Confused about the switch from Client Access network drives to AS/400 NetServer network file services? This easy-to-read article explains everything you need to know about setting up V4R4 AS/400 NetServer to provide AS/400 IFS file sharing for your Windows desktops, even if they are not running Client Access or Express client.
Editor’s Note: This article is written to the General Availability (GA) version of Express client that will be available in late May. As such, some of the features Bridget discusses here are not contained in the Express client beta, but they will be available in the final product.
Client Access Express for Windows (Express client), the newest member of the Client Access Family, relies on IBM AS/400 Support for Windows Network Neighborhood (AS/400 NetServer) for network file and print access. Unlike the Client Access for Windows 95/NT product, Express client uses AS/400 NetServer combined with the native file and print sharing capabilities found in the Windows operating system to provide these functions.
This article reveals how easy it is to use AS/400 NetServer to provide network file services to your Windows PCs. (For the network printing side of the equation, see “V4R4 AS/400 NetServer Bulks Up AS/400 Network Printing,” MC, February 1999.) I’ll explain what network file sharing is and discuss why IBM is moving from Client Access network drive support to AS/400 NetServer. I’ll also discuss how Express client’s AS/400 Operations Navigator has been changed to support this move and how Client Access for Windows 95/NT data conversion properties are migrated to AS/400 NetServer. The article also includes a review of some related V4R4 AS/400 NetServer features that may interest you.
What Is Network File Serving?
Network file serving allows you to access files in your AS/400 Integrated File System (AS/400 IFS) just as if they were located on your PC hard drive. For example, you can access and manipulate Lotus WordPro or Microsoft Word documents residing in the AS/400 IFS from your Windows PC. The Lotus WordPro application can also exist in an AS/400 IFS directory and be executed from your Windows PC. After it is mapped to a network drive, an AS/400 IFS directory looks just like another local drive on your Windows PC.
AS/400 NetServer is an AS/400 server that provides network drive support to Windows client PCs. AS/400 NetServer is an additional server that coexists with the Client Access/400 server, but because it is a separate AS/400 server, you are not required to install any member of the Client Access family on your Windows desktop PC to take advantage of file sharing through AS/400 NetServer. Express client and any other PC application can access network drives through AS/400 NetServer and the file sharing capability found in Windows 9x and Windows NT 4.0.
AS/400 NetServer and Express client are both supported in OS/400 V4R2 and above. Like AS/400 NetServer, Express client is available only on a TCP/IP network, so make sure your AS/400 and your client PCs have TCP/IP configured. On your Windows desktops, you need to install and configure the Client for Microsoft Networks network component included with Windows 95/98/NT, which provides the PC’s native file sharing capability. For more information on configuring your AS/400 and client PCs for AS/400 NetServer, see the AS/400 NetServer Web site at www.as400.ibm.com/netserver and the sidebar “Setting Up AS/400 NetServer in 1,000 Words or Less” in the article “V4R4 AS/400 NetServer Bulks Up AS/400 Network Printing,” MC, February 1999.
Why Use NetServer?
With AS/400 NetServer, you no longer need to install additional software on your Windows PC to access the AS/400 IFS, so your client PCs have a smaller desktop footprint. AS/400 NetServer provides file serving access to AS/400 IFS directories by using the industry-standard Server Message Block (SMB) protocol. Through AS/400 NetServer, Express client computers can rely on SMB to provide file serving while continuing to support the richer functions of the Client Access family of clients.
In addition to reducing the memory requirements for PC hard drives, Express client no longer requires background file service tasks for AS/400 IFS drive mapping. The background tasks that Client Access for Windows 95/NT needs for drive mapping are eliminated because the PC now relies on SMB and AS/400 NetServer for file services. More client PC memory is available, and the PC’s processor usage is lower because Express client does not use the Client Access file service tasks.
Client Access for Windows 95/NT exposes the entire AS/400 IFS from the Root (/) file system, meaning a user can access any AS/400 IFS directory that is present on the AS/400, even QSYS.LIB. When using AS/400 NetServer, you must configure an AS/400 NetServer file share for each file system and directory you want to share with the network. Only the /QCA400 directory containing the Client Access install images is shared, by default, with the network. An access mode (read-only or read-write) for each AS/400 NetServer file share provides yet another layer of security in addition to the AS/400 IFS permissions already in place for the directory. AS/400 NetServer offers more protection for the AS/400 IFS than Client Access for Windows 95/NT.
