A Web server is a set of programs that responds to requests coming from another program—a Web browser such as Netscape Navigator or Microsoft Internet Explorer. Having thrown its hat into the Web server ring, the AS/400 Web server development team has made steady strides in bringing the AS/400 into a respectable position. The AS/400’s Web server features include the following: an HTTP server that provides Web page content for Web browser users; a Workstation Gateway (WSG) server that delivers AS/400 5250 data stream content; and a server-side program execution gateway that calls a program on the server to interact with a Web browser user.
An HTTP server program transmits data representing an HTML document to a requesting host computer. The receiving computer reads the transmitted data into a Web browser. The Web browser is capable of interpreting the data into a display consisting of lines of text, artwork, sounds, and so on. For some applications, there must also be support for programs running on the server that collect data provided by the user (CGI programs, for example). As seen in Figure 1, the client/server structure upon which HTTP is built places part of the mechanism on the client and part on the server. The browser program resides on the client and acts as a general-purpose instruction interpreter. HTML data contains instructions that tell the client’s browser how to behave, plus textual and multimedia content.
The AS/400’s HTTP server support is capable of running more than one set of server programs at one time. Each set of the running programs is called an instance of the server. Normally, you want to run only a single default instance of the server. Each instance of the server must have its own port to use—no two TCP/IP server programs can use the same port at the same time. The well-known port for HTTP services is port 80, and this is where the Web browsers of the world send requests. Any other instance of the server has to use another port number, and, to avoid conflict with standard TCP/IP utilities, that port number should be above 1023. (Port numbers 1-1023 are reserved for common TCP/IP utilities such as FTP or Telnet.)
HTTP Server Configuration
An HTTP server, such as Apache for UNIX operating systems or the one that comes with OS/400, is a complex application capable of a variety of tasks. A server is designed to be
flexible in its operations, and the price of this flexibility is complexity in the program’s configuration.
HTTP Configuration Precedence
HTTP configuration information has five setting levels. Figure 2 shows the levels of configuration for HTTP and the associated methods—either a CL command or an HTTP administration form—you use to set values. As you might suspect, you can configure the AS/400’s HTTP server in two ways. Using Operations Navigator (OpsNav), however, is not one of them. You can perform most HTTP configuration tasks from an AS/400 5250 session by using CL commands such as Change HTTP Attributes (CHGHTTPA) and Work with HTTP Configuration (WRKHTTPCFG), which runs a special HTTP configuration editor in a green-screen session.
A more meaningful interface to the complex tasks attendant to HTTP configuration is available through a configuration utility made available by IBM.
The HTTP server Configuration and Administration utility groups related pieces of configuration details into a series of forms that makes the task easier. The IBM utility is a Java applet that runs on your Java-enabled Web browser. The applet is a program that interacts with the user to present and accept HTTP configuration information for the AS/400. As seen in Figure 3, the configuration applet has, on the left-side menu, a series of categories that are opened to allow access to the specifics. The specifics are presented in forms on the right-side panel.
The HTTP administration server groups configuration tasks into the following categories:
• Global server parameters apply to all instances of the HTTP server.
• Server instances create, delete, and manage server instance configurations.
• Configurations set details of server request processing.
• Internet users add, change, and remove Internet user entries. (An Internet user entry defines only an HTTP server user—not an AS/400 user as is defined with an AS/400 user profile.)
• Access control lists define access authority at the file level within a directory. A request for file access is evaluated by file name, request method, and user name.
Starting the HTTP Configuration Utility
The HTTP administration server runs over port 2001 and is not normally started automatically. You can start the HTTP configuration and administration server from a 5250 command line with CL command STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN) or with OpsNav. Allow the server time to start (you can check with WRKACTJOB for the status) and then access the utility from a PC Web browser.
To start the HTTP configuration applet (*IOSYSCFG system authority is required), start your Web browser. In the location/address box, specify the URL http://Your.AS400Host.AndDomain:2001/. If all is well, a welcome page will appear. Clicking on IBM HTTP Server for AS/400 starts the Configuration and Administration utility seen in Figure 3. (If you click on Related task information from this display, you bring up the IBM AS/400 Information Web page over the Internet at www.as400.ibm.com/anchor/MRI2924/anchhome.htm. This page gives you easy access to the HTTP server documentation as well as other related IBM manuals.)
HTTP Directive Statements
Traditionally, Web service functions take place under utilities (such as Apache) that run on a UNIX operating system. To make the AS/400 more appealing to the traditional UNIX market, the AS/400 Web server developers extended an effort to make its interface more UNIX-like. Configuring a server is done via special instruction statements called directives.
