The challenge of managing a heterogeneous enterprise is one of the most daunting problems facing IT professionals today. The sheer number of resources (systems, applications, network devices, etc.) in a single environment can be quite large and ever-changing, and a typical administrator may have no accurate catalog of his environment—let alone an understanding of the interdependencies that his resources have with each other. However, sophisticated tasks (e.g., taking down a server, moving workload, etc.) can be difficult (and risky) without this knowledge. Clearly, there's a need for advanced, automated applications to help system administrators in this area.
IBM took steps to address this problem by introducing the IBM Virtualization Engine console resource topology. Resource topology is an innovative approach to allowing systems administrators to visualize resources and relationships in their enterprise as collected and discovered by IBM Resource Dependency Service (RDS).
Resource topology makes overall system management in a heterogeneous environment easier by providing the following:
- Visualization of resources and relationships in an environment that facilitates reasoning about how changes to a particular resource might affect other resources. (For example, visual topology data could be used to improve backup and recovery strategies by allowing an administrator to infer what will happen if a disk unit, server, or application fails.)
- Powerful browse and search capabilities that help find the resources of greatest interest among the thousands (or millions) or resources potentially discovered by RDS
- The ability to display and edit resource properties
- Functionality to create and delete resources and relationships to augment the discoveries made by RDS
- User-defined groups that form user-defined logical sets of the resources of greatest importance
Understanding the Virtualization Engine Console
The goal of the Virtualization Engine console is to enable the management of solutions rather than specific IBM products by removing operating system boundaries and maximizing the sharing of resources. In its second release, the Virtualization Engine console consists of several complementary components that allow administrators to monitor and manage key eServer systems. It is the user interface identity of the set of Virtualization Engine technologies, and it works with any standard Web browser.
Understanding RDS
RDS gathers information about the IBM and non-IBM virtual and physical resources in an IT environment to be used by the resource topology user interface. RDS uses the following methods to gather this information:
- Collection is the process of gathering information that exists in remote data repositories or endpoints. RDS collects data from DB2 Universal Database, Enterprise Workload Manager (EWLM), IBM Director, System i server, Tivoli Business Systems Management (TBSM), Tivoli Configuration Manager (TCM), WebSphere MQ, WebSphere Application Server, and zSeries server.
- Discovery is the process of acquiring new information that is not in an existing data repository. To acquire this new information, RDS uses a component called Intelligent Device Discovery (IDD) to search the network for resources that are not in a data repository.
Using Resource Topology
After installing the Virtualization Engine console and RDS, open the console in any Web browser and select the following path in the left-hand navigation frame: Virtualization Engine Console > Hardware and Software > Resource Topology. This will launch the resource topology portlet (Figure 1).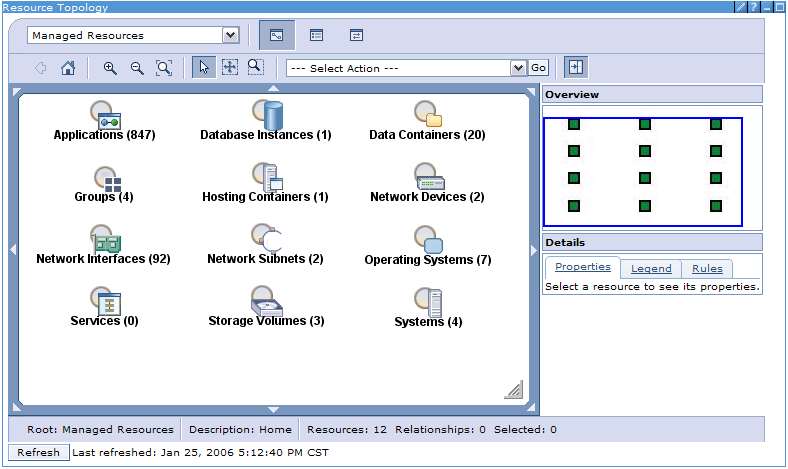
Figure 1: Here's your Managed Resources home view. (Click images to enlarge.)
Each node in the Managed Resources home view represents one of the 12 resource types known by RDS. The number next to each label represents the number of resources of that type that have been discovered (or, in the case of Groups and Services, the number that have been created by the user). The table below lists the resource types and their descriptions.
|
RDS Resource Types
|
|
|
Resource Type
|
Description
|
|
Applications
|
An application is a program that runs within a hosting container or an operating system instance.
|
|
Data Containers
|
Data containers are like file systems, containing collections of files and attributes associated with those files.
|
|
Database Instances
|
A database instance is a collection of interrelated or independent data items stored together to serve one or more applications.
|
|
Groups
|
Use groups to organize unrelated resources, creating personal views of specific resources from your environment.
|
|
Hosting Containers
|
Hosting containers are programs or applications that host other applications (e.g., WAS).
|
|
Network Devices
|
Network devices are special-purpose, dedicated computers like routers and load balancers that help manage network traffic.
