Fill the gap between modules and ILE programs for a full panorama of your ILE application.
Part I and Part II of this series have shown how some system commands can be used to dissect in depth one application, without the source code. But these analyses suffer from a lack of information for ILE programs—namely, the link between the program and embedded modules.
Indeed, for OPM programs, the command DSPOBJD provides a direct link between the program and source code. This is possible because the compiler goes directly from the source code to the program without going through an object module. Conversely, for ILE programs, DSPOBJD does not give such information. It cannot: ILE programs can be composed of several modules.
Although each module knows the name of its source code (and DSPOBJD knows how to find that), the link between a program and the list of modules is inaccessible: the command DSPPGM does not offer OUTPUT(*FILE).
This third article shows first the command RTVPGM, based on the six APIs shown below. This command and these APIs provide an OUTPUT(*FILE) equivalent to the output screens of DSPMOD, DSPPGM, and DSPSRVPGM. These OUTFILE outputs are a one-to-one relationship for most of the formats of these APIs.
- Retrieve Module Information (QBNRMODI) API
- Retrieve Program Information (QCLRPGMI) API
- Retrieve Service Program Information (QBNRSPGM) API
- List Module Information (QBNLMODI) API
- List ILE Program Information (QBNLPGMI) API
- List Service Program Information (QBNLSPGM) API
This article then shows the scripts used to extract information from these files.
The command RTVPGM explores objects of type * MODULE, * PGM, and * SRVPGM. It produces 16 files:
Three describe the basic information modules, programs, and service programs:
- MODI0100—Basic module information
- PGMI0100—Basic program information
- SPGI0100—Basic service program information
Five to describe the attachment of modules:
- MODL0100—Module export (*EXPORT) information
- MODL0200—Module import (*IMPORT) information
- MODL0300—Module procedures (*PROCLIST) information
- MODL0400—Referenced system objects (*REFSYSOBJ) information
- MODL0500—Module copyright (*COPYRIGHT) information
Five describe programs and service programs' attachments:
- PGML0100—ILE program module (*MODULE) information
- PGML0200—ILE service program (*SRVPGM) information
- PGML0300—Data items exported to the activation group (*ACTGRPEXP)
- PGML0400—Data item imports resolved by weak exports that were exported to the activation group (*ACTGRPIMP)
- PGML0500—ILE program copyright (*COPYRIGHT) information
Three describe specific service programs' attachments:
- SPGL0600—Procedure export information
- SPGL0700—Data export information
- SPGL0800—Signature information
Figures 1 through 3 show the three screens of the RTVPGM command.
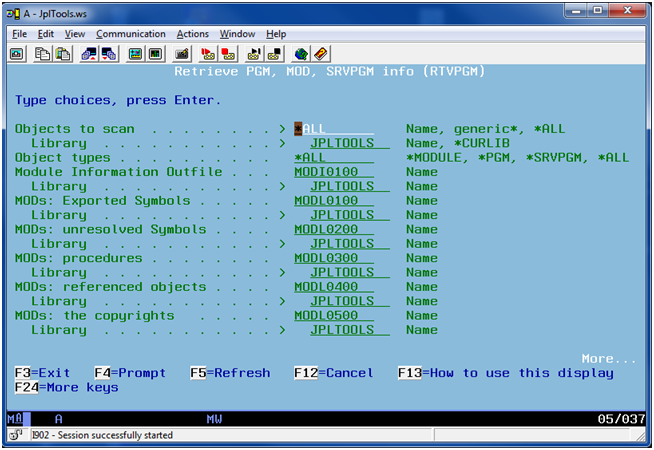
Figure 1: In RTVPGM page 1, choose the objects to analyze and the names for module information files.
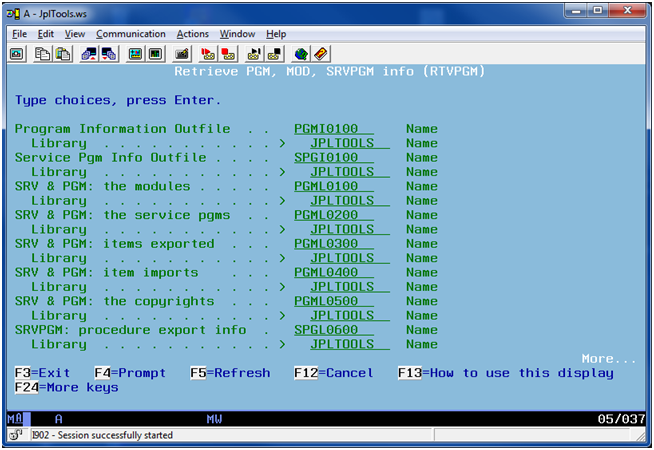
Figure 2: In RTVPGM page 2, choose the name for the program information files.
