(Editor's note: To read this article in Spanish, click here. To read it in Portuguese, click here.)
The Global Commerce Initiative (GCI) defines Global Data Synchronization (GDS) as "The continuous harmonization of data attribute values between two or more different systems, with the end result being the data attribute values are the same in all of the systems."
Trading partners--both demand-side (retailers) and supply-side (manufacturers)--face unnecessary costs due to master data problems, such as supply chain information inefficiencies, inaccurate data in transactions, invoice errors, warehousing/transportation errors, product ordering errors, etc. By continuously synchronizing master data, you will ensure it is the same in all systems. This will allow you to trade efficiently and globally, driving costs out of your supply chain.
Figures 1 and 2 below highlight the types of earnings before interest and tax (EBIT) benefits retailers and manufacturers, respectively, can expect to achieve by participating in GDS.
Figure 1: For demand-side (retailers), the benefits of GDS participation can represent up to 10 basis points of savings on total annual sales. (Click images to enlarge.)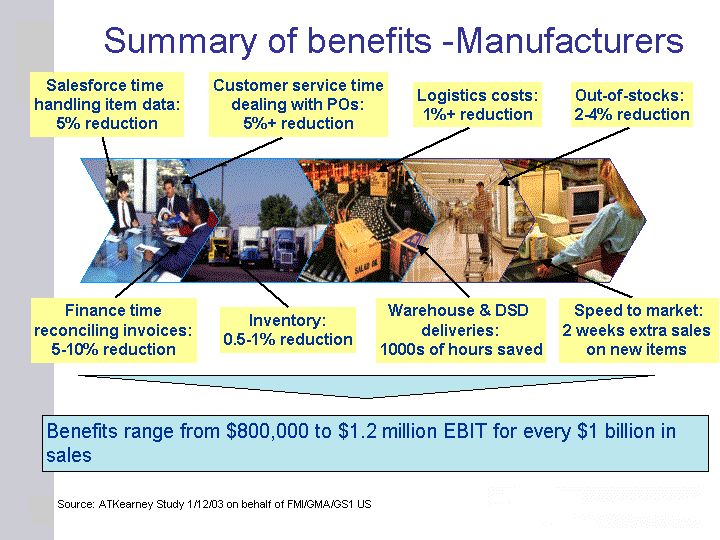
Figure 2: For supply-side (manufacturers), the benefits of GDS participation may exceed 12 basis points of savings on total annual sales
What Is the Global Data Synchronization Network?
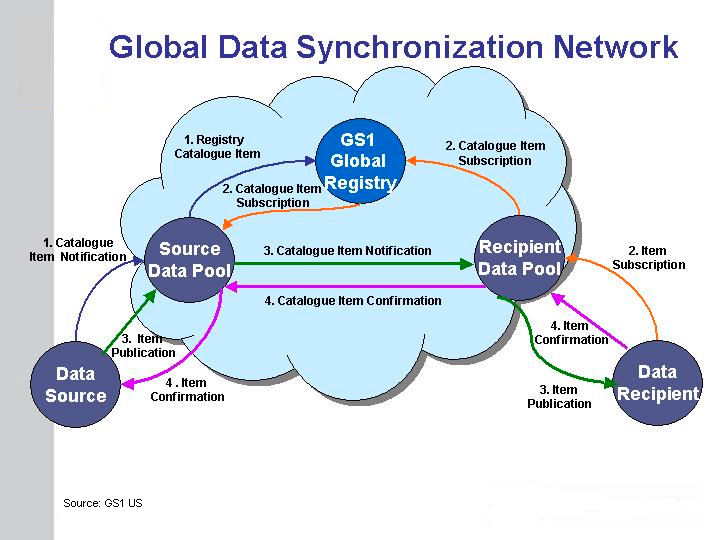
The Global Data Synchronization Network (GDSN) is a network of interoperable ("certified") data pools and the GS1 Global Registry. The GDSN allows the timely and "auditable" distribution of certified, standardized master data (trade item and party) from a data source to a final data recipient. Trading partners have a single point of entry to the GDSN through the certified data pool of their choice.
Within the GDSN, trade items (a.k.a. catalogue items) are identified using the Global Trade Item Number (GTIN) and Global Location Number (GLN) of the data source and target market while parties are identified using a GLN only.
How Does the GDSN Work?