Directives to the AS/400 HTTP server program are plain-text statements that the system administrator maintains.
You can maintain multiple sets of directive statements, each corresponding to an instance of the HTTP server. Each set is stored in its own member. When shipped, the AS/400 is preconfigured with a default set of directives residing in the member named CONFIG. The directive statements contained in the CONFIG member are mostly comments as designated by the number sign (#). The comments provide information about directives and are worth reading.
With a rudimentary IBM-supplied editor (somewhat similar to SEU), you can also edit a set of directive statements from an AS/400 5250 session. You invoke the editor with the CL command WRKHTTPCFG. The default configuration member is brought up for editing with WRKHTTPCFG CFG(CONFIG).
You usually edit directive statements with the less direct but more meaningful access that the HTTP Configuration and Administration utility provides.
Directive statements are a capricious little language of their own, and only the statements required for minimal configuration will be presented here. (See the HTTP Server for AS/400 Webmaster’s Guide V4R4 for complete information.) However, it is important to understand that the interpretation of some directive statements is done in mutual exclusion. That is, when a directive statement within a group is found that matches given criteria in a top-down search, the rest of the statements in the group are ignored. HTTP character interpretation is case-sensitive, and often some specifications are entered twice—once in uppercase and once in lowercase.
Directive statements are grouped by the following categories:
• General directives apply to a particular instance of the server as a whole.
• Mapping directives cross-reference incoming requests to actual resource locations.
• File name suffix directives bind incoming requests for a file with a particular extension to MIME content types or subtypes.
• Directory list directives control how the contents of a specified directory are made available to the requester.
• Welcome directives map requests without an explicit page reference to a default, or welcome, page (index.html, for example).
• Logging directives control HTTP access and error logging.
• Accessory program directives determine which CGI program to call when an incoming request for program execution cannot be mapped to a program.
• Timeout condition directives establish a timeout value for requests from the browser, the server, or an executing program.
Essential HTTP Directives
Only a few directive statements are required for basic HTTP configuration. Enable and Disable are general directives that enable or disable a connection request. Pass is a mapping
directive that redirects incoming URL requests to actual system directories or libraries. Exec is a mapping directive that indicates that the server may execute a CGI program and specifies where the program may be found.
The Enable and Disable Directive Statements
The Enable and Disable statements instruct the server program to accept or reject a specified type of connection request. The basic types of connection method requests are as follows:
• GET requests a retrieval of Web page content or output from an executable program.
• HEAD requests a connection. (The HEAD method causes the server to return an HTTP document header without the document body. Generally, you use this method for testing.)
• POST indicates that the input to the CGI program will be passed in a standard input stream format, which is required for some types of HTML form processing.
• OPTIONS allows a client to determine the options and requirements associated with an object or determine the capabilities of a server without having to retrieve the object.
• TRACE causes the server to echo the request message sent by the client. (This method is used for testing.)
The default settings enable the GET, HEAD, OPTIONS, and TRACE methods and disable the POST method. (If you are going to allow form processing, you must specify the Enable POST directive.)
Pass Directive Statements
The Pass directive replaces a matched string coming from a browser within a URL request with a replacement string. The string that is to be matched and replaced is called the template. Pass is the directive statement used to map an incoming request for page content to the actual directory and file name. You may have multiple Pass directives; when a template match is found, the search is ended. The format of the Pass directive is as follows:
Pass request-template [file-path] [IP-address-template]
In this format, request-template is the incoming string that is to be matched, file- path (optional) is the directory and file name (an asterisk (*) indicates that file names will be passed as they are), and IP-address (optional) is the server address that the client connected to.
As I mentioned, your AS/400 is preconfigured with several Pass directives entered in the default configuration member CONFIG. (Do not make any changes to the ADMIN configuration member. There are no directive statements anyway because all parameters are correct as defaults.)
Figure 4 shows these two preconfigured Pass directives (highlighted). The first Pass directive instructs the HTTP server to route URL requests that do not include a specific file request (for example, www.myas400.com) to the AS/400 Integrated File System (AS/400 IFS) directory/QIBM/ProdData/ HTTP/Public/TC1/ICSS/ HTML/. And in that directory, you will find the HTML document Welcome.html, which is to be served by default. (Welcome.html is an IBM-supplied page that is provided as a sample.)