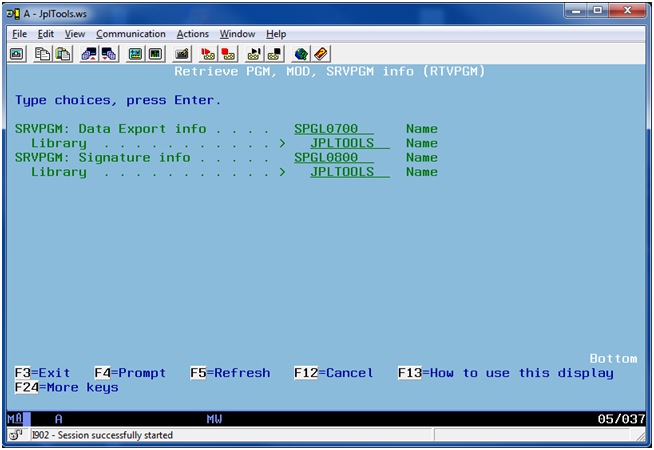
Figure 3: In RTVPGM page 3, choose the name for the service program information files.
These files by themselves are very interesting cross-references. For example, when a program crashes because of a service program (yes, it happens, especially in development), we can easily find out which procedure sent the error message (it's in F9 of the message), but how do we determine the name of the module that hosts this procedure? Is it the only one? MODL0300 provides the answer.
But back to the goal of this article: analyzing the structure of an ILE application. The difference is that here, with an ILE application, we must include the fact that a program consists of one or more modules and these modules have source code.
First, you will find below rewritten SQL to match some SQL from the previous article. I've done this because the previous SQL was prepared for a program, where source code name and module name are the same.
For an ILE program, there is no method to determine the list of modules within a program because DSPPGM does not have an OUTPUT(*OUTFILE). The modified SQL uses the OUTFILEs generated by RTVPGM to determine the list of the modules of any ILE program, irrespective of the number of modules. Depending on whether or not the *MODULE objects are available, we use either file MODI0100 or PGML0100. Finally, you will find SQL that gets the two or three pieces of information that were missing
Modules by Type and Year
This statistic concerns the counting of objects by type and year of source update:
*MODULE:
with stat as ( SELECT MODULE_ATTR "Attribute"
,trim(char(substr(source_date,1 ,1) + 19) ) concat substr(
SOURCE_DATE,2,2) "Year" FROM jpltools.modi0100 ) select "Year"
,"Attribute" , count(*) Number from stat group by "Attribute",
"Year" order by "Year", "Attribute"
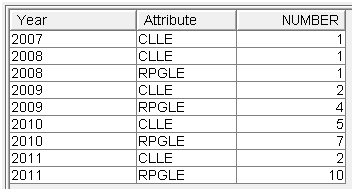
Figure 4: These are the modules by type and year.
Note: No OPM program here; OPM does not produce *MODULE.
*PGM & *SRVPGM:
with stat as ( SELECT MODULE_ATTR "Attribute"
,trim(char(substr(source_date,1 ,1) + 19) ) concat substr(
SOURCE_DATE,2,2) "Year" FROM jpltools.pgml0100 ) select "Year"
,"Attribute" , count(*) Number from stat group by "Attribute",
"Year" order by "Year", "Attribute"
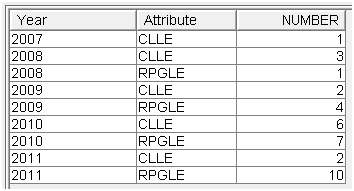
Figure 5: These are the modules by type and year from programs.
Note: No OPM here; that's discarded by RTVPGM.
Results are slightly different. These are some reasons:
1. Some programs need to be recompiled to include updated modules.
2. Some modules are not referenced.
3. Some modules are not available.
Source by Library
*MODULE:
SELECT count(*), SOURCE_LIB FROM jpltools.modi0100 GROUP BY SOURCE_LIB
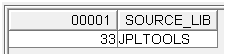
Figure 6: These are the sources by library from modules.
