Author's Note: The following article is based on honest feedback we at IBM received from a non-IBM customer who is currently using non-IBM servers to run his business. We provided him with a presentation showing him all the great graphical functions that come with iSeries Navigator. After the presentation, he offered his impressions. We were quite pleased with his comments and asked permission to publish them. He agreed, and what came out of it was another exciting chapter in the iSeries Superhero saga. In this episode, we glimpse into the Dark Agent, an enemy of the Super Squad who wants one last shot at success, and what happens when he crosses paths with an iSeries. Enjoy.
The stench was palpable, but he was used to it. This was his home. It had been a long time since the rotting user interfaces and oozing documentation bothered Lu-fesu (Lu for short). The only thing that bothered him was not knowing what his next assignment was. Hour after hour he waited, looking out his decaying window of despair. If he could only get back into the game, he could prove once and for all that his dark powers were superior to those of his archenemies, those loathsome heroes of good systems management usability: the Super Squad. The last time he met the Super Squad was disastrous, but if he was given the chance, Lu would prove that he has what it takes to be a master of the dark systems management powers.
As he flicked the fungus off the window trim, he thought back to when he first discovered his dark powers. His childhood friends had joined the Systems Management Superhero Academy, but he had longed for a far more powerful life. He experimented in the dark systems management powers and eventually became a master. He could create network problems faster than anyone else and could wield performance hogging jobs in a way that no mere administrator could defend himself against. Soon he found himself on a number of top-secret missions, infiltrating unsuspecting IT shops and causing havoc. For the next few years, he spent day and night making hapless systems administrators writhe in pain by causing serious IT problems while knowing that those administrators had only the most basic GUIs to solve them.
Then, he faced off against the Super Squad...and iSeries. He had no idea the iSeries has so many powerful graphical tools. Soon after that defeat, his dark powers were brought into question.
The Assignment
The day the assignment came, Lu was just returning from a week-long conference called "The Fiend in You: 10 Ways to Make IT Management a Living Nightmare." It was a great experience and he learned a lot, but it made him yearn even more deeply for the chance to prove his powers. Seeing his former friends graduate from the Systems Management Superhero Academy Masters program was just adding salt to the already gaping wound in his pride. He needed to stop their actions!
As he opened his assignment, he trembled in anticipation...and he was rewarded. He grinned as the implications set in: He was to target the latest superhero in training: Admin Boy. By targeting Admin Boy, he could strike down the next generation of the Super Squad before he came into full power. Reading further, he learned that Admin Boy was struggling to keep his IT shop afloat. The Super Squad was scheduled to come in and help Admin Boy save the day, but not if Lu could help it. He would throw every problem he could think at them. By the time Lu was done, he would make Admin Boy cry in usability pain...and possibly lure him into becoming a dark agent.
The Confrontation
He stepped through his window of despair and arrived at the shop. He knew Admin Boy was new to this game, so he planned to throw a number of IT problems at him, knowing full well that since Admin Boy hadn't purchased any third-party software, all he had available was base-level operating system functions. Based on his past experiences, Lu was sure no base operating user interface could handle what he was planning. His heart was pounding in anticipation as he crept into the shop. He got into position and readied all his ammunition for the day.
Suddenly, his face went white with fear. This was all wrong! What he saw confirmed his worst nightmare: iSeries. The Super Squad had already been here and deployed iSeries systems across Admin Boy's network. Lu didn't know what to do. He was unfamiliar with the capabilities of this sleek machine, but the time for battle had come. He had no other course of action than to use his tried-and-true methods of IT destruction, so he launched his first attack.
Attack One: Installing and Managing a Purchased Database
Lu knew that most IT administrators had to contend with finding a database to purchase, installing it, fixing install problems and conflicts, and finally buying the tools to manage it. This problem was sure to hurt. To his surprise, this attack didn't even get out of the cannon. iSeries comes with the perfect defensive shield by including its own integrated relational database. There is no need to install anything or check for conflicts. "Buying a box that has an integrated DB that includes the license is a big deal," said Admin Boy. He continued by commenting that the graphical tools are similar to his old tools, but he'd had to buy those (including upgrades to newer versions). With the graphical database management in iSeries Navigator, he found all he needed without any additional purchases.
