In the book/movie The Princess Bride, Inigo Montoya says, "You keep using that word. I do not think it means what you think it means." Whenever I hear the phrase "On Demand," I am haunted by Montoya's words.
What could it possibly mean, other than "what a business wants, when the business wants it"? Isn't it just another clever marketing ploy? Isn't the analogy that of a faucet? Want water? Turn on the faucet. Want computing [scaling/software/hardware]? Call IBM.
I do not think it means that. In fact, the depth of what On Demand at IBM really is will surprise you. I guarantee it. And I'm the kind of person who would scoff at such a guarantee. As a consummate IT professional who has spent most of my life around computers, nothing surprises me anymore. It's all the same old stuff, with different jargon, a different wrapper, right? If you feel the same way, then you should definitely read on.
I was fortunate enough to get an interview with Ian Jarman, Product Manager for the IBM iSeries. After our conversation, I was convinced of two things: 1) I did not know what e-business On Demand meant; 2) he did.
It Means Integration
"One of the themes of On Demand," Jarman said, "is the integration of technology, processes, and people so that a company can dynamically change and react to business opportunities." It seems that "integration" is another one of those words that does not mean what I though it meant, since I had only associated it with services integration at a software level.
The first experience I had with On Demand (although I didn't know I was having an On Demand experience), was at a Service Oriented Architecture (SOA) "boot camp" for IBM Senior Architects. At that time, my conception of SOA was simple: Web Services, which would sometimes involve the use of J2C adapters. SOA is a software design architecture that has at its core the integration of disparate software providers, hiding the implementation details of those providers by exposing only their "description" in a Web Services Description Language (WSDL) document. The consumer of the service knows what the various pieces of software provide, but not how they're provided or where these services originate. An ancillary (though not accidental) feature of this design is the decoupling of these software "partners" (a term taken from Business Process Execution language, or BPEL) from their central integration controller core, allowing the implementations to change completely, without affecting this core. This makes the software flexible and quickly responsive to sudden changes in business needs, which would affect the software.
This type of architecture is facilitated by WebSphere Business Integration - Server Foundation (WBI-SF, or "The Middleware Formerly Known As WebSphere Application Server, Enterprise Edition"), and in a very elemental way, it embodies the idea of integration. But, as Jarman's words imply, at a much higher level than integration within the technology, On Demand is the integration of technology with the business it serves--an entirely different concept than that of "technology as a tool of business." In this light, it becomes apparent that a tool such as Business Process Choreographer (BPC) is part of a grander design.
BPC generates BPEL, which executes in the business process engine of WBI-SF. This BPEL is an accurate reflection of the business model. The components of this business model are linked to implementations under the covers, but it is the business model that drives the choice of implementation; that is, the choice may be based not on the cost of the IT development cycle or the performance of one technology over another, but rather the likelihood that the preferred provider of this credit reporting service today may not be the preferred provider tomorrow. Another provider may emerge that is more cost-effective and offers the same or higher quality of service. Thus, a Web Service implementation, as opposed to an application, is a better choice, solely because of its flexibility, its ability to "dynamically change and react to business opportunities."
Also, rather than technology replacing people in business processes (Charlie Chaplin's fear in the movie Modern Times), e-business On Demand requires the "integration of people...." This idea brings into focus the staff functions of the business process engine's functionality, (an IBM value-add, beyond the BPEL4WS specification). Staff allows us to choose a person as the implementation of a business process component, just the same as we might have chosen a Web Service, and for similar reasons: It would be the best choice in terms of cost-effectiveness and flexibility in this particular case, as indicated by the results of business analysis. Thus, the Integration in WebSphere Business Integration - Server Foundation has really taken on a new, much deeper meaning with the advent of On Demand.
Jarman reminded me that WBI-SF is not the first IBM product to have integration at its design basis. "(The iSeries) has always been an integrated platform: customer data integrated for various applications on the same machine." It is, then, a logical progression that the iSeries continues this tradition of integration with WebSphere: "WebSphere is an integrated middleware product. Integrated middleware is the defining differentiator, if you will, for the iSeries versus other platforms, because we do integrate the database with the operating system. I would say that WebSphere is as important to the future of the iSeries as the integration of DB2 into the iSeries has contributed to our success today."