|
|
Network Interfaces
|
A network interface (a.k.a. network interface controller, or NIC) provides the interface control between a system and an external high-speed network.
|
|
Network Subnets
|
A subnet is an interconnected but independent segment of an entire network that is identified by its Internet Protocol (IP) address.
|
|
Operating Systems
|
An operating system is a collection of system programs that control the overall operation of a computer system.
|
|
Services
|
A service is a process or sub-process used to automate common tasks, such as verifying security credentials or calibrating system clocks.
|
|
Storage Volumes
|
A storage volume represents a medium used for storage of data on a computer. A storage volume can be an entire physical hard disk or portions of a hard disk.
|
|
Systems
|
A system represents physical computers or virtual computers, such as logical or physical partitions.
|
Note that RDS requires configuration to run collection and discovery. If it appears that discovery has not been run, resource topology provides a button to launch the Resource Dependency Service Configuration tool (which is also located in the console at Virtualization Engine Console > Virtualization Engine Setup > Resource Dependency Service Configuration) to allow the user to configure, schedule, and manage data collection of his physical and logical IT assets.
Finding Resources and Building a Topology
The search and browse features of the home view allow users to find a discovered resource of any type and make it the center of its own topology. This provides a powerful means for an administrator to drill down through arbitrary slices of his environment as he seeks to make informed management decisions.
For example, to see the list of resources for a given type, the user can right-click on the node for the type to see its context menu. Figure 2 shows the context menu for the Operating Systems node.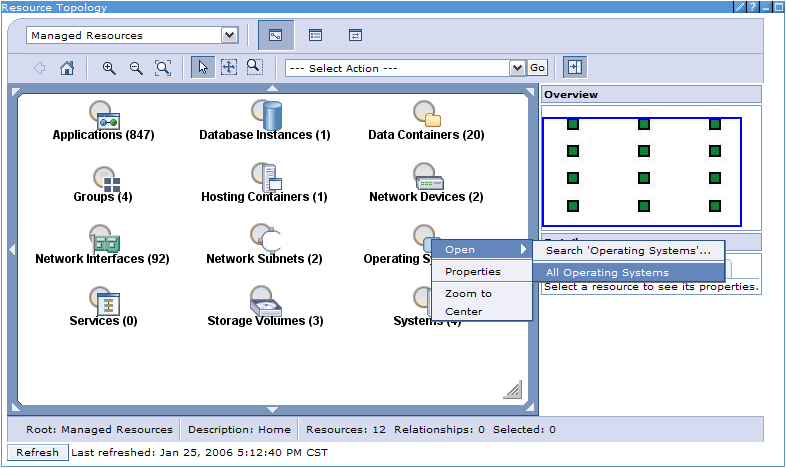
Figure 2: Right-click on the node to see the resource's context menu.
The Open submenu has options for Search 'Operating Systems...' and All Operating Systems. Depending on the enterprise, the number of resources for a given type can be quite large, so the search option (which allows a wildcard search based on name) is typically recommended to help reduce the result set size.
After clicking All Operating Systems, the user will see all of the operating systems that RDS has discovered (Figure 3). The table features advanced sorting and filtering to narrow down the list of resources if desired. 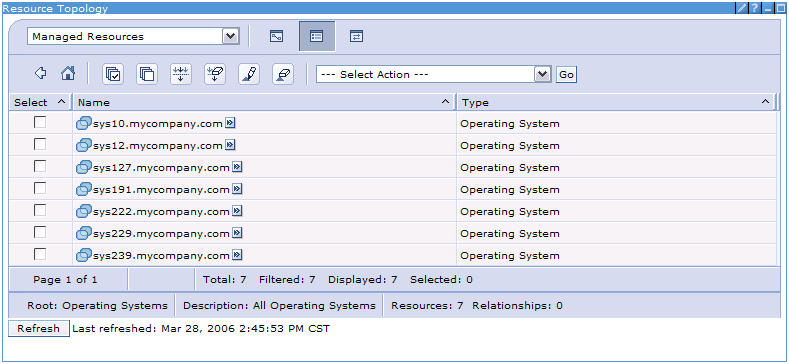
Figure 3: By selecting All Operating Systems, the user sees all of the operating systems that RDS has discovered.
