Binding language is not difficult, but it is multi-faceted. That is, binding directories did only one thing, but binding language provides a number of capabilities that will affect how you do service programs.
Editor's Note: This article is excerpted from chapter 20 of 21st Century RPG: /Free, ILE, and MVC, by David Shirey.
Please see the previous article here: Binding Directories.
Ready?
What Is Binding Language?
We will start with a simple question: what is binding language?
Actually, it is not a language at all but rather a pretty limited set of statements that help the service programs function.
These statements are not runnable from the command line but must be placed in a source member, preferably in QSRVSRC (you may have to create that). This source member will then be picked up and compiled as part of the CRTSRVPGM.
The member name you must use is the name of the service program.
The reason you might as well use QSRVSRC as your source file is that this is the default name used in the RTVBNDSRC command, which we will talk about in a few minutes. It is probably also the default value in the CRTSRVPGM command, but I don’t remember offhand.
The source type that should be assigned to this member is BND.
I want to be sure to mention that binding language is not necessary to creating and using service programs. On the other hand, we shall see when we talk about signatures that using it does make things easier, so you might want to partake.
What Is EXPORT?
Before we go on, let’s say something about the word EXPORT that is used on the beginning P-spec of a sub-procedure in a service program.
EXPORT basically relates to the ability to use (call) a sub-procedure from a program outside of the service program it is in. I know that sounds kind of weird, but the way service programs have been implemented by IBM it is not a given that you can use a sub-procedure outside of the service program it is in. That is, it’s not a given that you can call a sub-procedure in a service program from another program outside of that service program.
That is, when you put a sub-procedure into a service program you can, by default, call (use) that sub-procedure only in that service program. Do you see what I am saying there? Cause I would probably miss it. I am saying that when I put a sub-procedure in a service program and don’t do anything else, I can only call that sub-procedure from other sub-procedures in that specific service program. I can’t call it from an external point.
Why would you want to do that (only call it from within the service program it is in)? Maybe it accesses data from one or more files that is then used in a second sub-procedure in the service program to determine if the customer should be allowed to order. Or maybe it is something that you don’t want other programs to be able to kick off, for security reasons. How do I know why you might do this?
What is important is that unless you put the EXPORT keyword on the beginning P- spec of a given sub-procedure, you can only use that sub-procedure in the service program it belongs to. You will remember in chapter 10 we did in fact use that keyword and so were able to call that sub-procedure externally.
I just didn’t want you to be confused because we will use the word EXPORT a lot in this chapter and the next.
And remember, EXPORT does not go on the PR or PI D-spec. It goes only on the beginning P-spec.
The Binding Language Commands
OK, now let’s look at how you would set up the source file that contains binding language statements. We don’t know if or why we would use it yet, but let’s start with the simple task of building it.
Every binding language source file will have three different types of commands in it. All three must be present for the whole thing to work.
STRPGMEXP—starting the program export list
EXPORT—the name of the module you want to export
ENDPGMEXP—ending the program export list
STRPGMEXP—Start Program Export
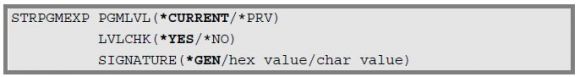
This is the first command in the binding language source member, and it kicks off the processing of the sub-procedures listed via the EXPORT command. Here is what it looks like, with the parameters associated with it.
The PGMLVL parm indicates whether the program level is to be the current list or a previous list.
A given binding language source member may contain more than one STRPGMEXP-ENDPGMEXP structure. There must be one, but only one, that uses the *CURRENT parm, and this indicates the most recent list of exportable sub-procedures. The others will be *PRV.
The idea behind a STRPGMEXP structure that uses *PRV was to allow you to hold on to old listings (old signatures) and have the calling program check not just against the current signature but old ones as well. Don’t worry now, this will make more sense in the next chapter.
For the moment, we will just use *CURRENT.
The LVLCHK parm indicates whether we will use the signature that is generated (however that might happen) to edit against the service program, similar to what we would do with a program level check and a file. You generally want this set to *YES, although we will discuss signatures more in the next chapter.