At another point in our conversation, Jarman repeated his definition of On Demand, but with a slight, yet profound twist: "(E-business On Demand) is the integration of technology, processes, and people, to help businesses grow." It is this very integration that will make the business grow. More important, without this integration, the business will not grow.
This certainly turned me around: E-business On Demand originates at the business end of the spectrum, motivated by the dynamically changing demands of our customers' businesses. Further, it represents IBM's understanding of the way today's business world is and IBM's ability to translate that understanding into a practice. Says Jarman: "This is not a marketing campaign; it's not one product. It's a way of doing business that our customers are implementing. And we are trying to help them implement those On Demand processes and adjusting throughout IBM to react to the very dynamic nature of business today. The concept of On Demand would be implemented as a business strategy, not a technology strategy."
It Means Autonomic Computing
A recent series of television commercials shows an insurance company rep appearing at some bewildered person's house with a new car. The person at the door doesn't understand the need for a new car because the old one is in perfect shape. The rep then calls the main office, only to discover that he is two days early: The customer won't total the old car for another two days. It seems as though the insurance company is able to see into the future.
Substitute, if you will, the insurance rep with an IBM customer engineer, who appears on site unsolicited (as far as the IT admin is aware) and says, "I'm here to replace your hard disk." IT admin says, "But I haven't lost a hard disk," and the engineer replies, "Oh, but you will in two days."
I'm not sure about the "reality" of the insurance ad, but I am sure that the IBM story is real; the iSeries has the ability to automatically dial up for service in anticipation of a failure. Of course, it's not the auto-dialing that's impressive; the insurance company could probably do that. It's the ability to predict the failure with a high degree of certainty that is impressive. Although this might be called precognition in humans, IBM considers it one of the themes of autonomic computing, another principle of e-business On Demand.
Instead of precognition, let's call it preemptive symptomatic analysis: the classification of certain behaviors as "symptomatic" of failure and the use of this classification to pre-determine systems failure and prevent it. The human body tries its best to do this type of thing. Unfortunately, the body often doesn't respond to, or even trust the validity of, the warning data it receives. We've all felt that moment of denial, when our throat gets a little scratchy, we have to clear our throats repeatedly, and we feel (more) exhausted (than usual). You've got it, buddy: the upper-respiratory bogey has arrived! At that point, we could start pounding the Echinacea, put a garlic wreath around our necks, get an H2O infusion, etc., but we often don't. Well, i5/OS is smarter than that. It believes what its sensors report as symptoms of a failure and dials up your IBM service engineer for a house call!
This symptomatic signaling, or "self-healing," is certainly a foundation for the concept of autonomic--and I must always stop myself before I write "computing" immediately after "autonomic" because all these concepts apply to business as well as to computing. For example, any successful restaurateur must develop a premonitory sense of dining trends to avert lost customers: If some diet magazine advises its readers of the tremendous weight-loss potential of cutting the ketchup, and all the entrees come slathered in ketchup, the customers might just stop coming, rather than think to say, "Hold the ketchup." The restaurateur might need to put up a sign that says, "We boast a ketchup-free menu!" Perhaps an absurd example, but perhaps not: Nothing the customer does should be considered absurd; at least, customer behavior should never be considered meaningless. Call it a fad if you will, but that fad can destroy the business that doesn't develop the agility to react to consumer trends.
It Means Virtualization
While critically important, it wouldn't really be sufficient for a computer to just preempt disk failures all the time or for a restaurant to focus solely on just keeping the doors open. The focus must go beyond protection of resources and consider the optimization of those resources. Thus, IBM adds "self-optimizing" to "self-healing" in its definition of autonomic computing--that is, not just keeping the doors to the restaurant open for business, but keeping all the tables at the restaurant full at all times.
How often does it happen, you suppose, that large restaurants often turn hungry customers away for lack of tables, while staring directly at scores of empty tables with "Reserved" signs on them? Yet, Jarman notes, "...most companies face the challenge that they have server farms with underutilized assets because each server is dedicated to an individual application." The IBM solutions to this problem fall under the heading of virtualization.
Let's start with a familiar form of virtualization: partitioning. Partitioning is simply the division of a CPU into sub-segments, or "virtual blades." Formerly a standard concept on just the main frame, partitioning is now applied to operating systems like Linux and Windows. The fact that partitioning is now done dynamically, or as needed, or, yes, on demand is what makes it so powerful for e-business.