For the purposes of this example, the user is interested in finding out what system the sys12.mycompany.com operating system is installed on. Figure 4 shows the context menu for sys12.mycompany.com. Under the Open submenu, there are three options (Child, Parent, All) for generating a topology with sys12.mycompany.com as the root node, showing what other discovered resources it's related to. The Child option would show what resources have relationships from the root node, the Parent option would show what resources have relationships to the root node, and the All option would show all resources that have relationships either to or from the root node.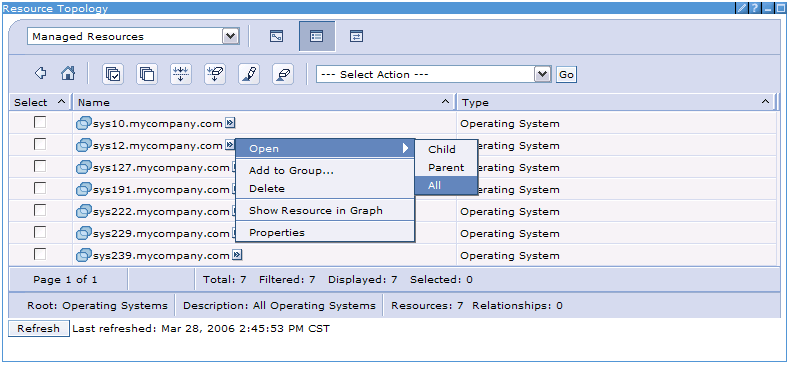
Figure 4: Choose Child, Parent, or All to see what other discovered resources the root node is related to.
Figure 5 shows the topology that resulted from choosing the Open > All option. With help from the relationship legend (Figure 6), it can be seen that the operating system represents an instance of i5/OS installed on the sys12.mycompany.com system (an System i Model 840). Furthermore, it hosts a data container (IFS1 of the IFS file system type), a network interface (1.2.3.4), a database (U102ZBDM), and 77 applications. (As a side note, it should be pointed out that RDS is uniquely capable of discovering System i-specific resources such as installed LPPs and IASPs in DB2.)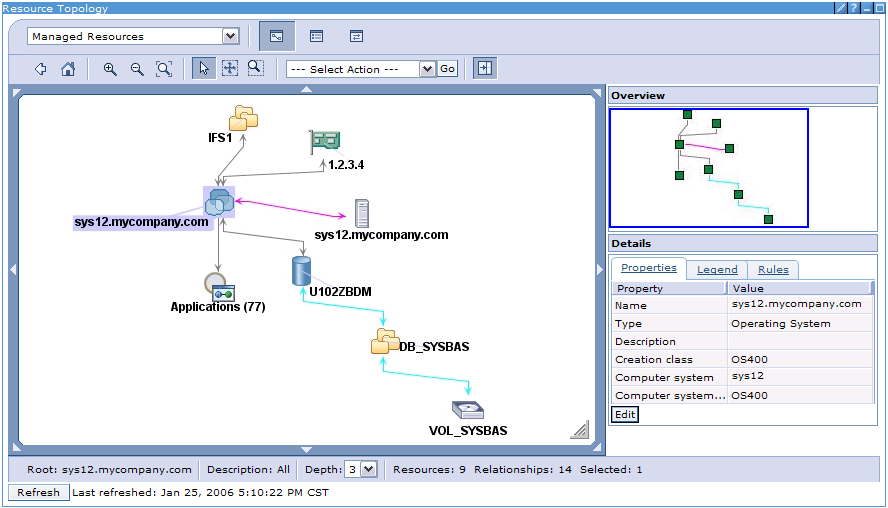
Figure 5: This is the "All" topology of depth 3 with a root node of sys12.mycompany.com.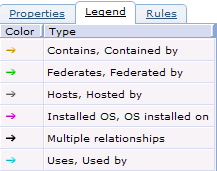
Figure 6: The topology relationship legend helps identify color-coded dependencies.
From this point, any resource of interest within the currently displayed topology can be explored to see what else it might be related to simply by invoking the appropriate context menu item. For example, if a user wanted to see what applications are hosted by the operating system, he could choose the Open > Applications menu option on the Applications node. Similarly, the depth of the topology can be changed (see the Depth box at the bottom of Figure 5) to go further from the root node to find more relationships.
In addition, this view enables other features:
- Properties for the selected resource or relationship are displayed in the area in the lower right of the display (which can also be edited by clicking the Edit button).
- RDS discoveries can be enhanced by creating user-defined resources and relationships that will also appear in the graph.
- Resources of interest can be added to custom groups (e.g., logical sets of resources representing business processes, etc.) to more easily find them from the home view later.
- Standard graphical options such as zooming, panning, etc. are available. In addition, when zoomed in on the graph, the blue box in the Overview window shows the part of the graph that's visible, and the small blue box can be used to pan to other parts of the graph.
Make Better Systems Management Decisions
The Virtualization Engine console resource topology provides a powerful means for system administrators to visualize, explore, and work with Virtualization Engine resources and relationships that RDS has discovered within their IT environments. With these advanced visualization capabilities, administrators are empowered to more efficiently keep track of their resources and make sophisticated systems management decisions.
Tony Erwin is a software engineer in IBM's Rochester, Minnesota, lab. He has extensive GUI design and development experience, working on such products as iSeries Navigator, the Abstract User Interface Markup Language (AUIML) toolkit, and the IBM Virtualization Engine Console. You can email him at




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online