*ALLOBJ Authority with a Catch
In last month’s column, I discussed granting programmers *ALLOBJ authority, which can pose a problem in many AS/400 installations. This month, rather than recommend blindly granting programmers *ALLOBJ authority, I provide you with a solution that I have implemented for several customers: the Log Commands (LOGCMD) command. LOGCMD allows programmers to adopt special access such as *ALLOBJ authority but records all commands entered in the audit journal. In this column, I describe the user interface for this function and give you the technical details for its implementation.
As you implement LOGCMD, try to set aside time to learn from this example; it includes several simple techniques you can employ in some of your future programs:
• The authorization list controls which users can access the LOGCMD function.
• Parameters allow customization of the application without changing the program source.
• The command definition uses CONSTANT values to hide these parameters from users.
• APIs swap user profiles rather than change the user profile for a job to activate auditing in the process.
• Display file LOGCMDDSP1 illustrates how a window displays information.
User Interface
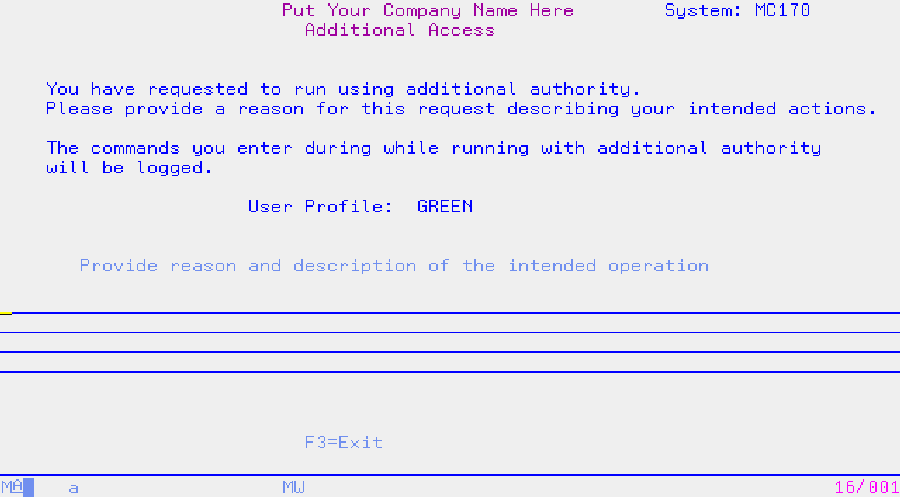
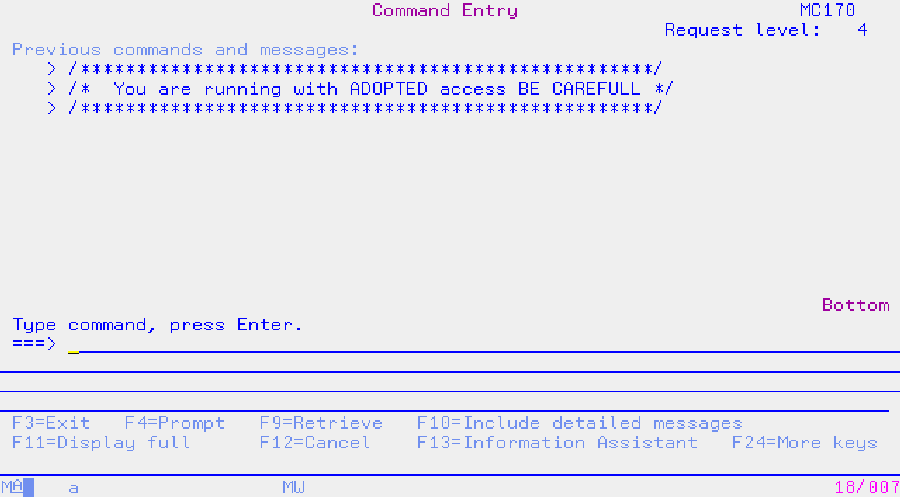
As shown in Figure 1, when you first run LOGCMD, you must enter a reason code that describes your intention to use *ALLOBJ support and press Enter for access. A screen like the one shown in Figure 2 then appears, in which you can enter, prompt, and retrieve commands, as on the IBM OS/400 Command Entry screen, and the commands you enter are logged to the audit journal. To minimize the volume of data logged, press F3 to exit after you complete the task at hand. For every 10 commands you enter, a reminder message appears, warning you to exit the program as soon as you complete the job that needs *ALLOBJ authority.
