Learn how to ensure the validity of extended character string assignment via the CPYECLAP instruction.
IMHO, high-level languages (HLLs) in IBM i do not treat character strings containing double-byte character set (DBCS) characters seriously enough. For example, assigning a long character string containing DBCS characters to a shorter character variable using the EVAL operation code of RPG would probably truncate the DBCS data in the source string and therefore lead to an invalid result character string.
The cause of this problem is quite clear: the EVAL op-code treats a character string containing DBCS characters the same way it treats a single-byte character set (SBCS) character string. However, at the MI level, things are quite different. MI defines four types of extended (double-byte) character types and provides the Copy Extended Characters Left-Adjusted With Pad (CPYECLAP) MI instruction for assignment of extended character strings. This article is intended to show you how to ensure the validity of extended character string assignment via the CPYECLAP instruction.
DBCS Data Types Defined at the MI Level
According to the documentation of the Set Data Pointer Attributes (SETDPAT) and the Copy Extended Characters Left-Adjusted With Pad (CPYECLAP) MI instructions, MI defines four extended (double-byte) character types: OPEN, EITHER, ONLYNS, and ONLYS. Except for ONLYNS, the double-byte character data must be surrounded by a shift out control character (SO = hex 0E) and a shift in control character (SI = hex
- An ONLYNS field contains only double-byte data with no SO/SI delimiters surrounding it.
- An ONLYS field can contain only double-byte character data within the SO/SI pair.
- An EITHER field can consist of double-byte character or single-byte character data but only one type at a time. If double-byte character data is present, it must be surrounded by the SO/SI pair.
- An OPEN field can consist of a mixture of double-byte character and single-byte character data. If double-byte character data is present, it must be surrounded by the SO/SI pair.
These extended character types can be described only by data pointers.
The Data Description Specification (DDS) defines similar character types: J (Only), E (Either), O (Open), and G (Graphic). The following table lists the data type name of each extended character type in MI and DDS, and the corresponding scalar type value when being represented by a data pointer.
|
Extended Character Types |
||
|
Scalar Type Value |
MI Data Type Name |
DDS Data Type Name |
|
06 |
ONLYNS |
G (Graphic) |
|
07 |
ONLYS |
J (Only) |
|
08 |
EITHER |
E (Either) |
|
09 |
OPEN |
O (Open) |
How Does the CPYECLAP Instruction Work?
The CPYECLAP instruction has three operands:
- Operand 1: Data-pointer that defines and addresses the receiver-extended character data.
- Operand 2: Data-pointer that defines and addresses the source-extended character data.
- Operand 3: Three-byte pad values that consist of a one-byte single byte pad value and a two-byte double byte pad value.
The operation is performed at the length of the receiver operand. If the source operand is shorter than the receiver, the source operand is copied to the leftmost bytes of the receiver, and the excess bytes of the receiver are assigned the appropriate value from the pad operand. If the pad operand is null, the default pad values (hex 40 for single byte, and hex 4040 for double byte) are used.
The valid copy operations that can be specified on this instruction are listed in CPYECLAP's documentation in the
When the source value is longer than can be contained in the receiver, truncation is necessary. The following truncation rules apply:
- Truncation is on the right.
- When the string to be truncated is a single-byte character string, or an extended character string when the receiver is ONLYNS, bytes beyond those that fit into the receiver are truncated with no further processing needed.
- When the string to be truncated is an extended character string and the receiver is not ONLYNS, the bytes that fall at the end of the receiver are truncated as follows: When the last byte that would fit in the receiver is the first byte of an extended character, that byte is truncated and replaced with an SI character. When the last byte that would fit in the receiver is the second byte of an extended character, both bytes of that extended character are truncated and replaced with an SI character followed by a single byte pad value. This type of truncation can occur only when converting to an OPEN field.
When the source value is shorter than that which can be contained in the receiver, padding is necessary. One of three types of padding is performed:
- Double byte (DB): The source value is padded on the right with double-byte pad values out to the length of the receiver.
- Double byte concatenated with a SI value (DB||SI): The source double-byte value is padded on the right with double-byte pad values out to the second to last byte of the receiver and an SI delimiter is placed in the last byte of the receiver.
- Single byte (SB): The source value is padded on the right with single-byte pad values out to the length of the receiver.
The type of padding performed is determined by the type of the receiver operand in the copy operation:
- If the receiver is ONLYNS, DB padding is performed.
- If the receiver is ONLYS, DB||SI padding is performed.
- If the receiver is EITHER and the source contains a double-byte value, DB||SI padding is performed.
- If the receiver is EITHER and the source contains a single-byte value, SB padding is performed.
- If the receiver is OPEN, SB padding is performed.
Define an Extended Character Field Using a Data Pointer
The CPYECLAP instruction accepts its source, receiver operands in the form of data pointers. A data pointer is one type of MI pointer that contains not only the addressability information of the data it addresses, but also the data type and length attributes of the data it addresses. The lower 8-byte portion of a data pointer is the Single-Level Store (SLS) virtual address of the data, and its higher 8 bytes contain the following data pointer-specific information:
Bits 0-3 of byte 0 0-3 indicate the MI pointer type; for data pointers, it's always hex C.
