PPTP, L2TP, IPSec, or SSL…what's a company to do?
Today, we often connect remotely to perform the same tasks we used to do onsite. The rapid acceptance and growth of the Internet has played a major role in organizations extending private networks. Now, organizations are creating and using Virtual Private Networks (VPNs) to provide access to network users whenever and wherever needed. With the introduction and blossoming of VPNs, working remotely is no longer a challenge. We have many choices, and connecting remotely is a relatively easy task. This article discusses and compares VPN options.
VPNs have been around for several years and have changed to provide an array of features. VPNs provide the capability for organizations to interconnect different office sites and allow mobile users, partners, or home users to securely access the company's private network services and data over the Internet from a remote location, no matter where that may be. Dialing in directly to a remote server was once the way to accomplish a remote connection. That method has some disadvantages, including cost of long-distance line charges and a need for multiple lines to accommodate multiple connections at a time. If a remote user has Internet connectivity and an organization has a connection to the Internet, the most cost-effective way is to tunnel in using a VPN.
Connecting remote sites or users together via VPN is accomplished using hardware and software on top of an existing private network to provide a secure extension of the private network. A variety of technologies provide security and privacy of information and control and separate traffic. A VPN can be implemented internally or accomplished using a service provider. Although the Internet is the most popular choice, a VPN may use Asynchronous Transfer Mode (ATM), Internet Protocol (IP), or Frame Relay infrastructure.
VPNs have grown in popularity as organizations look to save money on remote network access. Many organizations have included use of VPNs as a solution to providing secure private Wi-Fi wireless networks. It is likely VPN technology will continue to expand in upcoming years.
VPN Potential Benefits
- Enhanced geographic connectivity and global networking opportunities
- Security improvements
- Scalability
- Reduced transmit time and transportation costs for remote users
- Improved productivity
- Simplified network topology
- Cost savings
- Ability to share resources with partners
- Broadband networking compatibility
Security
Security is a key VPN factor and requires consideration. Security can be accomplished through several options.
- Firewalls—A firewall is a gateway that provides a barrier and layer between a private network and the Internet. Firewalls can be used to restrict the number of ports that are open, terminate VPN sessions, and control protocols allowed and types of packets allowed. They can also perform network address translation and packet filtration and may be used as proxy servers.
- Encryption—Encryption is the process of encoding data that a computer is sending to another computer in a form that only the receiving computer is able to decode. When data leaves a computer, it is encrypted and is then sent in a private tunnel across the Internet to the receiving computer, where it is received and decrypted. The data can't be read while encrypted (during transmission). This also means the data can't be changed. Encryption allows potentially sensitive information to be hidden from the general public.
- IPSec—Internet Protocol Security (IPSec) is a grouping of protocols used for securing IP communications by authenticating and encrypting IP packets. IPSec establishes mutual authentication at both ends of the connection and negotiates encrypted keys that are used during a VPN connection session.
- AAA Server—Authentication, authorization and accounting (AAA) servers ensure secure access in a remote access VPN environment. When a request to establish a session comes in from a remote user, the request is proxied to the server. Authentication determines who is connecting. Authorization dictates what the user is allowed to do. Accounting tracks what the user does, which is useful for security reporting, auditing, and billing.
Hardware
Hardware that is typically used when implementing a VPN includes servers, routers, firewalls, and concentrators. Routers and firewalls are considered VPN gateways. A router is an electronic device used to connect two or more computers, servers, or other electronic devices to each other. It may use either a wired or wireless connection and is usually used to connect to the Internet. A concentrator creates a remote-access VPN and incorporates use of advanced encryption and authentication techniques. A VPN concentrator works out well when you require a single device to handle a large number of incoming VPN tunnels. Concentrators provide VPN availability, performance, and scalability. They are usually Secure Sockets Layer (SSL) or IPSec, or some concentrators provide ability to utilize either.
Tunneling
VPNs typically rely on tunneling to create a private network accessed through use of the Internet. Tunneling is the process of placing a packet within another packet and sending it over a network from one location to a private network. Tunneling protocols create the connection, and encryption protocols provide security and privacy, allowing users to safely connect to and through an organization's private network. Link Layer protocols tunnel through the underlying transport network. The protocol of the outer packet is understood by the network. Both points, where the packet enters and exits the network, are called tunnel interfaces.
