I don’t know about you, but I’m feeling pretty lost in this new e-business, Internet- connected world. It seems like it was only a short time ago that I was safe in my little RPG programming world, cranking out subfiles and earning a comfortable, if not very exciting, living. When I began to get bored, I could always pick up a copy of Midrange Computing and read about some new technology coming down the road. Keeping current gave me a good feeling, and I felt smarter. For example, when someone asked me which was better, VisualAge for RPG or Java, I could come back with a response like “Well, VisualAge for RPG is probably better for your typical RPG coders because they can build on their current programming skills. Besides, I hear that IBM is going to make VisualAge for RPG generate Java byte code, so you’re covered either way.” When someone would say,
“What’s Java byte code?” I’d quickly turn away and find something else to talk about because I didn’t know what byte code was. It was then that I began to suspect that I was falling behind, and I didn’t much care for the feeling.
If you’re in the same boat, and you feel like you’re falling behind because there’s an information overload out there, then you have to start right now to catch up. You can’t hope that you’ll reach retirement age before your company decides to replace you with some kid who isn’t even old enough to vote. One area you need to start learning about right away is Java. If you haven’t started learning about it yet, and your entire exposure to the language is based on the myriad articles you’ve been reading in MC and other places, then, chances are, you’re probably lost by this point. If this is you, don’t despair. You’re not alone. There are legions of typical RPG programmers out there who are in the same boat.
I thought that an article covering the fundamentals of Java might be helpful. By the time you finish reading this article, you should have a good understanding of most of the terms you’ll need to be familiar with to get started programming in Java, and you’ll even be able to set up your own PC to write your first Java program.
Getting Started
I’ll start by going over some fundamental Java terms:
• Java—Java is a language based loosely on the C, C++, and Smalltalk languages. It was developed by programmers at Sun Microsystems back in 1991 to run on intelligent consumer electronics such as toasters and wristwatches.
• *.java—The .java extension on a file lets you know that this file is a Java source file. You must compile the *.java source file to create a Java *.class file (i.e., byte code).
• *.class—The *.class extension on a file tells you that this file is a binary representation of a Java source file. In other words, it is an object that can be referenced by other applications (such as Java programs or Web browsers). It is very similar in type to an object on the AS/400 such as a *PGM or *FILE object. A *.class file is made up of byte code, which is nothing more than the compiled Java source file.
• Java Development Kit (JDK)—You will use a JDK to build your own Java applications and applets. A JDK consists of the core Java classes, as well as many other commonly used Java programming classes. For example, every JDK comes with a Java compiler, which is used to create Java *.class files. Every JDK also comes with a set of utility packages or classes, such as the java.io package, that allows you to perform common functions. In the case of the java.io package, you can read bytes from a file, update a record, or perform any number of other file-related functions in a Java program.
JDKs are available in a variety of releases (such as 1.1.7, 1.1.8, 1.2.2, and 1.3), which makes things very confusing. It really doesn’t matter which release you use as long as that release contains the functionality you need. For example, if you want access to Java classes that are able to play *.wav sound files, then you’ll need to use release 1.1.8 or higher because the earlier releases only support the playing of *.au files. The other thing to keep in mind is that some releases of the JDK use class files that have been replaced or deprecated with newer versions in the later releases. For example, if you create a Java applet that uses one of these deprecated classes and the browser running your applet doesn’t recognize it, then your applet may not function correctly.
JDKs are available for both the PC and the AS/400. In fact, the same JDK that runs on the PC runs on the AS/400. The JDK (licensed program 5769-JV1) comes with every AS/400 beginning with OS/400 Version 4.1 and higher and is stored in the /QIBM/ProdData/Java400/ directory of the AS/400 Integrated File System (AS/400 IFS). The AS/400 also has a special JDK that contains Java classes that have been written by IBM especially for use with the AS/400. This JDK is known as the AS/400 Toolbox for Java (5769-JC1). The toolbox also comes free with OS/400. You can find the AS/400 Toolbox for Java by looking in the /QIBM/ProdData/HTTP/Public/jt400/lib directory in the AS/400 IFS. There is also a special development toolkit for the AS/400 known as the AS/400 Developer Kit for Java (also licensed program 5769-JV1). This licensed product contains the standard JDK in addition to other classes developed exclusively for use with the AS/400.
• Java Runtime Environment (JRE) —A JRE differs from a JDK in that JREs are used only to allow systems an environment in which Java programs can execute. In other words, you cannot develop Java programs in a JRE. You can only run them there. Most browsers have JRE plug-ins known as Java Virtual Machines (JVMs) that enable them to run Java applets. However, most Microsoft Windows PCs do not come standard with a JRE, so if you are writing Java applications to distribute to other PCs, you’ll probably need to distribute a JRE with the application. You can download a free JRE from Sun Microsystems that you are licensed to distribute with your own apps. OS/400 comes standard with a JRE.
• Java application—A Java application is a stand-alone program, much like an RPG program you’d write for the AS/400. It can perform any number of functions and is limited only by your imagination. A Java application can be run from a PC command line by calling it with the java command. It can also run on the AS/400 by calling it from a command line using the JAVA command.