Peeking over Admin Boy's shoulder, Lu saw Database Navigator. The database was all laid out, showing the relationships between data sources, views, tables, keys, etc. as well as all the actions that could be performed on each database object. Admin Boy was even able to save different views of his database for future reference.
Figure 1: Database Navigator shows the relationships between data sources, views, tables, keys, etc. (Click images to enlarge.)
Lu even saw a Web link that Admin Boy could use to learn more about database and iSeries, as well as what was involved in porting data onto iSeries.
Attack Two: System Monitoring and Trouble-Shooting
Lu knew this next problem would strike home. It was simple, really. He would cause all of Admin Boy's printers to hang by filling up storage. Lu had been able to inflict this common problem in the past. In fact, he recalled a quote from an earlier raid:
"One of my servers ran out of free disk space on its C drive, although it had capacity on other disks within the machine. As a result, it couldn't spool print jobs sent from clients, and several printers hung up until I freed up some space.
"Without any third-party system management tools, there was no way I know of for the server to alert me automatically when the free space ran below a certain threshold. So I had to just deal with the problem when someone told me about it, rather than being able to correct it before it started impacting users.
"Some people would say you should regularly monitor the free space on every disk in every server you have. My take is that the machine should manage that for me and just tell me when it needs me to do something, such as free up or allocate more space."
Immediately, Lu knew the results weren't what he expected. This pesky iSeries Navigator had multiple monitors, and Admin Boy had set up a number of them to monitor all aspects of system health. They watched for thresholds to be exceeded and then ran automation to fix the problem before anyone even knew about it. In this case, Admin Boy's disk storage monitor detected a sharp rise in storage usage, so his automation program started archiving data and notifying owners of large files. Lu heard Admin Boy say, "I used to have no system monitoring tools unless I purchased a third-party tool. Not only is iSeries Navigator a cost savings, but it's meant for the iSeries and tightly integrated." He was able to not only run automation but also view graphs charting the system's health over a period of time. And when a peak occurred, Admin Boy could select the point, find the jobs causing problems, and change the job's properties or even hold the job.
Attack Three: Patch Management
Requiring security patches always gave Lu a sick sense of joy. Nothing was worse than managing patches, or fixes, on a traditional business system. Even worse was managing these patches across multiple systems. Surely it was as difficult on iSeries! Nope. He tried to find a security breach he could apply to the iSeries, but he couldn't find one! Hadn't this system ever been compromised, he wondered? So he invented a problem and placed it into three iSeries and sat back to see when Admin Boy would start crying. He never did. As soon as Admin Boy saw the problem, he used the iSeries fixes support to help him. Lu stared in horror as Admin Boy pulled out out-of-the-box iSeries tool after iSeries tool to help manage his patches.
Tool #1: Fix Central
Fix Central is a Web site where Admin Boy can search for, find, and download the latest fixes, either singly or as a series. Some are even group PTFs that combine fixes to solve one particular problem. Admin Boy was able to use a universal connection set up to talk between his iSeries and IBM, so he quickly downloaded the fix he needed with high-speed VPN access.
Tool #2: Install Fixes Wizard
Once Admin Boy downloaded the fix, he opened iSeries Navigator and set out to install the fix. He collected fixes inventory to verify the fix was downloaded and then clicked through a simple install wizard that was almost too easy. "The fact that it's built into the platform is great. For serious patch management in the past, I would have needed a third-party product," Admin Boy said. He immediately saw the results of the install and was very happy that the install worked and that the fix solved the problem. He also appreciated the built-in rollback capabilities on the iSeries. "Rollback of patches is huge," Admin Boy said with a grin. Now that it was installed, he could using the built-in inventory function to collect and export the list of fixes into a Web page for later analysis.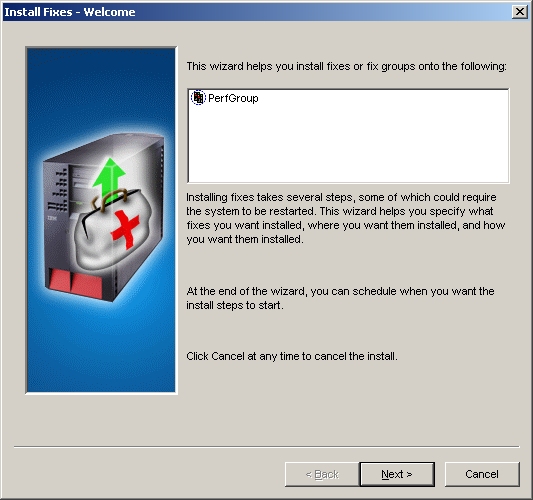
Figure 2: Use the Install Fixes wizard to install fixes quickly.