The SIGNATURE parm tells the system whether to generate a signature automatically or to use a hexadecimal or character value that is supplied with the command. Again, more on this in the next chapter. What is important now is to remember that you can modify what type of signature you use here in the binding language.
EXPORT—Export
This is not the EXPORT keyword on the beginning P-spec of a sub-procedure. But it does relate to exporting. This command defines the sub-procedure name that is to be exported from this particular service program.
EXPORT SYMBOL(sub-procedure-name)
Only one sub-procedure name can be specified on each EXPORT command. Thus you may have a bunch of them in your binding source member if the service program has a large number of sub-procedures.
You can either enclose the above procedure name in quotes or not. If you do not, it will automatically be converted to upper case. If you do use quotes, then it will keep whatever mixed-case syntax that you specify. Since this name must match the name of the procedure in the service program (including case), it is not a good idea to be casual about this. For RPG you would probably not want to bother with quotes, just in case you end up mixing cases when you type in the name.
When creating your EXPORT statements, you can’t just throw them in there willy-nilly. They must be in the order of the sub-procedures in the service program they apply to. Failure to do this could result in your calling the wrong sub-procedure.
ENDPGMEXP—End Program Export
This ends the list of procedures to be exported from a service program and is the last statement in the binding language source member.
There are no parms for this command.
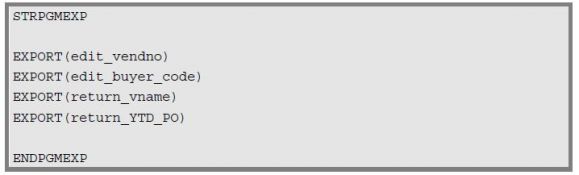
A typical example of a binding language source member would be:
Don’t forget that you could, if you want, have several of these structures. One of them must have the PGMLVL parm set to *CURRENT (which is the default), and the others must be set to *PRV. As we will see when we talk about signatures, we do not have to use *PRV structures. They are optional, and you may decide you want no part of that freakiness.
Plus, each service program that you create (type SRVPGM) should have a corresponding binding language source file (type BND). That is, if you use binding language. Remember, it’s not mandatory.
RTVBNDSRC Command
Before we move on, we should take a quick look at this command.
So far, we have sort of been thinking that we would create the binding language source file (that is, the stuff above) by manually keying in the data, and there is nothing wrong with that.
If you want something a little more automatic, however, you can use the RTVBNDSRC command to create the binding language source for a given module or service program.
The command creates a member in the QSRVSRC file for the particular service program you run the command over. At first glance, you might think that this command should allow you to span several service programs, but that is not the way that binding language works. Each binding language list relates to just one service program.
The command can be run for either add or replace mode, so it can be used to create as well as update the member on an ongoing basis. If you did run it in an update mode, please remember that you would still have to recompile the service program to take your source changes and roll them into the object.
Triggering Binding Language Use
So far we have talked about what binding language is and what it looks like but not how it gets turned on. After all, we didn’t use it in chapter 10, and so it’s not automatic.
The key is the EXPORT parm in the CRTSRVPGM command. It has two values.
*SRCFILE
This is the command default. In this case, the compile goes to look for a source file with a name equal to the service program name in the QSRVSRC source file. This is what kicks off using the binding language that you have put in that source file as what determines what sub-procedures are allowed to be exported. And, if it doesn’t find the properly named file, the compile will fail.
If you don’t use this parm, then even if you have a binding language source file set up, the CRTSRVPGM doesn’t use it.
*ALL
This option does not use the binding language source, even if it exists. Instead, the compile looks at the service program itself and makes a list of the sub-procedures from that source that have the EXPORT keyword on their beginning P-spec. And that is the whole point of this: to get a list of the sub-procedures that are in a service program. Otherwise, we might not bother. Might not— because binding language does other things as well.
























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online