Figure 3 below illustrates how a business may use the GDSN.
- Suppliers prepare internal data and systems to match EAN.UCC System standards (GTIN, GLN, etc.).
- Suppliers upload their data to the GS1-certified source data pool of their choice.
- The data pool sends basic information about each item (or party) to the GS1 Global Registry, which holds this information and the location of each item's (or party's) data pool.
- Retailers search the GS1 Global Registry via their recipient GS1-certified data pool for the item or party for which they want to subscribe. The GS1 Global Registry identifies the source data pool of the requested item or party.
- Trading partners perform the publication/subscription process. Thereafter, item (or party) information can be automatically and continuously synchronized between their respective data pools.
Figure 3: This image shows how the exchange of information between data source and data recipient works.
What Is the GS1 Global Registry?
The GS1 Global Registry (GR) is a central directory that provides information for subscription sharing. It ensures data pool interoperability and catalogue item uniqueness by registering items and parties. It provides the following:
- Uniqueness: Each catalogue item (GTIN + GLN + target market) must be unique for a particular data source.
- Data Quality: The GR will only register data from certified data pools, thus ensuring that all data pools comply with a basic set of validation rules that support data integrity in the system.
- Subscription Data Router: The GR associates GLNs to a data pool.
Who Has Adopted the GDSN?
Adoption of data synchronization has been significant over the past three years. The UCCnet Data Pool has over 4,300 customers, including over 35 retailers. Wal-Mart, Wegmans, SUPERVALU, and others are already in production. Transora (founded by suppliers) has nearly 300 customers. Because Transora represents many large, dominant suppliers (Procter &Gamble, Unilever, Gillette, Johnson & Johnson), it is the entry point to GDSN for a significant number of the GTINs most demand-side entities need. Transora also represents a growing list of retailers: Kroger, C & S Wholesale, Wakefern, Publix, Schnucks, and others. These two organizations are rapidly expanding GDSN adoption.
WorldWide Retail Exchange (WWRE) was founded in 2000 by 17 international retailers "to enable participating retailers and manufacturers to simplify, rationalize, and automate supply chain processes, thereby eliminating inefficiencies in the supply chain." Some of WWRE's founding and charter members include Ahold, Albertson's, Best Buy, CVS, Group, El Corte Ingl?s, Marks & Spencer, and Safeway. WWRE is very active in the areas of chain drug stores and consumer electronics.
Adoption is advancing quickly in the United States and is advancing in other areas of the Americas as well. Giovanni Biffi, senior IT consultant of CABASnet (a data pool in Bogota, Colombia, serving Colombia, Peru, and many Central American countries) said of their GDS participation, "We are working with two retailers and two manufacturers through GDSN: Almacenes Exito, Carulla, C.I. Hermeco, and Compa??a de Galletas Noel. We expect to have two more retailers soon and 25 members by year end. Local synchronization efforts are very successful. Currently, we have more than 150,000 products from 4,000 manufacturers, guaranteeing data quality for the products. Five hundred suppliers work with our Web-based GUI, and we expect to soon have 200 manufacturers connected and exchanging information through the CABASnet data pool."
David Garcia, Transora's vice president of Global Sales and Marketing, said, "Retailers and manufacturers are implementing Transora's data pool solution to synchronize valuable supply chain data around the world with their trading partners. Some companies begin data synchronization activities with core item data, then move to more advanced functionality to incorporate trading partner-specific information, such as price and promotional data. As a result, clean item data and an agreed-upon product assortment to be sold by retailers are a couple of the benefits gained from data synchronization."
Dan Wilkinson, vice president of Business Development at UCCnet, said, "Since UCCnet launched its data synchronization initiative in 1998, its mission was to make data synchronization easy, accessible, and affordable. The creation of the GDSN takes this effort to the next level. Each new participant in the GS1 Global Registry increases the collective value of the Network for every participant because as the number of trading relationships increases so do the trading relationship possibilities. For UCCnet, it's critically important to be at the forefront in driving mass adoption efforts of the Network as it expands geographically and into new industry verticals. Expansion drives up the value for our UCCnet data pool subscribers and drives down costs for all participants in GDSN. Our primary goal is to drive mass adoption of the GDSN and expand the user base so that the entire business community can realize the benefits of accurate, standards-compliant supply chain information."
