It comes as a surprise to some business people I talk to that they need to accommodate data sharing. “No” is sometimes their approach: “We don’t want to share data because it becomes more insecure; we want to protect it and limit data sharing.”
Editor’s note: This chapter is excerpted from chapter 9 of Identity Management: A Business Perspective.
You can’t argue with the logic “the more people who can access protected data, the harder it is to protect.” But it reminds me of the famous comedy sketch in which the hospital with no patients had the best KPIs: the lowest cost base and the shortest wait times. To not share data severely hinders the ability of an organization to do business. Organizations consist of people, and people need to share information in order to perform their job responsibilities.
Secure information sharing is a requirement of business today. Organizations can no longer secure the corporate network and pretend the company’s intellectual property and sensitive information is safe from malicious attacks or inadvertent loss. The network perimeter is so porous now that relying on firewalls and network edge devices is no longer tenable. Managers face an overwhelming amount of information, both structured and unstructured, and making efficient use of this data securely is becoming increasingly nuanced.
There is an increasing need to share data, not just within the organization but with business partners as well as customers. In the digital business, this increased communication has significant benefits to each line of business, improving efficiency and reducing costs. This data sharing also extends to business partners up and down the supply chain.
But there are increasingly more proficient solutions. As network solutions have become more and more incapable of providing robust data loss protection, secure data sharing solutions have become more competent in providing sophisticated solutions that organizations can use to protect themselves as they embrace data sharing—securely.
So organizational efficiency, cost reductions, and revenues improve as data is shared. But in order to support business processes, an organization must provide access to data that might be sensitive, so it is important that cybersecurity requirements are adequately observed. Determining the balance between security and business efficiency in the adoption of new technology is the task at hand.
The Options
There are two main approaches to securing the data: keep it in a data vault with access control in place, or use a rights management approach. A data vault is an encrypted data repository (e.g., database, document store) with the decryption keys given only to authorized personnel. This means that, if anyone needs access to the data, their request must be approved by the data custodian, who then gives them the decryption keys. Without the keys, the data is meaningless. One way to invoke a secure data repository is to use file system protection to give the appropriate access only to approved persons. Windows file shares are a form of data vault because only those users who have been granted access, often via the AD folder settings, can access the files. Yet another mechanism is to put the protected files in a document repository system on a protected subnet behind a firewall, and configure the firewall to allow access by approved personnel.
There are also multiple ways in which a rights management approach can be deployed. They rely on setting metadata on files, which controls who can access a file and what they can do with it. With information rights management (IRM), it is possible to allow someone to view a file but not allow them to edit, save, or print it.
Secure data repositories are best for secure document repositories—that is, files that contain corporate intellectual property that, if released, could cause damage to the organization.
A rights management approach is most appropriate for sharing information within a team, especially if team members work cooperatively on documents even though some are external. IRM gives the ability to invoke fine-grained, individual document rights to persons in the team.
Either option requires a robust and accurate IdM system to be in place within the company. In order to deploy a secure information-sharing solution, information such as department, job position, and AD group membership will be used to determine access to data and must therefore be accurate. It is equally important that as soon as a person leaves the company, his or her access rights are revoked. Of course, most organizations will use a mix of technologies. IRM might be used to share protected files within a department, while a secure data repository is used for corporate documents (e.g., board meeting minutes, financial information, audit reports).
Secure Data Repository
Establishing and maintaining a secure data repository is not a trivial exercise. The facility needs to support encryption, which means managing keys, and it requires the establishment of rules for access control. The key management requirement will vary depending on the type of keys being utilized. The simplest is a synchronous key operation in which the same keys are used for both ends of the transaction. Asynchronous keys are more secure, but policy on key validity must be addressed. A full public key infrastructure (PKI) deployment will require the establishment of a certificate authority (CA), hardware security modules, and revocation lists. For documents that must be stored in perpetuity, expiring certificates are a source of concern because a method to access to a document that has been signed by a key from an expired certificate needs to be accommodated. If there is no need for external access to a secure data repository, a simple configuration is to use a protected subnet and place the document repository behind the firewall. Maintaining access control within the firewall configuration then simplifies the task of keeping documents secure.
Rights Management
Rights management enables “seamless” protection of documents and files from the time they are created to the time they are destroyed, regardless of where the document is stored and to whom it is sent. A properly encoded document can be sent outside the company’s network, and the document will still carry the restrictions imposed at document creation.
Rights management is designed for unstructured data. It is not meaningful for databases, and indeed, database technology has strong and highly granular functionality for data sharing.
It is necessary, however, to have applications that are “rights aware.” Microsoft has been a leader in deploying rights management, and all Microsoft Office products are rights aware. The Microsoft Azure environment takes rights management to new heights. Azure Rights Management (RMS) enables wide collaboration within the Windows environment.
One of the issues with RMS is the granularity with which documents are to be classified. It is important that companies that engage IRM technology properly plan their classification scheme and ensure that all users adhere to the scheme. Automated, policy-based tools can be employed. There are particularly useful for classifying legacy documents, but such content-inspection functionality can also be used to “suggest” classification to users at the time of document creation.
The Secure Data vs. Rights Management Continuum
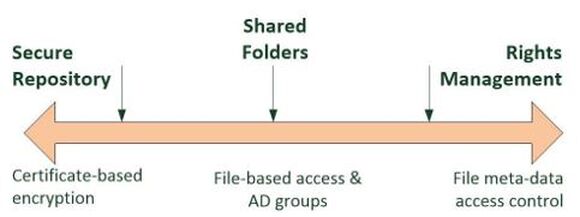
A useful approach to determining a preferred secure information-sharing approach is to map corporate requirements to a continuum, as shown in Figure 9.1, with secure data repositories at one end and rights management solutions at the other.
Figure 9.1: The secure data vs. rights management continuum
If the requirement is to keep board-level documents safe, a secure repository approach would be quite adequate, where each board member has been given a certificate for encryption. This will allow them to decrypt the documents they need to access for board meeting purposes, and to encrypt documents for other board members. A certificate approach will normally require digital certificates to be held in the user’s identity repository record for access by the authentication system that protects the secure repository.
Note: Using network protection—putting the server for board meetings behind a firewall and establishing an AD group for board members—will protect their documents at rest but not once they have left the server. Encryption will ensure that only those users with the appropriate decryption key will be able to read the documents.
At the other end of the continuum is the rights management approach, in which individuals who create documents can classify them and select who can explicitly access them, and if they can access them, the permissions they have for editing, printing, or saving the document. Such systems will need access to the organization’s identity repository to verify a user’s credentials in order to determine their permissions to access the protected resource. Increasingly, such rights management systems are being combined with a classification mechanism that will mark a document as secret, confidential, or personal and will, via policies established for the business, ensure that the conditions of access and user attributes satisfy the policy when access to a particular document is requested. (This will be discussed in more detail in the Classification section, page 175.)
Between these two extremes are file system functions that allow access by multiple users to designated folders. Shared folders in a Windows environment typically grant access to the documents and subfolders in the share to enrolled groups. This approach provides users access to resources typically on a group basis—that is, if you are in the appropriate AD group, you will get access to a shared folder and any file in the folder or subfolder. Access can be granted at varying levels as permitted under the file system: create, read, update, and delete.
Next time: More Data Sharing Considerations. Want to learn more now? Buy Graham's book today at the MC Press Bookstore.























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online