Are you a system administrator responsible for your iSeries or AS/400 systems? With today’s e-business and ever growing B2B needs, the health of your systems is critical to the success of your business. No matter how many safeguards you put in, your systems may still get into trouble—usually while you are away from the office enjoying a nice evening out or working on another project. It is for this very reason that in V4R5, IBM introduced Management Central - Pervasive (Pervasive). Now, from an Internet phone, as shown in Figure 1, personal digital assistant (PDA), or traditional Web browser, you can see the status of your systems and the status of any active Management Central monitor. From anywhere, many questions can be answered, including:
• Is my system up and running?
• Has it finished restarting?
• What is the CPU percentage on my five Web servers?
• How is my disk usage?
• Is my communication line usage up to par?
What is Management Central - Pervasive, how does it work, what devices does it run on, and what do you need to install and configure in order to use it?
Background of Management Central and Monitoring
Management Central is a part of Operations Navigator that is dedicated to providing systems management functions that make it just as easy to manage multiple systems as it is to manage one system. It is also a part of a larger three-pillar IBM systems management strategy with three specific goals:
• To integrate systems management function as part of the OS/400 operating system with Management Central
• To provide multiple-platform support with Tivoli
• To offer solutions from partner software providers
In OS/400 V4R3, Management Central was first introduced with the ability to group systems, monitor those system groups, and log events when thresholds were met. In V4R4, Management Central was expanded by providing the ability to perform specific
tasks across multiple systems and allowing actions to be scheduled:
• Running commands
• Working with hardware, software, and fixes inventory (collect, search, and export)
• Packaging files and folders, and send them
• Managing fixes
• Collecting performance data
In V4R5, additional performance monitor metrics and Pervasive were added. There is plenty in store for the future. Read the sidebar “Coming Soon to Management Central” on page 27 to learn what is planned.
One of Management Central’s highlights is the ability to monitor a number of metrics across multiple systems. You can choose any combination of metrics, select when the monitor should trigger and reset, and choose actions to occur when it does trigger and reset. Once the monitor is running, you can view a graph of the metric values, click on a point, and view the top 20 items for that collection period.
Pervasive takes advantage of the monitoring function. Once you have created your monitors and start them from the GUI, you can use your Internet phone or PDA to view various kinds of information about those monitors—the systems they are running on, which systems have been triggered, and the values of the metrics being monitored. As you can see in Figure 2, the graphs and phones are very different but can display similar information.
A Simple Preparation
Preparing to use Pervasive is simple but important. If you don’t follow certain steps, Pervasive won’t be very useful. Preparation involves three simple steps in the Management Central GUI:
1. Add endpoint systems—Only systems that have been added as endpoint systems in Management Central can be viewed or monitored from Management Central - Pervasive. To add endpoint systems, start Operations Navigator, explore Management Central, select AS/400 Endpoint Systems, and choose the New Endpoint System menu item.
2. Create monitors—Only monitors that you own will appear in Management Central- Pervasive, so be sure to create monitors that will be useful to you. In addition, because of the limited display size on a phone or PDA, monitor names should be short and meaningful. That way, when you see the list of monitors and one is triggered, you know exactly what the problem is and immediately how severe it may be.
3. Start your monitors—Only active monitors will appear in Management Central- Pervasive, so don’t forget to start them. Make sure that you start them on the systems you want. Currently, there is no way to change systems or start a monitor from Management Central - Pervasive.
How It Works
To start using Management Central - Pervasive, simply enter the URL that you specified on your central system. You will then see the summary page. This will tell you, at a high level, if all your systems and monitors are running smoothly. If they are, great—that’s all you need to know. In fact, it’s designed so that the summary page is all you will ever need to see to be reassured that everything is working fine. However, if a system or monitor needs attention, it will tell you on the phone by displaying Attention and either an exclamation point (!) or a bell (%) symbol, as shown in Figure 3, next to the items that need attention. An exclamation point indicates a system or monitor has failed, a bell indicates that a monitor has been triggered (e.g., CPU is above 75 percent on one of the systems it’s monitoring). Even if all your monitors are running smoothly, you have the option to navigate down to see the value of a particular metric on a system you are monitoring. Of course, there is more display space available on a PDA, as shown in Figure 4, than on a phone, thus allowing you to view more information on the summary page about how many systems and monitors need attention. Note: On devices on which artwork is not supported, the failed and triggered messages will be represented by the exclamation point (!) and the asterisk (*) symbol.