The GDS adoption rate is increasing rapidly. Information from the GS1 Web site indicates the rates of adoption for Registered GTINs, Subscriptions by Item, Subscriptions Matched, and Subscriptions Sent, as shown in the table below.
| GDS Adoption Rate | |||
| February 11, 2005 | May 13, 2005 | Percentage Increase | |
| Registered GTINs | 192,222 | 301,624 | 57% |
| Subscriptions by Item | 6558 | 15,561 | 137% |
| Subscriptions Matched | 155,400 | 301,348 | 94% |
Subscriptions Sent | 13,932 | 37,807 | 171% |
Significant Business Enhancements to Data Synchronization
Although the past year has produced many notable changes to the GDSN relative to the components that make it function, less visible changes have also occurred. These include changes to the processes, practices, and messaging that facilitate the synchronization cycle. Changes and enhancements to the process are varied in scope, yet a few stand out as notable advancements in areas that historically have been problematic. Multi-source distribution, the passing of category-specific attributes, and the exchanging of pricing are some processes that have received significant attention.
Multi-Source Product Synchronization
Multi-source products (private label or store brands) have long been an issue in GDS because of the unique circumstances surrounding their production and distribution. Examples of issues common to parties involved in multi-source product synchronization include inconsistency among the various definitions of a given product, brand owner participation in the GDSN, and the information provider's role in the synchronization. Task groups have collaborated to establish proposed solutions to these and other issues to advance multi-source product synchronization.
The task groups recommend that a baseline administrative record be established as a reference point for subsequent representations of any given product, which will be defined and maintained by the product's brand owner. Also, when a brand owner isn't participating in GDSN, a proxy can be nominated as an administrator.
Facilitating Attribute Extensions via the "Hook"
As product information is exchanged via GDSN, it's common that the attributes vary from category to category. To facilitate this attribute variation, category extensions have been added. These new attribute extensions will be known as Candidate Attributes until they become approved standards. As users of these attributes, it's important to be aware of their potentially fluid nature until becoming a standard. Of the extensions developed or revised over the last year, extensions for Office Supply and Entertainment and for retailer-specific attributes will soon be in use.
As important as the extensions themselves is how those attributes are included in exchanged XML documents. In that regard, a notable change is the inclusion of these extensions using a "hook" (a specific point of inclusion) within the documents. Using the hook method, the attributes are grouped and included in the XML in a consistent manner, regardless of the extension. This method paves the way to more easily define additional sets of extended attributes, which is key for the synchronization of more product categories and potentially recipient-specific information.
Relationship-Dependent Data and "Complex Pricing"
Recipient-specific attributes may be facilitated by the hook, but another aspect of product synchronization revolves around pricing, specifically "complex pricing." In many cases, pricing is specific to the customer who buys each product. To handle this kind of information in the network, a new command structure, Relationship Dependent Data (RDD), is being finalized. RDD's goal is to facilitate the definition and communication of complex pricing arrangements as they relate to each customer. The command structure supports this by using two documents: One describes the monetary values involved, and the other depicts the conditions under which those values apply. Combined, these documents provide the ability to specifically represent and exchange pricing as part of a real-world business process.
Significant GDSN Business Events of the Past Year
It has been a busy 12 months in the GDS world, seeing the separation of the GS1 Global Registry from UCCnet, the creation of the GDSN, the first round of data pool certifications, and two changes in data pools. Below are some perspectives on what we see as the three key events: the separation of the GS1 Global Registry, the resulting creation of GDSN, and two industry mergers.
Independent Global Registry
The first major development was the GR's separation from UCCnet and its establishment as a separate entity under GS1. This separation provides the basis for the GDSN to expand and grow. While this change initially created some confusion in the market and may have slowed short-term adoption, from a long-term perspective, the new structure is likely to be good for all parties in the global supply chain. The separation of the GS1 Global Registry combined with the formation of the GDSN provides three critical benefits:
- Fosters competition and advancement of functionality in the Global Standards Management Process (GSMP)-GDSN worlds
- Sets clear standards for how data pools become certified and thus participate meaningfully in the worldwide supply chain
- Introduces free markets to the GDSN world; the adoption of the standards and certification process allows data pools to compete on quality and variety of services and price. History has generally shown that this sort of free market environment fosters innovation and efficiency.