On the iSeries, this is referred to as Capacity Upgrade on Demand (CUoD). Say that your CPU usage varied such that you required multiple processors at peak times, but you required only one at low-demand times. Simple enough: What was one processor now becomes--or rather, behaves like--four processors, and the workload is balanced across them.
Let's extend this a bit: Say that we have a Regatta server with one CPU running AIX, which hosts our main database and our most important WBI applications. This database is used by other applications that run on either Linux or Windows. Of course, our WBI applications can run on AIX, Windows, or Linux, too. Multiple operating systems are not an uncommon situation in many e-business environments today. There are a number of things that businesses require of this computing infrastructure, and e-business On Demand from IBM delivers.
First of all, we can partition our "frame" into one Linux and two AIX. Or one AIX and two Linux. Or...well, you get the picture: Mix and match is allowed. If usage demands, we can spawn a new virtual blade dynamically, creating rules beforehand, of course, as to which OS is hosted on the new processor.
Enter the Virtualization Engine (VE), now a feature of all the IBM eServers. The VE, first of all, views and manages all these partitions in a consistent manner, allowing processes, such as WBI's Java Virtual Machine (JVM), to "borrow" processing power that it requires from other, presently underutilized processors (partitions) on the same machine.
But what about Windows? What about multiple physical machines? You now have the ability not only to balance workloads across physical machines and share resources across these machines, but also to break the chip barrier (my own phrase). First, the Virtualization Engine grid services directly communicate with any/all physical servers in an integrated system. Then, if you want to run, say, a Windows system on an xSeries Intel server and an iSeries running POWER5, these can be integrated using a shared storage adapter called Integrated xSeries (IXS), like a blade that plugs into the iSeries.
With all of these CPUs spawning and sharing all over the place, how is it that IBM does its pricing on a CPU basis? If this kind of flexibility is provided by integration and virtualization, wouldn't the pricing model have to be dynamic as well? Jarman gave me an insightful example of how, in one well-known tech segment, consumers demanded flexible, tightly refined pricing and got it: the cell phone.
The incorporation of cell phones into world society was certainly rapid, as was the dynamic change in every aspect of that industry, from phone design to pricing. The initial pricing model was traditional, rigid: The providers charged a lot of money for a pre-determined number of minutes and then a lot more money for every minute the phone was in use beyond that number. If you used fewer minutes, you certainly weren't charged less.
Now, of course, rollover minutes, pay-as-you-go plans, no charge for dropped calls, and no charge for wrong number incoming calls are pretty standard components of pricing plans, as is the ability to switch plans quickly to accommodate varied usage patterns. This reflects precisely the public's "on demand" savvy.
IT consumers are no less savvy or demanding. Your JVMs may be fully utilizing three CPUs and a bit of a fourth CPU. Would you like to pay the price for four full CPUs? Enter IBM's subcapacity pricing, a pricing scheme that "takes into account the dynamic nature of software use" (Jarman). Either IBM monitors the customer's usage or the customer simply submits monthly usage reports. But, in any case, Jarman says, "they demand flexibility in the way they do business with their suppliers: [IBM] need[s] to have flexible pricing that adjusts to the dynamic nature of business today."
At this point, I always like to point out the wisdom in all of this: We all know that the IT industry thrives on--and ultimately innovates by virtue of--competition. By the same token, IT management would probably say that many (most) of their headaches come from the disparity produced by this competition. They also know that the only way e-business will ever function at the level business demands is for all of the proprietary technologies to fit together seamlessly, but loosely coupled enough to allow for rapid change.
Sounds like a pipe dream, but modern business demands it, so it cannot be a pipe dream. IBM knows that the demand must be met. Shoulder shrugs and don't-look-at-me looks are not an option. Many attempts have been made over the years to solve this puzzle. Basically, these attempts fall into three categories: domination, assimilation, and interoperability. World languages provide us with a good analogy. The initial premise is, of course, that if everyone speaks a different language, no one can communicate. Simple as that. Domination would say that everyone will speak one of the world languages. Didn't work with Latin. Assimilation would require every language to contribute a piece to a new, synthesized, but still singular way of doing things. Esperanto is a language created synthetically, by combining features of all world languages. Do you speak Esperanto? Neither do I (although I applaud the intellectual effort of its inventor). The third tack is interoperability: This allows everyone to do their own thing but agree on a common interface. Something like French or English as a lingua franca would be good examples of this. Unlike the first two, the "interface language" approach has proven quite successful. The corollary for e-business has been open standards, the final piece in IBM's e-business On Demand strategy.
