The Internet provides various protocols for network communications. Two popular protocols are HTTP and FTP. Microsoft exposes both of these protocols via the Win32 Internet (WinInet). WinInet is an API for Internet communications on the Microsoft platform and is contained within the wininet.dll file. Microsoft’s Internet Transfer Control (ITC) is a Component Object Model (COM) wrapper for the WinInet dynamic link library (wininet.dll). It can be used from any COM-enabled environment to communicate using the HTTP, FTP, Gopher, and HTTPS, (Secure HTTP) protocols. In this article, I will describe how to incorporate the ITC into a sample Visual Basic application and do an HTML form post to Midrange Computing’s Web search engine. The results received from the search engine will be raw HTML, which I will parse and display in a VB list box. The VB application for this article can be downloaded at www. midrangecomputing.com/mc.
The Internet Transfer Control
The ITC provides synchronous and asynchronous Internet communication. Using the Open URL method is synchronous, while using the Execute method is asynchronous. This article uses the Execute method. During an asynchronous request, you can monitor the ITC’s StateChanged event to watch underlying network activity. You must write code for this event in order to capture the results returned from the Web server.
The sample VB application provides the same search capabilities as the HTML form found at www.midrangecomputing.com/ search. This application provides a Windows GUI interface to the search engine. The sample app posts to the same process page as the HTML form and includes all form fields, including hidden fields. In this way, the process page treats the request as if it were coming from the standard HTML interface.
Before using the ITC, verify that you are using the latest version of msinet.ocx, the Microsoft Internet Transfer Control. I developed the sample application using the version that came with Visual Studio Service Pack 5 (version 6.00.8862). If you are unsure which version you have, you can find the latest version included free of charge in Visual Studio Service Pack 5. Service Pack 5 is chock-full of bug fixes—133 MB, to be exact. Nothing builds more confidence in the software you run than 133 MB of bug fixes. It is cumulative, so you don’t have to start at Service Pack 1.
Take Me to the Code
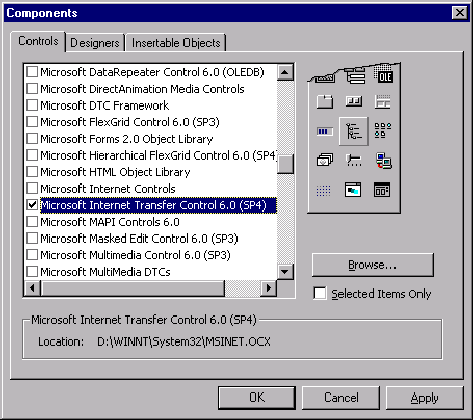
To use the ITC, start VB and select a Standard EXE project. Press Control-T, scroll down, and select Microsoft Internet Transfer Control. Figure 1 (page 69) shows an example of this screen. If the list of controls is missing or small, make sure to uncheck the Selected Items Only check box in the lower right section of the dialog box.
Now that VB has a reference to the ITC, you can place it on a form by selecting Toolbox from the View menu. Double-click Form1 from the Project window to display the form. Now, double-click on the Inet control in the Toolbox. This will put a single control onto the VB form and name it Inet1. This control is invisible during runtime and is only visible during design time.
You now have access to the ITC control and can begin writing code to post an HTML form. The sample application has six important controls: an ITC named Inet1 that handles all Internet communications; a text box named txtSearch that allows you to type a search string; a combo box named cboArea that allows you to select which section of Midrange’s Web site to search; a text box named txtResults where you place the raw HTML results retrieved from the form post; a list box named lst Results where you place parsed search results; and, finally, a command button named cmdSearch that submits the form.
As you can see in Figure 2 (page 69), adding code to the Search button’s Click event allows you to submit your search form to the search engine. The forms search criteria must be set by concatenating a string variable that represents the area to search, based on the combo box selection, and the keywords to search for, based on the value typed into the txtSearch text box. This string is passed, along with the URL www.midrangecomputing.com/ search/search1.cfm, and the HTTP header Content-Type: application/ x-www-form-urlencoded, to the ITC’s Execute method. This method submits the form to the search engine.