WWRE-GNX Merger
The second major development was the April 2005 merger between WWRE and GNX. WWRE is a data pool largely founded and funded by large retailers. GNX is known within the industry as Retail Connect, providing e-business solutions and services that connect retailers, manufacturers, and their trading partners. Under the agreement, the combined entity will operate under a new name, as of yet undetermined. As we have not worked extensively with these two entities, we cannot comment meaningfully on their merger or its impact.
UCCnet-Transora Unification
The third major business development was the May 2005 announcement by UCCnet and Transora of their intended unification. The first paragraph of the press release announcing this change says: "UCCnet and Transora have agreed in principle to unite their operations, business strategies, and vision to ultimately form a single organization that can more effectively serve companies seeking to realize the value of data synchronization. Once approved, the new organization would be a subsidiary of UCC. The shared vision is to leverage the strengths of the two organizations by assisting retailers and manufacturers to more quickly realize the value of data synchronization."
In theory, this merger has the potential to benefit GDS. UCCnet, one of the original data pools, has made huge strides in providing a clear way for companies to quickly get on board through its TESTregistry and then move seamlessly to production. UCCnet has reduced the complexity for small suppliers to participate in the GDSN by providing simpler and more cost-effective plans that allow them to join one organization under one contract and receive data pool services, GS1 Global Registry subscription, and onboarding support. UCCnet has also worked to reduce the complexity and cost of subscription for larger participants and worked extensively to bring GDS to new industries, such as Consumer Packaged Goods (CPG), Hardlines, Office Supplies, and Alcoholic Beverages.
As for Transora, along with its U.S. data pool services, its representation of the majority of the GTINs in the GR, and its growing number of retailers, it provides significant international operations, plus complimentary services (price and promotion synchronization, etc.) that many of their customers desire and that many of UCCnet's customers likely desire but which are outside of the scope of the GDSN.
The combined UCCnet-Transora entity could be of real benefit to the global supply chain and the advancement of GDSN. This alliance brings together the biggest suppliers, the world's largest retailer (Wal-Mart), and a significant base of major retailers, offering good domestic and international operations and ancillary services that many companies desire.
Don't Be Left Behind
Much analysis and study of data synchronization has been performed, and we provide you with plenty of reference material in the sidebar at the end of this article.
The initial idea of data synchronization as outlined in the "Action Plan" is good. The benefits are real. As shown in "Global Data Synchronisation at Work in the Real World," participation in GDS returns about $1 million per billion in sales to participants' bottom lines.
With the reasonable costs now available for data pool services as well as the software and implementation services required to integrate companies' installed ERP systems with a certified data pool, these projects can now be easily cost-justified and should move ahead rapidly.
GDS may have gotten off to a rough start: The complexities of the data pools were not fully worked out; software and implementation were not streamlined (all projects being large and customized), and Structure of the GDSN (separate Global Registry) was not exactly right.
But that is not where we are today. Today, we have data pools that work, functionality that is increasing rapidly, and prices for both data pool and implementation onboarding that have dropped to easily manageable levels, permitting projects with great ROI. Participate now, or face competitors with more efficient supply chains and lower cost structures than your own.
Jeff Holzman is LANSA's director of solution product sales and regional director of Latin America. Jeff is responsible for moving LANSA into the GDSN business and has led the company's international expansion. Jeff welcomes any questions you may have; you may reach him at
Randy Mercer is the solutions group manager at LANSA's GDSN product lab and represents LANSA as a voting member of the GDSN Task Group. Randy has led the implementation of GDSN solutions at many Fortune 500 companies and is currently leading the movement of the Alcoholic Beverage Industry to GDSN.
Sidebar: Useful References and Information Resources
- GDSN reports and materials
- Trading partners currently using GDSN--Go to http://www.gs1.org/ and look for Trading Partner statistics
- "Action Plan to Accelerate Trading Partner Electronic Collaboration"--Case studies that outline the benefits of GDS to supply-side entities
- "The Case for Global Standards: Creating the Business Case for Global Data Synchronisation in Your Company"
- "Global Data Synchronisation at Work in the Real World"--How to benefit from the lessons of the last few years
- GDSN FAQs
- Global Standards Management Process (GSMP)-GDSN Task Group
- GDSN Background and other useful resource materials
- A GDSN Overview





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online