It Means Open Standards
"Open standards" is not the same thing as "open source." Open source is the practice of making your source code public rather than proprietary. While this has provided many powerful Linux applications, it has not provided us with Linux itself, nor with the high-profile applications such as OpenOffice or Evolution, for example. These were the result of open standards, not open source.
Clearly, IBM has provided real response to the demand for interoperability through almost ubiquitous adoption and support of the JVM, or, more exactly, the JVM specification--in my opinion, the most important demonstration of the power of open standards in the last 10 years--in most of its software product set, from DB2 to ICS. Many people are likely unaware of the millions of dollars IBM has dedicated to improving the JVM for Windows and Linux.
The JVM would not have succeeded, however, without the evolution of the J2EE specification, insofar as J2EE codified and made standard technologies that were de facto communication protocol standards, such as HTTP, Internet Inter-ORB Protocol (IIOP), etc. Still, WebSphere's true strength is realized at the point it goes beyond Java, or, rather, where it connects Java to the rest of the computing world through the collection of open standards that support SOA, (e.g., WSDL and J2C, both based on specifications created, enhanced, and donated to the open standards community by IBM). Jarman points out, "WebSphere is obviously the integrating and extending middleware that brings together not only the existing applications that you have today, but also extends to the new applications that you're deploying to grow in the future." And that's the ticket--the future. While some integration technologies may allow today's applications to work together, it is only open standards that ensure that tomorrow's applications will.
The On Demand Operating Environment
The most accurate summary of what I've mentioned in this article will not be a summary paragraph inserted here. The examples I've given to illustrate e-business on demand should have rendered you incapable of coming up with a simple, coherent answer to the question, "What is e-business on demand?" unless your answer would be, "On demand is as much a way of thinking as it is a way of doing business."
Alternatively, I could (and will) leave you with picture: a formal model of the discrete system that encompasses and describes IBM's on demand visions: the On Demand operating environment (ODOE).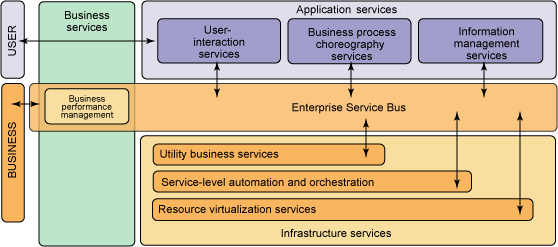
(Click image to enlarge.)
An On Demand enterprise has greater focus, heightened responsiveness, variable cost structures, and improved resilience. The ODOE, then, is a model for an agile IT environment, which facilitates these four characteristics. Let me emphasize that the ODOE is a model, not a product, not something concrete, shrink-wrapped, and ready to deploy out of the box.
But the thing is, it makes a lot of sense to me. It makes a lot of sense to a lot of people at IBM, and I say this as an IBMer. I see On Demand everywhere, permeating everything we do. It's present at all our meetings. I see it in the code I write. And when I see it, it makes sense to me.
If it makes sense to you, then you've already taken the first step in what may prove to be a journey that will ultimately grow your business. The hard part, for some anyway, is that there is no end in sight. In fact, what inspired the title of this article was the title of the chapter "A Journey, Not a Destination" in Jim Hoskin's book, Building an On Demand Computing Environment with IBM: How to Optimize Your Current Infrastructure for Today and Tomorrow. Reading this book may be your next step.
Kameron Cole is currently a Senior Learning Specialist with IBM ITES (IT Education Services), where he does instruction, onsite mentoring, and course development for the complete range of WebSphere course offerings. He is IBM certified for WebSphere Administration and J2EE Development up through V6 and Sun certified for J2EE Developer. He was a contributing author to an MC Press certification guide for WSAD V5, Developing J2EE Applications with IBM WebSphere Studio. Kameron has nine years of Java development experience, including CORBA-to-Java implementations. He is most at home on Linux or AIX.
In another life, Kameron is a cellist and currently can be heard on Jen Gloeckner’s new CD, Miles Away, on One Little Indian records.























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online