PowerTech Compliance Monitor scorecards make easy work of a tedious, but critical, task.
One of the most common requests I receive from customers is a way to provide the management team and auditors with a simple dashboard-type report of a system's configuration and its conformance with a baseline policy. For single systems, this can be a time-consuming task, prone to human error. When there are tens, or even hundreds, of system partitions, the work involved can become prohibitive.
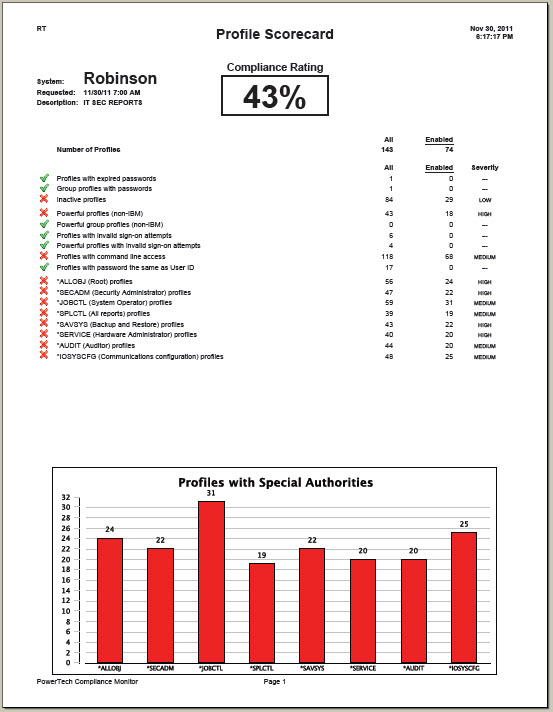
The same holds true with the analysis of the user environment. In addition, many auditors still don't realize they're missing profiles that are inheriting powerful capabilities from one or more group profiles. It's critical that a profile review also includes those users who might qualify by gaining capabilities via this inheritance.
What these customers need is a scorecard report, ranking the vulnerabilities in the system configuration and user statistics and comparing them against a customizable baseline. The scorecard needs to clearly indicate if the system is "in compliance" and provide areas of focus if it's not. Of course, detailed information needs to be accessible for those problem areas.
Compliance Monitor has become the mainstay in hundreds of IBM i shops around the globe. This is due partly to its unparalleled ability to deliver hundreds of granular reports on system values, user profiles, and object authorities, as well as provide forensic analysis of the entire collection of audit journal entries from IBM and PowerTech. But sometimes you just want a simple summary report. Fortunately, the powerful analytics engine of Compliance Monitor allows you to create scorecards designed specifically to rate the state of compliance. If you're not a security expert, rest assured that PowerTech provides a preconfigured baseline based on experience gained over 15 years as the IBM i security leader. If you have your own policy directives, you can customize that initial baseline to your own unique requirements. This includes the ability to maintain multiple policies, perhaps to accommodate different regulatory standards, different geographic boundaries, or simply the role of a partition.
To run one of the preconfigured scorecard reports, start by logging in to the Compliance Monitor browser interface and right-clicking the partition you want to analyze. You can simplify your reporting by associating related partitions in a virtual system "group," making the selection of multiple partitions a one-click task. From the fly-out menu, select Request Assessment (see Figure 1).
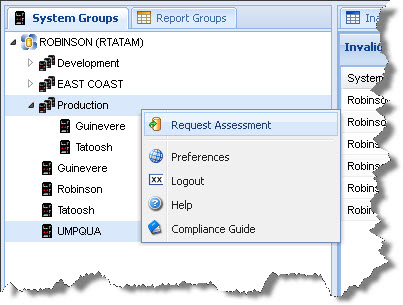
Figure 1: Select the systems and request an assessment.