Viewing Systems
Any endpoint system is available to be viewed from Management Central - Pervasive, but only systems that you have added to your personal system list will be shown. This allows you to view only systems that you are interested in while away from the office. Adding systems to your personal system list is simple:
• Using the phone—Select Systems from the summary page. Then, on the systems list, select Menu, then Add System. Enter the system name, and then select OK.
• Using the PDA—Select the Settings button, add the systems you want, then select Summary for an updated list.
Viewing Monitors
As I mentioned, only your active monitors will be added to your list. Once you see that a monitor needs attention, you can navigate to see the particular monitor, the systems in that monitor, and detailed monitor metrics for each system that is being monitored. Looking at Figure 5, you can see that the metric names are shortened compared to the GUI metric names. That was done to allow you to view as much information as possible on the small display sizes. To see a mapping of the shortened names to the GUI names, look at IBM’s Management Central - Pervasive’s Web site at www.ibm.com/eserver/iseries/ sftsol/pervasive.htm.
What’s Needed
Pretty cool, huh? Here’s a brief summary of what you need to run Management Central- Pervasive:
• A device to run Management Central-Pervasive, such as an Internet-enabled phone with a wireless Internet service, PDA with a Web browser, a wireless modem and wireless Internet service, or a traditional Web browser on a workstation.
• One V4R5 system running in a TCP/IP network. (This will be your central system that is used by Management Central.
It’s from where all of your monitors have been created and are running.)
• A Web application server running on your central system, such as WebSphere Application Server, Domino Application Server, or any other application server that runs on the central system and possesses the capability to host servlets.
• Two Management Central fixes installed on your central system, namely SF62901 (product 5769SS1) and SF64097 (product 5769SS1).
Pervasive runs on three types of devices—Internet phones, PDAs, and traditional Web browsers on a workstation. All three types will show you the same information but may display it in a different way to take advantage of the unique characteristics of each device. You should consider these points before investing in a particular device:
• Display size—In general, the more you can see at one time, the better. Internet phones have the smallest display size with ranges from three to eight lines in height, whereas a PDA has 10 to 15 lines. However, using a phone has a big advantage in that if you do discover a system that needs attention and you have an Internet phone, you can use it to call your office from wherever you are.
• Wireless service—Since the whole point of a wireless device is to view information from anywhere, make sure your service provider supports the areas in which you live and travel. Having the “coolest” phone on the planet isn’t very cool when it’s not in range of your service provider.
• Browser—The Internet phone you buy has a browser built into it. Make sure it is one that Pervasive supports. On a PDA, you can install and use any browser you wish, so you can choose from the browsers supported by Management Central - Pervasive.
Pervasive uses Wireless Markup Language (WML) to communicate with the Internet phone. Figure 6 outlines the Internet phones that Pervasive supports and indicates whether it was tested on the real phone or a simulator and the service provider used. Each of these phones use the UP.Browser microbrowser developed by Phone.com (See the Phone.com Web site at www.phone.com). Many other Internet phones use the UP.Browser and Pervasive should work with any of those as well. However, I did find that some UP.Browser-supported phones had different behaviors such as not supporting graphics or displaying tables in different ways. If you use an Internet phone not listed above, contact me at gregh@ us.ibm.com and let me know how it works. I am very interested in knowing what works and what doesn’t.
For PDAs, Pervasive uses HTML to communicate with a browser on a PDA. These browsers are supported by Management Central - Pervasive:
• AvantGo Version 3 (See the AvantGo Web site at www.avantgo.com for more information.)
• EudoraWeb version 1.1 (See the Eudora Web site at www.eudora.com for more information.)