AS/400 NetServer also provides guest user support for Windows users who want to take advantage of the AS/400’s file and print services but do not have a matching user profile. This reduces your administrative work because you need to enable and configure only one user profile (with a password, of course) to give any network user immediate access to AS/400 file and print resources.
Express Client Operations Navigator and AS/400 NetServer
With the AS/400 Operations Navigator that comes with Express client, the File Systems folder still allows you to manage file systems and directories with ease. However, you now see two new icons under File Systems in Operations Navigator: Integrated File System and File Shares. If you work under the Integrated File System icon, you use Client Access System Program Interfaces (SPIs) to access the AS/400 IFS directories. If you work under the File Shares icon, you use the combined efforts of the PC’s native file sharing capability and AS/400 NetServer to access those same directories. Here’s how they both work.
The Integrated File System Icon
All IFS file systems and their corresponding folders are listed under the Integrated File System icon. If a file system or folder in a file system is currently shared with the network, Operations Navigator shows the file system or folder being held by a hand, as illustrated in Figure 1. If you right-click on a file system icon or folder icon under Integrated File System and then select Sharing and New Share from the pop-up menu, you can create a new file share for that file system or folder. If you right-click on an icon held by a hand, you can either add a new share for that directory or work with the currently configured AS/400 NetServer file shares for that directory.
If you right-click on an actual file in a folder under Integrated File System, Operations Navigator no longer presents you with the Open option. With V4R4, you must open files by using the PC’s native file sharing capability and AS/400 NetServer. With Express client Operations Navigator, an Edit option is available for file types that are registered with Windows Notepad. This editor uses Client Access SPIs to open the file for editing.
It is now possible to create, rename, and delete AS/400 IFS directories with Express client Operations Navigator. To create a subdirectory under an AS/400 IFS directory, right-click on a folder icon and select New Folder. You can rename or delete a directory by right-clicking on a folder icon and selecting the appropriate action.
Cut, copy, and paste options are available when you right-click on the file system or the folder icon. Drag and drop is also available from within the AS/400 IFS folder. These capabilities are also executed through Client Access SPIs.
If Secure Sockets Layer (SSL) is enabled for your AS/400 system in Operations Navigator, you will see a padlock on the AS/400 system icon itself and a padlock/regular lock combination icon in the lower-left corner of the Operations Navigator windows. All functions that do not support SSL are disabled in Operations Navigator when SSL is enabled. Neither the PC’s native file sharing capability nor AS/400 NetServer supports SSL, so the File Shares icon is disabled in Operations Navigator if SSL is enabled for your AS/400 system. However, both of these functions still remain available through your regular desktop environment outside of Operations Navigator.
Note: While AS/400 NetServer and the PC’s native file sharing capability do not support the SSL, the Client Access SPIs do support SSL. Because Client Access SPIs are available only in the Operations Navigator File Systems-Integrated File System path, you need to use those functions in Operations Navigator when SSL is activated to copy files to, or move files from, your Windows PC desktop.