Tool #3: Compare and Update Fixes Wizard
Now that Admin Boy had installed the fix on one system, he used the Compare and Update Fixes wizard to find all the other systems that needed the fix. The compare results indicated that two other systems needed the fix, so he quickly ran the Update wizard. The fixes were sent to those systems and installed. 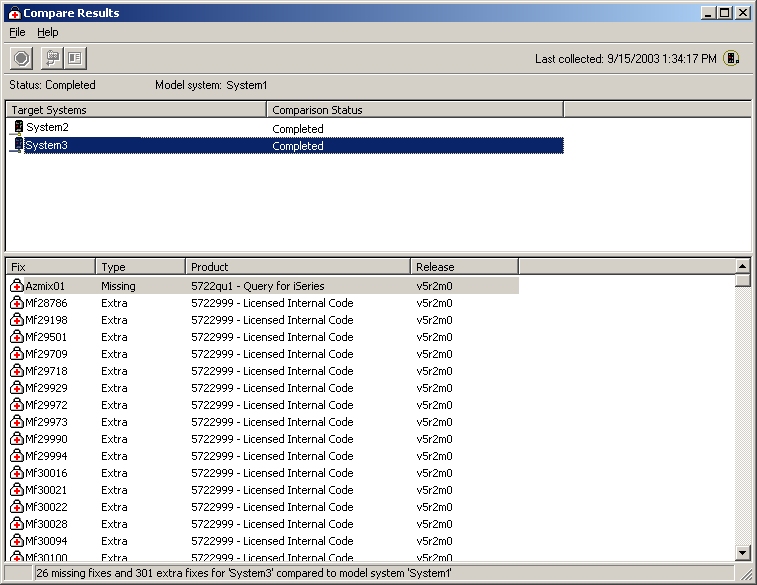
Figure 3: Use the Compare Results wizard to determine which other systems need fixes.
Lu was repulsed. Not only did his patch management attack fail to crack Admin Boy, it actually brought a smile to Admin Boy's face because he was starting to really enjoy solving all these IT problems in such an efficient manner.
Attack Four: Performance History
One surefire way to make an administrator fail in the eyes of his management is to give him systems with highly fluctuating performance levels. Lu knew that a common remedy was to increase the performance potential for the system, but that left much of the system unused except during those rare but highly needed times. Lu was sure that by making Admin Boy's systems vary over a long period of time, he would force Admin Boy to guess when those peak times would be and ultimately force him to upgrade his systems unnecessarily.
But Lu was in for a surprise. Admin Boy took hold of two powerful features of iSeries: Capacity On Demand (COD) and iSeries Navigator's Graph History. With Graph History, Admin Boy found an easy-to-read graph outlining how his performance had been over time. It was able to show performance over a day, week, month, year, or longer! Using this as a guide, he was able to accurately judge when he would need to use On/Off COD to temporarily activate the processors he needed, therefore paying for the upgrade only when he needed it. Admin Boy said, "Viewing these graphs is big, especially when tied to COD. Now, I can see when I need additional processing as opposed to guessing. It saves me from wasting money. I can get a handle on what resources we really need."
This one really made Lu's head spin. In fact, deep in the recesses of his mind, he started to doubt his devotion to the dark powers. He quickly squelched the thought, but not before his mind started to ponder whether there was a better life waiting for him.
Attack Five: Disk/Hardware Problems
Angry that he could doubt his life-long passion for inducing nightmares in IT shops, Lu launched the most lethal weapon in his arsenal: a disk problem. This was his favorite because it was the most elusive and destructive. This attack made a disk unit start to report problems but then stop after a period of time. The result was a very frustrated administrator and low data access due to the error correction and mirroring recovery that would be going on.