Devices
Phones
PDAs
Other browsers may work as well, but remember, the way the HTML is displayed affects browser behavior and display. Some browsers support graphics, others do not. Some browsers support tables, others do not. As far as the PDAs themselves, I tested the PDAs shown in Figure 7, but as long as your PDA can run the browsers previously mentioned, any PDA should work.
Traditional Browsers
Since workstation browsers are much more advanced than those on a PDA, most any workstation browser will work. Just keep in mind that Pervasive is designed for a small wireless device, so it won’t look very fancy on your workstation browser. One option is to open a small browser window and place it in the corner of your monitor. You can keep current on how your systems and monitors are doing while you are working.
What to Install
Because Management Central - Pervasive communicates with the central system, only the central system has to be set up to work with a wireless device. Once the central system is working, any other system can be added as an endpoint and it will work with Pervasive without any additional installation or configuration. To get Pervasive running on your central system, you will need to add two Management Central fixes, install a Web application server, and set up your firewall to allow your central system to be accessed from the Internet.
Caution: I suggest that you develop an Internet protection plan before setting up Pervasive so you are clear as to the level of security you require on your systems. Ask yourself these questions:
• Will Pervasive be accessed via the Internet or from browsers on clients attached inside the server’s firewall?
• Do I need to use SSL? (The UP.Browser microbrowser and AvantGo Version 3 support SSL, but others do not.)
• Can my desired protection be set up on the Web application server I choose, such as IBM WebSphere Application Server and IBM HTTP Server for AS/400?
• How sensitive (to me) is the data that Pervasive sends?
In developing this protection plan, I suggest you reference the IBM Redbook, AS/400 Internet Security Scenarios: A Practical Approach (SG24-5954-00).
Management Central Fixes
There are two Management Central - Pervasive fixes to install onto your central system:
• SF62901 (product 5769SS1)
• SF64097 (product 5769SS1)
Once the fixes are installed, run this command to move the Java programs to the OS400 folder:
RST DEV(‘/QSYS.LIB/QYPVPERVSF.FILE’) OBJ((‘/QIBM/PRODDATA/OS400/*’))
Note: If the time is not shown correctly when running Pervasive from a PDA or traditional browser, install fix SF63718 (product 5769SS1). This will correct a problem with WebSphere Java Virtual Machine not being able to pick up the locale settings correctly.
Web Application Server
Any Web application server that supports servlets can be used with Pervasive. Management Central - Pervasive was tested with IBM WebSphere Application Server Standard Edition for AS/400 version 3.0.2. You should follow these required configuration steps:
1. Update classpath information—Add the two JAR files used by the Pervasive servlet to the WebSphere class path. From the WebSphere Administrative Console, select the Topology tab and select the application server that will be running the Pervasive servlet (in my case, it was WebSphere). Add this classpath information to the command line arguments parameter:
-classpath
/QIBM/ProdData/OS400:/QIBM/ProdData/OS400/mcypvperv.jar:/QIBM/ProdData/Http/Public/jt4
00/lib/jt400.jar
Then press apply. This identifies the two JAR files used by the servlet to the Java Virtual Machine that was started by WebSphere.
2. Implement a protection plan—The Web application server will have to be set up to provide the necessary level of security. Set up the Web application server to implement the protection plan developed to provide proper authentication security based upon your client devices, browsers, and network. IBM recommends implementing HTTP with SSL (HTTPS) whenever possible.
3. Give proper authority to users—Specify that the user profile running the McYpvPervasive servlet (for WebSphere, it’s QEJBSVR) has read/write authority to the directory /QIBM/UserData/OS400. The servlet will create and update a personal system list for each user using Pervasive and will store them in this directory.