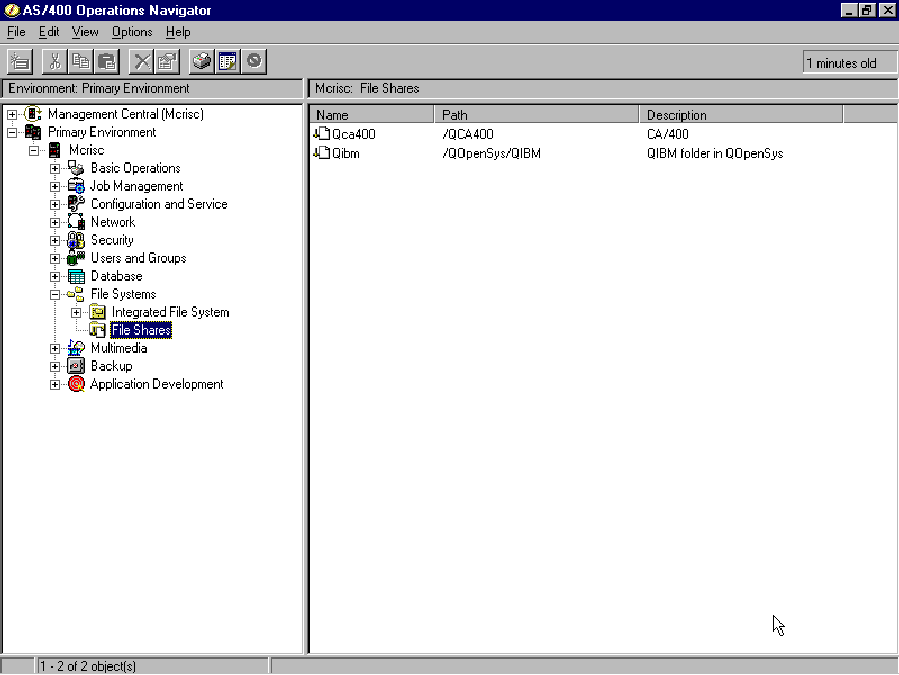
File Shares Icon
The File Shares icon under File Systems (shown in Figure 2) is a new feature that is specific to the PC’s native file sharing capability and AS/400 NetServer. When you click on the File Shares icon, you obtain a list of currently configured AS/400 NetServer file shares. Right-clicking on the File Shares icon and selecting Open AS/400 NetServer brings up AS/400 NetServer with its sessions and shared objects in a separate window.
If you right-click on an individual Shared Object icon under File Shares and then select Open, the Windows Explorer application executes, using the Universal Naming Convention (UNC) name associated with the file share as input. Windows Explorer presents a window containing just the contents of the AS/400 IFS directory for which the
share is configured. If you right-click on an individual Shared Object icon under File Shares and select Explore, the Windows Explorer application again executes, but this time it explores the entire Network Neighborhood until the AS/400 NetServer and share name are found. The contents of the AS/400 IFS directory are displayed in the right-hand pane of the Windows Explorer window.
You can map a network drive on your Windows PC by right-clicking on an individual Shared Object icon under File Shares and selecting the Map Network Drive option. When presented with the Map Network Drive dialog, enter the name of the local drive letter to which you want to map the network drive and press the Enter key.
Finally, you can access the AS/400 NetServer File Share Properties dialog by right- clicking on an individual Shared Object icon under File Shares and selecting Properties. Use this dialog to make any changes to your File Share.
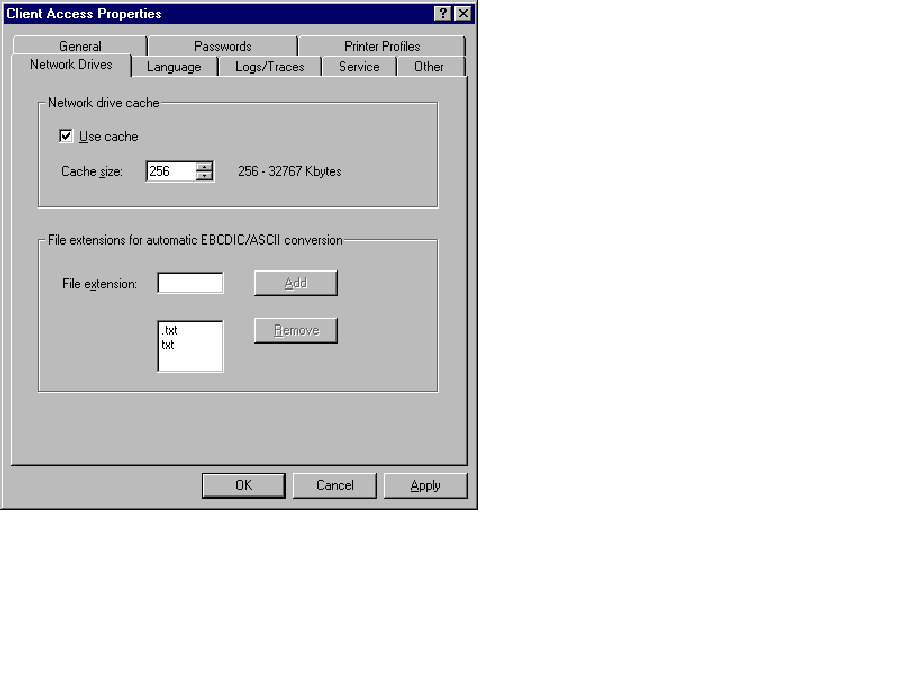
Migration of Text Conversion
Because the Express client no longer provides network drive services, your Client Access Properties dialog no longer has a Network Drives tab. With previous clients, you could configure EBCDIC/ASCII conversion once for all AS/400 systems, but now you enter this information when configuring an AS/400 NetServer file share or when configuring the Integrated File System Properties for an AS/400 system. The following shows examples of how the EBCDIC/ASCII conversion properties are migrated from Client Access for Windows 95/NT (the Windows 95/NT client) to Express client Operations Navigator.