*PGM & *SRVPGM:
SELECT count(*), SOURCE_LIB FROM jpltools.pgml0100 GROUP BY SOURCE_LIB
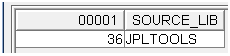
Figure 7: These are the sources by library from programs.
Sources by File
*MODULE:
SELECT count(*), SOURCE_NAME FROM jpltools.modi0100 GROUP BY SOURCE_NAME
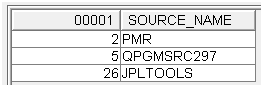
Figure 8: These are the sources by file from modules.
*PGM & *SRVPGM:
SELECT count(*), SOURCE_NAME FROM jpltools.pgml0100 GROUP BY SOURCE_NAME
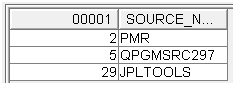
Figure 9: These are the sources by file from programs.
Objects by Version
*MODULE:
SELECT count(*), RELEASE_MODULE_CREATED_FOR FROM jpltools.modi0100 GROUP BY RELEASE_MODULE_CREATED_FOR
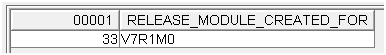
Figure 10: These are the objects by version from modules.
*PGM & *SRVPGM:
SELECT count(*), RELEASE_FOR FROM jpltools.pgml0100 GROUP BY RELEASE_FOR
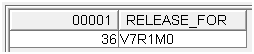
Figure 11: These are the objects by version from programs.
Objects by Owner
*MODULE:
SELECT count(*), MODULE_OWNER FROM jpltools.modi0100 GROUP BY MODULE_OWNER
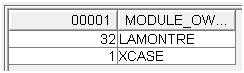
Figure 12: These are the objects by owner from modules.
*PGM:
SELECT count(*), PROGRAM_OWNER FROM jpltools.pgmi0100 GROUP BY PROGRAM_OWNER
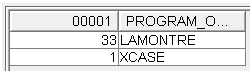
Figure 13: These are the objects by owner from programs.
*SRVPGM:
SELECT count(*), OWNER FROM jpltools.spgi0100 GROUP BY OWNER
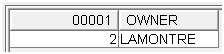
Figure 14: These are the objects by owner from service programs.
Check the Date of the Source Code
Reminder: MODI0100 or PGML0100 give us the exact date of the source code when compiling the module. DSPFD MBRLIST gives us the exact date of last modification of the source code.
Step one: Simplify the reading of DSPFD-MBRLIST (remember, the code is the same as in the previous article).
For the modification date of the source code:
SELECT MLNAME, case when MLCHGc = '' then ' ' else trim(char(
MLCHGC+ 19)) concat MLCHGD concat MLCHGt end Upddate,MLMTXT FROM
jpltools.mbrlist WHERE MLCHGc <> ''
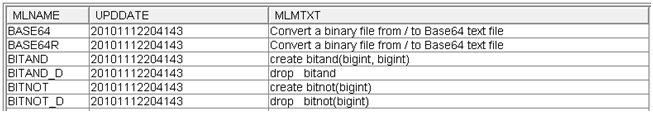
Figure 15: Simplify reading DSPFD-MBRLIST.
Step two: Simplify the reading of MODI0100.
For the compilation date of the source code:
SELECT src, srcmbr , case when srcdate = '' then ' ' else
trim(char(substr(srcdate,1 ,1) + 19) ) concat substr( srcdate,2)
end cpldate , modattr FROM jpltools.modi0100
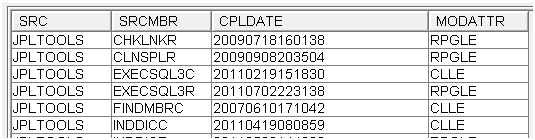
Figure 16: Simplify the reading of MODI0100.
The join of the two previous results (with SQL CTE - Common Table Expression) gives the list of modules without source:
with obj as (
SELECT src, srcmbr , case when srcdate = '' then ' ' else
trim(char(substr(srcdate,1 ,1) + 19) ) concat substr( srcdate,2)
end cpldate , modattr FROM jpltools.modi0100
) , src as (
SELECT MLNAME, case when MLCHGc = '' then ' ' else trim(char(
MLCHGC+ 19)) concat MLCHGD concat MLCHGt end Upddate,MLMTXT FROM
jpltools.mbrlist WHERE MLCHGc <> ''
) select src , srcmbr , cpldate, modattr from obj exception
join src on srcmbr = mlname
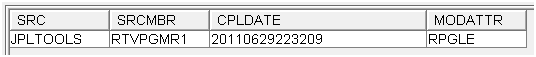
Figure 17: These are the modules without source.
