One of the most daunting obstacles facing iSeries and AS/400 administrators has been computer virus infection. This is not because the native iSeries itself is particularly susceptible to infection (it's not!). Rather, as a server hosting and delivering PC- and UNIX-derived files on its Integrated File System (IFS), the iSeries can harbor viral contaminants, worms, and Trojan horses that have been uploaded to the IFS by client machines. These viruses can be promulgated throughout the network among the client machines, creating serious damage while simultaneously leaving the organization open to liability damages from other companies with whom the iSeries network does commerce.
Still, some iSeries customers labor under the delusion that the iSeries is immune to viruses as long as they keep the IFS locked up. Unfortunately, this is no longer true, as the iSeries is based upon the same RISC technology as the pSeries, and as the differences between their underlying technologies grow smaller with each release. As OS/400 moves to embrace Linux and UNIX subsystems, it's opening itself to the same contaminants that impact those operating systems. So the belief that the iSeries today is immune to viruses is a myth: iSeries IT administrators must approach anti-virus security with the same focused attention as Windows NT/2K and UNIX administrators.
Unfortunately, until recently, an iSeries administrator had few tools to directly manage this kind of data infection.
One of the few options employed by many is to load up a PC with virus-scanning software and connect it to the iSeries. However, this solution is a severe security hole: In order to be effective, the scanning PC must be signed on to the iSeries with *AllOBJ authority and pointed to the root folder of the IFS. This leaves the iSeries vulnerable to hacking by others on the network.
Furthermore, an IFS-scanning PC is incredibly slow, tying up network bandwidth while simultaneously being subjected to technical interruptions.
The bottom line is simple: Though the iSeries object-oriented architecture itself is still relatively secure from viruses, its IFS--containing user PC data--is a natural viral incubator for real problems that can shut down the entire network. And the more IBM upgrades the iSeries to make use of the IFS, the more vulnerable it will become.
Bytware's StandGuard Anti-Virus
Now, Bytware has joined forces with Network Associates (of McAfee Security fame) to deliver the first and only native iSeries virus detection solution. Called StandGuard Anti-Virus, the product was engineered by Bytware and is powered by the McAfee Security technology.
The product does exactly what you expect an anti-virus suite to do, except that it does it on the iSeries platform much faster than its PC counterparts. According to Bytware, StandGuard Anti-Virus...
- Scans the entire IFS file structure using native iSeries software
- Scans within any compressed files that it finds in the IFS
- Decompresses and scans files compressed in packages such as PKZip, .lha, and .arj files
- Detects and cleans macro and script viruses
- Detects and cleans encrypted and polymorphic viruses
- Detects and cleans new viruses in executable files and Microsoft OLE compound documents
- Detects and removes Trojan horses, worms, and many other types of malicious components
Upgradeable Based upon McAfee Anti-Virus Technology
Of course, new viruses are constantly appearing and spreading across the Internet on an almost daily basis, and Bytware estimates that there are over 60,000 viral contaminants moving about in the wild. So one of the key elements that StandGuard Anti-Virus or any other potential iSeries anti-virus software must provides is a means of upgrading the suite with new anti-virus technology as new virus threats occur.
Here, Bytware's partnership with Network Associates gives it a clear edge over other competitive products that may appear in the future and raises the bar for any vendor that chooses to enter into this market niche.
By leveraging the McAfee Security technology, Bytware has engineered its product to complement the McAfee Security solution to work across the entire IT infrastructure. As new viruses are discovered, this partnership will help Bytware deliver upgrades to its iSeries StandGuard Antivirus software faster. Customers will receive the latest anti-virus definition files directly from McAfee, providing an enterprise-level solution to virus alerts.
Combine that with Bytware's other substantial suites of iSeries security products, and IT can begin to feel comfortable about opening the IFS to much more use on the iSeries.