When you use the V3R2M0 (or prior) Windows 95/NT client, you click on the Network tab on the Client Access Properties dialog (found when you double-click on the Client Access icon in your Windows Control Panel) to reach the dialog shown in Figure 3. This dialog controls how EBCDIC/ASCII conversions are accomplished for all AS/400 systems to which you are connected.
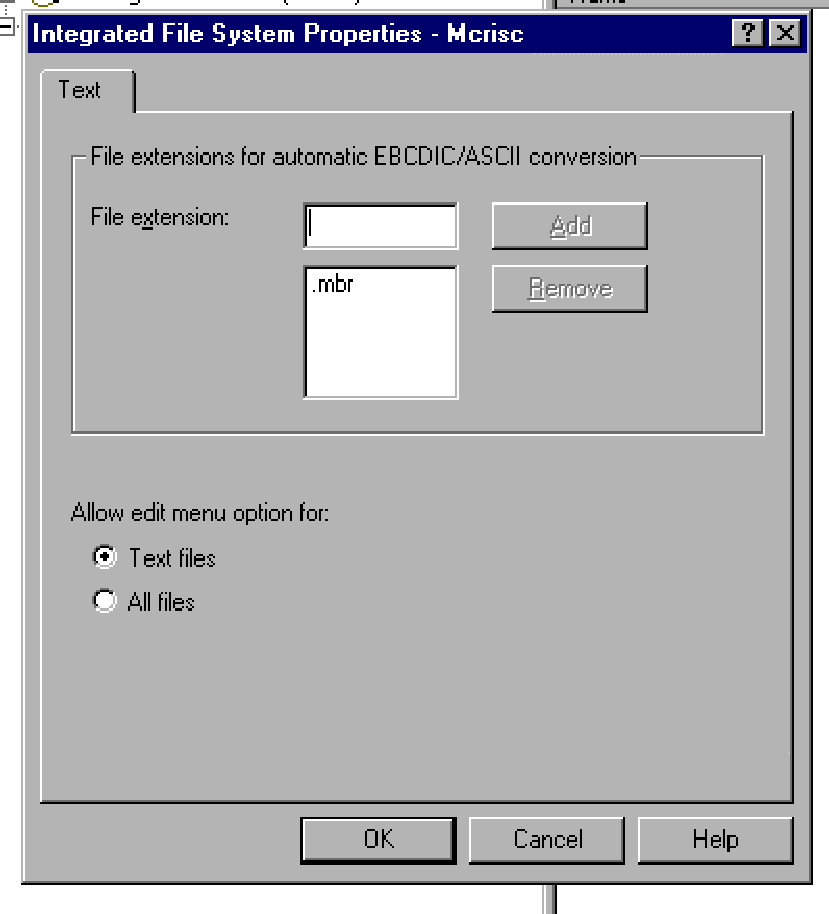
Integrated File System Text Conversion
By using Operations Navigator in Express client, the AS/400 administrator can find the Integrated File System icon under File Systems. Right-click on the Integrated File System icon and select Properties to access the Integrated File System Properties dialog (see Figure 4).
