Companies interested in improving their IT department's effectiveness recognize ITIL's contribution in optimizing IT processes and thereby providing better service for their users.
Editor's note: This article is an extraction from the free white paper "ARCAD and the ITIL Framework," which is available at the MC White Paper Center.
Companies that are concerned about the effectiveness of their IT organizations can take advantage of best practices models such as the IT Infrastructure Library (ITIL), the Capability Maturity Model (CMM), and Control Objectives for Information and related Technology (COBIT) to help them evaluate and improve their processes. Let's take a look at the advantages of adopting the ITIL framework in your organization.
For more than 25 years, ITIL has provided an outside perspective and a practical guide to assist companies in optimizing their IT processes. Use of the ITIL model is growing; it has become a de facto standard for a growing number of companies throughout the world. It is, above all, the basis for a business culture of service. It provides factors for improving your organization when and where you need it.
Today, users have become genuine clients. The day is over when the IT expert could hide behind his intimidating technology to impose his views on the user. IT specialists must see users as demanding clients who deserve a satisfactory level of service.
Previously, IT services were constantly in reactive mode. People ran from one problem to the next while trying to maximize service. This is not sufficient today. We expect people to be proactive--in other words, to plan for problems rather than have to correct them. This change in viewpoint is essential to really understanding the spirit of ITIL.
Cultural Change
If you retain only one word from ITIL, it should without a doubt be "service." In ITIL, all of the activities of an IT department are identified as services. This approach is extremely useful because IT experts always tend to focus more on technology. It is time to start thinking, above all, of the service provided to the user, rather than of the technology that provides this service.
The objectives in an ITIL implementation can be numerous and vary from one company to the next. However, it is possible to distinguish three that are fundamental:
- Align IT services with the current and future needs of the company and of its clients.
- Improve the quality of services provided to the user. If we maintain excessively "manual" methods when faced with the rising tide of user needs, it is impossible to provide a satisfactory level of service.
- The third objective is medium- and long-term cost reduction. A better-organized IT department is more efficient and is thus less expensive.
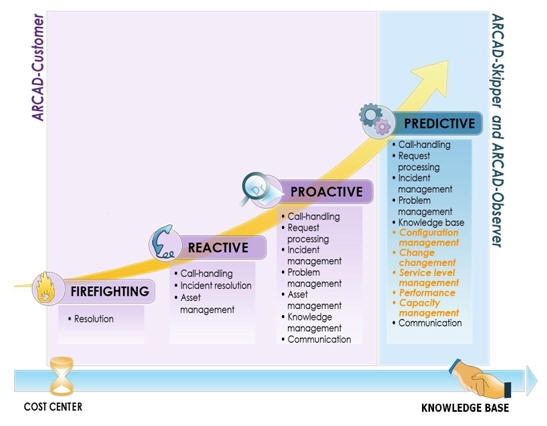
The diagram in Figure 1 could be called "the maturity progression curve for an IT department." It clearly illustrates the different steps in implementing processes in order to transition from a reactive to a proactive mode. This transformation is a required to ensure that IT in a company will no longer be considered as a cost center, but as a services center.
Figure 1: This diagram illustrates the maturity progression curve for an IT department. (Click image to enlarge.)
Initial Steps in Adopting ITIL
The first step is documentation. You will find a substantial amount of information on the site of the organization responsible for promoting the ITIL model, itSMF. The site brings together documentation, events, and players in this field.
After this documentation step, you will need training, and you will need to train other professionals in your organization. In this area as well, there are numerous organizations standing by to help you.
You can finally get started with ITIL by leveling all of your processes and by detecting those that appear to be the weakest. It is always a good idea to recall that the strength of a chain of values is only equal to the force of its weakest link.
ITIL Processes
ITIL divides IT department processes into two categories:
- Support for services can be summarized as everything that ensures the correct functioning of services.
- Provision of services concerns all processes related to making services available under good conditions.
The services support category encompasses the following:
- Incident management
- Problem management
- Configuration management
- Change management
- Release management
The service provision category comprises the following:
- Service-level management
- Financial management for IT departments
- Capacity management
- Service-continuity management
- Availability management
We suggest that you brush up on, one by one, all of the processes that constitute the services support section.
Incident and Problem Management
These are unquestionably companies' most advanced processes in their implementation of ITIL. Why is this? Because companies have to start somewhere, and the benefits created by the processes are clear.
Configuration, Change, and Release Management
The processes of configuration, change, and release management are intended to improve organization around change phases. Information technology undergoes changes of all kinds in terms of equipment and even more so in terms of software. This constitutes the main difficulty in automating processes in our line of work. What is the best way to consolidate an organization when everything is constantly changing around you? By mastering change.
Configuration Management
This process consists of identifying, in a unified manner, all of the components of an IT department, whether these components are software, equipment, network, or others. It is also important to identify all of the inter-relationships between these components. This will result in the establishment of a repository. In ITIL, this index is called a Configuration Management Database (CMDB). From the moment this repository is created, all successive configuration stages can be managed, controlled, and audited.
Change Management
In the case of software, change management provides a framework for the entire application change process during the development phases. Fundamentally, the need is simple: to ensure coordination between developers who often work on the same components at the same time. When performed manually, this task is tedious, time-consuming, and not very reliable.
The simple initial idea is to create a single code repository from which all new development will come and then add to it a component allocation system (the check-in, check-out principle). This mechanism allows a natural dialog to be established when two developers have to modify the same source code. It avoids any potential regression situations that could result.
Release Management
Change management is the act of changing. Release management is the act of transferring changes to production. This process can rapidly become extremely complex in terms of technology, because it often involves different technologies--in terms of security because care must be taken not to degrade established rules (permissions, ownership) and in terms of organization because a number of players are involved. For example, users must be informed before and after the execution of transfers to production. They may need training on this new release.
It's ITIL for Effective IT
When you start an ITIL implementation process, it is essential to sound out the tools. The contribution of software tools in each of these process areas is clear:
- Service desk
- Incident management
- Problem management
- Change management
- Release management
- Service-level management
Companies that are concerned about improving the effectiveness of their IT organizations recognize the positive contribution that ITIL makes in optimizing IT processes and thereby providing better service for their users.
To learn more, download the free white paper "ARCAD and the ITIL Framework" from the MC White Paper Center.





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online