Alternatively, perhaps you'd rather keep your private data private.
The life of the security administrator used to be simple. Application menus insulated the user from the back-end database, and restrictions in a user's profile easily limited access to only a few basic commands. Then things started to get complicated as "dumb terminals" gave way to the more functional personal computer (PC). Spreadsheet applications arrived, and simple file transfers quickly became commonplace. But it was like opening Pandora's Box!
IBM responded to demands for open access to the database by building TCP connectivity into the server, thereby allowing data to be accessed by numerous powerful interfaces, including File Transfer Protocol (FTP), Open Database Connectivity (ODBC), and Distributed Data Management (DDM).
As these services all connect to the database directly, the underlying fabric of our menu "defense" is gone. While resource (object) security is applicable to every interface that the server supports, PowerTech's annual "State of System i Security" study has reported year after year that it is rarely implemented and is easily circumvented by overly powerful user profiles.
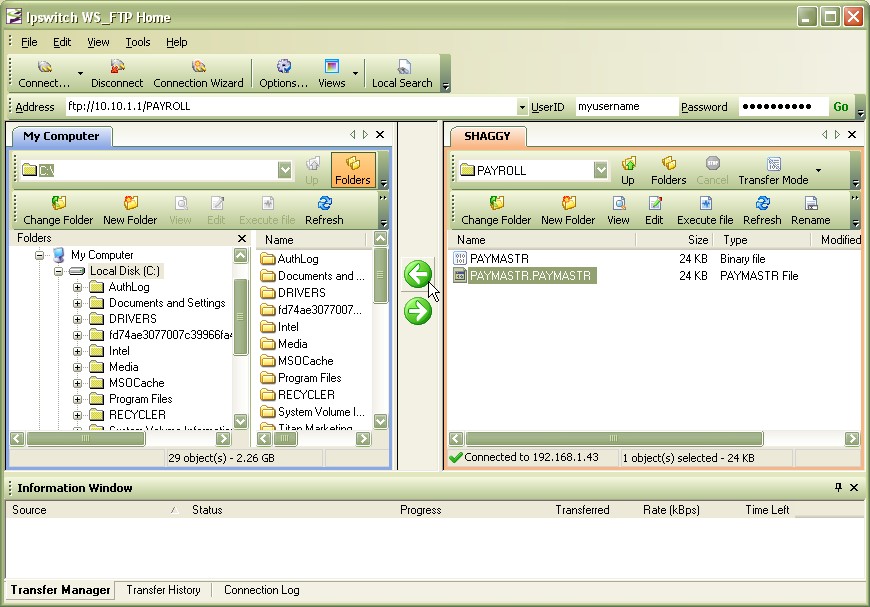
A simple FTP program, such as the example represented in Figure 1, can provide graphical access to any unsecured data. Costing a mere $40, mine even came with a free 30-day trial!
Figure 1: Users often have drag-and-drop access to sensitive data. (Click image to enlarge.)
While resource security is recommended for the core layer of object protection, it is a one-size-fits-all mechanism as the operating system does not distinguish between interfaces.
If that were not enough to raise an auditor's eyebrows, network activities are not audited, regardless of any auditing controls that you turn on. The best you can hope for is to know when a file is opened, but not what type of request was made of the data. Several of these interfaces also permit commands to be executed, sometimes regardless of the "limit capabilities" setting in the profile.
|
|
Fortunately, the operating system comes with a number of exit points related to network interfaces. To access the exit point registration facility, use the Work with Registration Information (WRKREGINF) command, and define the name and location of a desired exit program for each exit point. The exit program will be invoked when a request is received by the server. The exit program is passed details about the request and can perform any programmatic task, commonly to assess the legitimacy of the request or to log the activity.
While writing your own exit programs is possible, many organizations are reluctant to commit to the ongoing research and development of a security-sensitive application. Other considerations when developing your own solution should include performance implications, dynamic rule functionality, and separation of duties when programmers have access to a system that their code is protecting.
If you decide not to trust this functionality to your own exit programs, we recommend a professional solution called PowerTech Network Security. This solution enables visibility of network requests and permits rules to be established for access control and reporting. Requests can also issue message alerts to ensure immediate notification and reaction from the appropriate parties.
Imagine being able to report on users accessing your IFS, including the directories they navigated through and the files they viewed or deleted. How reassuring that an administrator is alerted when an FTP request targets a production file rather than a test file, all while the system blocks the unauthorized access attempt!
One of the advanced features of Network Security is the ability to override a request to run under an alternate profile. This permits the recommended "deny by default" methodology to be implemented, while still granting access to preapproved requests. For example, you can set a library to *EXCLUDE but still allow an FTP download of a specific file to be permitted (and logged) by your accounting group. Likewise, take a normally unrestricted user profile with *ALLOBJ special authority, and downgrade that profile to have read-only capabilities over production data! Both are on-the-fly security changes that are transparent to the user and are only in effect for specific requests. And of course, the logging is against the signed-on user.
For more information on PowerTech Network Security or to receive a free security assessment of your system (including a review of your network vulnerability), please visit www.powertech.com/mcp.






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online