Technical Description
Figure 3 illustrates the flow of the different segments of the LOGCMD program objects. The command definition source (which you can retrieve at www.midrangecomputing. com/mc/) has four parameters that set the scope for *ALLOBJ support. You can change the parameters to constants customized for your installation:
• &HANDLE passes user profile swap handles from program LOGCMD1 to program LOGCMD2. This 12-character field uses Transfer Control (TFRCTL) command, so all parameters passed must be external to LOGCMD1. You should not modify HANDLE.
• &JRNCDE logs reason codes and user requests in the audit journal. If you want
to modify this two-character field for other commands, you first need to change the LOGCMD_RPT selection criteria to match.
• &PGM issues commands. You can change this parameter to specify different programs, but the libraries in which the programs reside must be on the library list.
• &REMIND specifies the number of commands you can enter before the reminder screen appears.
Creating the Application
Here is a step-by-step solution to implement LOGCMD:
1. Create an authorization list that allows you to control which users can access LOGCMD:
CRTAUTL LOGCMD AUT(*EXCLUDE)
You create the authorization list first so you can immediately secure commands and programs as soon as you create them.
2. Customize display file LOG-CMDDSP by adding your com-pany name and information to the source.
3. Create display files LOGCMDDSP and LOGCMDDSP1 in a library that is on the library list during execution and compilation of the CL programs:
CRTDSPF DSPF(your-library/LOGCMDDSP) + AUT(*CHANGE)
CRTDSPF DSPF(your-library/LOGCMDDSP1) +
AUT(*CHANGE)
4. Create program LOGCMD1 to adopt the authority of the program owner:
CRTCLPGM PGM(your-library/LOGCMD1) +
USRPRF(*OWNER) LOG(*NO) +
ALWRTVSRC(*NO)
5. Change the owner of LOGCMD1 to a user profile with *ALLOBJ and *SECADM authority:
CHGOBJOWN OBJ(your-library/LOGCMD1) +
OBJTYPE(*PGM) NEWOWN(QSECOFR)
The owner of LOGCMD1 must have *ALLOBJ and *SECADM authority specified in the user profile so the API can get a profile handle without a password.
6. Create program LOGCMD2 to adopt the authority of the program owner:
CRTCLPGM PGM(your-library/LOGCMD2) +
USRPRF(*OWNER) LOG(*NO) +
ALWRTVSRC(*NO) AUT(LOGCMD)
7. Change the owner of LOGCMD2 to a user profile that you want users of LOGCMD to adopt:
CHGOBJOWN OBJ(your-library/LOGCMD2) +
OBJTYPE(*PGM) NEWOWN(user-profile-to-adopt)
The owner of LOGCMD2 should have the special authority needed for the programmer to access the objects.
8. Create program LOGCMD3 to adopt the authority of a user with *ALLOBJ and *SECADM authority:
CRTCLPGM PGM(your-library/LOGCMD3) LOG(*NO)
ALWRTVSRC(*NO) AUT(*USE)
9. Create the LOGCMD command:
CRTCMD CMD(your-library/LOGCMD) PGM(LOGCMD1)
AUT(LOGCMD)
Figure 4 shows examples of commands logged by this utility.
LOGCMD is a powerful addition to your collection of security tools but must be tailored to your shop’s needs. Pay special attention when setting up your authorization list and don’t forget tocustomize the display files and programs for your operation and test the utility thoroughly before releasing it to production programmers.
Figure 1: Enter a reason for having *ALLOBJ authority on this screen.
 |
 |





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online