Find out why security officers represent your greatest security threat.
OK, I know that the title of this article is probably going to upset some people. After all, I'm a professional security officer and make a good living helping customers secure application environments from both external attacks and "inquisitive" end users. So why would I be so willing to throw my own profession under the proverbial bus? It's actually quite simple. I truly believe that the security officer (SO) represents the biggest threat to many shops. To make matters worse, I will extend my definition of SO to include programmers and system administrators.
The sad reality for a lot of organizations is that many regular users are fulfilling a security role without any formal training or experience. They are the users who "know the most" and so become responsible for administering security for others. According to PowerTech's annual "State of IBM i Security" study, many users carry powerful capabilities without having any associated business requirement. But, even when the staff is trained or specifically hired because of their skills in this discipline, there is still major exposure.
As with most illegal or illicit activities, a perpetrator usually has a combination of means, opportunity, and motive. Let's discuss each of these as they apply to security personnel.
Means
When I talk about means, I'm referring to the skills and the knowledge to be able to perform specialized system tasks. Security officers and other power users (such as programmers and administrators) typically possess advanced skills to be able to access applications, manipulate private application data, and configure system controls—including those that manage the security of the server. Having worked on the "i" platform for 20 years, in numerous roles from systems programmer to security officer, hardware engineer to auditor, I've learned many shortcuts and workarounds. If there is a loophole in your security infrastructure, I can probably find it—and that means that my fellow SOs probably can too!Opportunity
As the most powerful users on the system, security personnel are presented with constant opportunity. Special authorities, such as *ALLOBJ, grant complete and uncontrollable access to every object on the system. And what programmer or SO doesn't at least request that level of access? Who knows enough to argue the reality of "necessary access" with a programmer or security officer? To make matters worse, command line restrictions are tough to enact for this group, since you can't secure and maintain a server without running commands.Motive
The lack of motive is the only saving grace for most organizations. As system guardians, most SOs take their responsibility seriously. But we are also human. The last couple of years have been tough on most industries, and I think a person would be naive to think that fear of job loss doesn't impact ethics. We all like to believe that nothing could ever compromise our scruples, but that mortgage payment and college tuition bill isn't going to pay itself. I don't wish to dwell on a negative aspect, but the bottom line is that people will usually put family and personal responsibilities before corporate responsibility. As a security officer, it is my professional responsibility to acknowledge that I need to be secured as much as—actually more than—the data entry clerk. My position is not above reproach, and I need to ensure that the security controls that I establish pertain to everyone.Finding the Balance
PowerTech Authority Broker is an award-winning solution from the leader in IBM i security solutions. Designed from the ground up to provide a secure environment for powerful users, Authority Broker easily satisfies even the most stringent audit requirements. Authority Broker helps you offset auditor concerns by removing day-to-day access to secure resources and powerful functions, yet it accommodates administration needs by enabling key personnel to continue to perform critical tasks. Working in conjunction with IBM's own auditing capabilities, Authority Broker provides on-demand access to an unlimited number of pre-authorized FireCall profiles, including QSECOFR, in both batch and interactive environments. But, unlike the operating system, Authority Broker comes with usage controls and notification, timing restrictions, and secure activity tracking and reporting (see Figure 1).
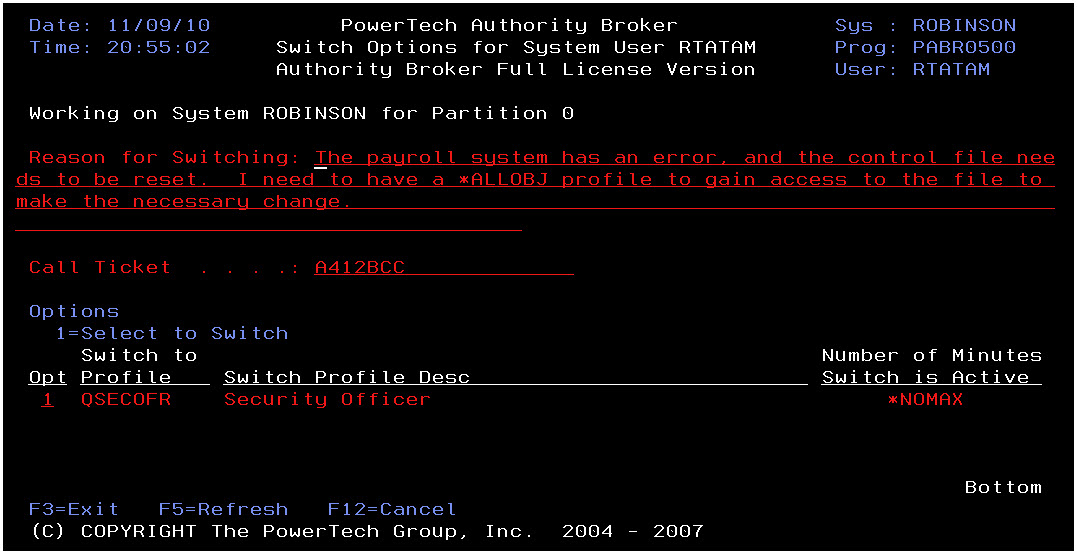
Figure 1: Authority Broker permits users to elevate authority in a secure manner. (Click image to enlarge.)
Simply put, if you have powerful users, you need Authority Broker. Click here to request a FREE Authority Broker Information Kit.
as/400, os/400, iseries, system i, i5/os, ibm i, power systems, 6.1, 7.1, V7,




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online