What Lu never counted on was a built-in graphical viewer where Admin Boy could view disk status in real time and take corrective action by simply selecting the picture of the disk unit and tower that was in trouble! Admin Boy said, "This may not seem impressive to the CIO types, but it's a big hit with administrators."
Figure 4: Use the Disk Units Graphical View to see disk status in real time and take corrective action.
What Lu also never counted on was actually being found out! Admin Boy, while searching for the disk unit in trouble, also ran his trusty "trouble-shooter" job monitor that looked for any job with a status of "waiting for locked object." The monitor notified him when any job appeared with that status; then, he could open the monitor window to see the particular job that matched the criteria. Upon viewing the job, he looked at the call stack and noticed that a program from a library called Useful was being called (which of course, is Lu-fesu spelled backward!). Admin Boy quickly launched countermeasures to stop Lu from getting away. Lu's proximity detector immediately went off, and the chase was on!
Attack Six: Problems While Not on Site
As a last-ditch effort to salvage the mission, Lu launched his remote IT-fire-starter daemon. Even though every single attack had been thwarted by this amazing graphical interface called iSeries Navigator, Lu thought that if he could cause a problem while leading Admin Boy on a chase through town, Admin Boy wouldn't be around to see this wonderful software light up when problems happened. Bursting outside into the alley, Lu hid behind a dumpster and activated the daemon. Instantly, Admin Boy's iSeries Navigator monitors lit up, indicating there were problems to solve. At last, Lu would succeed! Surely, by the time Admin Boy got back to his office, it would be too late to fix the problems that the daemon was causing. However, as Admin Boy passed the dumpster, Lu noticed he wasn't even looking around. He was looking at his phone! What could that mean?
Good gracious! Wireless access! Admin Boy had iSeries Navigator for Wireless running! Lu couldn't believe the rich set of functions and tools available to Admin Boy. He watched in defeat as Admin Boy received instant updates from iSeries Navigator monitors and tasks. Not only did Admin Boy see the problems that his monitors and tasks were reporting, but by using iSeries Navigator for Wireless, he could hold and end jobs, reply to messages, run command definitions from his run book, and even run any batch command or program right from his Internet-capable phone. As an extra bonus, Admin Boy was even able to run commands to his integrated xSeries servers inside his iSeries. Admin Boy grinned as he said, "This sure makes my life easier."
Lu knew he had lost. How could he compete against a superhero with the kind of tools provided by iSeries?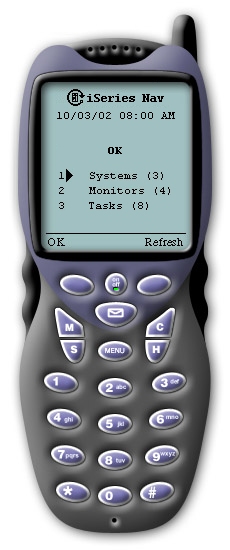
Figure 5: Use iSeries Navigator for Wireless to handle problems when you're away from the office.
Epilogue
Lu and his daemons were quietly rounded up. Utter defeat prevented any further attacks by Lu. Later that week, as Admin Boy accepted his Superhero Academy graduation pin, he said, "I knew iSeries Navigator was powerful, but I had no idea it could do these kinds of things." From that point on, Admin Boy kept this powerful systems management tool by his side. As he walked off the podium, he continued, "I love having integrated tools I don't have to buy."
As for Lu, he was sentenced to the Dark Agent Reform School, where he nurtured a new-found respect for iSeries that helped him grow into a respected analyst. He regularly worked for the Super Squad, decoding messages from other dark agents and developing ways to thwart the endless attacks on administrators using the rich, powerful functions of iSeries Navigator.
Additional Resources
To find out more about iSeries Navigator and other system values information, go to the following links: iSeries Navigator and iSeries Information Center.
Greg Hintermeister is an eServer user interface designer at IBM Rochester and has worked extensively with iSeries Navigator, iSeries Navigator for Wireless, and several Web applications. You can reach him at





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online