4. Add MIME type—When using an Internet phone, an image is used in Management Central - Pervasive. In order for the servlet to be able to send back the bitmap, the HTTP server must know where it is located and how to handle bitmap files. To access the HTTP configuration, go to the 2001 port on the system running HTTP. Under the HTTP configuration, go to Request processing > Request routing for the HTTP instances being used. This Request routing directive must have specific values:
• Action: Pass
• URL template: /McYpvPervasive/*
• Replacement file path: /QIBM/ProdData/OS400/*
Next, go to Languages and Encoding > MIME Types, and enter this information:
• File extension: .bmp
• Content type: image/bmp
• Encoding: binary
• Quality: 1.0
5. Update server authority—The user profile running the servlet (for WebSphere, it’s QEJBSVR) will need *USE authority to the service program QYPVJNI in library QSYS.
Be sure that you have WebSphere running before trying these steps. The steps are required to make WebSphere work with Management Central - Pervasive. It will assume that you already have WebSphere configured and running.
For help on getting WebSphere configured, first try to get the HelloWorld servlet running. This will help you become familiar with WebSphere and will verify that the setup was successful. Once that works, follow the five steps to enable Pervasive. For more detailed help, be sure to look at the references at the end of this article for Web sites that offer helpful information. Management Central - Pervasive is a powerful new way to stay informed of your system’s status and performance. It gives you the flexibility to get the information you want from anywhere you want to be.
References and Related Material
IBM HTTP Server for AS/400 Web site: www.ibm.com/eserver/iseries/http
IBM Management Central-Pervasive Web site: www.ibm.com/eserver/iseries/sftsol/pervasive.htm
IBM Redbooks Web site: www.redbooks.ibm.com
IBM WebSphere Application Server Web site: www.ibm.com/eserver/iseries/Websphere
Coming Soon to Management Central
Can’t wait? Take a peek at Management Central in the near future. Youll be excited about the features Management Central will offer in 2001. Watch for these items in an upcoming version of Management Central:
• Manage users and groups across systems
• Package your products as well as files and folders and manage them across systems
• Monitor jobs, messages, and system performance from a workstation or wireless device
• View graphs of system performance history over long periods of time
• Perform actions on jobs listed in monitors from a workstation or wireless device
• Compare and update system values across systems
Figure 1: With Management Central - Pervasive, you can access OS/400 system status from an Internet phone, PDA, or a traditional Web browser.
Figure 2: By adding Management Central - Pervasive to its Management Central function, IBM now allows you to view the same monitoring information on several different devices.
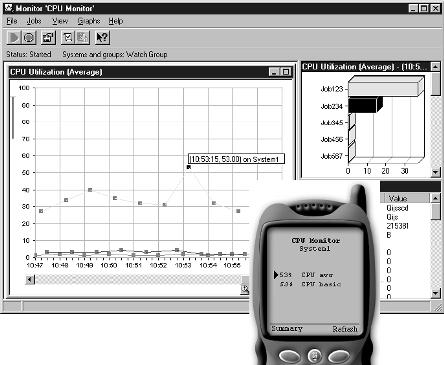

Figure 3: The Internet phone summary page tells you on at at glance whether all your systems and monitors are running smoothly.
Figure 4: The PDA version of Pervasive gives you more screen space to display OS/400 monitor information.

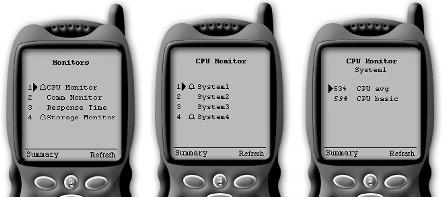
Figure 5: Metric names have been shortened in Pervasive so that you can see as much as possible on the small display sizes.
Phone Type Wireless Comments of Testing Service
Mitsubishi T250 device AT&T PocketNet Small font preference is recommended.
Ericsson R280 LX simulator n/a
Figure 6: Pervasive supports these Internet phones.
PDA Operating System Wireless Wireless
Modem Service
Palm V or Vx Palm OS Version 3.3 Minstrel V AT&T Palm III or IIIx Palm OS Version 3.3 Minstrel III AT&T
Figure 7: We tested Pervasive on these PDAs, but as long as your PDA can run one of the approved PDA Web browsers, that device should also work.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online