobile, she gets a page. After putting the car in autopilot, she reads that her file monitor triggered. She knows full well what that means: Henry the Hacker has struck again! She knows it's an inside job. Although the iSeries is nearly impossible to break into, Henry's been using temporary user profiles to access files he shouldn't. This particular file monitor was monitoring files created just to catch Henry. She sees that the file was modified, and she instantly runs a command to disable the user profile that accessed the file as well as capture a trace of all related activities. Not only was Henry the Hacker caught, but the inside accomplice was caught as well. Thanks to iSeries Navigator for Wireless, Wireless Wonder was able to act as soon as the file was modified.
Henry the Hacker foiled again!
5:00 p.m. Back at the Wonder Cave, the Wired Whiner approaches the Wireless Wonder, and he's mad! "You've been gone all day long, and all I wanted was to help out and use iSeries Navigator for Wireless to save the world, but I can't do anything!" She calms him down and promises to look into it, but the secret is that she already knows what happened. Even though he has monitors running and is a help with distributing software, he tends to be a tad dramatic. If he sees a small problem, he blows it out of proportion and starts ending jobs and running high-powered commands that he really shouldn't. Just this morning, he became very concerned about all the cryptic jobs that started with Q and decided that they should be ended. And that's not a good solution. Because Wireless Wonder anticipated just such an event, earlier in the day she set up the iSeries Navigator for Wireless read-only access function, which allows users to see monitors and tasks and system health but denies them the ability to run commands, hold jobs, reply to messages, or any other supported action. This allows him to see a problem and call the Wireless Wonder to fix it.
6:00 p.m. The day is nearly done. The Wireless Wonder has foiled the attacks of many of the top criminal minds in the iSeries today, in addition to a well-meaning but paranoid coworker. As she leaves the Wonder Cave, she kicks off a few tasks to run during the night: Send and install software across 10 systems, send and install fixes on three system groups, and schedule user management tasks and system value updates. Later, at her leisure, she can confirm that these tasks ran successfully using iSeries Navigator for Wireless. If they didn't, she'll know that something needs attention as soon as she logs on.
Summary
By just viewing a typical day in the life of our superhero, we have witnessed the power of iSeries Navigator for Wireless. By taking advantage of iSeries Navigator functions such as endpoint systems, system groups, monitors, definitions, tasks, and automation, the Wireless Wonder saved her IT shop against some nasty villains. And even though the villains were imaginary, their potential to cause problems was very real.
I hope you had some fun learning about what iSeries Navigator for Wireless can do for you. Stay tuned next time for "The Adventures of the Compare and Update Kid!"
More Information
For more information on iSeries Navigator and iSeries Navigator for Wireless, check out IBM's iSeries Navigator Web site for articles, fixes, setup scripts, and links to other information.
Greg Hintermeister is an eServer user interface designer at IBM Rochester and has worked extensively with iSeries Navigator, iSeries Navigator for Wireless, and several Web applications. You can reach him at




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online