If you’d like to make your life easier with a click of your finger, then this article is for you. I will examine PC5250’s hotspots feature and tell you how to make PC5250 more graphical and use your mouse more in an OS/400 green-screen session. I’ll discuss what hotspots are, how to set them up in your users’ display sessions, and how OS/400 processes them. The techniques I will present are geared toward Client Access for Windows 95/NT V3R2M0, but they are also valid in the new AS/400 Client Access Express for Windows product.
Where the Hotspots Are
A hotspot is an area in the PC5250 display session window where you can use your left mouse button to execute a command or function. Hotspots are generally used for the following functions:
• To simulate function keys with point-and-click technology
• To execute a macro by clicking on a word on your PC5250 display screen
• To execute a word or string on your PC5250 screen as if you had typed it in as an AS/400 command or option
• To provide a point-and-click facility by simulating the Enter key at the current cursor location
• To interface PC5250 with your Web browser by launching Web sites directly from your OS/400 display session
Although you may not realize it, there are many predefined hotspots on a PC5250 screen. You can activate PC5250 hotspots in the Hotspots Setup window (see Figure 1), which is accessed by clicking on Assists and then Hotspots setup from the PC5250 menu bar. When any of the hotspot types shown in the Hotspots setup window are checked, all predefined hotspots of those types are automatically activated. You can then select a hotspot function by double-clicking on that area of the screen. For example, to set up the F-key descriptions on your screen as hotspots (i.e., the text that reads F3=Exit, F4=Prompt, etc.), check the Fnn check box in the Hotspots Setup window. Then, when you double- click on function key text on your PC5250 display, the appropriate F-key command is sent to your AS/400.
By default, PC5250 sets up hotspots for any AS/400 function key and URL text that is displayed on your PC5250 screen, but there are other hotspots you can activate. Hotspots are activated and deactivated by clicking the following Hotspots Setup window check boxes:
• PFnn—When a user double-clicks on screen text in the format PFnn, the appropriate F-key command on the AS/400 is executed. For example, double-clicking on the PF3 text when your screen displays PF3=Exit is the same as sending an F3 command to your AS/400.
• FPnn—Whenever a user double-clicks on screen text in the FPnn format, the appropriate F-key command is executed. Double-clicking on the FP3 literal in the FP3=Exit screen text sends an F3 command to OS/400.
• Fnn—When a user double-clicks on Fnn formatted text, the corresponding F-key command is executed. Double-clicking on F3 in the F3=Exit text sends an F3 command to OS/400.
• nn—When a user clicks on any number displayed on your PC5250 screen, PC5250 sends the corresponding F-key to OS/400. For example, double-clicking on 12 on your AS/400 will send an F12 command to your AS/400. In V3R2, there is no hotspot activation that will allow you to use numbers for selecting AS/400 menu items. You can get numeric hotspot activation by either creating a macro for that number (e.g., create a macro that is called “12” that will type in the number 12 and then simulate the Enter key) or activating the Point-and-Select (Enter selected string) hotspots.
• Point-and-Select (Execute macro/ script)—If a word, number, or character string appears on your screen that is the same as a PC5250 macro defined on that workstation, then clicking on that word will execute the macro. If you create a macro called messages that displays the operator message queue, any time you double-click on the messages literal on your display, the message macro will be executed.
• Point-and-Select (Enter selected string)—When this box is checked and the user double-clicks on any string on your PC5250 display, PC5250 will simulate keying that string into the display at the position that the cursor is located (so make sure the cursor is in an input field) and then will simulate an Enter key, which will cause that string to be sent to the application (or OS/400) as if it were directly typed into the PC5250 display. If an OS/400 Work with Active Jobs (WRKACTJOB) command is displayed on your screen, then double-clicking that text will send the WRKACTJOB command to your AS/400. If the AS/400 is able to process that string, it will execute the command.
• Point-and-Select (ENTER at cursor position)—In situations when you would normally move the cursor to a certain position and press Enter, you can now double-click on that position and OS/400 will perform the cursor move/Enter sequence for you. This shortcut is valuable because, depending on how your application is programmed, it provides a point-and-click function for PC5250 emulation.
• Point-and-Select (Execute URL)—If a URL appears on your PC5250 display, you can double-click it to start your default Web browser and connect to the Web address.
You can also make your hotspots more obvious by displaying them as 3-D buttons. To turn hotspots into buttons, use the three check boxes marked with a series of periods on the Hotspots Setup window. These boxes are shown in the far right-hand column of the function key, macro, and URL check box selection items. By placing a check mark in any of these boxes, the corresponding hotspots will be shown on your PC5250 display as 3-D buttons (see Figure 2). Another benefit of 3-D hotspots activation is that it simplifies hotspot execution. If a hotspot is set up as a 3-D button, you only need to single-click on the hotspot to activate it rather than double-clicking it as you would for normal hotspots.
How PC5250 Searches for Hotspots
One of the problems with hotspots is that a single hotspot can be used for more than one hotspot function. If you have activated all hotspot types and you have defined a macro called WRKACTJOB, how do you know whether clicking on WKRACTJOB executes the
wrkactjob macro or command? PC5250 solves this problem by providing a search tree for matching hotspot execution with the appropriate function. When you click on a hotspot, PC5250 evaluates it in the following sequence and executes the first hotspot match it finds:
1. Point-and-Select (Execute URL) for web site processing
2. PFnn, FPnn, Fnn, nn for function keys
3. Point-and-Select (Execute macro/ script) for repetitive macro execution
4. Point-and-Select (Enter selected string) for selecting items from a prompt display
5. Point-and-Select (ENTER at cursor position) for cursor-sensitive applications
This Stuff Is Easy
As you can see, it’s not difficult to set up hotspots on a user’s PC. By using hotspots, you can make your PC5250 display sessions more graphical and provide a better Windows interface for your users
Figure 1: Activate your PC5250 hotspots by using the Hotspots Setup window.
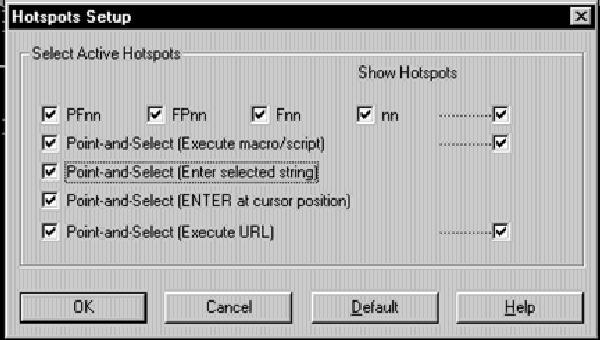
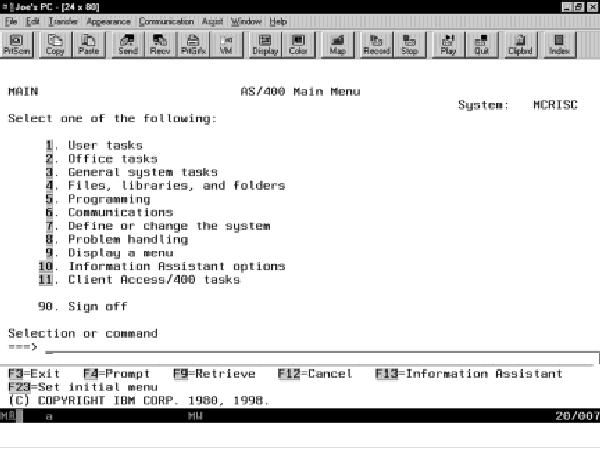
Figure 2: You can make your function key, macro, and URL hotspots more obvious by defining them as 3-D buttons.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online