Bits 4-7 of byte 0 4-7 indicate the data type of the data pointer:
- 0=Signed binary
- 1=Floating point
- 2=Zoned decimal
- 3=Packed decimal
- 4=Character
- 6=ONLYNS
- 7=ONLYS
- 8=EITHER
- 9=OPEN
- A=Unsigned binary
Bytes 4-5 describe the length attribute. For zoned or packed decimal, byte 4 is the fractional digits, and byte 5 is the total digits of the decimal field. For signed or unsigned binary, bytes 4-5 can be set to value 2, 4, or 8 indicating 2-byte, 4-byte, or 8-byte binary data. For floating-point, bytes 4-5 can be set to 4 or 8 (4-byte, 8-byte floating-pointer data). For ONLYS, EITHER, or OPEN extended character data, bytes 4-5 are the number of bytes of the data. For ONLYNS, extended character data, bytes 4-5 are the number of characters of the data. DDS applies the same rule for G (Graphic) type fields.
In an OPM MI program, the Set Data Pointer (SETDP) and Set Data Pointer Addressability (SETDPADR) MI instructions can be used to set the addressability of a data pointer, and the SETDPAT MI instruction can be used to set or change the data attributes of a data pointer. In an ILE program, these two tasks can be achieved via a single invocation of the _SETDP system built-in, which accepts an address operand and a data attributes operand and returns the result data pointer. The following prototype of _SETDP is extracted from mih-dtaptr.rpgleinc.
|
/** * @BIF _SETDP (Set Data Pointer (SETDP)) * * @remark In a sense, the _SETDP system built-in combines the * functionality of the SETDP and SETDPAT instructions in the OPM * MI instructions set. It assigns both the scalar type and * length attributes and the addressability to the returned data * pointer. */ d setdp pr * extproc('_SETDP') d addr * value d attr
/** * Data pointer attributes */ d dpat_t ds qualified * Scalar type d type * Length d len 5u 0 d dec_pos d digits * Reserved (binary 0) d
/** * Scalar types */ d DPAT_SIGNED_BINARY... d c x'00' d DPAT_FLOATING_POINT... d c x'01' d DPAT_ZONED_DECIMAL... d c x'02' d DPAT_PACKED_DECIMAL... d c x'03' d DPAT_CHARACTER... d c x'04' d DPAT_ONLYNS... d c x'06' d DPAT_ONLYS... d c x'07' d DPAT_EITHER... d c x'08' d DPAT_OPEN... d c x'09' d DPAT_UNSIGNED_BINARY... d c x' |
The following RPG example (t183.rpgle) sets up a data pointer that defines an 8-byte OPEN field.
|
h dftactgrp(*no) /copy mih-dtaptr d ptr_val ds d @opn * d opn s d dpat ds likeds(dpat_t)
/free dpat = *allx'00'; dpat.type = DPAT_OPEN; dpat.len = 8; @opn = setdp( %addr(opn) : dpat); // Check @opn: EVAL ptr_val:x // e.g. C9000000
*inlr = *on; /end-free |
A Real Example of Copying Extended Character Data via the CPYECLAP Instruction
The following example RPG program (cpyeclap01.rpgle) demonstrates a couple of extended character data copy operations:
- Copy an OPEN field to a shorter OPEN field for test of truncation.
- Copy an EITHER field to a longer EITHER field for test of padding.
|
h dftactgrp(*no)
/copy mih-comp /copy mih-dtaptr
* OPEN fields * long_o contains 4 DBCS characters: '????' d long_o s d short_o s d @long_o s * d @short_o s * * EITHER fields d long_e s d short_e s d @long_e s * d @short_e s *
d dpat ds likeds(dpat_t) d pad ds likeds(cpyeclap_pad_t)
/free // Set up data pointers dpat = *allx'00'; dpat.type = DPAT_OPEN; dpat.len = 10; @long_o = setdp( %addr(long_o) : dpat); dpat.len = 6; @short_o = setdp( %addr(short_o) : dpat);
// [1] Test for truncation cpyeclap( @short_o : @long_o : pad ); // Result:
// Test for padding dpat.type = DPAT_EITHER; dpat.len = 10; @long_e = setdp( %addr(long_e) : dpat); dpat.len = 4; @short_e = setdp( %addr(short_e) : dpat); pad.single_byte_pad_value = '-'; // [2.1] SB padding should be performed cpyeclap( @long_e : @short_e : pad ); // Result:
// [2.2] DB||SI padding should be performed short_e = x'0E pad.double_byte_pad_value = x' cpyeclap( @long_e : @short_e : pad ); // Result:
*inlr = *on; /end-free |
The results of our test for truncation and padding are the following:
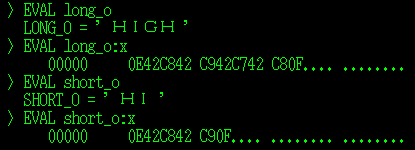
Figure 1: Test for truncation.
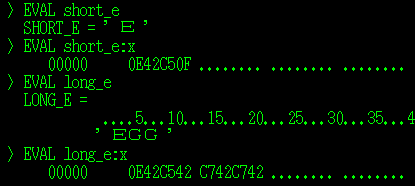
Figure 2: Test for padding.
Yeah, we did it!





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online