While it’s easy enough to know whether my own connection to IBM i is secure—that is, encrypted—how can I tell whether all connections are encrypted?
By Carol Woodbury
Some organizations have a requirement that all connections to their IBM i be encrypted. I applaud those organizations and encourage everyone to adopt this practice. Most organizations encrypt outbound connections, but not everyone encrypts internal traffic. Encrypting all communication (including internal) ensures that no passwords or data are flowing anywhere in cleartext.
As I said, it’s easy to determine whether my connection to IBM i is encrypted. If I’m using Access Client Solutions (ACS) to establish a Telnet session, all I have to do is look in the lower right corner of the session to see the port used, an open or closed padlock, and encryption strength if the connection is secure. For ODBC, I simply look for the job name to be QZDASSINIT (SS meaning secure) rather than QZDZSOINIT (where SO is open or not encrypted). But if I’m an administrator and I want to prove to myself or am required to prove to an auditor that all connections are secure, how might I do that?
NETSTAT
One way to look at all connections is to use the Work with TCP/IP Network Status (WRKTCPSTS) command. Choosing to look at the IPv4 and IPv6 connections will show you the established connections and which server they’re connected to. The server name will indicate whether the connection is secure, typically by adding either -s or -ssl to the end of the server name, e.g., Telnet-ssl. The port used is also an indication of whether the connection is secure. For example, if the Telnet session is using port 23, then it’s not secure. But if it’s coming in via port 992, the connection is encrypted. Here’s a list of the well-known ports. In addition, you’ll need the list of ports used by the ACS. By analyzing the output of NETSTAT, you can determine if there are currently any unsecured connections established to your IBM i. The problem with NETSTAT is that it’s a point in time; it’s accurate only for the time at which you ran the command. Other connections may be established in the middle of the night, for example.
The Audit Journal
If you need a complete analysis of your connections, you’ll need to utilize the audit journal. To analyze all TCP/IP connections, you’ll need to add two values to the QAUDCTL system value: *NETTELSVR to audit Telnet connections and *NETSCK to get all other IP connections. (If you want to analyze UDP connections, you’ll need to add *NETUDP.) Once you’ve added these two values, all connections will be logged. (Note that these values may generate a significant number of audit journal entries, so once your analysis is completed you may want to remove them.)
To analyze the connections, you’ll need to gather the SK audit journal entries. Here’s an example (you’ll need to fill in the appropriate start and end times and dates.)
CPYAUDJRNE ENTTYP(SK) JRNRCV(*CURCHAIN) FROMTIME(startdate starttime)
TOTIME(enddate endtime)
The Copy Audit Journal Entry (CPYAUDJRNE) command will, by default, produce a file in QTEMP called QAUDITxx, where xx is the two-letter audit journal entry type. So in this case, I now have a file in QTEMP called QAUDITSK that I can use for analysis.
There are many subtypes within the SK audit journal entry (for the full list, see the IBM i Security Reference manual, Chapter 9) but the subtype we’re looking for is ‘A’, meaning that the connection has been accepted. So right away, I’m going to use the following SQL statement to filter the SK entries to just look for the accepted connections
SELECT * FROM qtemp/qauditsk WHERE SKTYPE = 'A'
Even with this filter, you’re still likely to have a lot of entries. At this point, your next step depends on why you’re examining these entries. If you think you’ve gotten all connections secured, you may want to specifically look for connections coming in over unsecured ports. The following SQL lists the ports that the connections should be using; anything coming in over a different port will be listed. (Note: This is not a complete list of secure ports!)
SELECT * FROM qtemp/qauditsk WHERE SKTYPE = 'A' and SKLPRT not in ('22','443','992')
If you are just starting out with this project, you’ll probably want to be more selective in the entries. For example, if you want to ensure all Telnet sessions are encrypted, you can use an SQL that will only include cleartext Telnet sessions (that is, connections coming in over port 23).
SELECT * FROM qtemp/qauditsk WHERE SKTYPE = 'A' and SKLPRT = ‘23’
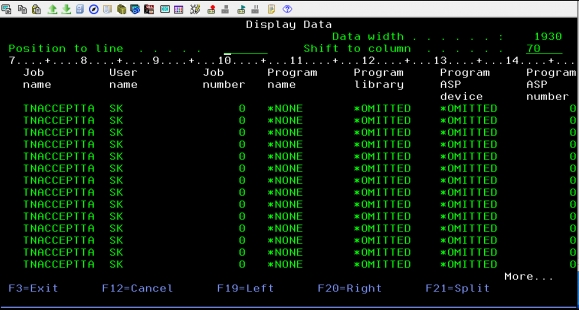
Now that you’ve selected the audit entries, how do you read/make sense of the information in the audit journal entry? For most audit journal entry types, I find the job name, user, and number helpful as well as the program and program library. But in this case, these fields are worthless. That’s because these entries are generated before the user’s job has started. Take a look at Figure 1 and you’ll understand what I mean.
Figure 1: These entries were generated before the user’s job started.
Likewise, the User profile field that typically contains the name of the current user is also worthless in this audit journal entry as it will always contain the value *NONE. So what is helpful about this entry? You’ll want to focus on these two fields:
- SKLPRT—Local port
- SKRADR—Remote IP address
To decipher where the connection is coming from, you’ll have to do a reverse DNS lookup using the remote IP address. You may also find the timestamp (SKTSTP) field helpful if the connections are coming from remote servers and you have to look through scheduled jobs to find the incoming task.
Helpful Hints
As you start to play around with the SK entries, you may be tempted to force a few entries to understand how to better read and understand what you’re seeing. (That’s what I always do when I start using an entry I’m not familiar with.) To force the entry, remember that SK entries log new connections; therefore, it’s not sufficient to simply log off your Telnet session and log back on. That will not generate an SK entry. You must close and reinitiate the session to get an SK entry generated.
In V7R3 IBM reworked the *NETCMN value such that it no longer logs accepts and connects. If you have *NETCMN specified in QAUDLVL and think you’re going to get the audit journal entries I’ve been describing, you won’t. As I said earlier, you must specify *NETTELSVR and *NETSCK (and NETUDP if you want to analyze your UDP connections) in the QAUDLVL system value.
Summary
As I said earlier, I encourage my clients to make sure all communications—external and internal—are encrypted. I hope this article will provide you with the information that you’ll need to either start this project or ensure it’s already been completed.



























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online