Since the Execute method is asynchronous, the application must contain code in the ITC’s StateChanged event. This event allows monitoring of network communication activity of the control; see Figure 3 for an example. The ITC’s GetChunk method is used when a state of icResponseCompleted is received in the event. The GetChunk method allows you to read a certain number of bytes from the buffer. One caveat is that during development, break points disable the StateChanged event. The event simply does not happen if a break point is in either the cmdSearch’s click event or the ITC’s StateChanged event.
Parsing Results
The ITC returns only raw HTML source. It does not return embedded images, sounds, or multimedia, but rather the URL to those resources. If you wish to retrieve that content, you must parse out the URL and use the ITC to download in a separate Execute or OpenURL request.
In this case, once the search form’s results are returned, it has to be parsed for the desired data. Parsing data simply means taking the results (HTML-formatted ASCII), looking for and retrieving the desired data, and ignoring the rest. To find the search form’s results, it is necessary to view the source code of the returned page. One of the easiest ways to do this is to copy the contents of the txtResults text box into your favorite HTML editor. Find the search results text within the HTML source. Now, look for a tag that is unique and to the left or above the search results. Near the search results text, there is an HTML
not the focus of this article, but there is an example in the sample download. Take a look at the ParseResults procedure in the sample application.
One problem that can arise from parsing text of a Web page is that the page may change. If a page’s HTML is changed in any way, there is a chance that the parsing routine used to extract the results will fail. The Midrange Computing example searched for a value of 89 percent that was located next to the desired search results. If Midrange Computing changed the Web page such that 89 percent changed to 88 percent, the parsing routines would fail. If you are parsing an intranet, you probably have more control, but Internet sites can and do change at various intervals, and often without warning.
This article provides a general example for one possible use of the ITC. Using Visual Basic and the Internet Transfer Control makes it fairly easy to communicate over the Internet, and this control can provide programmatic solutions for many applications that rely on network connectivity and communications. The ITC makes it possible to write an application that does anything from polling a Web server for connectivity to periodically polling for a stock price to transferring files.
Figure 1: Select Microsoft Internet Transfer Control 6.0 to add the OCX to your Visual Basic project.
Private Sub cmdSearch_Click()
Dim strURL As String
Dim strFormData As String
' Post to the form's process page.
strURL = "http://www.midrangecomputing.com/search/search1.cfm"
' Include all visible and hidden form fields and values
strFormData = "searcharea=" & SearchArea & "&criteria=" & _
Me.txtCriteria.Text & "&StartRow=1"
Inet1.Execute CStr(strURL), _
CStr("POST"), _
CStr(strFormData), _
CStr("Content-Type: application/x-www-form-urlencoded")
End Sub
Figure 2: The Search button uses the ITC to submit the form’s values to the search engine.
Private Sub Inet1_StateChanged(ByVal State As Integer)
Dim strMess As String
Dim vtData As Variant
Dim strData As String
Dim bDone As Boolean
‘ helps us to see what is going on while retrieving results.
ShowState = State
Select Case State
‘ Retrieve server response using the GetChunk
‘ method when State = 12. This example assumes the
‘ data is text.
Case 12
strData = “”
bDone = False
‘ Get first chunk.
vtData = Inet1.GetChunk(1024, icString)
DoEvents
Do While Not bDone
strData = strData & vtData
DoEvents
‘ Get next chunk.
vtData = Inet1.GetChunk(1024, icString)
If Len(vtData) = 0 Then
bDone = True
End If
Loop
‘ place the raw results recieved into a text box on the VB form.
Me.txtResults.Text = Trim(strData)
‘ Parse the raw HTML to retrieve the search results
ParseResults CStr(Me.txtResults.Text)
ShowState = Me.lstResults.ListCount & “ results found.”
Case 11 ‘ error!!
‘ Get the text of the error.
Me.txtResults.Text = “ErrorCode: “ & Inet1.ResponseCode & _
“ : “ & Inet1.ResponseInfo
End Select
End Sub
Figure 3: The ITC’s StateChanged event allows you to monitor asynchronous transfers and take programmatic action upon state changes.



















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online