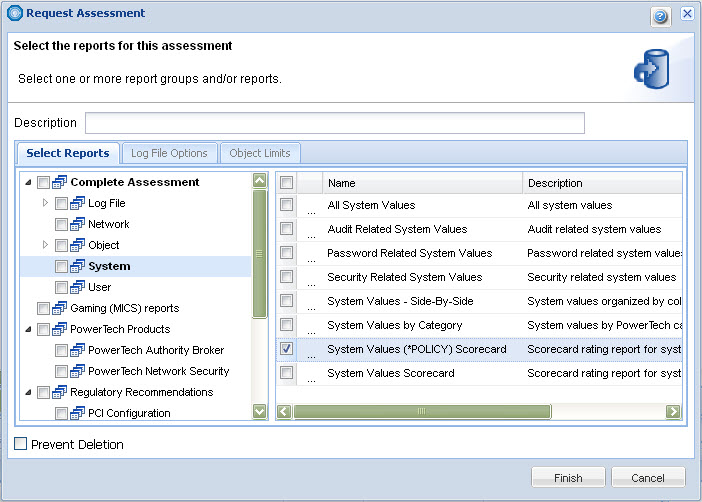
From the extensive list of available reports, select the System Values Scorecard under the System category and the Profile Scorecard under the User category (see Figure 2).
Figure 2: The Compliance Monitor report categories house hundreds of critical reports. (Click images to enlarge.)
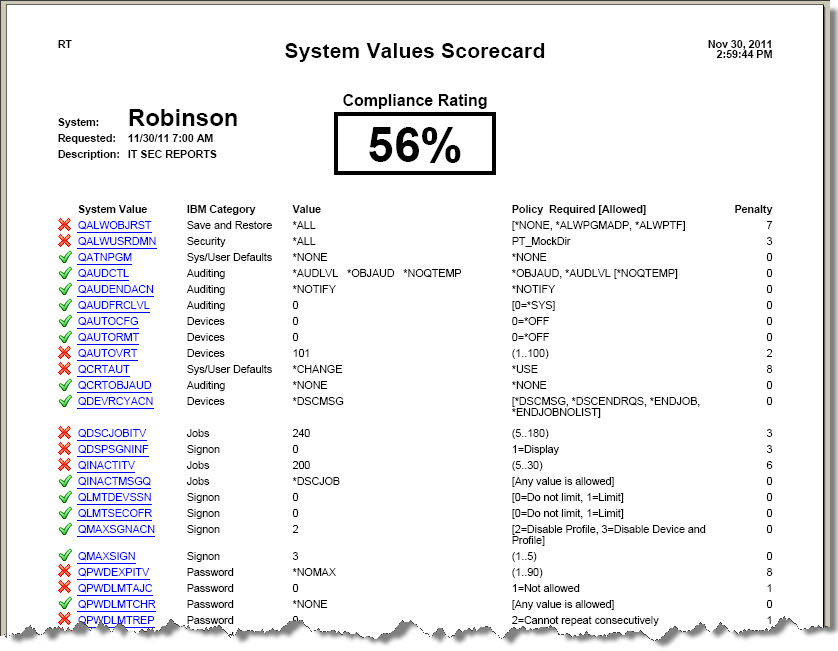
After Compliance Monitor analyzes the partition, it displays the scorecards, with numerical ratings to help you understand the criticality of any non-compliant items (see Figure 3).
Figure 3: Compliance Monitor scorecards provide easy-to-digest compliance information.
As mentioned earlier, you have the option to modify the system values scorecard, including the ability to decide which system values to include in the report. A simple, yet powerful, policy editor allows you to specify the values you need to comply with on your particular server.
We recently introduced Compliance Monitor's new batch reporting capability. This popular feature makes light work of generating and distributing reports—including scorecards—to any number of recipients. You simply specify when the reports should run and provide distribution information, such as email addresses or an IFS location. Compliance Monitor extracts the data, formats the report into several popular file types, and distributes it securely.
Compliance Monitor 3 eliminates the burden of audit reporting. Its hundreds of report options give visibility to static information, such as user profiles and system values, as well as dynamic events recorded in the security audit journal, QAUDJRN. Click here to learn more about Compliance Monitor.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online