The file extensions for automatic EBCDIC/ASCII conversion previously specified on the Network Drive tab of the Client Access Properties dialog, shown in Figure 3, are now specified under the Text Conversion tab on the Integrated File System Properties dialog (see Figure 4). Although the location of this configuration has changed, Client Access still provides this support, which operates in the same way with two exceptions. First, you can now configure this support for each AS/400 system, where previously you could configure it only one time for all AS/400 systems.
Second, this system-wide EBCDIC/ASCII support applies only to operations performed from the File System-Integrated File System part of Express client Operations Navigator. These operations include, but are not limited to, copy and paste and drag and drop operations within Express client Operations Navigator for OS/400 V4R2 and above. When using these operations with Operations Navigator, files with the specified extensions are automatically converted between
EBCDIC and ASCII, the same as they are in Client Access for Windows 95/NT. However, this system-wide setting does not apply to files accessed through a network drive, because that function has now migrated to AS/400 NetServer. Network drive EBCDIC/ASCII file conversion is now specified at the AS/400 NetServer file share level, which means that each individual file share must be configured for automatic ASCII/EBCDIC conversion if it is needed. I will cover this feature next.
Individual File Shares Text Conversion
Using Operations Navigator in Express client, right-click on the File Shares icon under File Systems and then select Open AS/400 NetServer. On the AS/400 NetServer
screen, double-click on the Shared Objects icon. The AS/400 NetServer File Share Properties dialog can be accessed by right-clicking a file Shared Object icon and then selecting Properties from the context menu. From the AS/400 NetServer File Share Properties dialog, select the Text Conversion tab to reach the dialog shown in Figure 5. If you are using the Express client to access V4R2 or V4R3 AS/400 NetServer, you are not presented with the Text Conversion tab. Text conversion using AS/400 NetServer file shares is available only with V4R4 and later OS/400. You need *IOSYSCFG special authority to add or change the AS/400 NetServer file share configuration. In V4R4 of OS/400, AS/400 NetServer also allows the owner of an AS/400 IFS directory (including file systems) to add, change, or remove AS/400 NetServer file share configurations without *IOSYSCFG special authority. A change to a file share takes effect immediately.
The file extensions for automatic EBCDIC/ASCII conversion previously specified on the Network Drive tab of the Client Access Properties dialog (Figure 3) are specified on the Text Conversion tab of the AS/400 NetServer File Share Properties dialog (Figure 5). In V4R4 of OS/400, AS/400 NetServer does text conversion on the fly when reading or writing files to the AS/400 IFS if the Allow file text conversion check box is selected. The contents of only those files with the configured extensions are converted. The code page configured for the AS/400 NetServer file share is the code page used for the text conversion. AS/400 NetServer performs text conversion by using this code page and the current code page of the AS/400 file.
Possible Conversion File Extension Values
Here are some possible file extension values that you can enter for EBCDIC/ASCII file conversions:
• ‘*’—AS/400 NetServer converts all files.
• ‘.’—AS/400 NetServer converts all files without extensions.
• ‘TXT’—AS/400 NetServer converts all files ending in .TXT (e.g., a.TXT,
.TXT, a.b.c.TXT). Any values with more than one leading period (..TXT, ...TXT) have no effect on AS/400 NetServer. No conversion is done.
• ‘T*T’—AS/400 NetServer converts all files ending with an extension that substitutes any number of characters for the * wildcard (e.g., a.T123T, b.TXT).
• ‘T?T’—AS/400 NetServer converts all files ending with an extension that substitutes any one character for the ? wildcard (e.g., a.T1T, b.TXT).
Note: The text conversion support is migrated from Client Access for Windows 95/NT to AS/400 NetServer file shares on V4R4 of OS/400. If you use Express client to access AS/400 NetServer file shares on an AS/400 running V4R2 or V4R3, you will not be able to configure AS/400 NetServer file shares for text conversion. Text conversion using AS/400 NetServer file shares is available only with V4R4 and later OS/400.
Related AS/400 NetServer Enhancements
In V4R4 of OS/400, AS/400 NetServer supports the NT dialect of the SMB protocol. This means things like share names and path names are passed in UNICODE between the client PC and AS/400 NetServer. The user notices this support in that the code page configured on the AS/400 NetServer General Next Start dialog is not referenced when AS/400 NetServer is serving Windows 95/98/NT PC clients. This means that AS/400 NetServer is no longer limited to one code page, configured for AS/400 NetServer properties to service all clients in the network. German, French, and English clients can now seamlessly coexist without relying on this configuration value.
