Speed up your search with the free, open-source JCRLKEY utility.
Why open source? Real simple. I use most of these pain-eliminator tools on the job every day to save myself time and effort. As I stated on my website, many people around the world have made excellent suggestions for improvement or enhanced functionality to meet their specific requirements. After making a requested modification, it invariably winds up with the tool being even more useful to me!
The other thing I have noticed is you meet a lot of people with more experience than yourself in many specific areas. It is has helped my performance to converse and link with these people to understand how they are using these utilities.
None of the tools on the website were written because I like writing utilities…well, yeah, I do. You always have to balance the time and effort it takes to write a utility compared to the lifetime of pain and suffering you will endure if you do not write the utility. In the case of open source, someone has saved you the time by already writing the utility, you get the immediate benefits, and—big plus—you can modify the tool to meet your specific need.
In this TechTip, I'll go into details on just one of the tools, JCRLKEY, which will definitely speed up your search for which logical file you can use and can cut the number of new logicals being created as you can now easily find the path you need. If you're in large shop with restrictions on logical file creation, then this is also a great tool for the database administrator to see what is already out there.
At some point in our careers, we have all inherited a logical file soup with some physicals having 200 or many more logical files (something we would never do!). How on earth can we find a logical with the access path we need and determine what select/omits were used? I suspect one of the reasons we have this mess is that it's easier to create a new logical than spend half a day or more trying to find something you could use.
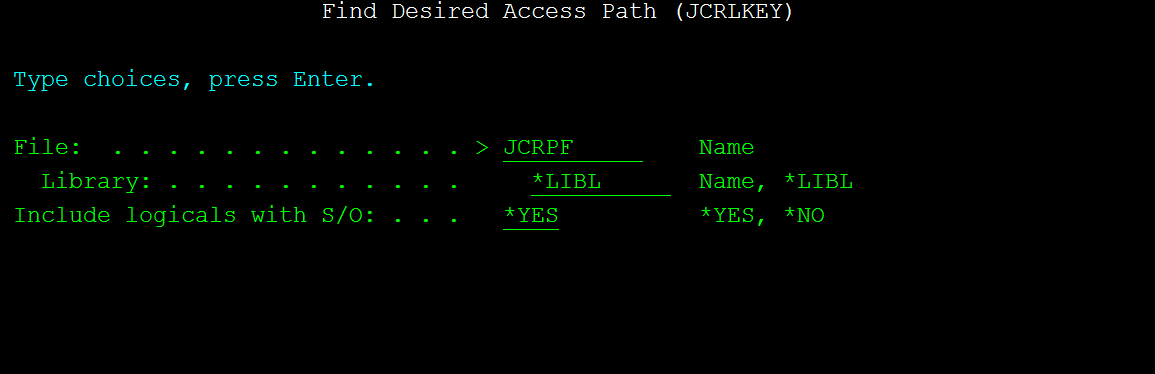
Enter the name of the physical file or any of the logical files named in JCRLKEY (leading key) as shown in Figure 1.
Figure 1: Use the command prompt for the JCRLKEY command.
The command will prompt you to select the keys, and then it will list every dependent file meeting your selection criteria. You can also choose to exclude files with select/omit from your search.
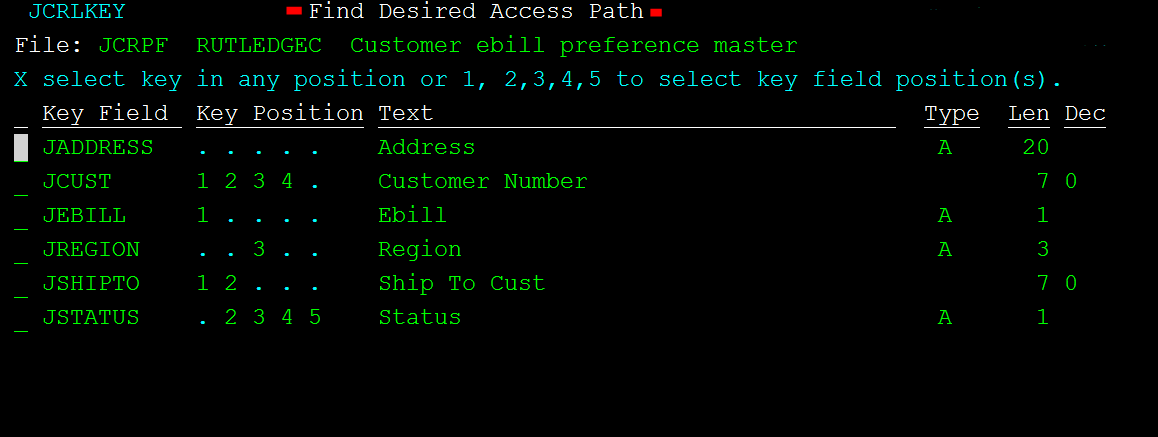
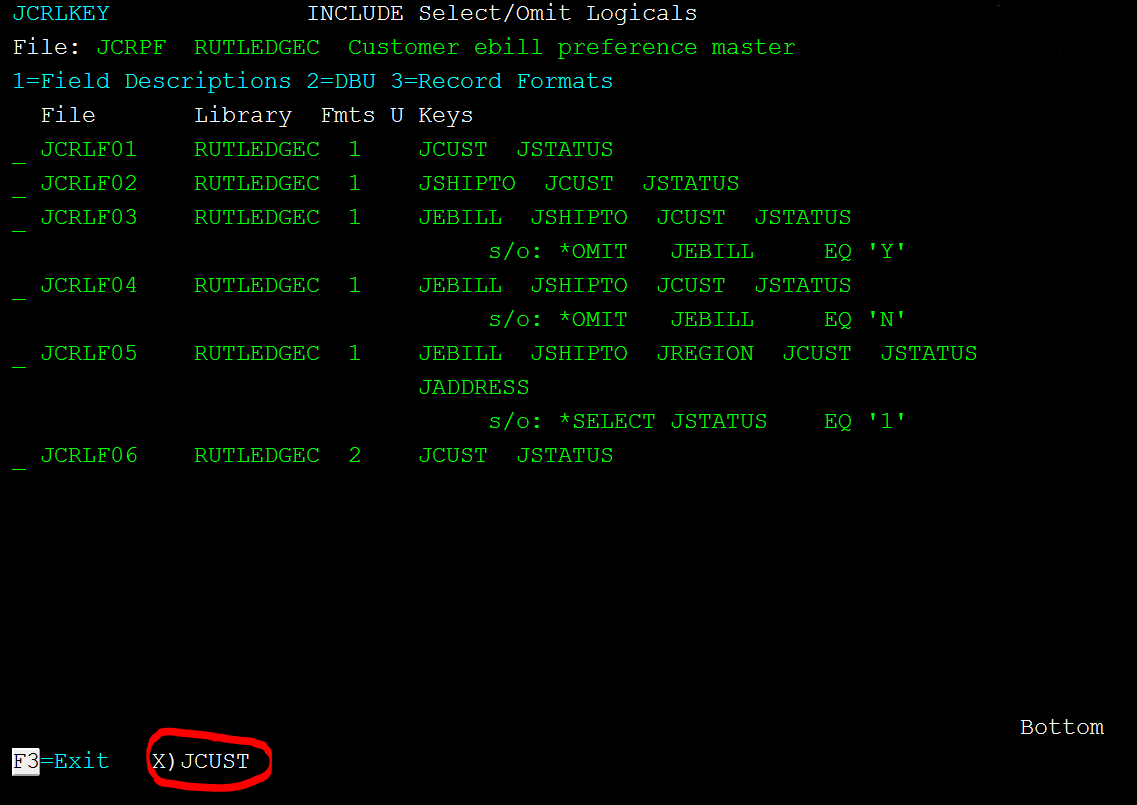
As shown in Figure 2, the command shows a subfile of all keys over the selected file and all database relations (logicals) of that PF. You can select a field in any klist sequence or selected klist sequence to show the desired logical.
Figure 2: This shows the entire Key Selection screen.
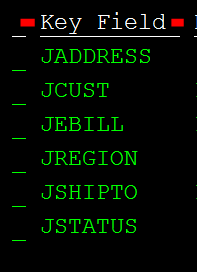
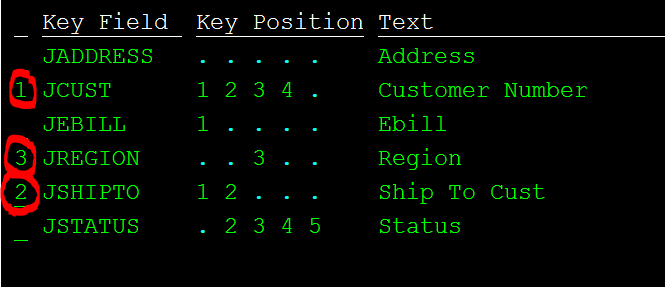
The first column of data, shown in Figure 3, lists the field names that are keys in the selected file set (file set meaning the physicals and all logical files related to that physical file).
Figure 3: This image shows the list of key fields.