Built for iSeries Implementation
In addition to basic PC-like features, StandGuard Anti-Virus also delivers the following:
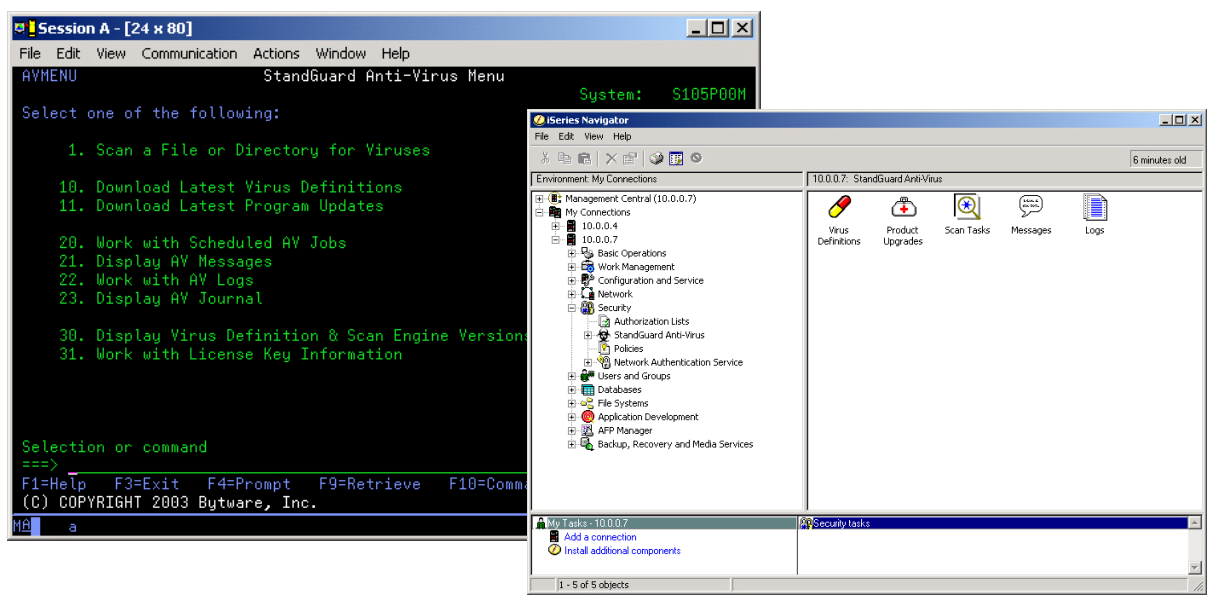
- Both green-screen and iSeries Navigator plug-ins to enable iSeries administration (see Figure 1)
- The ability to automatically download virus definitions files
- A feature to automatically download software updates and fixes to the iSeries
- A built-in scheduling feature for scanning and updating
- The ability to provide extensive logging of discovered viruses
- The ability to network the virus software across multiple iSeries servers
Figure 1: StandGuard Anti-Virus offers green-screen and iSeries Navigator interfaces.
Overcoming the Superman Syndrome
No doubt, there will be nay-sayers who continue to proclaim the invulnerability of the iSeries to virus attacks. "It's never happened before!" they'll proclaim. But like teenagers who believe they are supermen, the first real brush with a substantial virus infection will certainly make them blanch. And by then, it will be too late.
It's time for iSeries managers to overcome the myth of the iSeries Superman Syndrome, because IFS viruses can definitely be the Kryptonite that brings the network to its knees. Bytware's StandGuard Anti-Virus is an excellent new product choice to help maintain the iSeries' immunity while allowing iSeries administrators the opportunity to open the IFS to more functionality for the users.
For more information about computer virus vulnerability, visit the CERT Coordination Center.
For more information about StandGuard Anti-Virus and other StandGuard products, visit Bytware's StandGuard Anti-Virus Web site.
For more information about McAfee Antivirus, visit the Network Associates Web site.
Thomas M. Stockwell is Editor in Chief of MC Press, LP. He can be reached for comment at






















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online