Using Operations Navigator in Express client, the AS/400 administrator can find the AS/400 NetServer icon by following the Network-Servers-TCP/IP-AS/400 NetServer path. Right-click on the AS/400 NetServer icon, select Properties, select the General tab, and then press the Next Start button. Any changes you make to the AS/400 NetServer do not take effect until the AS/400 NetServer server is stopped and restarted.
An additional Operations Navigator file-related enhancement involves using Express client to configure AS/400 IFS directory permissions for the path referenced by an
AS/400 NetServer file share. Using Operations Navigator, right-click on the File Shares icon under File Systems and select Open AS/400 NetServer. By right-clicking on a file Shared Object icon and then selecting Permissions, you can now configure directory permissions (authorities) for the AS/400 IFS directory that is configured for that file share.
File Serving Has More Options Although Express client frees up resources on the Windows desktop PC, AS/400 NetServer allows you to still enjoy the same level of support found in Client Access for Windows 95/NT. Relying on AS/400 NetServer to handle Express client’s file serving needs gives you more industry-standard network drive capabilities and shrinks the client’s desktop footprint. After you have added an AS/400 NetServer file share, mapping network drives from your Windows PC is easy and you can begin using the powerful new connectivity features that AS/400 NetServer provides.
Related Reading
IBM’s AS/400 NetServer Web site: www.as400.ibm.com/netserver “Setting Up AS/400 NetServer in 1,000 Words or Less,” MC, February 1999 “V4R4 AS/400 NetServer Bulks Up AS/400 Network Printing,” MC, February
References
Client Access Express for Windows: Setup Manual (SC41-5507) “Client Access without Client Access,” Client Access/400 Expert, July/August IBM’s Client Access Web site: www.as400.ibm.com/clientaccess “Transform Your AS/400 into a Network Print Server with AS/400 NetServer,” AS/400 Network Expert, January/February 1999
1999
1998
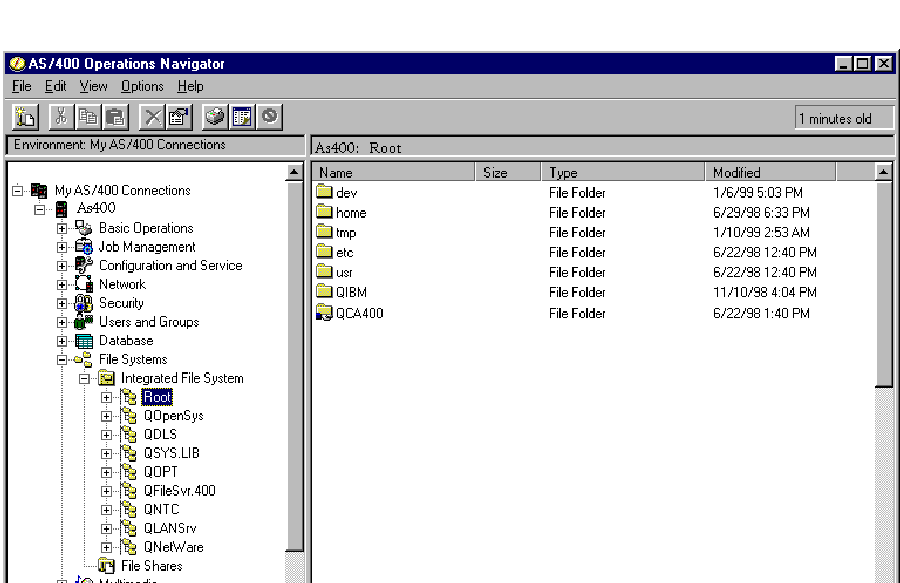 |
Figure 1: You can view which AS/400 IFS directories are shared with the network from the File System-Integrated File System path in the Express client AS/400 Operations Navigator.
Figure 2: The File Shares icon is a new feature that is specific to the PC’s native file sharing capability and AS/400 NetServer.
 |
 |
 |
 |




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online