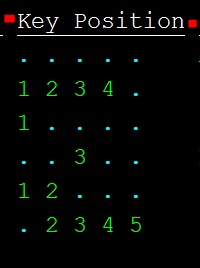
Figure 4 is where the second column shows the relative position of that field in any of the key lists. For example, the second entry shows a 1,2,3,4. That field is used as the first key or it has a key in front of it, so it is the second key and so on for any of the files in this file set.
Notice that the first key field is not showing any numbers; this means the field is a key but only in the sixth and beyond relative position.
Figure 4: This image shows the ordinal number position of the key.
The F7 function key at the bottom of the screen, shown in Figure 5, toggles the display to show the keys from logical files with select/omit values. Or press F7 again and you see only keys from files without select/omit. This is a good function key. How many times have you found what you thought was the perfect logical only to find the select/omits messed up your perfect vision?
Figure 5: Use function key F7 to include or exclude logical files with select/omits.
Figure 6 is the good part; notice the options you have to select beside the subfile entries. If you want to list access paths that have your selected key field in any relative position, place an X beside the field and press Enter. This is also the way to select logical files with the key in the sixth or greater position.
If you want the find a logical with your field as a key in the first position, put a 1 into the selection option and press Enter.
Figure 6: Use your selection options.
Here's a really neat feature. Suppose you need a specific field in the first position, a specific field in the second position, and the other field in the third position. As shown in Figure 7, simply number the subfile entries in the desired key sequence and press Enter. A list will be shown of any access paths with keys in that sequence of positions.
Figure 7: Select the sequence of keys you want.
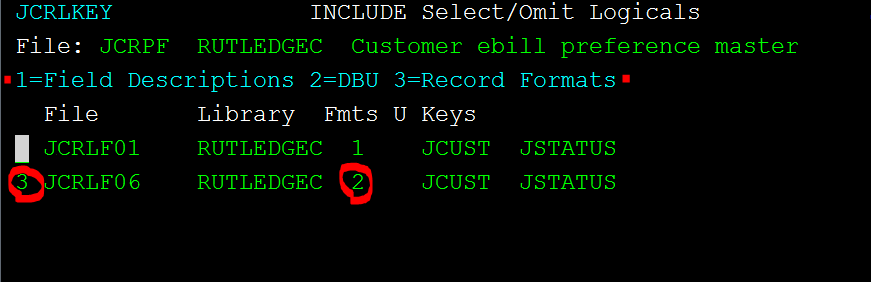
After you make your selections and press Enter, notice the options available on the logical file list shown in Figure 8. If you have DBU or WRKDBF installed, option 2 will execute one of those utilities.
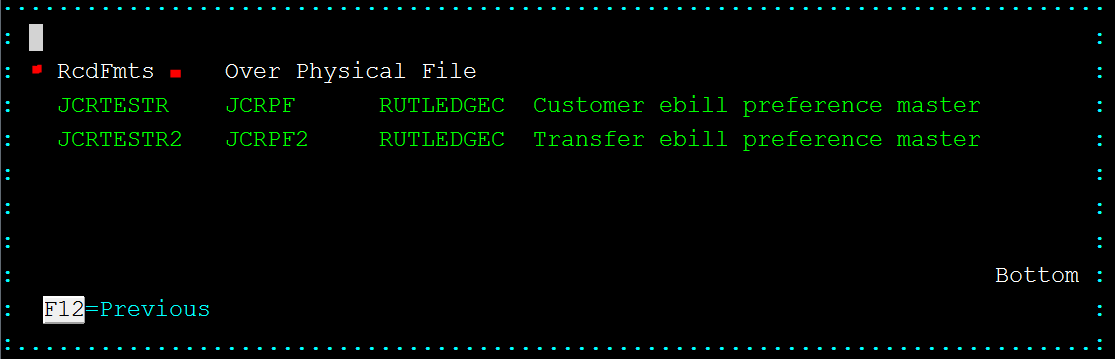
Option 3 to show record formats was a requested feature that I have also found useful. If your logical is built over multiple physicals, this option will show the different record formats and the physical file names as shown in Figure 9.
Figure 8: Select option 3 to see record formats.
Figure 9: See the record formats contained in the selected logical.
The bottom of Figure 10 shows what key you selected and what option you used to select it. In this case, I said I want see all paths with field JCUST in any position.
Figure 10: This is the list of access paths that meet your selection criteria.
There are many other free, open-source tools on my website. The help text displayed for each utility describes what it does.
For the record, get written permission from your employer or get a timeshare account before publishing any code. I had my own AS/400 back when, which was cool, but for past many years these tools have been written and maintained on much more affordable Internet time share developer accounts. If you have some ideas or code to publish, these accounts are great. These tools are maintained at TimeShare400.












 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online