Find the list of sources that do not build a program directly—for example, code description of a service program or code of an SQL procedure or uncompiled code (i.e., copied code):
with obj as (
SELECT srcfile, srcmbr , case when srcdate = '' then ' ' else
trim(char(substr(srcdate,1 ,1) + 19) ) concat substr( srcdate,2)
end cpldate , modattr FROM jpltools.pgml0100
) , src as (
SELECT MLNAME, case when MLCHGc = '' then ' ' else trim(char(
MLCHGC+ 19)) concat MLCHGD concat MLCHGt end Upddate,MLMTXT FROM
jpltools.mbrlist WHERE MLCHGc <> ''
) select src.* from src src exception join obj on srcmbr = mlname
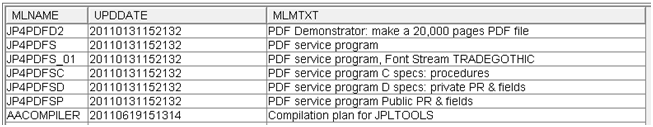
Figure 18: These are the sources without objects:
Get the list of sources modified but not recompiled:
with obj as (
SELECT src, srcmbr , case when srcdate = '' then ' ' else
trim(char(substr(srcdate,1 ,1) + 19) ) concat substr( srcdate,2)
end cpldate , modattr , text FROM jpltools.modi0100
)
, src as (
SELECT MLNAME, case when MLCHGc = '' then ' ' else trim(char(
MLCHGC+ 19)) concat MLCHGD concat MLCHGt end Upddate,MLMTXT FROM
jpltools.mbrlist WHERE MLCHGc <> ''
) select src "Object", srcmbr "Src Mbr",
cpldate concat case when upddate = cpldate then '' else ' was
updated ' concat upddate end "Compiled_date"
, case when mlmtxt = text then ' ' concat text else '>> '
concat text concat ' changed to ' concat mlmtxt end "Text"
from obj join src on srcmbr = mlname and (cpldate <> upddate
or text <> mlmtxt)
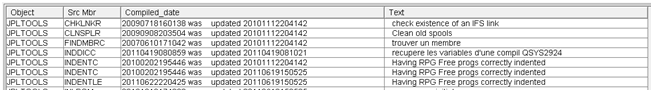
Figure 19: These sources were modified but not recompiled.
I changed my machine; we see the traces dated 2010-11-12-20:41:42.
Program Cross-References
These are based on DSPPGMREF output; that is to say on objects themselves, not on the source. Therefore, there is nothing to add to DSPPGMREF from the 16 files of RTVPGM. These analyses, exposed in the second article, are already accurate. They are not replicated here.
ILE Cross-References
ILE Cross-references are focused on module, procedure, program, and service program information received from RTVPGM outfiles. Their goal is to complete the data got from DSPPGMREF. Here, you will find a starter: the two SQLs needed to get the missing information quoted in previous articles:
Program by Activation Group:
select activation_group_attribute, count(*) count from jpltools.pgmi0100 group by activation_group_attribute
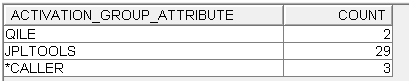
Figure 20: Get information about programs by activation group.
Monitor the Rights Acquisition:
select USER_profile_option, use_adopted_authority, count(*) count from jpltools.pgmi0100 group by USER_profile_option, use_adopted_authority
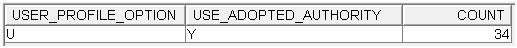
Figure 21: Monitor rights acquisition.
None of the programs in this application uses the owner authority. I don't need to further analyze which program runs under owner profile authority and check whether this is compliant with my policy rules. But if you need that information, you may want to quickly run an analysis:
SELECT program_name, program_library_name, program_owner FROM
jpltools.pgmi0100 WHERE USER_profile_option <>'U'
I'll stop here; there is so much information in these files! Depending on your own interests, you can now easily understand how your software is built. Now, it's up to you.





















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online