It's not hard to get SNMP v1 up and running. Just follow these simple steps.
A few weeks ago, I received an email from a fellow AIX system administrator, who was having issues trying to get his SNMP v3 (Simple Network Management Protocol) client talking to the local SNMP monitor server. After a few email exchanges, I suggested he revert back to SNMP v1 to test the connectivity. I sent him a bare bones config file for SNMP v1 to test. The system admin was surprised by how small in size the config file was to get SNMP working. So let me share with you in this article how to mskr SNMP v1 communicate with an SNMP-aware monitor server. The standard configuration file AIX ships is over a 100 lines long. You don't need all those config entries to get SNMP up and running.
First, though, what is SNMP?
SNMP in a Nutshell
SNMP allows the system to collect data about your hardware and then send it back to an SNMP monitor server using traps. In its simplest form, this is a notification request. SNMP works on the basis that an SNMP monitor server sends out a request to an SNMP client, and the client then returns a response containing information about the hardware that the client has stored in its own internal tables.
The SNMP community string defines the relationship between an SNMP monitor server and the client. This string acts like a password to control the access from the monitor server's request to the client. A community string (identifier) is sent along with all requests. SNMP can monitor CPU, disk usage, memory, and network devices. You get the picture. How SNMP works underneath will not be discussed in this article. Let's just get SNMP up and running with minimal configuration.
SNMP for AIX comes in three versions: v1, v2, and v3. Version 3 offers enhanced security with secure user credentials when authenticating; plus, it's encrypted. Version 2 is the same as version 3, except it's not encrypted. Version 1 is the entry-level standard for any SNMP monitoring. Most, if not all, SNMP monitoring servers are backward-compatible with v1.
Choose Your Community Name Well
By default, all SNMP installs come with the community string called "public" or, in some instances, "private." Using the default is not a good idea; expect other SNMP administrators to guess this community string to gather information from your SNMP client that is one of your AIX hosts, which could be a problem. In this article, the community string will be called acers6k.
Stopping the Services
Before any changes can be done to SNMP, the current services need to be stopped, like so:
# stopsrc -s aixmibd
# stopsrc -s hostmibd
# stopsrc -s snmpmibd
# stopsrc -s snmpd
Ensure You Are Running with SNMP v1
Next, inform AIX that SNMP v1 binary is to be used to handle all requests by changing the link from snmpd to point to snmpdv1:
# snmpv3_ssw -1
Confirm the change has taken place
# cd /usr/sbin
# ls -l snm*
lrwxrwxrwx 1 root system 17 Jan 30 2008 snmpd -> /usr/sbin/snmpdv1
That Confirmation File
The simple configuration is located in /etc/snmpd.conf, the contents of the file shown below.
logging file=/usr/tmp/snmpd.log enabled
logging size=0 level=0
community acers6k
view 1.17.2 system enterprises view
trap acers6k 127.0.0.1 1.2.3 fe # loopback
smux 1.3.6.1.4.1.2.3.1.2.1.2 gated_password # gated
smux 1.3.6.1.4.1.2.3.1.2.2.1.1.2 dpid_password #dpid
snmpd smuxtimeout=200 #muxatmd
smux 1.3.6.1.4.1.2.3.1.2.3.1.1 muxatmd_password #muxatmd
smux 1.3.6.1.4.1.2.3.1.2.1.3 xmtopas_pw # xmtopas
Looking briefly at the file, we see the following:
- The logging file/location is specified.
- The community name in this demonstration is acers6k.
- The view specifies what priveges a community has.
- The trap specifies what host to notify when a request comes in.
- The snmpd is additional configuration entries.
- The smux specifies information between the server and client.
Note we have an entry for xmtopas. Though not required, it is best to keep this, especially for other AIX monitoring tools that request information.
Start Your Services Up
The config file is completed. All that is needed now is to re-start your services. We restart the SNMP services appended with the community name we're using. To make this a permanent fixture, amend the entries in the /etc/rc.tcpip by parsing the community name to them, as shown below:
# startsrc -s snmpd
# startsrc -s aixmibd -a "-c acers6k"
# startsrc -s hostmibd -a "-c acers6k"
# startsrc -s snmpmibd -a "-c acers6k"
A Test You Can Query
Now wait a few minutes for the SNMP client to gather information. Then issue a local command to see if data is displayed. In the following example, processor information is output:
# snmpinfo -v -m dump -c acers6k hrProcessorLoad
hrProcessorLoad.1 = 0
hrProcessorLoad.2 = 0
hrProcessorLoad.3 = 0
hrProcessorLoad.4 = 0
If you want to dump the complete tree of information (expect a lot of output), use this:
# snmpinfo -m dump -c acers6k –v
sysDescr.0 = "IBM PowerPC CHRP Computer
Machine Type: 0x0800004c Processor id: 00CD94A64C00
Base Operating System Runtime AIX version: 05.03.0012.0001
……
If you're not getting any information back and you're quite sure that there are no typos in the file, check the UDP size. Maybe your UDP packets are not large enough. Change it to a max of 65535, like so:
# no -o udp_sendspace=65535
Setting udp_sendspace to 65535
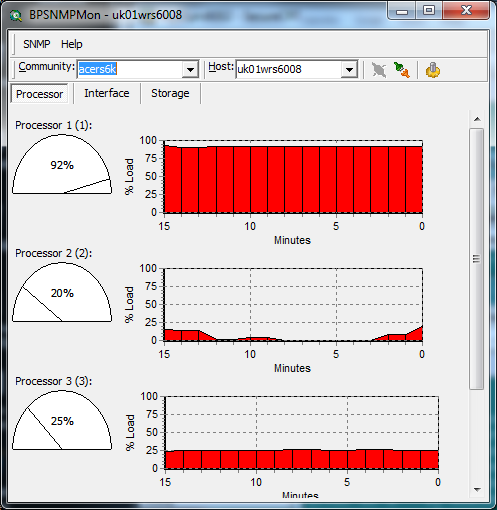
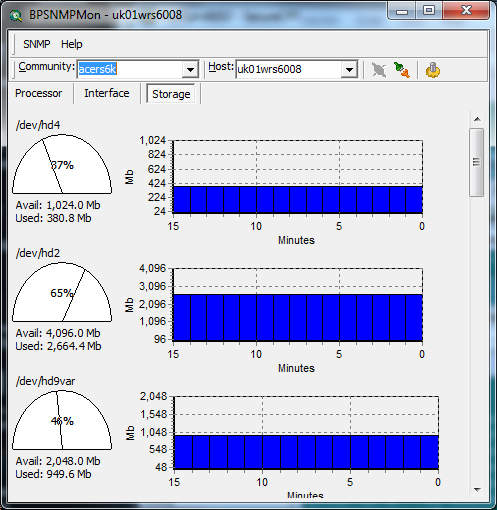
Figures 1 and 2 show an SNMP monitor agent monitoring the AIX client uk01wrs6008 that was demonstrated in this article, along with the configurations used.
Figure 1: This is what the processor looks like.
Figure 2: And here's the disk output.
See how easy it is to get SNMP up and running?





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online