Types of VPN Access
A VPN can be run over a shared public infrastructure and have the same security, quality, reliability, and manageability as is provided within an organization's internal private network infrastructure. The basic types of VPN services are site-to-site VPNs, point-to-point VPNs, and remote access VPNs.
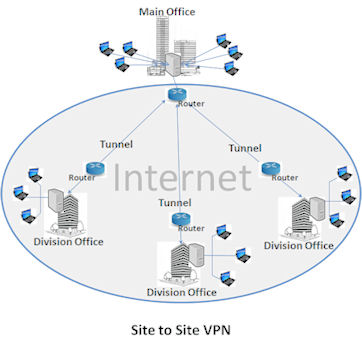
A typical VPN might have a main local area network (LAN) at the main office and other LANs at remote office sites. This is referred to as a site-to-site VPN. Site-to-site is similar to point-to-point except that there is no dedicated line in use. Each site has its own Internet connection, which may not be from the same Internet Service Provider (ISP) or even the same type of ISP. One may have a DSL connection while another may have a T1 connection. Unlike point-to-point, the routers at both ends do all of the work. They act as gateways and manage routing and encryption. Site-to-site is an easy way to connect two offices without having each user dial up using a point-to-point tunneling protocol (PPTP) connection. Site-to-site may also include use of additional hardware and firewall devices.
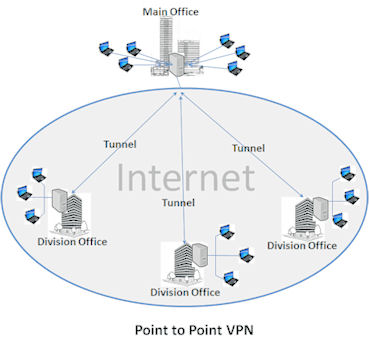
A point-to-point VPN connection is two or more networks connected using a dedicated line from an ISP. These types of connections can be expensive because a physical loop of fiber or wire is required to connect the locations. This type of connection would likely be accomplished using a high-speed circuit-based leased line. The point-to-point connection does not use the Internet, so performance is not impacted by routing issues, resource sharing with external users, or latency. Point-to-point may be considered when maximum connection throughput is required.
Usually, a VPN has a network topology more complex than a point-to-point connection. A VPN can be used to separate groups of user traffic over an underlying private network with extra security features or to provide access to a private network using customized or private routing mechanisms. VPNs are often used to mask the IP address of a connecting computer within the Internet to allow accessing the Internet anonymously or to access an organization's restricted resources.
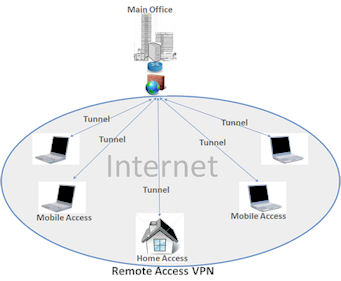
A remote access VPN is used to connect remote office locations, mobile users, remote users, and/or partners through the Internet.
Types of VPNs
Protocols are used to establish the tunneled connections. The types of VPN protocols available include PPTP, Layer 2 Tunneling Protocol (L2TP), IPSec, and SSL. Each type has advantages and disadvantages. The key to choosing a VPN technology that best suits your specific needs is understanding your user's access requirements and your organization's needs. Key consideration factors include number of users, performance and throughput requirements, server and client operating systems deployed, network resources to which access is needed, administrative requirements, security, topology, and cost. Less expensive may not always be the best choice. The starting point in deploying a VPN is understanding the protocols and selecting the type of VPN technology to use. These protocols emphasize use of authentication and encryption. Authentication allows VPN clients and servers to establish identity of users on the private network. Encryption allows potentially sensitive information to be hidden from unintended users.
The Open System Interconnection (OSI) model is a description for layered communications and computer network protocol design. OSI divides network architecture into seven layers: physical, data-link, network, transport, session, presentation, and application.
Point-to-Point Tunneling Protocol (PPTP)
A simple type of VPN protocol, PPTP is an extension of the Internet standard Point-to-Point Protocol (PPP). It is a software-based VPN system that exists at the data link layer (Layer Two) in the OSI model and uses an organization's existing Internet connection to create a secure tunnel between two points, allowing a remote user to connect to a remote network. Several corporations, including Microsoft, worked together to create the PPTP specifications. PPTP is usually associated with Microsoft because nearly all versions of Windows include built-in client support for this protocol. Juniper and Cisco also provide PPTP ability and require third-party software to be loaded on remote clients. Currently, PPTP is the most common method of VPN connection and is the easiest to set up within a Windows environment.
