Inherited authorities can be a hidden vulnerability if not carefully controlled.
Everyone loves an inheritance! Imagine the excitement of discovering that a long-lost uncle has left you a fortune. Or perhaps the recent Royal Wedding has you wondering where you are in the line of succession for the throne of England! While these possibilities are a long shot for most of us, you can inherit power on IBM i using the age-old IBM i facility called "group profiles."
Basically, a group profile links users with similar security requirements. It allows a security officer to quickly define object authorities that automatically apply to all group members.
Creating a Group Profile
A group profile starts as a regular user profile, created with the CRTUSRPRF command. The promotion to group status comes when another user profile (the member) references the group profile. Having one or more member profiles pointing to a group profile makes it a group. (To simplify things, a group profile can't be a member of another group.)
A user can be a member of 16 groups—one primary group and up to 15 supplemental groups. Typically, you don't want a profile to be in more than a few groups. It just complicates things when you need to determine the order in which to list the groups.
Benefits of Group Profiles
The biggest benefit comes from increased efficiency. Defining the authority of a group to an object also defines the authority of each group member. You don't have to authorize each group member individually. And, if people join or leave a role, you just add or remove them from the group.
You can assign authority to an object based on the group, and you can override that authority by defining authority for individual members. IBM i checks an individual's authority before checking the group authorities. If you define a private authority for user, the user gets that level of access and the group's authority is not checked. If the user has no individual authority specified, IBM i checks the group authority. If the user is in multiple groups, the authorities of each group are consolidated. For example, if Group 1 has *EXCLUDE authority and Group 2 has *USE, the user's authority is *USE.
You also can specify whether the member's primary group profile should own new objects. This allows other members of the group equal access to the objects. Alternatively, individuals can own the objects they create and define the amount of private authority for other group members.
Follow the Chain of Inheritance
One important thing to remember about group profiles is that a group's special authorities are inherited automatically by all group members. This is in addition to a member's own special authorities. So, if a member profile has *SECADM authority, and one of its group profiles has *ALLOBJ and another has *JOBCTL, that member effectively operates with *ALLOBJ, *SECADM, and *JOBCTL authorities. This inheritance extends to all groups a member belongs to. While this can be beneficial, it also can have serious implications to the capabilities of the members. For example, it's possible for members to grant themselves authority to a restricted file by using the group's *ALLOBJ authority.
Documenting this "chain of inheritance" is a challenge. Audits can miss that a seemingly benign user is actually running with powerful inherited authorities, like *ALLOBJ. The operating system offers only rudimentary reports to display the relationship between a user profile and its associated group profiles.
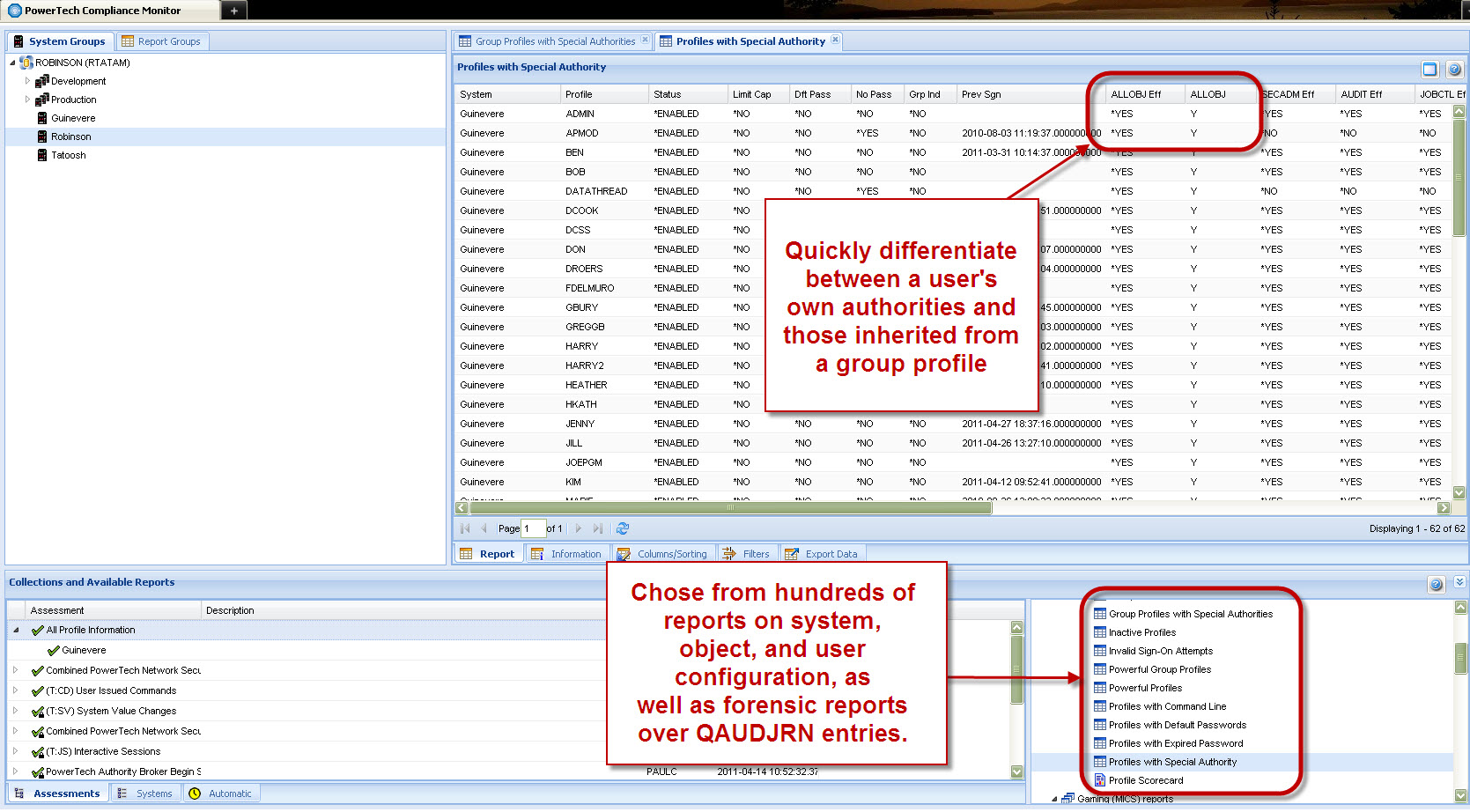
PowerTech Compliance Monitor eliminates the time and effort needed to determine a user's true power (see Figure 1). Predefined reports identify powerful users—and indicate whether special authorities are inherited from a group. Flexible report filters allow you to define additional criteria, such as command line access or whether the profile hasn't been used recently. Plus, Compliance Monitor can report this information across all your systems and partitions with a single request.
Figure 1: PowerTech Compliance Monitor reports allow you to customize, filter, and export data to satisfy compliance requirements. (Click image to enlarge.)
Group profiles simplify authorizing users to objects and make your security infrastructure more efficient. Compliance Monitor helps ensure that those groups provide the member profiles with appropriate inherited authorities.
For more information on Compliance Monitor, or any of PowerTech's line of security solutions, visit www.powertech.com.
as/400, os/400, iseries, system i, i5/os, ibm i, power systems, 6.1, 7.1, V7, V6R1




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online