The other highlighted Pass directive redirects all requests to the directory /sample/* to the real directory /QIBM/ProdData/HTTP/Public/TC1/ICSS/ HTML/*. The asterisk (*) is a wild card character meaning “any file.” With these directives in place, a browser user could reference the URL http://s101901r.evergreen.com/ with no further identification of a
desired document, and the HTTP server would deliver the file Welcome.html. References within Welcome.html to resources (such as artwork files) in the directory /sample/ are likewise mapped to the real directory. You might consider replacing these preinstalled Pass statements (comment them out) with your own to point to your welcome page (usually named index.html) so your users will access your page, rather than IBM’s, when none is specified.
The directive Pass /www/* /webpage/* converts requests to www (the directory published to the world) to a real directory named webpage. The actual directory name is hidden from the browser user, thereby enhancing security. However, here is an important note: Specifying Pass /* (with no replacement string after it) is a serious security exposure. Specifying Pass /* disables any further access control that the server would impose. Using this directory, though, does not override any object-level security that you have in place.
Exec Directive Statements
The Exec directive indicates that the server may execute a CGI program and specifies where the program may be found. (All AS/400 CGI programs must reside in a regular library such as QGPL.LIB.) After a match to the template string is found, the request string is not compared with any other templates.
The format of the Exec directive is as follows:
Exec template program-path [ IP-address ]
[ CGI-conversion-code ]
Here, template is the request string that you want your server to accept and respond to by executing a CGI program; program-path is the name of the AS/400 library (in QSYS.LIB format) where the CGI programs are located; IP-address (optional) is the IP address of the HTTP server to which the client is connected (when HTTP servers represent themselves with more than one address); and CGI-conversion-code specifies the conversion coded character set IDs (CCSIDs) that are to be used (None is the default).
For example, the Exec directive statement Exec /cgi-bin/* /QSYS.LIB/MYCGI.LIB/* directs requests for program execution that refer to directory /cgi-bin/ to the real AS/400 library MYCGI. (Enabling an HTTP server for execution of CGI programs also requires the general directive Enable POST.)
It’s Your Server
The AS/400 Web server gives your users access to current AS/400 data and allows you to collect data from the users with an ordinary PC browser—altogether, an applications solution with very compelling potential.
References and Related Materials
• AS/400 TCP/IP Handbook. Chris Peters. Carlsbad, California: MC Publishing Co., 1999
• HTTP Server for AS/400 Webmaster’s Guide V4R4 (GC41-5434, CD-ROM QB3AEO04)
• IBM AS/400 Information Web site: www.as400.ibm.com/anchor/MRI2924/anchhome.htm
• OS/400 TCP/IP Configuration and Reference V4R4 (SC41-5420, CD-ROM QB3ANL03)
Web Browser
PC Database Applet Support
HTTP Server Program
HTML Documents
Other Page Content, Artwork,
Multimedia, Applets AS/400 Database
CGI Programs
Figure 1: In a Web server/browser arrangement, the server program delivers text, artwork, multimedia, and applet content to a browser program for interpretation and display.
HTTP server configuration item If using the HTTP configuration If using an AS/400 CL command (listed in ascending priority) and administration form access
Server defaults n/a n/a
Global server parameters Global server parameters form CHGHTTPA HTTP server directives in the Multiple forms in the
configuration file instance configuration section WRKHTTPCFG Instance configuration parameters Instance configuration form n/a Parameters specified when the Instance startup form HTTPSVR parameter on HTTP server instance is started STRTCPSVR command
Figure 2: There are five setting levels for HTTP configuration information, and the values can be set using either a CL command or an HTTP administration form.
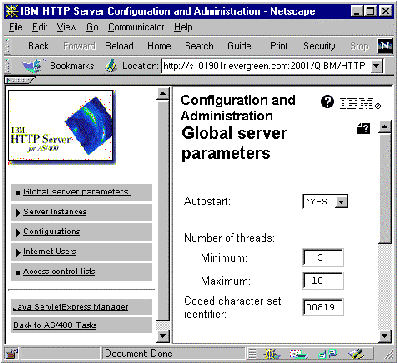
Figure 3: HTTP server configuration may be performed through the IBM- supplied HTTP Server Configuration and Administration applet in a Web browser.
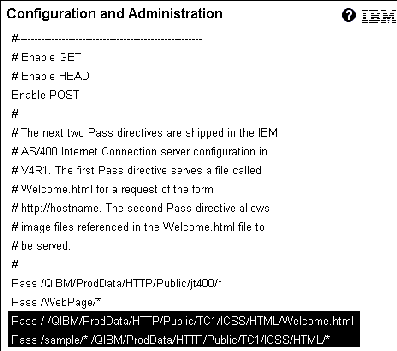
Figure 4: Pass directive statements align incoming requests for services with real AS/400 resources.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online