Microsoft's implementation of PPTP uses PPP to encapsulate the data and then encrypt the data with Microsoft Point-to-Point Encryption (MPPE). Authentication is provided by Windows' built-in dialup authentication protocols. The protocols authenticate both the client and the VPN server by use of a user ID and password, a computer certificate, or a smart card. Once the data is encrypted, it is encapsulated inside a Generic Routing Encapsulation (GRE) packet. The packet provides the information necessary to transmit PPP information over the Internet. To complete data transmission, two more layers are added. First, an IP header containing the source and destination IP addresses is constructed; then, a data link header and trailer, appropriate to the type of network being used, are created. In the case of Internet, an Ethernet header is the appropriate MAC address for the local network interface and the gateway. PPTP uses a separate unencrypted command channel to carry commands used to open, close, and maintain the connection. It uses port 1723 on the server and a dynamic port on the client. PPTP establishes the tunnel but does not provide encryption; it is used with the MPPE protocol to create a secure VPN.
PPTP is easy to set up in Windows environments because it doesn't require installing client software. Windows servers can also function as PPTP VPN servers. Clients are freely available for all of the popular versions of Microsoft Windows, Linux, Mac OS, and other operating systems. PPTP is faster than some other VPN methods because of relatively low overhead and is supported by many firewall appliances and firewall software, including Cisco, PIX, Sonic Wall, and some models of WatchGuard.
PPTP does not choose a single standard for authentication and encryption. Several products are compliant with PPTP but may not be compatible with each other. PPTP may not be as secure as other alternatives, but many of the security features and flaws have been improved in more current versions of the protocol. Confidentiality and encryption are not provided. PPTP relies on the protocol being tunneled to provide privacy. Security of PPTP VPNs can be enhanced by using Extensible Authentication Protocol (EAP). EAP uses digital certificates for improved security and mutual authentication. It requires there is not a public-key infrastructure.
L2TP and IPSec may one day obsolete PPTP. However, it currently remains quite popular.
Layer 2 Tunneling Protocol (L2TP)
L2TP, implemented primarily in Cisco products, is a newer technology developed in cooperation between Cisco and Microsoft that combines some of the features of PPTP with Cisco's Layer 2 Forwarding (L2F) protocol. L2TP is a direct competitor to PPTP for VPN tunneling. In an attempt to improve on L2F, the best features of it and PPTP were combined to create a new standard called L2TP. Like PPTP, L2TP exists at the data link layer (Layer Two) in the OSI model. In Windows implementations, L2TP wraps the whole thing up in Microsoft's version of the IPSec encryption and authentication protocols. IPSec's Encapsulating Security Payload (ESP) protocol provides the encryption for L2TP tunnels.
IPSec encrypts the data securely and authenticates both ends of the connection at the computer level through the exchange of a security certificate or pre-shared key. Standard PPP authentication validates the user with a user ID and password combination. The IPSec authentication provides an extra level of security by ensuring that the machines at both ends of the VPN are known and trusted.
L2TP can be used without IPSEC, but this would not be a feasible option, as it uses no other form of encryption. L2TP VPNs do not use a separate, unencrypted connection to send control information as PPTP ones do. Rather, data needed to start, maintain, and close a VPN tunnel through the Internet is sent and received through the same port, in the same form as the data from that tunnel, using L2TP control data instead of PPP encapsulated data that would normally be the payload. L2TP uses IPSec to encrypt and unencrypt both the control and data packets.
L2TP has several advantages over PPTP. One advantage is that it can be used on non-IP networks, such as ATM, X.25, and frame relay. L2TP VPNs are supported by many major firewall products, including Internet Security and Acceleration (ISA) Server, Check Point, Cisco PIX, and WatchGuard. The L2TP client is built into Windows 2000, XP, and 2003, but you can download client software for most pre-Windows 2000 operating systems (Windows 98, ME, and NT 4.0). L2TP requires the use of digital certificates. User authentication can be performed via PPP authentication. This adds an extra level of security. L2TP goes further and also provides data integrity for protection against modification of the data between the time it leaves the sender and the time it reaches the recipient, authentication of origin in confirmation that the user who claims to have sent the data really did, and replay protection, which keeps a hacker from being able to capture data that is sent. The overhead in providing extra security can result in slightly slower performance in comparison to PPTP.