• Java applet—A Java applet is also a stand-alone program, but it can only run in a Web browser. Many times, a Java program is designed so that it can be run as both an application and an applet. Turning an applet into an application is as simple as adding the following line of code to any applet:
public static void main (String args[]) {}
• Abstract Window Toolkit (AWT)—AWT is a set of Java classes that are packaged together to provide the Java programmer with a set of easy-to-use GUI interfaces. Using AWT, you can create frames to hold buttons, text fields, labels, and more in a GUI. You can also use AWT to create most other standard GUI components, such as lists and trees.
• Swing—Swing is the replacement for AWT and is rapidly gaining in popularity as the standard for GUI programming. Swing contains more sophisticated GUI classes than AWT and is generally easier to use when creating Java GUIs. It also has more functionality than AWT. (Actually, Swing was the beta name for Java Foundation Classes [JFC], but the beta was so widely used that, even though Swing is long out of beta, Swing and JFC are synonymous.)
• CLASSPATH—For some reason, when you read articles about Java programming or you read about someone’s cool new Java utility, you don’t hear much about the CLASSPATH variable. And that’s a shame, because the CLASSPATH is extremely important to your Java environment. That’s because the CLASSPATH tells your PC, or your AS/400, where to find the Java classes you want to run. On a PC that you are using to develop Java programs, you will need to set the CLASSPATH in your PC’s autoexec.bat file so that your DOS-based command line compiler and run commands (javac and java, respectively) can be found. That is, if you download and install the free JDK from Sun Microsystems and you use a DOS command line to compile your Java code (which is the way most hard-core Java programmers do it), then you will need to tell Windows where the JDK resides. If you use an integrated development environment (IDE) such as VisualAge for Java, the IDE will create the CLASSPATH statement for you when you install the package. Other IDEs, such as JBuilder from Borland International, let you specify the CLASSPATH as a runtime option when using the tool. A CLASSPATH statement is also used to tell the Java compiler where to find other Java packages, such as the AS/400 Toolbox for Java that you have installed on your PC. Figure 1 shows a typical autoexec.batUTOEXEC.BAT file. This is the setup on my development PC for Version
1.3 of the JDK from Sun Microsystems and the AS/400 Toolbox for Java. You can also set the CLASSPATH explicitly each time you compile or run a Java program by prefacing the appropriate command with the CLASSPATH command.
On the AS/400, the CLASSPATH is set for you automatically when you install the JDK and the AS/400 Toolbox for Java licensed programs. However, you can also specify it explicitly in either a CL program or on a Qshell command line by using the CLASSPATH command, followed by the appropriate path statement.
• JAR—A JAR file is really nothing more than a standard Zip file. The only real difference, besides the three-letter file extension, is that JAR files contain another file, known as a manifest file. The manifest file contains a list of the contents of the JAR file. JAR files are used by Java as a way to package common Java classes together in a convenient manner. For example, swingall.jar, which is part of the Swing JDK that you might download from Sun Microsystems, contains all of the Java classes you will need to call to build and display Java GUIs. So, rather than having to reference the location for each individual component separately in a Java source file or on a CLASSPATH statement, you can instead simply reference the JAR file. That way, every class that resides in the JAR file is immediately available to the program.
Getting the Components
OK. Have you had enough definitions? Me too. Instead of defining more terms, I’ll move on to something more interesting. I’ll tell you all of the components you need to start coding Java programs for the AS/400, then you can configure your PC to be able to use the components. Finally, you’ll write your very first useful Java program!
The first thing you’ll need to do is to download and install the Java 2 software development kit. If you’ll notice, Sun Microsystems is calling this a software development kit (SDK), rather than a Java Development Kit (JDK). Don’t let that confuse you. The SDK is, for all intents and purposes, the same as a JDK. I’ll still refer to it as JDK in this article. You could get this JDK from your AS/400, but it’s just as easy to grab it off the Internet from Sun Microsystems’ Web site. Fire up a connection to the Internet and point your browser to www.javasoft.com/j2se/1.3/downloadwindows. html. Scroll down the page until you see the section titled “Download Java 2 SDK, v 1.3.0 Software for Windows 95/98/2000/NT 4.0 (Intel Platform).” Select an option to download in either one large bundle or in multiple pieces. It doesn’t matter which option you choose. Just choose the one that works best for your Internet connection speed. Click on the continue button. You’ll be asked to read and accept a license for the JDK. Click on the Accept button and you’ll be taken to the appropriate download page. Download the file(s) to an empty directory on your PC named C:Java. Note that you don’t have to name the directory C:Java, but, if you do, you will be able to use the same configuration on your PC that I used on mine. When you have the file(s) downloaded, double-click on the executable file you just downloaded to install the Java 2 JDK.
This version of the Java JDK also automatically installs the Swing APIs for GUI development as well as the Java Runtime Environment for this version of Java. In previous versions of the JDK, you had to download some of the components, such as Swing, separately. When you install the JDK, several new subdirectories will be created, beginning with a directory named jdk1.3 under the C:Java path.