Internet Protocol Security (IPSec)
IPSec is a collection of multiple related protocols that can be used as a complete VPN protocol solution. It can be used by itself as a tunneling protocol, or it can be used as the encryption scheme within L2TP or PPTP. IPSec exists at a higher layer of the OSI model (Layer 3). It provides enhanced security features such as better encryption algorithms and more comprehensive authentication. Often, it is considered to be the standard VPN solution, especially for site-to-site VPNs that connect two LANs.
IPSec has two encryption modes: tunnel and transport. Tunnel encrypts the header and the payload of each packet, while transport encrypts only the payload. All devices must use a common key, and the firewalls of each network must have similar security policies. IPSec in tunnel mode secures packets that are transmitted between two gateways or between a client computer and a gateway, including router to router, firewall to router, PC to router, and PC to server. An IPSec VPN works only with IP-based networks and applications. Like PPTP and L2TP, IPSec requires that the VPN client software is installed. Several vendors include managed client features within the VPN client software, making it possible to establish policies, including requiring client machines to have anti-virus and/or personal firewall software installed before allowing access to the VPN gateway. There may be a charge to purchase client software licenses.
Several hardware VPN appliances use an implementation of IPSec. For example, Cisco's VPN Concentrator products and PIX firewalls support IPSec, as do NetScreen, Sonic Wall, and WatchGuard appliances. Enterprise-level software firewalls—such as ISA Server, Checkpoint, and Symantec Enterprise Firewall—also support IPSec VPNs.
Authentication is accomplished through the Internet Key Exchange (IKE) protocol with either a pre-shared key or digital certificates, which is a more secure method. IPSec VPNs can protect against many of the most common attacks, including Denial of Service (DoS), man in the middle, or replay attacks.
IPSec support is included in Windows 2000/XP/2003 but not in older versions of Windows operating systems. VPN gateway vendors, such as Cisco and CheckPoint, provide client software for their IPSec-based VPNs.
Secure Sockets Layer (SSL)
SSL—which has been renamed Transport Layer Security (TLS)—is a VPN technology that has been growing in popularity. SSL VPNs don't require VPN client software loaded because SSL uses the Web browser as the client application. This means the protocols that SSL VPNs can use are limited, which may be a security advantage. With SSL, rather than provide VPN client access to the entire network or subnet, access can be restricted to specific applications. If the applications that you would like users to access are not accessible, browser-based programming may be necessary to create Java or Active X plug-ins, and the client browser settings will need to be opened to allow active content, which may expose the browser to other malicious applets unless you set it to block unsigned active content and ensure that the plug-ins are digitally signed. SSL VPN gateways can use applets to provide managed client features to verify that anti-virus software or firewall software is installed on the VPN client before allowing access. Applets may provide additional security features as well.
SSL VPNs operate at the session layer of the OSI model (Layer 5). This provides the ability to control access at a more granular level. SSL VPNs use digital certificates for server authentication. Other methods may be used, but digital certificates are considered the most secure and preferred method.
VPN Providers
Now that you are familiar with VPN options, you must determine which solution best fits your needs. The next step is to design the solution and determine the hardware, software, and services that will be used to implement it. A good starting point is to take inventory of what you already have and determine what you need. Numerous vendors provide VPN-related products and services. Your solution may require additional hardware, including routers and concentrators, or may require firewall software or VPN client software. Keep in mind there are open-source solutions available, and many vendors will provide trial use of software. If you decide VPN client software is needed, lots of options are available. If PPTP is an option that will work for your solution and you are already using Microsoft servers, no other software may be required. Cisco, a very popular VPN solution, adds some additional security features. AT&T, GreenBow, Sonic, and many other options are also available. Options like Secure Remote include a fob that is used in addition to a user ID and password. The fob continually changes an access token displayed on the fob screen.
VPN for Remote Access
VPN is often the best and most cost-effective way to provide remote access to an organization's network. The first step in deploying a VPN is selecting the type of VPN technology to use, with PPTP, L2TP, IPSec, and SSL being the most common. Each has advantages and disadvantages, so it is important to familiarize yourself with the characteristics of each and assess your needs before making a decision.
A well-designed VPN should include security, reliability, scalability, and network and policy management. The world has changed a lot over the last couple of decades. Many organizations have expanded to include global markets and business relations. Connecting remotely has become much more widely accepted. Setting up a VPN is an ideal solution to providing access to a private network wherever the remote users may reside.
























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online