Now you need to get a copy of the AS/400 Toolbox for Java and install it on your PC. Point your browser to www.as400.ibm.com/ toolbox/currentModDownload.htm and download the evaluation copy of the Toolbox. Don’t be concerned about the term evaluation. This is a fully functioning copy of the latest version of the AS/400 Toolbox for Java. Download this Zip file to your PC to a directory named C:JavaJT400. Again, you can use any directory you want, but if you use C:JavaJT400, you can configure your PC the same way I configured mine. You’ll download a file named jt400All.zip. Unzip this file to the C:JavaJT400 directory. It will create several new subdirectories inside of this directory.
Setting Your Environment
Now you need to set your CLASSPATH variable in your autoexec.bat file. Look at the file in Figure 1. If you followed the same naming scheme I suggested above, then you can enter the code shown in Figure 1 into your own autoexec.bat file, and you’re done with the configuration. If you didn’t, then you’ll need to modify the path names on the CLASSPATH variables to match your own setup.
Writing Your First Application
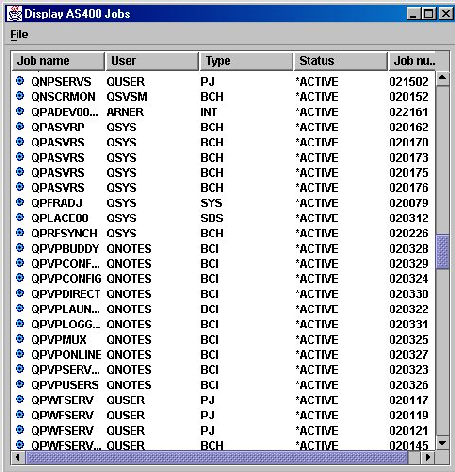
So far it’s been pretty painless, right? Let’s keep it that way. The next thing to do is to create a Java program that will display a list of AS/400 jobs in a Java GUI. I’m not going to explain the syntax of the code here because, unfortunately, I’m out of space. However, rest assured that the Java application shown in this article is extremely uncomplicated once you begin learning a little bit about Java syntax. To learn more about the pieces that make up this little Java application, see the References and Related Materials list at the end of this article.
You can download the source for the program shown in Figure 2 from Midrange Computing at www.midrangecomputing. com/mc. When you do, save the file to any directory on your PC and open a DOS window. You need to compile the code to create the Java *.class file. Assuming that you’ve already set your CLASSPATH variables as I’ve described and that you have rebooted at least once since then, you’re ready to compile the source code. To do this, type the following on a DOS command line from the directory where you saved the Java source file that you downloaded from MC:
javac DisplayAS400Jobs.java
Pay attention to the case of each letter in the command. Java is case-sensitive. If all goes well with the compile, you should see no messages and you will be prompted with a blank DOS prompt. If there are errors, you probably don’t have the CLASSPATH set up correctly. Go back and double check path names and, if necessary, modify the autoexec.bat file and reboot your PC.
OK. If you’re still not sure if the *.class file was generated, display the directory where you created it and you should find a file named DisplayAS400Jobs.class. Found it? Good! Now you’re ready to try it out. To run the Java application, enter the following command from a DOS command line:
java DisplayAS400Jobs
You should have been prompted to log on to your AS/400, and then a list of AS/400 user profiles should have been displayed for you. If you right-click on any of the user profiles, you can display the properties for that user profile. Cool, eh? Java can be a lot of fun (when everything works correctly)!
Time to Practice
I recommend that you check out the References and Related Materials list at the end of this article for some resources to get you started learning more about the Java language. Invest in a couple of good books on Java programming and visit the online tutorials provided by Sun Microsystems. All of these resources—plus practice, practice, practice—will soon turn you into a great Java programmer!
There’s a lot of information out there, and trying to separate the wheat from the chaff can be a real bear. Hopefully this little primer on Java fundamentals will take some of the confusion and fear out of learning about and using this really cool language.
REFERENCES AND RELATED MATERIALS
• AS/400 Toolbox for Java Evaluation Copy Download site: www.as400.ibm.com/toolbox/currentModDownload.htm
• Java Application Strategies for the AS/400, Second Edition. Don Denoncourt. Midrange Computing Publishing Co., 2001
• Java How to Program. Paul J. Deitel and Harvey M. Deitel. Upper Saddle River, New Jersey: Prentice Hall, 1999
• Sun Microsystems Java Products and APIs page: www.javasoft.com/products
• The Java Tutorial: A practical guide for programmers (available in electronic format at http://java.sun.com/docs/books/tutorial/index.html)
REM Begin Java environment: JDK 1.3 (JAVA 2), JT/400
REM [JKD 1.3]
SET JAVAHOME=C:JAVAJDK1.3
SET PATH=%PATH%;C:JAVAJDK1.3BIN
SET CLASSPATH=.;C:JAVAJDK1.3LIB
REM [JT/400]
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBjt400.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBuitools.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBdata400.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBjt400proxy.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBjt400servlet.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBjui400.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIBx4j400.jar
SET CLASSPATH=%CLASSPATH%;C:JavaJT400LIButil400.jar
Figure 1: Don’t forget to set your Java CLASSPATH!
Figure 2: You can create this Java GUI in just minutes.






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online